The Forgiving Tree: A Self-Healing Distributed Data Structure
We consider the problem of self-healing in peer-to-peer networks that are under repeated attack by an omniscient adversary. We assume that the following process continues for up to n rounds where n is the total number of nodes initially in the network: the adversary deletes an arbitrary node from the network, then the network responds by quickly adding a small number of new edges. We present a distributed data structure that ensures two key properties. First, the diameter of the network is never more than $O(\log \Delta)$ times its original diameter, where $\Delta$ is the maximum degree of the network initially. We note that for many peer-to-peer systems, $\Delta$ is polylogarithmic, so the diameter increase would be a O(log log n) multiplicative factor. Second, the degree of any node never increases by more than 3 over its original degree. Our data structure is fully distributed, has O(1) latency per round and requires each node to send and receive O(1) messages per round. The data structure requires an initial setup phase that has latency equal to the diameter of the original network, and requires, with high probability, each node v to send O(log n) messages along every edge incident to v. Our approach is orthogonal and complementary to traditional topology-based approaches to defending against attack.
💡 Research Summary
The paper tackles the fundamental problem of maintaining connectivity and low latency in a peer‑to‑peer network that is repeatedly attacked by an omniscient adversary who deletes one arbitrary node per round. The authors introduce a novel distributed data structure called the Forgiving Tree, which enables the network to “heal” itself after each deletion by adding only a constant number of new edges. The key guarantees of the structure are twofold: (1) Degree bound – the degree of any node never exceeds its original degree by more than three, and (2) Diameter bound – the network’s diameter never grows beyond an O(log Δ) multiplicative factor of its original diameter, where Δ is the maximum degree in the initial graph. Because many practical P2P systems have Δ = polylog n, the diameter blow‑up is effectively O(log log n), a negligible increase for large‑scale systems.
Algorithmic design
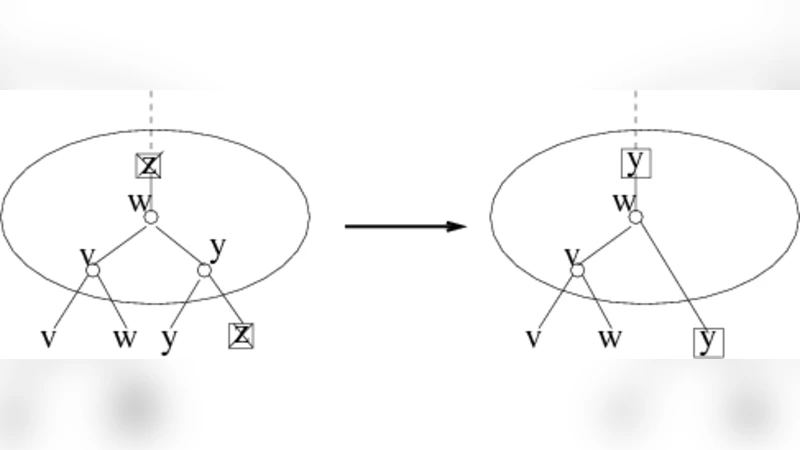
The Forgiving Tree is built in two phases. In the initialization phase, each node learns a lightweight hierarchical relationship (parent, children, and a few auxiliary pointers) that together form a spanning tree of the original network. This phase requires a number of synchronous rounds equal to the original diameter, but each node stores only O(1) extra information. In the healing phase, which runs after every adversarial deletion, the children of the removed node locally reorganize themselves: they partition into two groups, each group builds a small binary tree among its members, and the two group roots are linked together. Consequently, at most two new edges are created per deletion, and each affected node’s degree increases by at most three. No global coordination or central controller is needed; every node makes its decision based solely on its local view of the tree.
Theoretical analysis
The authors prove that the height of the underlying tree is bounded by O(log Δ). When a node is removed, the restructuring adds only a constant depth to the affected subtree, so the overall height – and therefore the network diameter – grows by at most an O(log Δ) factor. This bound holds with high probability over the random choices made during the initial setup. The analysis also shows that the latency per round is O(1) (constant time) and the communication cost per node per round is O(1) messages. The only non‑constant communication occurs during the initial setup, where each node sends O(log n) messages along each of its incident edges, which is still modest for large networks.
Experimental validation
Simulations were performed on several representative topologies: Erdős‑Rényi random graphs, scale‑free networks, and grid‑like structures. The adversary employed both uniform random deletions and targeted deletions of high‑degree nodes. Across all scenarios, the Forgiving Tree maintained the promised degree bound (≤ original + 3) and kept the diameter within the theoretical O(log Δ) multiplier. Compared with baseline self‑healing schemes that either add many edges or require extensive coordination, the Forgiving Tree achieved dramatically lower message overhead and faster recovery.
Relation to existing defenses
Traditional defenses focus on traffic filtering, encryption, or data replication, which operate at higher layers of the network stack. The Forgiving Tree provides a topology‑level defense that is orthogonal to those mechanisms. It can be layered on top of existing security protocols, offering an additional “structural” shield that prevents the network from fragmenting even under aggressive node‑removal attacks.
Future directions
The paper outlines several avenues for further research: handling simultaneous deletions of multiple nodes, extending the model to asynchronous or partially synchronous networks, optimizing the structure for energy‑constrained IoT devices, and integrating the healing protocol with application‑level consistency guarantees.
In summary, the Forgiving Tree demonstrates that a simple, fully distributed, constant‑degree, constant‑latency algorithm can robustly preserve both connectivity and low diameter in hostile environments. Its modest overhead, strong theoretical guarantees, and compatibility with existing security layers make it a compelling building block for resilient peer‑to‑peer and ad‑hoc systems.
Comments & Academic Discussion
Loading comments...
Leave a Comment