Overlay Cognitive Radio in Wireless Mesh Networks
In this paper we apply the concept of overlay cognitive radio to the communication between nodes in a wireless mesh network. Based on the overlay cognitive radio model, it is possible to have two concurrent transmissions in a given interference regio…
Authors: Ricardo Carvalho Pereira, Richard Demo Souza, Marcelo Eduardo Pellenz
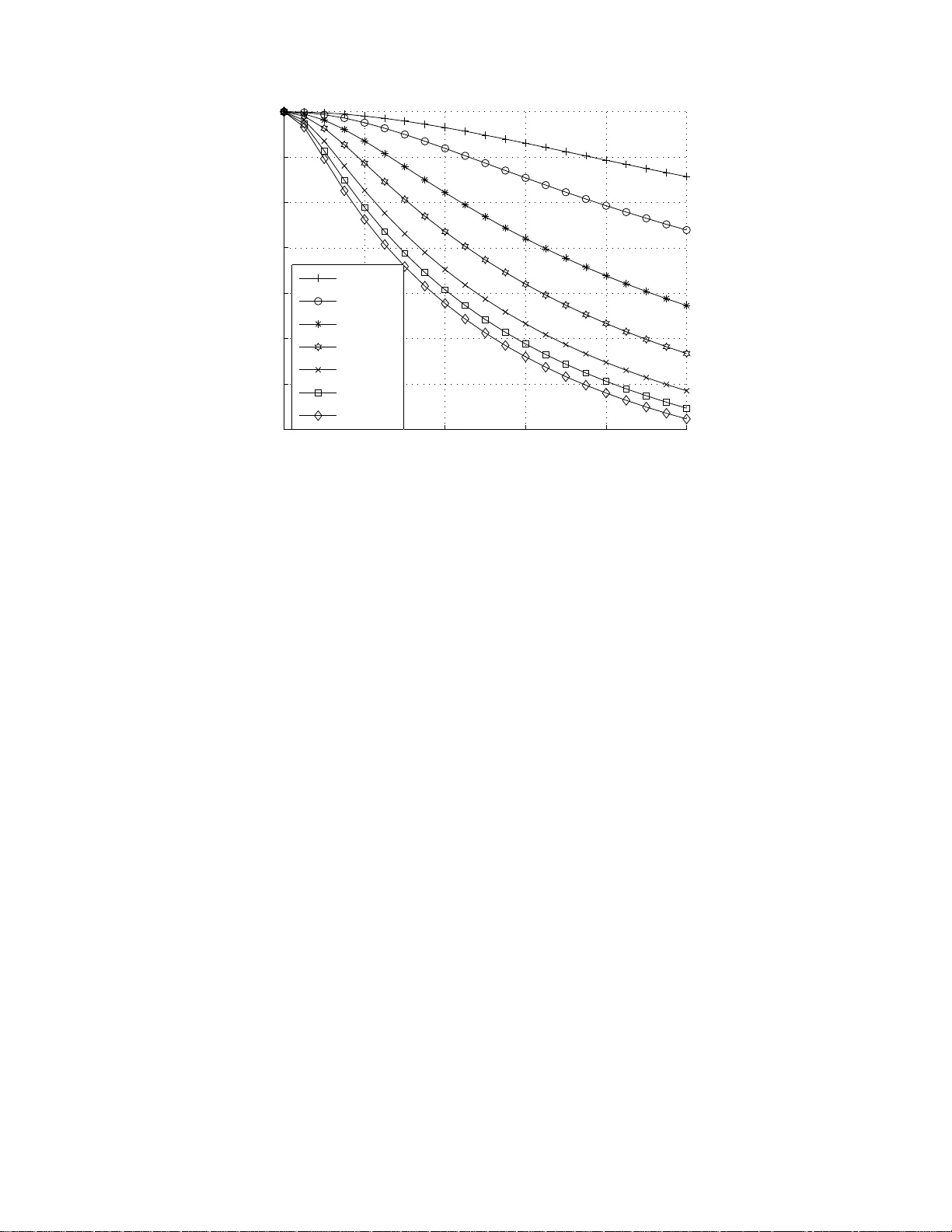
1 Ov erlay Cogniti v e Radio in W ireless Mesh Netw orks Ricardo Carvalho Pereira, R ichard Demo Souza, and Marcelo Eduardo Pellenz Abstract In this paper we apply the concept of ov erlay cogn iti ve radio to the comm unication between n odes in a wireless mesh network. Based on the overlay cogniti ve radio m odel, it is possible to have two co ncurren t tr ansmissions in a giv en interference re gion, where usually only one communication takes place at a giv en time. W e analyze the cases o f wireless m esh networks with re gular and random topolog ies. Numerical results show that considerab le network capacity g ains can b e achieved. I . I N T R O D U C T I O N W IRELESS Mesh Networks (WMNs) are expected t o resolve some of the limit ations and to sig- nificantly improve the performance of ad ho c networks, wireless local area networks (WLANs), wireless personal area networks (WP ANs), and wireless m etropolitan area networks (WMANs) [1]. Ac- cording to i ts architecture, WM Ns may be seen so mewhere between a well structured WLAN and an ad hoc netw ork. On one s ide, each user accesses a fi xed gateway i n order to est ablish a communication w ith the internet. On the other side, every node can reach any ot her node withi n a coverage area di ctated by the transmissio n range or be routed through the destination by adjacent users. In WMNs, each user node can operate either as a ho st or as a wireless router , forwarding packets on behalf of another no de that m ay not be wit hin t he coverage range of a wi reless gatew ay . The coverage extension ob tained by allowing the users to hope along other users in order to reach the gateway is an i mportant feature not only to b roader the cover age area, but also to allow users t o connect from indoor environments or from pl aces with h igh penetration losses. This results on a s ubstantial reduction of gatew ays deployment and, cons equently , the amount o f inv estments and operatio nal expenses. The WMN technology p resents a set of features that make it an i nteresting approach for future n etworks. Some of th em are related to the reduced in vestment s requi red to settle a startup network and to keep it growing, bec ause the technology can be inst alled incrementally , one node at a time, just as needed. In order to in crease the network capacity , accordingly to the demand, more gatew ays can be added. The reliability is imp rove d too, since the m esh structure ensu res the av ail ability of mu ltiple paths for each node in the network. If a node or a gate way fails, the traf fic is re-routed to av ailable nodes and gateways. Another interesting characteristic of WMNs is the fact that t he network coverage i ncreases with the number of gatew ays and users [2]. These features are driving t he ev ol ving of con ventional cellular networks int o Multihop Cellular Networks aim ing at th e enhancement of coverage, data rates, QoS p erformance in terms of call blo cking probability , bit error rate, as well as QoS fairness for different users [3]. Diffe rently o f ad hoc networks, the u ser traf fic pattern in WMNs is, essentially , between a user and a gate way [2]. Even th ough, th ere is s ome signaling t raf fic among users for routin g, configuration and control procedures, since this network is sup posed to be dynami cally self-forming, self-healing and self- organizing [1]. U sers can be stati onary or mobil e. Mobile users are able to be connected or roam as long as t hey are supported by the WMN coverage. R. C. Pereira and R. D. Souza are with CPGE I, UTFP R. A v . Sete de Setembro, 3165, Curitiba, PR, 80230-9 01, Brazil. Ph: +55 41 331046 86, Fax: +55 41 33104683. rcapereira@timbrasil.com.br,richard@cp gei.cefetpr .br . M. E. Pellenz is with PPGIA , PUCP- PR. Rua Imaculada Conceic ¸ ˜ ao, 1155, C uritiba, P R, 80215-9 01, Brazil. Ph: +55 41 32711777, Fax: +55 41 32712121. marcelo@ppgia.pucpr .br . 