Hiding Information in Retransmissions
The paper presents a new steganographic method called RSTEG (Retransmission Steganography), which is intended for a broad class of protocols that utilises retransmission mechanisms. The main innovation of RSTEG is to not acknowledge a successfully received packet in order to intentionally invoke retransmission. The retransmitted packet carries a steganogram instead of user data in the payload field. RSTEG is presented in the broad context of network steganography, and the utilisation of RSTEG for TCP (Transport Control Protocol) retransmission mechanisms is described in detail. Simulation results are also presented with the main aim to measure and compare the steganographic bandwidth of the proposed method for different TCP retransmission mechanisms as well as to determine the influence of RSTEG on the network retransmissions level.
💡 Research Summary
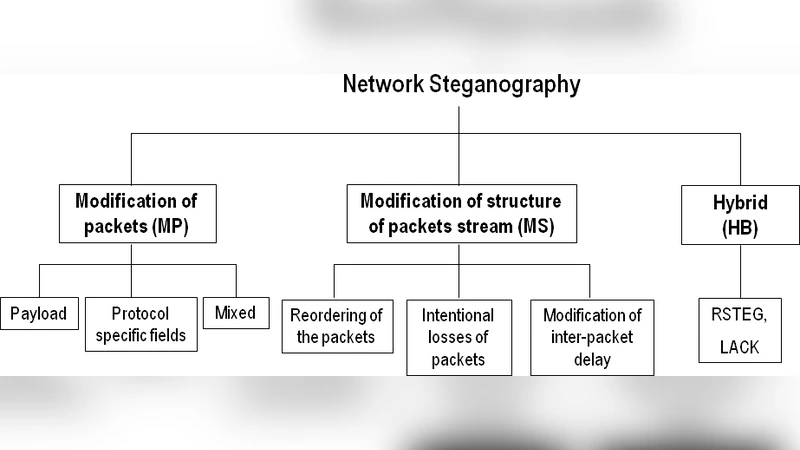
The paper introduces RSTEG (Retransmission Steganography), a novel network steganography technique that exploits the retransmission mechanisms of transport protocols, with a focus on TCP. Traditional network steganography is categorized into three groups: methods that modify packet contents (MP), methods that alter packet ordering or timing (MS), and hybrid methods (HB) that affect both. RSTEG falls into the hybrid category but distinguishes itself by using the retransmission process itself as a covert channel rather than directly altering payloads or headers.
The core idea is simple: the receiver deliberately withholds an acknowledgment (ACK) for a successfully received packet, causing the sender to trigger a retransmission after a timeout or duplicate‑ACK detection. The retransmitted packet, which would normally carry the original payload, is instead replaced with a steganogram. Because the retransmission is a normal part of protocol error recovery, network devices treat it as legitimate traffic, making detection difficult.
Four communication scenarios are described. Scenario 1 is the most straightforward, where the sender (Steganogram Sender, SS) and receiver (Steganogram Receiver, SR) cooperate directly; the receiver suppresses an ACK for a chosen packet, and the sender inserts hidden data into the retransmission. Scenarios 2‑4 involve one or two intermediate nodes that intercept, store, and later replace payloads, allowing covert communication without the end hosts’ explicit participation. These intermediate‑node scenarios increase stealth because only a segment of the end‑to‑end path carries the hidden data, and the manipulation is hidden within normal retransmission traffic.
Applying RSTEG to TCP, the authors examine three retransmission mechanisms:
- RTO (Retransmission Timeout) – triggered when an ACK is not received within a calculated timeout.
- Fast Retransmit/Recovery – triggered by three duplicate ACKs, indicating out‑of‑order delivery.
- SACK (Selective Acknowledgment) – allows retransmission of only missing blocks.
RSTEG can be implemented on any of these mechanisms. To coordinate the hidden exchange, the sender and receiver share a secret Steg‑Key. For each segment selected for covert use, a hash of the TCP sequence number, checksum, and a control bit (CB) is computed to generate an Identification Sequence (IS). The CB enables the receiver to differentiate a normal retransmission request from a segment that carries a steganogram, while keeping the packet format indistinguishable from ordinary TCP traffic.
The authors conduct simulations using realistic Internet traffic models. Results show that RSTEG can achieve covert bandwidths of roughly 5 bps (RTO), 12 bps (Fast Retransmit), and up to 20 bps (SACK) while keeping the overall retransmission rate below 7 % of total traffic. Increasing the hidden payload raises the retransmission rate and consequently the risk of detection, so the authors recommend dynamic throttling of covert data based on observed network congestion.
From a security perspective, because RSTEG leverages legitimate retransmission behavior, conventional anomaly detectors that monitor packet loss or retransmission counts may miss it. Effective detection would require statistical analysis of retransmission patterns, cross‑checking of retransmission requests against payload modifications, and possibly forensic examination of intermediate nodes that could be injecting hidden data.
In conclusion, RSTEG offers an efficient way to embed covert data without altering protocol semantics, but it demands careful management of hidden data volume versus retransmission frequency. Future work suggested includes extending the technique to other transport protocols (e.g., SCTP, DCCP), exploring multi‑path environments, and developing adaptive transmission strategies to further evade detection.
Comments & Academic Discussion
Loading comments...
Leave a Comment