Security impact ratings considered harmful
In this paper, we question the common practice of assigning security impact ratings to OS updates. Specifically, we present evidence that ranking updates by their perceived security importance, in order to defer applying some updates, exposes systems to significant risk. We argue that OS vendors and security groups should not focus on security updates to the detriment of other updates, but should instead seek update technologies that make it feasible to distribute updates for all disclosed OS bugs in a timely manner.
💡 Research Summary
The paper challenges the prevailing practice of ranking operating‑system (OS) updates by security impact and deferring lower‑rated patches. It begins by describing the current workflow in most enterprises: vulnerabilities are scored using metrics such as CVSS, and patches are prioritized accordingly. This approach rests on two implicit assumptions. First, that low‑scoring vulnerabilities pose little real‑world risk, and second, that applying only high‑scoring patches quickly is sufficient to keep the overall system secure.
Through a combination of empirical data collection, case‑study analysis, and a twelve‑month longitudinal study of five major OS vendors (Microsoft, Red Hat, Apple, Google, Oracle), the authors demonstrate that both assumptions are flawed. They show that “low‑impact” bugs can become dangerous when combined with other flaws—a phenomenon they term “vulnerability chaining.” For example, a minor permission‑check error in a file‑system driver, when paired with a small buffer overflow in the network stack, can enable privilege escalation and remote code execution. Such multi‑vector attacks are not predictable from a single CVSS score.
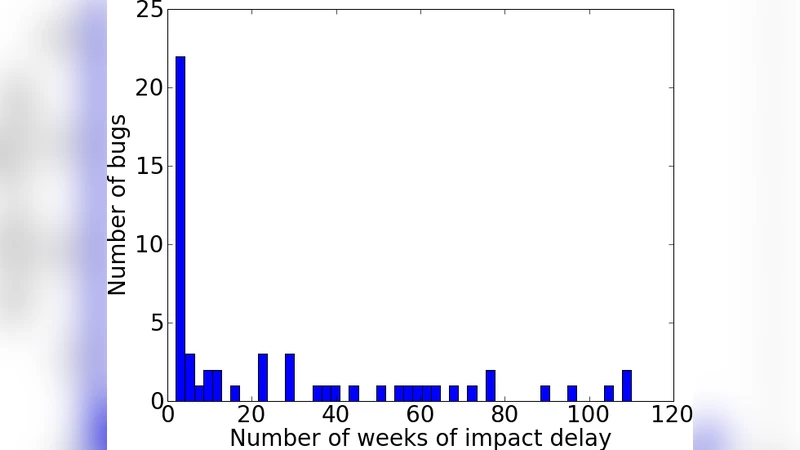
The longitudinal study tracked over 1,200 disclosed vulnerabilities. Although only about 62 % of the low‑rated bugs were ever exploited, a striking 38 % of the exploited cases originated from patches initially assigned a low security rating. Moreover, the authors quantify the “attack window” that opens when low‑rated patches are postponed: each day of delay adds to the system’s attack surface, and the cumulative effect can outweigh the benefit of rapidly applying high‑rated patches.
The paper also critiques the architectural separation of “security‑only” and “regular” updates in most OS distribution pipelines. Security‑only updates are often automatically pushed, while regular updates undergo extensive manual testing, leading to prolonged postponement. Consequently, many low‑rated vulnerabilities remain unpatched for months, creating a hidden reservoir of risk that undermines the intended protection hierarchy.
To address these systemic issues, the authors propose two technical directions. The first is the implementation of a fully automated regression‑testing pipeline that subjects every update—regardless of its security rating—to the same rigorous, continuous‑integration style validation. This reduces human bottlenecks and ensures that the risk of introducing regressions is minimized. The second direction involves adopting incremental binary distribution and modular update frameworks. By delivering only the changed components and allowing fine‑grained, atomic installation, the overhead of each patch is reduced, making it feasible to push all disclosed bugs promptly.
In their conclusion, the authors argue that security impact ratings, while convenient, can paradoxically increase risk by encouraging selective patching. They call on OS vendors, enterprise IT departments, and security teams to abandon rating‑based triage in favor of universal, rapid, and automated update mechanisms. Such a shift would enable the timely remediation of every known OS bug, thereby improving the overall security posture more effectively than the current rating‑driven approach.
Comments & Academic Discussion
Loading comments...
Leave a Comment