2 Usually , the capacity of WMN s is deriv ed based on the capacity of ad hoc networks and it is affe cted by m any factors su ch as [1]: n etwork architecture, network topology , traffi c pattern, network n ode density , number of channels used for each node, transmissi on po wer le vel, node mobi lity , to say a few . In [4] analytical lower and upper bounds of wireless network capacity are determined for the stat ionary case. The through put capacity per node reduces sign ificantly wh en the node densi ty increases, such that i t is O (1 / √ n ) , wh ere n is t he number of nod es. For a m obile scenario, in [5] it is sh own that lo ng term per node throughput can stay constant over the network. In [2] it is dem onstrated th at the existence of gatew ays in WMNs int roduces hot spot s i n t he network that act as bott lenecks. Du e to the presence of these bot tlenecks, the ava ilable capacity for each nod e is reduced to O (1 / n ) , wh ere n is the number of users for on e gateway . Nandiraju et al [6] p oints o ut that although there are s e veral research solutio ns to the capacity problem for ad hoc n etworks, cons idering the diffe rences between WMNs and ad hoc networks, many open research i ssues still exists. F or instance, such open research is sues include a strategy to decide on the opt imal placement of gatewa ys, optimal route selection strategies to increase th e throughpu t of the n etwork, and cross-layer d esign for network capacity improvement. In [7], t he concept of layerless commun ications is introduced, which opens a new perspectiv e to provide reliable and hi gh-quality end-to-end performance in w ireless multim edia networks, by means of a gl obal design and op timization. Recently , in [8] it was s hown that in a dense wireless ad hoc network in which nod es may cooperate, a hierarchical cooperation strategy can achieve an asy mptotically constant t hroughput per node. In this paper we discuss t he app lication o f a n e w comm unication paradigm to WMN, the cognit iv e radio model. At first, cognit iv e radios were viewed as a s olution to the problem of overc rowded spectrum by opportunist ic commu nication [9]. The basi c idea of cognitive radi o is to explore the existence of room in the licensed spectrum band s to accommodate secondary (unlicensed) wireless devices wi thout disrupt ing the communications of the pri mary (li censed) users of the spectrum. The cognitive radio concept can be implemented in d if ferent ways, which m ay try to underlay , interweav e, or overlay [10], [11 ] the secondary user’ s signal s with those of the primary users, such that the primary users of th e spectrum are as unaffected as po ssible. W e are particularly interested in the o verlay approach because of its special feature of al lowing concurrent transmissio ns within a gi ven interference region. In this paper we in vestigate the effe cts, in terms of network capacity , of applying t he overlay cognitive commu nication m odel between no des i n a WMN. Our numerical results show that the proposed schem e can bring con siderable capacity gains. Moreover , one of the key chall enges of the overlay cogn itiv e radio mo del, the secondary transm itter non - causal knowledge of the message to be sent by the primary transm itter , is overc ame by the sequential nature of WMNs transmis sions. The rest of this paper i s structured as follows. In Section II, we briefly discus s WMNs capacity . In Section III we revise so me cognitiv e radio models found i n the literature. In Section IV , we app ly the overlay cognitive communication m odel in a WM N. Section V presents numerical results that show the potential capacity improvements of this approach. Section VI concl udes the paper . I I . C A P AC I T Y O F S I M P L E W M N S Let us suppose the case of a simple WMN network that c onsists of a chain of nodes. W e assume that only one node in a given region (interference region) transmits at a time (assum ing a single frequency channel and no code-division mul tiple access). The interference region i s defined by the union of t he interference range of each radio regarding the communicatio n link un der consideration. The reason t o include the interference range regarding the receiver is based on the fact t hat this node, receiving a transmiss ion, must transmit b ack to the transmitter info rmation related to contenti on p rocedures, ackno wledge and channel st ate messages, routing procedures and so on. Al though a more realistic i nterference mod el would be continuous and take some aspects of the wireless en vironment into account, we follow the discrete interference model us ed by [12]. Such a discrete model is also used in [2]. 3 Fig. 1. Example of the discrete transmission and interference range model used in this paper . An example of the discrete in terference mod el is d epicted i n Figure 1. The s olid line circle is the transmissio n range of nod e 5. The d otted lin e circles are t he in terference ranges of nod es 5 and 4. Note that in t his example we considered the in terference range to be three tim es the transmissi on range. In this model we assum e th at if the receiv er is closer to the t ransmitter than the transm ission range radius, the receiv er will experiment error free reception. Moreover , any radio w ithin the int erference range of an active radio is forbidden to est ablish a com munication, since i ts transmi ssion would af fect the active radio. This