Computing the biases of parity-check relations
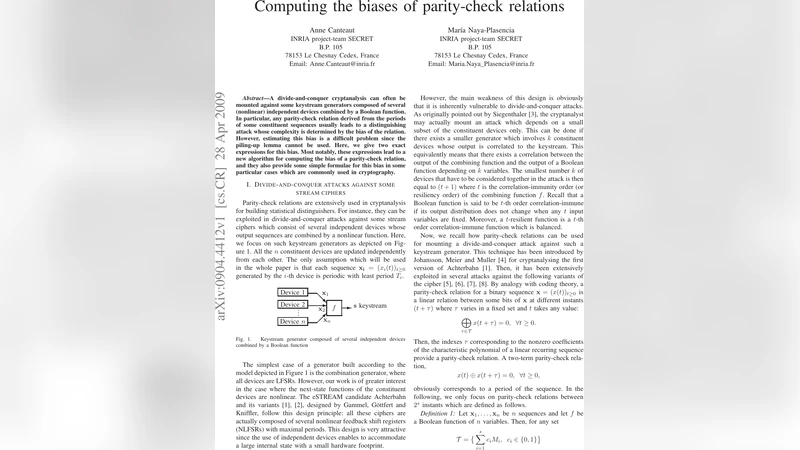
A divide-and-conquer cryptanalysis can often be mounted against some keystream generators composed of several (nonlinear) independent devices combined by a Boolean function. In particular, any parity-check relation derived from the periods of some constituent sequences usually leads to a distinguishing attack whose complexity is determined by the bias of the relation. However, estimating this bias is a difficult problem since the piling-up lemma cannot be used. Here, we give two exact expressions for this bias. Most notably, these expressions lead to a new algorithm for computing the bias of a parity-check relation, and they also provide some simple formulae for this bias in some particular cases which are commonly used in cryptography.
💡 Research Summary
The paper addresses a fundamental problem in the cryptanalysis of stream ciphers that are built from several independent nonlinear components combined by a Boolean function. In many such ciphers, an attacker can exploit the periods of the constituent sequences to construct a parity‑check relation – a linear combination of selected keystream bits that should equal zero. The distinguishing power of this relation depends on its bias ε, i.e., the deviation of the probability that the relation holds from ½. Estimating ε has traditionally relied on the piling‑up lemma, which assumes independence of the component outputs. This assumption is often violated in real ciphers, making the lemma give overly optimistic or pessimistic bias estimates and consequently inaccurate attack complexity predictions.
The authors present two exact expressions for the bias of any parity‑check relation, together with efficient algorithms to evaluate them. The first expression works in the Walsh‑Hadamard domain. By expanding the Boolean combining function f into its Walsh spectrum W_f(u) and introducing character functions χ_Ti(u_i) that capture the periodic structure of each component sequence, the bias can be written as
\
Comments & Academic Discussion
Loading comments...
Leave a Comment