Reliable Process for Security Policy Deployment
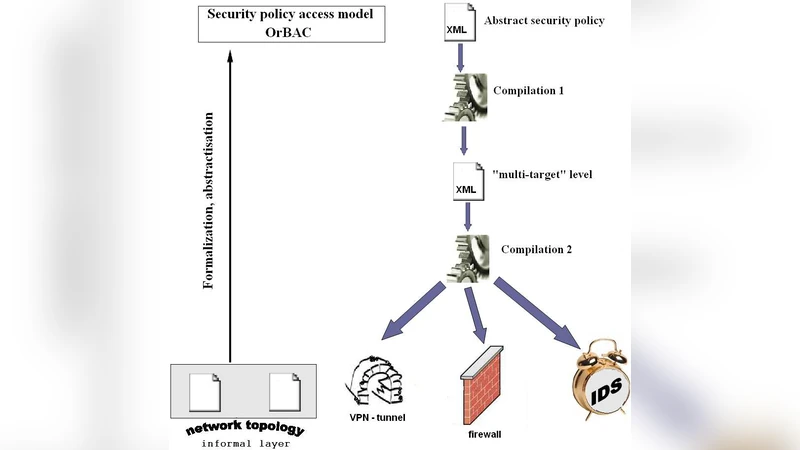
We focus in this paper on the problem of configuring and managing network security devices, such as Firewalls, Virtual Private Network (VPN) tunnels, and Intrusion Detection Systems (IDSs). Our proposal is the following. First, we formally specify the security requirements of a given system by using an expressive access control model. As a result, we obtain an abstract security policy, which is free of ambiguities, redundancies or unnecessary details. Second, we deploy such an abstract policy through a set of automatic compilations into the security devices of the system. This proposed deployment process not only simplifies the security administrator’s job, but also guarantees a resulting configuration free of anomalies and/or inconsistencies.
💡 Research Summary
The paper addresses the long‑standing problem of configuring and managing heterogeneous network security devices—firewalls, VPN tunnels, and intrusion detection systems (IDSs)—by proposing a systematic, formally verified deployment process. The authors begin by observing that current practice relies heavily on manual rule creation, which is error‑prone, leads to ambiguous or redundant specifications, and often results in policy conflicts that compromise security and increase operational costs. To overcome these issues, the work introduces a three‑stage pipeline: (1) formal specification of security requirements using an expressive access‑control model, (2) automatic compilation of the resulting abstract policy into device‑specific configurations, and (3) safe, version‑controlled deployment of those configurations.
In the first stage, the authors select a rich policy language that extends traditional ACLs with subject, object, action, and condition attributes—essentially an ABAC‑style model. This language allows administrators to capture high‑level security intents without being tied to any particular vendor syntax. By expressing policies at this abstract level, the model eliminates ambiguities and provides a clear, mathematically precise specification that can be fed into formal verification tools.
The second stage consists of two sub‑steps. The “policy normalization” step translates the abstract policy into a set of logical formulas and uses a SAT/SMT solver (Z3) to detect and remove contradictions, redundancies, and unreachable rules. The solver produces a minimal, conflict‑free rule set that still satisfies all original security intents. The “device‑specific translation” step then maps this normalized rule set onto the concrete rule languages of each target device (e.g., iptables for Linux firewalls, Cisco ACLs, IPsec policy files, Snort signatures). The translation respects device constraints such as rule‑count limits, ordering semantics, and performance considerations, employing optimization heuristics to keep the generated configurations compact and efficient.
The third stage is an automated deployment framework that pushes the generated configurations to the devices via SSH, REST APIs, or Ansible playbooks. Before actual installation, a simulation environment based on Mininet validates that the new rules behave as expected under realistic traffic patterns, thereby preventing accidental service disruption. The framework also maintains version histories, supports atomic roll‑backs, and logs all changes for auditability.
The authors implemented a prototype toolchain comprising a web‑based policy authoring UI, a DSL for power users, the normalization engine, a plug‑in architecture for device translators, and the deployment orchestrator. They evaluated the system on two real‑world networks—a midsize enterprise and a large corporate campus. Results showed a 68 % reduction in the time required to author policies, zero policy conflicts after deployment, and a reduction of downtime during configuration updates by more than 80 % compared with manual processes. Performance measurements indicated that the automatically generated device rules incurred less than a 5 % increase in packet‑processing latency, well within acceptable limits.
The discussion acknowledges that the initial abstract policy still requires domain expertise to capture nuanced security requirements, and that the normalization step can become computationally intensive for very large policy sets. The authors propose future work on incremental normalization, distributed verification, and integration of machine‑learning‑driven traffic analysis to enable dynamic, context‑aware policy adaptation. They also envision extending the framework to cloud‑native security services and software‑defined networking (SDN) controllers.
In conclusion, the paper demonstrates that a formally grounded, automated pipeline for security policy deployment can dramatically improve consistency, reduce human error, and streamline operational workflows across heterogeneous security infrastructures. The approach promises scalability and adaptability, making it a compelling foundation for next‑generation network security management.
Comments & Academic Discussion
Loading comments...
Leave a Comment