ass umption imposes t hat during th e communicati on between n odes 5 and 4, n odes 8, 7, 6, 3, 2 and 1 are forbidden t o com municate because they are wi thin the interference range composed by the union o f the interference ranges o f nodes 5 and 4. Moreover , we assume that nodes are not abl e to simul taneously t ransmit and recei ve. In other words, they mu st follow the half-duplex constraint. The case where only the nod e furthest from the gatewa y generates traf fic to be sent to the gateway was anal yzed in [12], while the case of all no des generating traf fic was analyzed in [2]. The analysis we carry out in th is paper is based o n that presented in [12], since we cons ider that only one nod e (or a few nodes) generates traf fic. The case of traf fic coming from the gateway to t he nodes would be analy zed in t he same way . The g eneralization to th e case o f all nodes generating traffic can be done by analyzing each no de separately . The capacity of the WMN und er consideration is a funct ion of the extent of the interference that a node generates to other nodes. For instance, suppose t hat t he transmiss ion range is considered to be t he distance of on e unit (hop) when transmittin g at th e m aximum power level, and that the i nterference range is the s ame. T hen, since nodes can not transmit and receiv e at the same time, in [12 ] it is shown that the network capacity equals B / 3 , where B is t he capacity of the point to point communicati on between nodes. If we consider a m ore realistic scenario, where the interference range is g reater than the transm ission range 1 , then the network capacity is e ven small er . Suppose that the interference range i s three tim es t he transmissio n range, as i s the case in Figure 1 . So, if t here is a transmiss ion bet ween t wo nodes, any node within the interference region, dictated b y the i nterference ranges of both t ransmitter and receiver , i s not allowed to t ransmit. Figure 2 shows an o ptimum transmiss ion schedul e for this network, consid ering t he interference range to be three times the transmission range, as dis cussed above. In th e figure the arrows represent the links which are transmittin g at a giv en tim e. From t he figure we can see that concurrent transmissio ns occur only for every other fifth l ink. Therefore, the capacity o f the WMN in Figure 2, equals B / 5 . From no w on, in this paper , we will consider the interference range to be three times the transmissio n range. In a real scenario, using real radios and real protocols, the capacity would be even smaller . Howe ver , 1 According to [13] the interference range is t ypically more than twice the transmission range. 4 Time Flow 1 2 3 4 5 6 7 8 Fig. 2. Example of a W MN composed of a chain of nodes and a gate way . The arro ws represent the links which are transmitting at a given time. The interference range is three hops. since in this paper we discuss a theoretical novel transmi ssion scheme for WMN s, w hich is not based in any current wi reless com munications standard, w e focus in the simplified case of ideal protocols 2 . I I I . C O G N I T I V E R A D I O M O D E L S Cognitive radios are able t o listen to the surroun ding wireless channel, make decision s on th e fly , and encode data using a variety of schemes in order to better explore the channel characteristics and to mitig ate the interference [15]. As mentio ned earlier , the cognitiv e radio model can be classified into underlay , interweav e, or overlay mo dels [10], [11]. In t he und erlay model, the secondary users prot ect prim ary us ers by enforcing a spectral mask o n t he secondary signal, so th at the in terference generated b y the secondary devices is below the acceptable noise floor for the prim ary user of the spectrum [10]. Due to th e spectral mask constrain t imposed to the secondary users, this model is suitable for short range appli cations. Mo reov er , it i s ass umed that the secondary cognitive radio has k nowledge o f t he i nterference caused by its transmit ter to all no n cognitive users. The i nterference cons traint for t he no n cognitive users may be m et by using m ultiple antennas to guide the cognitiv e signals away from the noncognitive receiv ers, or can b e spread below the noise floor , th en despread at the cogni tiv e receiv er [11]. In [16], the authors propose an adaptive antenn a array approach, while the latter technique is the basis of bo th spread and ultrawideband (UWB) communicatio ns. Due to th e usual restriction o f short range appl ications of this ty pe of cognitive m odel, it will no t b e in our d iscussion on the connection o f cognit iv e radios and WM Ns. The interweave model requires that the s econdary transmit ter a voids in terference to the primary user by t ransmitting onl y over spectral s egments uno ccupied by the primary radios. This approach brings an