Design and Implementation Aspects of a novel Java P2P Simulator with GUI
Peer-to-peer networks consist of thousands or millions of nodes that might join and leave arbitrarily. The evaluation of new protocols in real environments is many times practically impossible, especially at design and testing stages. The purpose of this paper is to describe the implementation aspects of a new Java based P2P simulator that has been developed to support scalability in the evaluation of such P2P dynamic environments. Evolving the functionality presented by previous solutions, we provide a friendly graphical user interface through which the high-level theoretic researcher/designer of a P2P system can easily construct an overlay with the desirable number of nodes and evaluate its operations using a number of key distributions. Furthermore, the simulator has built-in ability to produce statistics about the distributed structure. Emphasis was given to the parametrical configuration of the simulator. As a result the developed tool can be utilized in the simulation and evaluation procedures of a variety of different protocols, with only few changes in the Java code.
💡 Research Summary
The paper presents the design and implementation of a novel Java‑based peer‑to‑peer (P2P) simulator that emphasizes scalability, ease of use, and built‑in statistical analysis. Recognizing that many researchers resort to custom simulators because existing tools lack user‑friendly interfaces and systematic data collection, the authors set out to create a platform that allows high‑level designers to construct overlays, configure key distributions, and obtain performance metrics without extensive programming.
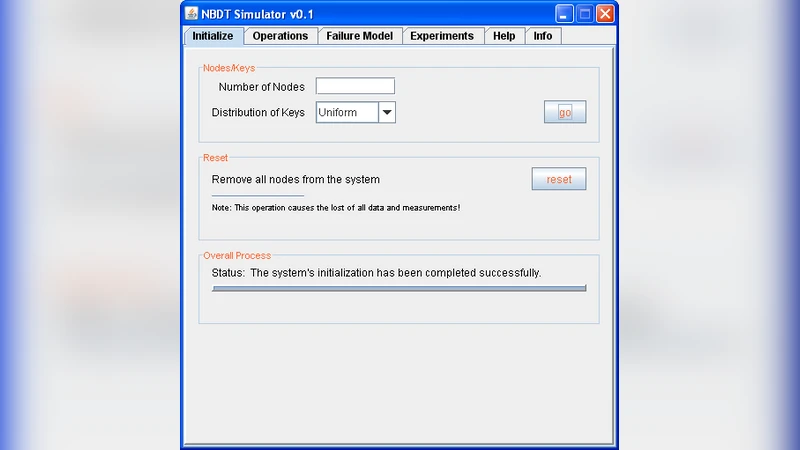
The simulator is organized into three layers. The lowest “kernel” layer implements the core entities: a Message class (containing sender ID, receiver ID, type, and a Data payload), a Network class that maintains a global message buffer (a Java Vector<Message>), a counter for total messages, and a log file for operation tracing. Message transmission is realized through a non‑blocking sendMessage() method that synchronously appends a message to the buffer, while reception uses a blocking recvMessage() that mimics POSIX socket semantics. The middle layer provides a SystemUI class exposing high‑level operations such as initialization, search, insert, delete, and queries about the current state (node count, key range, load balance). The top layer is a Swing‑based graphical user interface (GUI) with tabs for “Initialize”, “Search”, “Insert”, and “Delete”, allowing users to set the number of nodes, select key distributions (uniform, normal, Zipf, etc.), and watch real‑time logs and statistical charts.
To demonstrate the simulator’s capabilities, the authors adopt the Nested Balanced Distributed Tree (NBDT) as a case study. In NBDT each peer belongs to multiple recursively nested Balanced Distributed Trees. Each peer stores two index tables: a Left Spine Index (LSI) pointing to the left‑most spine nodes (size O(log log N)) and a Collection Index (CI) pointing to peers that share the same parent at a given level (size O(N^O)). The theoretical analysis shows that, under “smooth” key distributions (a superset that includes uniform, normal, Zipf, binomial, and power‑law), the load per peer remains polylogarithmic with high probability, and search/insert/delete operations require only O(log log N) hops.
Implementation details reveal that every peer is represented by a Java Thread (class Node extends Thread). Each node runs an infinite loop invoking eventHandler(), which checks the network buffer for messages addressed to it via msgForNodeId(). Upon receipt, the node dispatches the message to resolveMessage(), which calls either forwardJoinMessage() or forwardSearchMessage() depending on the message type. Join operations are sequential: an introducer forwards a join request to the current “last” node, which replies with the necessary LSI/CI tables and updates its pointers. Search operations traverse the LSI and CI tables to narrow the key range, achieving the O(log log N) hop bound.
The authors compare their tool with three well‑known simulators: PeerSim (pure Java, highly scalable but lacks GUI), p2psim (C++ based, limited to ~3000 nodes), and OverSim (built on OMNeT++, provides visualization only for small networks and requires detailed lower‑layer modeling). Their simulator distinguishes itself by integrating a GUI, automatic logging, and statistical output while still supporting a reasonable number of nodes (tens of thousands) for research prototypes.
Experimental results on NBDT with varying key distributions and node counts (10 K–100 K) confirm the theoretical predictions: average hop count stays near log log N, message overhead is modest, and load remains balanced across peers. The GUI displays real‑time logs such as “Search message for node 3 to node 45”, and after each run the system produces summary statistics (average hops, total messages, load variance).
The paper acknowledges limitations. The thread‑per‑peer model incurs high memory consumption, limiting scalability compared to event‑driven simulators. Concurrency control relies on synchronized methods, which may become bottlenecks under heavy simultaneous joins. The network model assumes lossless, zero‑delay communication; extensions for latency, packet loss, and churn are suggested as future work. Moreover, the current design enforces sequential insertion of joining nodes, which does not fully capture realistic concurrent join scenarios.
In conclusion, the presented Java P2P simulator offers a valuable bridge between theoretical protocol design and empirical evaluation, especially for researchers who need a quick, visual, and statistically rich environment. Future enhancements—such as moving to an event‑driven core, adding realistic network impairments, and optimizing concurrency—could further improve scalability and fidelity, making the tool suitable for large‑scale, production‑level P2P protocol studies.
Comments & Academic Discussion
Loading comments...
Leave a Comment