On the Secrecy Rate of Interference Networks using structured codes
This paper shows that structured transmission schemes are a good choice for secret communication over interference networks with an eavesdropper. Structured transmission is shown to exploit channel asymmetries and thus perform better than randomly generated codebooks for such channels. For a class of interference channels, we show that an equivocation sumrate that is within two bits of the maximum possible legitimate communication sum-rate is achievable using lattice codes.
💡 Research Summary
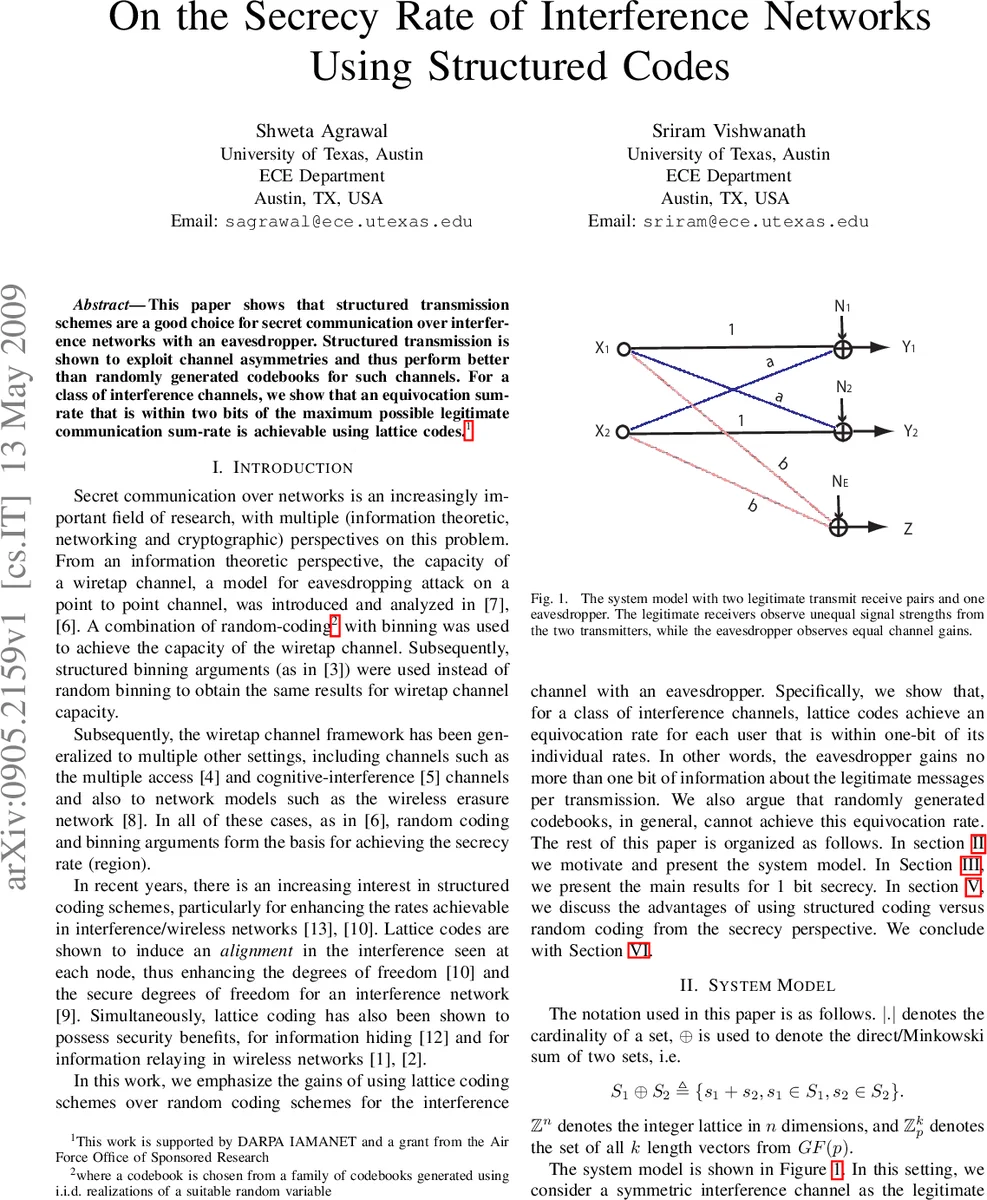
This paper investigates the use of structured transmission schemes—specifically lattice (or “structured”) codes—for achieving secure communication over a two‑user Gaussian interference network in the presence of an external eavesdropper. The authors begin by reviewing the classical information‑theoretic approach to secrecy, which relies on random coding together with binning (as originally introduced for the wiretap channel). While random coding achieves the secrecy capacity in many point‑to‑point and multiple‑access settings, it does not exploit asymmetries that naturally arise in interference networks where the legitimate receivers observe unequal signal strengths from the two transmitters, whereas the eavesdropper observes a symmetric linear combination of the transmitted signals.