improvement of the spectrum utilization by op portunistic frequency reuse over the spectrum hol es [11]. The interweav e techni que requires knowledge of the activity in formation of the p rimary users of the spectrum. In [1 7] t he authors propose the two-switch i nterwea ve model, which enables secondary activity only if there is no activity of the primary users within the interference range of bot h secondary transmit ter and receiver . Figure 3 sh ows a b lock diagram representing the two-switch model as propo sed in [17]. S T is t he secondary transmi tter and S R is the secondary receiv er , while P U is the primary user as seen by the transmitter or the receiv er . X S is the m essage that S T wants to send to S R . S t and S r are the secondary transmitter and receiv er swi tches. S t ( S r ) assumes the value of 1 when primary us er activity is n ot sensed at t he transmit ter (receiv er). If a primary user is sensed then the corresponding s witch assumes the value of 0. Y S is the message recei ved by S R , while Z S is random noise. In this cognitive radio m odel the capacity of th e primary t ransmitter is unaf fected by the behavior of the s econdary transmitt er . Let P S be 2 A good starting point for designing a real MA C protocol for t he method we propose in this paper is the work in [14]. 5 ST SR PU PU s t s r Z Y Y = s r (s t X + Z) X Fig. 3. The two-switch cognitiv e radio model proposed in [17]. Fig. 4. The overlay cognitiv e radio model proposed in [ 20]. the secondary transmi t power . Based on these definitions, in [17] the authors give an u pper bound on t he capacity for the secondary communication wi th global side i nformation, C ts , which is reproduced h ere: C ts ( P S ) = Pr ( S t , S r = 1) log 2 1 + P S Pr ( S t , S r = 1) ! , (1) where Pr ( θ ) is the probability of a given ev ent θ . By its turn, the overlay approach is consid ered t o be a form of cooperative transmissi on by Devro ye et al [18], [19]. The autho rs consider the case where two users asymmetrically cooperate to send two independent mess ages t o two separate non-cooperative recei vers, and the case when the second transm itter operates as a relay in order to help the primary transmitter . In both ca ses, it is assumed perfect channel state information at the primary and secondary transmitters, and that th e secondary transm itter has non-causal knowledge of the message to be transmi tted by the prim ary . Jovicic and V iswanath [20] introduced a computation for the capacity of bot h transmi tters in the overlay cognitive radio model, very s imilar to that in [18], [19], assuming that there is no chang e i n the encoding and decoding of the prim ary user . In o ther words, the primary transmitt er and receiver are un aw are of the secondary user . Figu re 4 illustrates the model considered in [20]. P T is t he primary t ransmitter , P R is the primary recei ver , X P is the message to be transmitted by the pri mary , Y P is the message received at the primary recei ver , Z P is random noise at the primary recei ver , a i s the channel g ain b etween S T and P R and b is the channel gain between P T and S R . The rest of the notation fol lows the definitions for Figure 3. X P and X S are lin ked in Figure 4 to ind icate t hat the secondary transmitter mu st hav e a pr iori knowledge of t he message that wi ll be sent by t he prim ary transmitter . In [20] it is s hown that, whil e the primary transm itter is unaffec ted, the secondary transmit ter can achie ve a rate as high as: 6 C over = 1 2 log 2 (1 + (1 − α ∗ ) P S ) , (2) where α ∗ = √ P P q 1 + a 2 P S (1 + P P ) − 1 a √ P S (1 + P P ) 2 , (3) P P is t he primary transmiss ion power , a ≤ 1 and α means the amoun t of power th e secondary transmitter uses to assist the primary communication and can assume values between zero and one. If α = 0 , th ere is no assistance to the primary comm unication. On the oth er hand, if α = 1 the total power of t he secondary transmitter i s us ed to assist the p rimary communi cation. The constraint t hat a ≤ 1 in the model i n [20] means t hat t he system is affected by a low interference gain, o r that t he secondary transm itter is closer to the secondary receiv er than to the primary receiver . N ote t he in dependence of b in (2). T hat is due t o the fact th at the second ary transmitt er has a prio ri knowledge of what the pri mary transmit ter wi ll send, and als o due to t he us e of dirty paper coding techniqu es [21]. Sriniv asa and Jafar [17] ind icate that the secondary transm itter capacity achiev ed with the ov erlay approach can be considerably greater than t he secondary transm itter capacity achieved through the inter- wea ve approach. The clear advantage of the overlay cognitive radio model i s the possib ility to have two concurrent t ransmissions within the s ame in terference region. W e finish t his section by noting th at it is possibl e to draw an analogy between the two-switch cogni tiv e radio m odel in [17] and the definition of the interference region. When a node i s transm itting the o ther nodes wi thin its interference region can not transmit, just as if thei r switches were open in the two-switch model. The t ransmitting node can be seen as the primary user , while the other nod es in its interference region are seen as secondary transmitters. At this point it is interesting to ask w hat would happen if the nodes withi n a g iv en interference region could commu nicate based on an overlay cognitive model as in [20] inst ead of the two-switch model. While a give n node is transmit ting (the prim ary user), another node in its interference region (the secondary user) could transmit t o a different node. In the next section we elaborate on this issue. I V . C O G N I T I V E R A D I O A N D W M N S One of the main challenges on the practical application of the o verlay mo del is the fac t that the s econdary transmitter must know the message that will b e sent by the primary transmi tter . From an in formation theoretic perspectiv e, if the secondary transm itter does not have such a p riori information (non-causall y), it may be possible to obtain such information causally , if t he capacity of the channel between both transmitters is m uch greater than the capacity of the channel between the primary transm itter and the primary receiv er [10]. In practice that mi ght b e hard to impl ement, and i t would require both transmit ters to be relatively close to each ot her . Howe ver , consider the case of a WMN where an intermediate node is relaying a message t o the next node t ow ards the g ate way . The source nod e, or a no de that relayed that s ame message at th e beginning of the chain of hops, knows what i s goin g to be transmitted from that int ermediate node. Therefore, it may be seen as the secondary t ransmitter o n the overlay cognit iv e radio model, while th e i ntermediate node would be the primary transmitt er . Due to the particular topol ogy of a WM N, and suppo sing perfect synchronization, t he i ssue of the non-casual k nowledge of th e primary transmitter message is naturally overc ame by the sequential natu re of WMNs transmissi ons. Note that usually in cognitive radio application s the primary and the secondary transmi tters belong to diffe rent communicatio n systems. For instance, the prim ary may be a broadcast TV transmitter , while the secondary may be part of a wireless l ocal area network. In our scenario both the pri mary and the secondary transmitt ers belong to th e sam e com munication system, a wireless mesh network. Mo reov er , the 7 nodes can dynamically operate as either primary or secondary transmitters, depending on the transm ission schedule. In a typical cognitive radio scenario, the primary transm itter is supposed to transmit at least at the same rate as if the secondary transm itter was not there. Here, for fairness purpos es, we want bo th primary and secondary transmitters to have the s ame rate. For that sake we consider the model defined as t he interference channel with degraded message sets (IC-DMS) discus sed in [20], which wa s also analyzed in [22]. The achiev able rate regions for that channel, the primary transm ission rate R P and the secondary transmissio n rate R S , are given by [20]: 0 ≤ R P ≤ 1 2 log 2 1 + √ P P + a √ αP S 2 1 + a 2 (1 − α ) P S , (4) 0 ≤ R S ≤ 1 2 log 2 (1 + (1 − α ) P S ) . (5) Then, we search for t he value of α that will guarantee the pair of closest rates ( R P , R S ) for a given value of a , P P and P S . In this case, and for a 6 = 0 , we enforce that the two concurrent transmi tters wil l operate at t he rate dictated by min( R P , R S ) . Thus, the prim ary achiev able rate will b e sm aller than t he rate that the primary user would experience i f the secondary user was n ot active. In order to m easure th e advantage o f empo lying concurrent t ransmissions withi n the same interference region according to th e overlay cognitive radio m odel, let B be the original rate of t he p rimary user . Depending on the cross coefficient a , different pairs of rates ( R P , R S ) can be achiev ed. Let γ be defined as γ = min ( R P , R S ) B , (6) where 0 < γ < 1 . Fig ure 5 s hows γ as a functi on of a for P P = P S ∈ { 1 , 2 , 5 , 10 , 20 , 30 , 4 0 } . From the figure i t is clear that γ decreases wi th the increase of the transmissio n power . This result is jus tified by the fact th at the greater is eith er the transm ission power or the channel gain a , the greater i s the interference experienced by the primary receiver du e to the secondary transmit ter . So, the secondary transmitter has to use m ore power (greater α ) to assist the pri mary commu nication and, therefore, less p owe r will last for its own communi cation. As a cons equence, its rate will