The system model consists of two legitimate transmitter‑receiver pairs operating over a symmetric interference channel: (Y_1 = X_1 + a X_2 + N_1), (Y_2 = X_2 + a X_1 + N_2), with (a \neq 1). The eavesdropper observes (Z = b X_1 + b X_2 + N_e). All transmitters are subject to the same average power constraint (P); the noises (N_1, N_2) have unit variance, while (N_e) is arbitrary (the results hold even for (N_e=0)). The goal is to maximize the sum‑rate ((R_1+R_2)) achievable on the legitimate interference channel while ensuring that each message’s equivocation rate satisfies (R_{e,i} \ge R_i - 1), i.e., the eavesdropper learns at most one bit per channel use about each message.
The core contribution is a lattice‑coding construction that achieves this “1‑bit secrecy” across three regimes of the interference parameter (a):
-
Very Strong Interference ((a^2 \ge P+1)).
In this regime the interference is strong enough that each receiver can decode the interfering signal before decoding its intended message, effectively turning the network into two parallel point‑to‑point links. The authors employ a “good” Construction‑A lattice (\Lambda) (good for both source and channel coding) and define a nested lattice codebook (C = \Lambda \cap \mathcal{V}_L). Both transmitters use the same codebook and choose codewords uniformly at random. Lemma 1 shows that the entropy of the sum of two independent lattice points satisfies (H(X_1+X_2) \le \log|C| + n). Lemma 2 then yields (\frac{1}{n} I(X_1; X_1+X_2) \le 1). Since the eavesdropper observes exactly (X_1+X_2) (up to a scaling factor), the mutual information between any message and the eavesdropper’s observation is bounded by one bit per channel use. Meanwhile, each legitimate receiver can decode its own lattice point at rates arbitrarily close to the unconstrained point‑to‑point capacity, thus achieving the sum‑capacity of the interference channel with only a 1‑bit secrecy penalty. -
Weak Interference ((|a|<1)).
Here the optimal strategy for the interference‑free channel is to treat interference as noise. The authors demonstrate that the same lattice codebook can be used, together with a carefully chosen scaling factor (\alpha = \frac{P(1+a^2)}{P(1+a^2)+N}), to effectively “whiten” the interference at each receiver. After modulo‑(\Lambda_c) processing, the effective noise variance becomes (\frac{P(a^2 P + N)}{(1+a^2)P + N}), which is independent of the transmitted lattice point. Using standard lattice decoding results, each user can reliably decode at rates (R_i < \frac{1}{2}\log\bigl(1 + \frac{P a^2}{P+1}\bigr)), which matches the optimal rates for treating interference as noise. The secrecy analysis follows the same steps as in the very‑strong case: because both transmitters use the identical lattice codebook, the eavesdropper’s observation is again a sum of two independent uniform lattice points, and Lemma 2 guarantees the 1‑bit leakage bound. -
General Interference ((a) arbitrary, neither very strong nor very weak).
For intermediate values of (a) the authors adopt the multi‑stage lattice coding scheme of
Comments & Academic Discussion
Loading comments...
Leave a Comment