be smaller and so γ , since it is a function of min ( R P , R S ) . In practical scenarios of WMN s, it is fair to assum e small values for a , since t he pri mary and secondary links mus t hav e at least another link between them. Moreover , the further the primary recei ver and the secondary transmi tter are (smaller a ), the larger is the capacity of both transmit ters. Supposing a l og- distance path los s model [23] with an exponent between 3 and 4, that the channel gain between P T and P R i s 1, and that the distance between S T and P R is about three t imes greater t han that of P T and P R , it i s fair to say that a in our case wil l be small (between 0.1 and 0.2). For th is case, even for l ar ge values of p owe r , from Figure 5 we can s ee that γ is at least close to 0.9. In the sequel we consider a = 0 . 2 and P P = P S = 10 for ev aluating num erical result s. In t his case, γ ≃ 0 . 95 . Th en, two concurrent transm issions with i nstantaneous rates of 0 . 95 B bits per channel u se can occur within a certain interference region, where before onl y one transmissi on occurred at a instantaneou s rate of B bits per channel us e. Therefore, we expect to obtain a consi derable capacity improvement when applying the overlay cognit iv e radio model for the comm unication b etween nod es in a WMN. V . N U M E R I C A L R E S U LT S In order to in vestigate t he effect of considering that nodes in a WM N can comm unicate using the overlay cognitive radio model [20], three kinds of WM Ns will be discussed. The first one is the simple chain o f nodes as introduced earlier . The second one is a generalization of the first one, a set of regular topologies. Th e last one is an arbitrary topolo gy with the gate way placed at the center and th e nod es 8 0 0.2 0.4 0.6 0.8 1 0.65 0.7 0.75 0.8 0.85 0.9 0.95 1 a (channel gain between ST and PR) γ P P =P S =1 P P =P S =2 P P =P S =5 P P =P S =10 P P =P S =20 P P =P S =30 P P =P S =40 Fig. 5. Factor γ as a function of a (channel gain between S T and P R ) and P P = P S . randomly placed around t he gat e way . Throughout this section w e consider that active nodes generate the same amount o f traf fic, that each node has an infinite packet buffe r and retains copies of the packets it forwards until that p acket is transmitted to the gat e way or has been forwar ded on by the nodes withi n its i nterference region, and that γ = 0 . 95 ( a = 0 . 2 , P P = P S = 10 ). Moreover , we define C W M N to be the ordinary wi reless mesh n etwork capacity , and C W M N over to be the wireless mesh network capacity when us ing the overlay cognitive radio model for the communi cation between nodes. Comparisons wil l be based on the ratio between these two capacities. A. S imple Chain T opology In the first case we consider th e same sim ple WMN composed of a chain of nodes s howed in Figure 2. Applying t he cognitive radio model, the second transm ission from node 8 to n ode 7 can occur at the same time th at node 6 is forwarding to node 5 the previous m essage sent by node 8. The second transmission from node 8 to node 7 would be seen as the secondary transmi ssion relative to the first transmi ssion from node 6 t o 5, whi ch of course would be the p rimary transmission . Not e th at in Figure 2 the second transmissio n from no de 8 occurs on ly during the first t ransmission from node 3 to node 2. Generalizin g this example, we hav e the transmission schedule shown in Figure 6. The transmission s represented by solid arrows are considered as primary t ransmissions regarding the cognitive radio model. The empt y arro ws represent the secondary transmissi ons that can occur in the prim ary’ s interference region si nce t he message of the primary transmitter is known by the s econdary transmitt er . Comparing Figures 2 and 6 w e can predict th at by using the cognitive radio m odel the network capacity will be increased. Indeed, t aking into account t he s ame definition for t he interference range as used in Figure 2 (three times the transmissio n range), we can show that C W M N over = γ 2 B / 7 . Since we assumed γ = 0 . 95 , this is a 36 % increase because in thi s case C W M N = B / 5 . B. R e gular T opology Consider now a regular topo logy as shown in Figure 7 with th ree possi ble different arrangements: nodes { 33 , 37 } generate traffi c, nodes { 33 , 35 , 37 , 3 9 } generate traffic , and nodes { 33 , 34 , 35 , 36 , 37 , 38 , 3 9 , 4 0 } 9 Time Flow 1 2 3 4 5 6 7 8 Fig. 6. Example of a WMN composed of a chain of nodes and a gatew ay . The nodes are able to communicate with each other by means of the ove rlay cogniti ve radio model. T he transmissions represented by solid arrows are considered as primary transmissions. The empty arro ws represent the secondary transmissions. The interference range i s three hops. generate traf fic. Th erefore, we have a generalization o f the previous setup, where now we con sider two chains, four chains and eight chain s of nodes. Considering γ = 0 . 95 , we can show t hat th ere is a capacity im prove ment of 19% , 22% and 1 6% for the cases of two, four and eigh t nodes generating traffic , respectiv ely . For ins tance, consid er the case where the ov erlay cogn itiv e radio m odel is not used and that only nodes 33 and 37 generate traffic towards the gatew ay . Therefore, we have two different network branches separated b y t he gatewa y . When n ode 1 3 is transmitt ing to node 5, node 9 can not t ransmit to node 1 since nod es 9 and 1 are wi thin the int erference region of nodes 13 and 5, ev en though they are in ano ther network branch. Following this procedure, where each node h as t o respect the interference regions not only of the nodes within its own chain, but also of t he nodes within neighbor chain s, we can show that in the steady s tate each packet from n odes 33 and 37 takes in average 5 transmissi on inst ants to reach the gatew ay . Therefore C W M N = B / 5 . A different schedule is obtained when applying t he overlay cognitive radio model. For instance, while nod e 5 is forwarding the first packet of no de 37 to the gateway , node 21 is already forwarding to node 13 the second packet of node 37. Generalizing, we can show t hat each packet from eit her nodes 3 3 or 37 will take in av erage 4 transmis sion i nstants to reach the gateway , which means a capacity of C W M N over = γ B / 4 . Therefore, si nce we assumed γ = 0 . 95 , t he improvement i s of 19 % . In the case of eight no des g enerating traf fic the gain i s smaller since there is an excess of branches close to each other . Many of the cognitive transmiss ion opportuni ties that appeared i n the other cases can not be exploited in this one since th ey would interfere with t he transmis sion of some ot her branch. This indicates that the future i n vestigation of inter branches coo peration can bring additio nal capacity gains. Finally , we end this section b y noti ng that such regular topolog ies as those in Figure 7 are not very likely in practice due, for instance, to topo graphical constraint s and us er densit y . C. Arbi trary T opology Let us now consider a more general, and practical, network topology sho wn in Figure 8. The interference range is considered to be three ti mes th e t ransmission range, as in th e previous examples. Therefore, each node h as a possibly different interference region which has to be taken i nto account in the capacity calculations. T he interference regions are listed i n T able I. W e consider a scenario where six no des { 4 , 5 , 12 , 22 , 24 , 26 } are generating traf fic. In thi s case we can show that by using the overlay cognitive radio model, and suppos ing γ = 0 . 9 5 , the capacity im provement is of around 36 % with respect to t he ordinary case (capacities of C W M N over = γ B / 12 and C W M N = B / 17 ). Furthermore, note also that i n the subnetwork composed of nodes 8 and 12 the overlay cognitive radio model is never used. Therefore, the improvement could be even larger if the packets comin g from node 12 required one more hop t o reach the gatew ay . 10 Fig. 7. Regular WMN topology . GW 5 1 2 3 4 6 7 8 10 11 12 14 15 16 17 18 19 22 23 24 25 26 Fig. 8. Arbitray W MN topology . 11 Node Nodes in its In terference Region 1 2,3,5,8,12 2 1,3,5,6,8,10 3 1,2,4-8,10,14,15,GW 4 3,6,7,10,11,17 5 1-3,8,12,14,GW 6 2-4,7,8,10,11,15-1 7,GW 7 3,4,6,10,11,15-17 ,GW 8 1-3,5,6,10,12,14-1 6,18,19,22-24,GW 10 2-4,6-8,11,14-19 ,25,GW 11 4,6,7,10,15-17,19 ,25,26,GW 12 1,5,8,14,15,18,22-2 4,GW 14 3,5,6,8,10,12,15-19 ,22-25,GW 15 3,6-8,10-12,14,16 -19,23-26,GW 16 6-8,10 ,11,14,15,17-19,24 -26,GW 17 4,6,7,10,11,14-16 ,18,19,25,26,GW 18 8,10,12,14-17 ,19,22-26,GW 19 8,10,14-18,23 -26,GW 22 8,12,14,18,23,24 23 8,12,14,15,18,19 ,22,24,GW 24 8,12,14-16,18 ,19,22,23,25,26,GW 25 10,11,14-19 ,24,26,GW 26 11, 15-19,24,25 GW 3,5-8,10-12,14-1 9,23-25 T ABLE I I N T E F E R E N C E R E G I O N F O R T H E N O D E S I N V O LV E D I N T H E C A L C U L AT I O N S O F T H E C A PAC I T Y O F T H E N E T W O R K S H O W N I N F I G U R E 8 . T opology Impro vement Simple Chain 36 % Regular - 2 branches 19 % Regular - 4 branches 22 % Regular - 8 branches 16 % Arbitrary 36 % T ABLE II C A PAC I T Y I M P R OV E M E N T AC H I E V E D B Y U T I L I Z I N G T H E O V E R L AY C O G N I T I V E R A D I O M O D E L F O R T H E C O M M U N I C A T I O N B E T W E E N N O D E S I N A W M N . V I . F I NA L C O M M E N T S WMNs and cognitive radios are two sub jects of intense research nowadays. W e propos e a way to bring these two ideas together . Our results show that the capacity of a WMN can be substant ially i ncreased by consid ering that the network nodes can commu nicate using t he overlay cognitive radio model. Such a model all ows for t wo concurrent transmiss ions wi thin a given interference region. T able II summarizes the results obtained in thi s paper , in terms of the capacity improvement achiev ed by utilizin g the overlay cogni tiv e radio model. From th e table we can see th at for the practical case of an arbit rary (randomly generated) topology the capacity gain was of 3 6% . There are many open questio ns related to our pro posal. For instance, h ow does t he capacity gain beha ve with no des density , number of gatewa ys, ty pe of traffi c? How to s ynchronize the primary and secondary transmitters? How to design a real transmission scheme that can approach the predicted performance o f the overlay cogni tiv e radio model? The promisin g results motivate further in vestigations in the pot entials and i mplications of the current p roposal. 12 R E F E R E N C E S [1] I. Akyildiz, X. W ang and W . W ang, ”Wireless mesh networks: a surve y , ” Elsevier Computer Networks , vol. 47, no. 4, pp. 445-487, Mar 2005. [2] J. Jun and M. Sichitiu, ”The nominal capacity of wireless mesh networks, ” IEE E W ir eless Communications , vol. 10, no. 5, pp. 8-14, Oct 2003. [3] L. Le and E. Hossain, ”Multihop cellular networks: potential, gains, research challenges, and a resource allocation framew ork, ” IEEE Communications Maga zine , vol. 45, no. 9, pp. 66-73, Sept 2007. [4] P . Gupta and P . R. Kumar , ”T he capacity of wi reless networks, ” IEEE Tr ansactions on Information T heory , vol. 46, no. 2, pp. 388-404 , Mar 2000. [5] M. Gr ossglauser and D. Tse, ”Mobility increases the capacity of ad-hoc wireless networks, ” Pr oc. IEEE Infocom , Apr 2001. [6] N. Nandiraju, D. Nandiraju, L. Santhanam, B. He, J. W ang, and D. P . Agrawa l, ”Wireless mesh networks: current challenges and future directions of web-in-the-sk y , ” IEEE W ire less C ommunications , vol. 14, no. 4, pp. 79-89, Aug 2007. [7] R. Pr asad, ”A perspecti ve of layerless communications, ” W ireless P ersona l Communications , vol. 44, no. 1, pp. 95-100, Jan 2008. [8] M. V u, N. De vroye and V . T arokh, ”An ov ervie w of scaling laws in ad hoc and cognitiv e radio networks” W i r eless P erson al Communications , vol. 45, no. 3, pp. 343-354, May 2008. [9] J. Mitola, Cognitive Radio: An i nte grated A r chitectur e f or Softwar e Defined R adio , Ph.D. Dissertation, KTH, Stockholm, Sweden, 2000. [10] S. S riniv asa and S. A. Jafar , ”The throughput potential of cognitiv e radio: a theoretical perspectiv e, ” IEEE Communications Maga zine , vol. 45, no. 5, pp. 73-79, May 2007. [11] A. Goldsmith, S. Jafar , I. Maric, S. Sri ni v asa, ”Breaking spectrum gridlock with cogniti ve radios: an information t heoretic perspecti ve, ” Submitted t o the IEE E Journ al on Selected Are as in Communications , 2008. [12] J. Li, C. Bl ake, D. S. J. De Couto, H. I. Lee, and R. Morris, ”Capacity of ad hoc wireless networks, ” Pr oc. 7th ACM I nt’l. Conf. Mobile Comp. and Net. , July 2001. [13] J. Jun, Capacity Estimation of W ir eless Mesh Net works , M.Sc. Thesis, North Carolina S tate University , U.S. A, 2002. [14] S. B oppana, M. Siv akumar , J. M. Shea, ”The ov erlapped carrier-sense multi ple access (OCSMA) protocol, ” Pr oc. IE EE MILCOM , 2007. [15] N. Devro ye, P . Mitran, and V . T arokh, ”Limits on communications in a cogniti ve radio channel, ” I EEE Communications Magazine , vol. 44, no.6, pp. 44-49, Jun 2006. [16] R. T aranto, H. Y omo, P . P opov ski, K. Nishimori, and R. P rasad, ”Cognitiv e mesh network under interference from primary user , ” W ir eless P erson al Communications , vol. 45, no. 3, pp. 385-401, May 2008. [17] S. A. Jafar and S. Sriniv asa, ”Capacity l imits of cognitive radio with distributed and dynamic spectral activ ity , ” IEEE Jo urnal on Selected A r eas in Communications , vol. 25, no. 3, pp; 529-537, April 2007. [18] N. Devro ye, P . Mitran, and V . T arokh, ”Achiev able rat es in cognitiv e radio channels, ” IEEE T ransa ctions on Information Theory , vo l. 52, no. 5, pp. 1813-1827, May 2006. [19] N. D e vroye, P . Mitran, O. -S. Shin, H. Ochiai, and V . T arokh, ”Cooperation and cognition in wireless networks, ” SK T elecom R evie w , Special Issue on 4G Spectrum and System E ngineering, February 2007. [20] A. Jovicic and P . V iswanath, ”Cogniti ve radio: an i nformation theoretic perspectiv e, ” Pro c. IEEE Int’l. Symp Inf. Theory , 2006. Also accepted in IE EE Tr ansactions on Information Theory . [21] M. Costa, ”Writi ng on dirty paper , ” IEEE T ransactions on Information Theory , vol. 29, n. 3, pp. 439-441, May 1983. [22] W . W u, S. V i shwana th, and A. Arapostathis, ”Capacity of a class of cognitiv e radio channels: i nterference channels with degraded message sets, ” IEEE T ran sactions on I nformation Theory , vol. 53, no. 11, pp. 4391-4399 , Nov . 2007. [23] T . S. Rappaport, W ir eless C ommunications: Principles and Practice , S econd Edition, Prentice-Hall, 2002.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment