Truthful Unsplittable Flow for Large Capacity Networks
In this paper, we focus our attention on the large capacities unsplittable flow problem in a game theoretic setting. In this setting, there are selfish agents, which control some of the requests characteristics, and may be dishonest about them. It is…
Authors: Yossi Azar, Iftah Gamzu, Shai Gutner
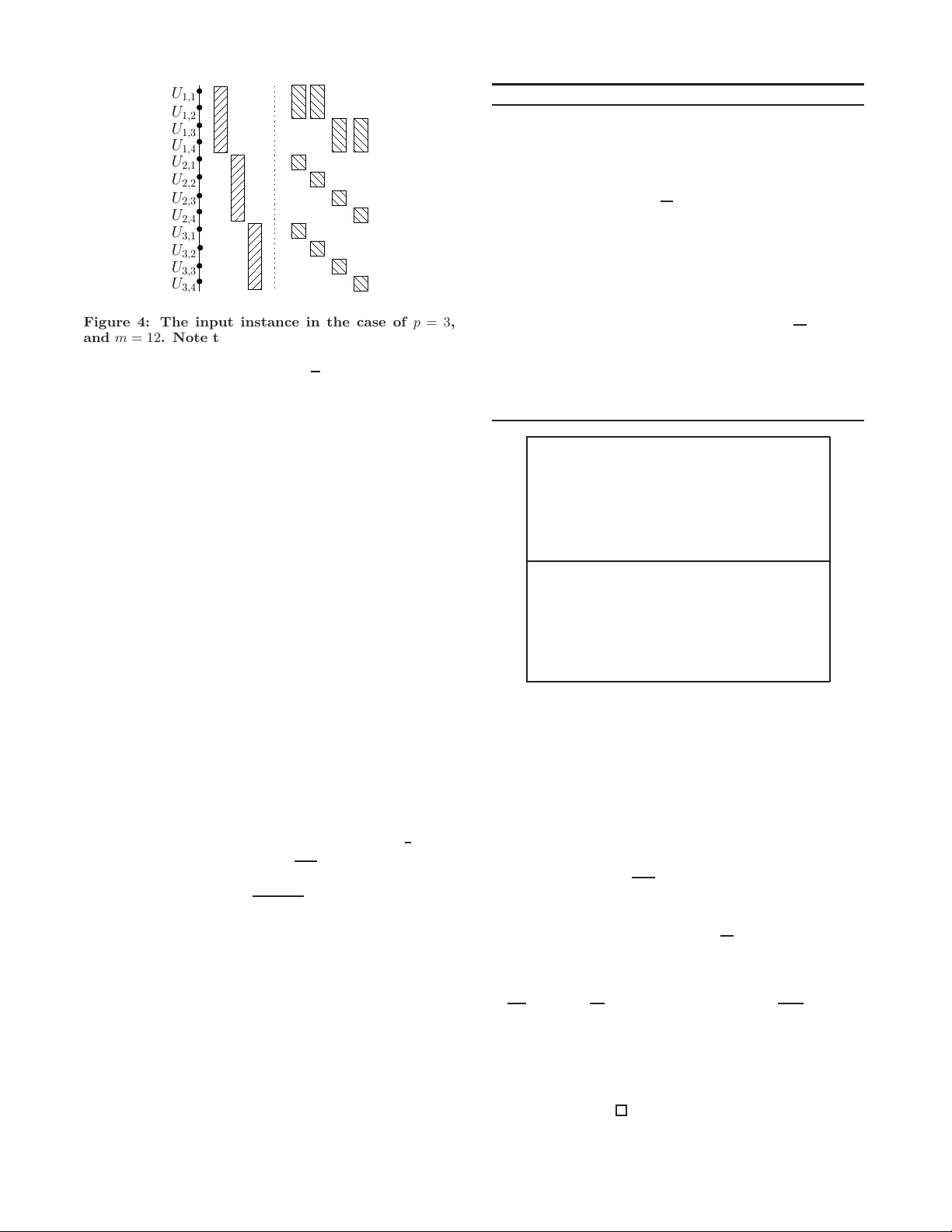
T ruthful Unsplittable Flo w f or Lar ge Capacity Netw orks Y ossi Azar ∗ Microsoft Research, Redmond and T el-A viv Univ ersity T el-A viv , 69978, Israel azar@tau.ac.il Iftah Gamzu School of Computer Science T el-A viv Univ ersity T el-A viv , 69978, Israel iftgam@post.tau.ac.il Shai Gutner † School of Computer Science T el-A viv Univ ersity T el-A viv , 69978, Israel gutner@tau.a c.il ABSTRA CT The unsplittable flow pr oblem is one of the most extensiv ely studied optimization problems in the field of net w orking. An instance of it consists of an edge capacitated graph and a set of conn ection requests, each of which is associated w ith source and target vertice s, a demand, an d a val ue. The ob jective is to route a maxim um v alue subset of requests sub ject to the edge capacities . It is a well known fact that as the capacities of th e ed ges are larger wi th resp ect to the maximal demand among th e requests, the p roblem can be approximated better. In particular, it is known that f or sufficiently larg e capacities, th e integr alit y gap of the corre- sp on d ing integer l inear p rogram b ecomes 1 + ǫ , which can b e matched by an algorithm that utilizes the rand omized rounding technique. In th is pap er, we fo cus our attention on the large capac- ities unsplittable flo w problem in a ga me theoretic setting. In th is setting, there are s elfish ag ents, which control some of the req u ests characteris tics, and may b e dishonest ab out them. It is worth noting t h at in game theoretic settings many stand ard tec hniques, such a s randomized ro unding, violate certain monotonicit y prop erties, which are imp era- tive for tru t hfulness, and th erefore cannot b e emp lo yed. In ligh t of t his s tate of affairs, we design a monotone determin- istic algorithm, which is based on a primal-dual machinery , whic h attains an approximatio n ratio of e e − 1 , up to a dispar- it y of ǫ a w a y . This implies an improv emen t on the curren t b est truthful mechanism, as well as an improv ement on the current b est combinatoria l algorithm for th e p roblem under consideration. S urprisingly , w e demonstrate that an y a lgo- rithm in th e family of reasonable iterative path minimiz- ing algorithms, cannot yield a b etter appro ximation ratio. Consequently , it follo ws that in order to achieve a mono- ∗ Researc h supported in part by the Israel Science F ounda- tion and by th e German-Israeli F oundation. † This pap er forms part of a Ph.D. th esis written by the author un der the sup ervision of Prof. N. Alon and Prof. Y . Azar in T el Aviv U niversit y . Permission to make digital or hard copies of all or part of this work for personal or classroom use is granted without fee prov ided that copie s are not made or distributed for profit or commercial adva ntage and that copies bear this notice and the full cita tion on the first page. T o cop y otherwise, to republi sh, to post on serv ers or t o redist ribut e to lists, requ ires prior speci fic permission and/or a fee. SP AA’07, June 9–11, 2007, San Die go, California , USA. Copyri ght 2007 A CM 978-1-5959 3-667-7/07/ 0006 ... $ 5.00. tone PT AS, if exists, one w ould ha ve to exert different tech- niques. W e also consider the large capacities single-minde d multi-unit c ombinatorial auction pr oblem . This problem is closely related to the unsp littable flo w problem since one can form ulate it a s a sp ecial case of the in teger li near program of the un splittable flow p roblem. Accordingly , we ob t ain a comparable performance guarantee by refin ing the algorithm suggested for th e unsp littable flow problem. Categories and Subject Descriptors F.2 [ Theory of Computation ]: Analysis of Algorithms and Problem Complexity General T erms Algorithms, Economics, Theory Keyw ords Mec hanism d esign, approximatio n algorithms, com binato- rial and multi-unit au ct ions, prima l-dual metho d 1. INTR ODUCTION The problems. W e stud y the unsplittable flow pr oblem . As input to th is problem, w e are given a directed or undi- rected g raph G = ( V , E ), suc h that n = | V | , m = | E | , and every ed ge e ∈ E has a p ositive capacity c e . An additional ingredient of th e input is a set R of connection requests, in whic h ev ery requ est r ∈ R is characterized b y a quadruple ( s r , t r , d r , v r ) s uch t hat s r and t r are the resp ective s our c e and tar get vertices of the request, d r is the p ositiv e demand associated with the requ est, and v r is the positive value or profit gained as a result of allocating the req uest. The ob jec- tive is to select a maximum va lue subset of requests S ⊆ R , along with a path for eac h selected request, so that all the requests in S can simultaneously route th eir demand along the co rresp onding path, w hile preserving th e capacity con- strain ts. Denoting by B = min e { c e } / max r { d r } the ratio b etw een the minimal capacit y of an edge and t he ma ximal demand among th e requests, the problem is referred to as the B-b ounde d un splittable flow pr oblem . Since one can nor- malize b oth the d emands of the requests and the capacities of the edges, the B-bounded unsplittable flo w problem can b e equiv alently defined to hav e d r ∈ (0 , 1] for every request r , and B = min e { c e } . N ote th at w e shall use the latter definition t h roughout this p ap er. W e also consider the single-minde d multi-unit c ombina- torial auction pr oblem . This problem is closely related to the unsplittable fl o w p roblem since one can form ulate i t as a sp ecial case of the integ er linear program of the unsplit- table fl o w problem. A n instance o f it consis ts of a set U of m non- identica l items, s uch that item u ∈ U has a positive integ er multiplicit y c u . The input also consists of a set R of requests, in which every req uest r ∈ R is characterized by a pair ( U r , v r ) such that U r ⊆ U is an items bund le, which is the demand associated with the request, a nd v r is the p os- itive value gained as a result of allocating the bund le. The goal is t o select a maximum va lue subset S ⊆ R , so that every item u ∈ U app ears in at most c u bundles of requests in S . Denoting by B = mi n u { c u } the minim u m multiplic- it y of an item, the problem is referred to as th e B-b ounde d multi-unit c ombinatorial auc tion pr oblem . The setting. I n the p resen t pap er, w e stud y the Ω(ln m ) - b ounde d unsplittab le flow pr oblem , and the Ω(ln m ) -b ounde d multi-unit c ombinatorial auction pr oblem from a me chanism design [15] p oint of v iew. In th is game-theoretic setting, some characteristics of the req uests, which are henceforth referred to as the typ e of the requests, are controll ed by self- ish agents . A n agen t is selfish in a sense that it migh t declare a fa llacious t yp e in order to manipulate t he a lgorithm in a w a y t h at will maximize its own u t ilit y . Ou r goal is to d esign mec hanisms, which are referred to as inc entive c omp atible or truthful , in whic h each agen t’s b est strategy is alwa ys to re- veal the tru e type of t he requ est that it controls, regardless of the other requests t yp es, a nd regar dless of th e wa y that the other agen ts decide to declare their requests types. In particular, w e aim to devise monotone algorithms whic h are, roughly s p eaking, eq uiv alent to trut hful mechanisms. Note that in the u nsplittable flow problem, the typ e of a request is its demand and v alue, whereas in the multi-unit com b i- natorial auction problem the t yp e of a request is its v alue. Also note that the other c h aracteristics o f the request, e.g. the source and t arget vertices in the unsplittable flow p rob- lem, are assumed to be kn o wn and thus, th e agen t cannot b e untruthful about t hem. The motiv ation. O n e of th e closely related problems to the u nsplittable fl o w problem is t h e mul tic ommo dity flow pr oblem . Since the multicommodity flow problem can b e mod eled by the relaxation of the in teger l inear program of the unsplittable fl ow problem, it may b e considered as its fractional vers ion. It is well k now n t hat the integr alit y gap of the integer linear program of the unsplittable flo w problem b ecomes 1 + ǫ when the ratio b etw een the minimal capacity of an edge and the maximal demand among the requests is sufficie ntly large. Consequently , it i s conjectured that in such case, the p erformance of a lgorithms for the fractional and integral versions w ould b e similar. S p ecifically , since the multico mmod ity flow problem ad m its a monotone PT AS by com binatorial primal-dual base d algorithms [9 , 8], one may exp ect that an integral version of these monotone PT AS w ould yield a monotone PT AS for the unsplittable flo w prob- lem. In the follo wing, we refute this p ercept ion. In particu- lar, w e design a primal-dual base d monotone algorithm for the Ω(ln m )-b ounded un splittable fl ow problem that attains the b est p ossible app roximation ratio with resp ect to any r e asonable iter ative p ath mini mizing algorithm 1 , and is not a PT AS. Nevertheless, This algorithm still impro ves up on the b est prev ious k n o wn result [7]. 1 The family of r e asonable iter ative p ath minimi zing algo- rithms is formally defin ed in Su bsection 3.3. 1.1 Our r esults Monotone deterministic algorithms. W e describe a monotone d eterministic algorithm based on a primal-dual approac h for the Ω(ln m )-b ounded unsplittable flow prob- lem, which obtains an approximation ratio that approac hes e e − 1 ≈ 1 . 58. This result implies a corresponding incen- tive compatible mec hanism. In addition, w e sho w that the aforesai d algorithm can b e attuned for the Ω(ln m )-b oun d ed multi-unit combinatori al auction problem, and attain a com- parable app roximation ratio, i.e. e e − 1 -approximation. These results improv e ove r the approximation guarantee suggested by Briest et al. [7] for both problems, whic h app roac hes e ≈ 2 . 71. Deterministic low er bounds. W e pro ve that any algo- rithm for the Ω(ln m )-b ounded unsplittable flow problem, whic h is part of t h e reasonable iterative path minimizing algorithms family , cannot y ield an approximation guaran- tee th at is b etter than e e − 1 − o (1). This implies, on the one h an d , that the analysis of our algorithm is tight, and on the other hand, that to ac hieve a monotone determin- istic PT A S , if exists, on e w ould hav e to employ different techniques. Additionally , w e reinforce this inapp ro ximabil- it y result by d emonstrating th at even if we ease th e problem setting, e.g. assume that the minimal capacit y of an edge is arbitrarily large, still n o reasonable itera tive path minimiz- ing algorithm can attain PT AS . Corresp ondingly , we also establish a lo w er b ound of 4 / 3 on the app ro ximation ratio of any reasonable iterativ e bundle minimizing algorithm for the Ω(ln m )-b ounded multi-unit combinatoria l auction problem. A deterministic (1 + ǫ )-appro x i mation algorithm. W e study th e Ω(ln m ) -b ounde d unsplittable flow wi th r ep e- titions pr oblem , which is a v arian t of the Ω(ln m ) -b ounded unsplittable flow problem in whic h one is allo w ed to satisfy every req uest multiple times using p ossibly m ultip le paths. In contrast with our prior findings, we demonstrate that this versi on admits a d eterministic primal-dual based algorithm, whic h yields an (1 + ǫ )-approximati on. 1.2 Related work The u nsplittable flow problem, and i ts fractional vari ant, the multicommodity flow problem, has been give n an exten- sive attention in recent yea rs, b oth from an algorithmic p oint of view and from a game-theoretic one. These fundamental optimization problems mo del a diverse collection of appli- cations in netw ork routing, parallel compu ting, an d even in VLSI la yout. Obviously , the fractional problem is easier. In particular, it is kn o wn to admit an op t imal solution by lin- ear programming, and an ( 1 + ǫ )-approximate solution by com binatorial algorithms, see e.g. [9, 8]. In contrast with the fractional p roblem, app ro ximating the integral problem is hard. Guruswami and T alw ar [11] hav e recently show ed that th e directed version of the problem is n Ω(1 /B ) -hard to approximate unless NP ⊆ BPTIME( n O (log log n ) ), where B = O (log n/ log log n ) is the minimal capacity of an edge. This result extended the prominent result of Guruswa mi et al. [10], which states that if B = 1, it is NP-hard to approximate the problem to within a factor of O ( n 1 / 2 − ǫ ). Resp ectively , when the graph is u n directed, Andrews et al. [1] established an (log n ) Ω(1 /B ) -hardness for any B = O (log log n/ log log log n ), under th e assumption that NP * ZPTIME( n p olylog( n ) ). Nev erth eless, when B is sufficien tly large, e.g. B = Ω(ln m ), th e integral ity gap of the inte- ger linear program of the problem b ecomes 1 + ǫ , whic h can b e matc hed by an algorithm that utilizes the random- ized round ing technique [17, 16, 18]. Unfortunately , this standard technique violates certain monotonicity prop erties, whic h are imp erative for truthfulness and thus, cannot b e directly used in th e presence of selfish agen ts to obtain a truthful mechanism. Accordingly , u ntil recently , the known truthful results for the Ω(ln m )-b oun ded unsplittable flow problem only guaranteed approximation ratios that were at least logarithmic in the size of the graph [5, 6, 4]. Briest et al. [7] seem to ha ve b een the first to propose a constant factor appro x imation al gorithm. Essentia lly , they desi gned a monotone primal-dual based alg orithm, which w as moti- v ated b y the no vel work of G arg and K¨ onemann [9 ] on the fractional problem, th at ac hieves an approximation guaran- tee t hat approaches e . The resea rch of the singl e-minded multi-unit combinato- rial auction problem, whic h is closely related to the unsplit- table fl o w problem, yielded similar results. Bartal et al. [6] sho we d that appro ximating the problem to within a factor of O ( m 1 / ( B + 1) ) is N P-hard, where B is the minimum multiplic- it y of an item. Y et, when B = Ω(ln m ), the integ ralit y gap of the correspond ing integ er linear program b ecomes 1 + ǫ . Ac- cordingly , A rcher et al. [2], and La vi and Swa my [12] devised truthful (1 + ǫ )-approximation mec hanisms. How ever, these mec hanisms are trut h ful only in a p robabilistic sense and hence, the best known deterministic t ruthful res ult for the Ω(ln m )-b ounded multi-unit com binatorial auction p roblem is by Briest et al. [7], which attains e -approximation. 2. PRELIMINARIES In what follo ws, we present the n otions of monotonicity and exactness , and then turn to d escribe a characterizati on that reduces the goal of d esigning tru thful mec hanisms to that o f designing monotone and exact algori thms. Remark that the illustrated terms are p resented in th e context of the problems under considerations and h ence, the kee n reader ma y refer to Lehmann et al. [13] or Briest et al. [7] for more formal and comprehensive d efinitions of the underlyin g con- cepts. Definition 2.1. An algorithm A f or the unspli ttable flow pr oblem is said to b e monotone w.r.t. the demand and value of a r e quest r ∈ R , i f it satisfies the fol lowing pr op erty: if algorithm A sele cts r when its demand i s d r and its value is v r then algorithm A would have sele cte d r if its demand was ˜ d r ≤ d r , its value was ˜ v r ≥ v r , and the demands and values of al l t he oth er r e quests wer e fixe d. Definition 2.2. An algorithm A f or the unspli ttable flow pr oblem is c al le d exact , if it al l o c ates the exact demand of every r e quest sele cte d, and do es not al lo c ate anything other- wise. Theorem 2.3. ([13, 7]) If algorithm A for the unsplit- table flow pr oblem is m onotone and exact w. r.t. the demand and value of every r e quest then ther e exists a c orr esp ond- ing truthful me chanism. In addition, t his me chanism c an b e efficiently c ompute d using algorithm A . Note that similar definitions can analogousl y b e made for the single-minded m ulti-unit com binatorial auction prob- lem. The only exception is that the monotonicity p rop erty , and the characterization theorem are only defined with re- sp ect to th e v alue of every request, i.e. the demand terms need to b e cast off. 3. UNSPLITT A BLE FLO W PROBLE M 3.1 The algorithm In this sub section, w e devise a deterministic monotone al- gorithm for th e Ω(ln m ) -b ounded unsplittable fl o w problem, whic h achieve s an approximation ratio t h at approaches e e − 1 . Our algorithm is based on a primal-dual machinery . Accord- ingly , w e present in Figure 1, th e primal-dual formula tion of the unsplittable flow problem. This will b e later used t o motiv ate the algorithm. max X r ∈R v r · “ X s ∈ S r x s ” s.t. X s ∈ S | e ∈ s x s d s ≤ c e ∀ e ∈ E X s ∈ S r x s ≤ 1 ∀ r ∈ R x s ∈ { 0 , 1 } ∀ s ∈ S min X e ∈ E c e y e + X r ∈R z r s.t. z r + d r X e ∈ s y e ≥ v r ∀ r ∈ R , ∀ s ∈ S r y e ≥ 0 ∀ e ∈ E z r ≥ 0 ∀ r ∈ R Figure 1: The integer line ar program of the unsplit- table flo w proble m (top), and the dual of its rel ax- ation (b ottom). Note that S r denotes the set of all the simpl e paths be tw een s r and t r in G , S = S r ∈R S r , and d s and v s denote the respe ctive demand and v alue of path s , i. e. if s ∈ S r then d s = d r and v s = v r . Algorithm Bounded- UFP , formally describ ed below, is a primal-dual based algorithm for the Ω(ln m )- b ounded un - splittable fl o w problem. Informally , th e algorithm maintains the va riables of the primal and dual programs, and in eac h it- eration selects to satisfy a request, whic h corresp onds to the “most viol ated” constrain t of the dual linear program. F a- vora bly , this redu ces t o finding a ( normalized) shortest path in t he graph G , whose edge w eigh ts correspond to t h e set of dual v ariables y e . It is wo rth n oting that the algorithm, and part of its analysis is in the spirit of the algorithm suggested by Briest et al. [7]. W e w ould like to note t h at since t he path related vari ables, and th e request related v ariables, i.e. the x s and z r v ariables respectively , pla y no role in th e ex ecution of the algorithm, lines 2, 3, and 12 are not regarded part of the algorithm. Nevertheless, we decided not to neglect them from the algo- rithm’s description since they ease th e analysis presentation. Algorithm 1 Bounded-UFP ( ǫ ) Input: An accuracy parameter ǫ ∈ (0 , 1] Output: A (request, path) pairs set W , which h olds th e requests to b e allocated 1: Let L b e a list of all th e requests, and let W b e an empty set 2: for all r ∈ L do z r = 0 end for 3: for all s ∈ S do x s = 0 end for 4: for all e ∈ E do y e = 1 c e end for 5: while ` L 6 = ∅ and P e ∈ E c e y e ≤ e ǫ ( B − 1) ´ do 6: for all r ∈ L do 7: Let p r b e the shortest path b etw een s r and t r in G with resp ect to the wei ghts y e , and let | p r | = P e ∈ p r y e b e its length 8: end for 9: Let ˆ r b e the request, which minimizes d r v r | p r | with respect to every r ∈ L 10: for all e ∈ p ˆ r do y e = y e · e ǫBd ˆ r /c e end for 11: Add ( ˆ r, p ˆ r ) to W , and remov e ˆ r from L 12: Let x p ˆ r = 1 and z ˆ r = v ˆ r 13: end while 14: return W 3.2 Analysis In t h is sub section, we will prov e the follo wing theorem. Theorem 3.1. F or any ǫ ∈ (0 , 1] , algorithm Bounded- UFP ( ǫ 6 ) r eturns a fe asible ( (1+ ǫ ) e e − 1 ) -appr oximate solution for the Ω( ln m ǫ 2 ) -b ounde d unsplittable flow pr oblem, runs i n p olynomial-time, and i s m onotone and exact w.r.t. the de- mand and value of every r e quest. Cor ollar y 3.2. F or al l values ǫ ∈ (0 , 1] , ther e exists a p ol ynomial-time truthful ( (1+ ǫ ) e e − 1 ) -appr oximation me ch- anism for the Ω(ln m ) -b ounde d unsplittable flow pr oblem, wher e ever y r e quest’s demand and v alue is unknown. W e b egin by in trod ucing a notation that ease the analysis presentatio n: • Let x i s , y i e , and z i r b e the resp ective v alues of the v ari- ables x s , y e , and z r at the end of t h e i -th iteration of the a lgorithm, where i ≥ 0. Mind that we reg ard the end of iteration 0 as th e b eginning of th e algorithm. Additionally , w e let ( y i , z i ) denote the set of d u al vari - ables at the end of the i -th iteration. • Let P ( i ) = P r ∈R v r · ( P s ∈ S r x i s ) be the v alue of the primal solution at the end of the i -th iteration, and let P be the v alue of the primal solution when the algo- rithm termi nates. N otice th at P is the sum of v alues of requests selected to be allocated by the algorithm, i.e. t h e outcome of the alg orithm. In addition, we let ∆ P ( i ) = P ( i ) − P ( i − 1) b e t h e v alue in which the primal solution i s incremented in t he i -th iteration. • Let D 1 ( i ) = P e ∈ E c e y i e and D 2 ( i ) = P r ∈R z i r b e t h e respective va lues of the first and second parts of the dual solution a t the end o f the i -th iteration, and l et D ( i ) = D 1 ( i ) + D 2 ( i ). Also, let D den ote th e v alue of the optimal solution f or the du al linear program. • Let α ( i ) d enote the normalized length of the path se- lected after the en d of th e i -th iteration. Note that if path p is selected in the ( i + 1)-th iteration then α ( i ) = d p v p | p | = d p v p P e ∈ p y i e . Correctness and T ruthfulness. The follo wing lemmas establish the feasibil ity of the solution, and the monotonicit y and exactn ess of th e algorithm. Lemma 3.3. Algorithm Bounded-UFP ( ǫ ) outputs a f e asi- ble solution. Pr oof. Assume b y con tradiction that the output of the algorithm is n ot feasible. Let ¯ p b e the fi rst path that induces a violation in the capacity of ed ge e in th e ℓ -th iteration, an d let P b e the family of paths selected before the ℓ -th iteration, whic h consist of e . Since ¯ p indu ces a capacit y v iolation then P p ∈P d p + d ¯ p > c e . Clearly , since d ¯ p ∈ (0 , 1] it follo ws that P p ∈P d p > c e − 1. Consequently , we get that c e y ℓ − 1 e = c e y 0 e Y p ∈P e ǫBd p c e = e ǫB c e P p ∈P d p > e ǫB c e − 1 c e ≥ e ǫB B − 1 B = e ǫ ( B − 1) , where the last ineq u alit y results from th e fact that x − 1 x is an increasing monotonic function for all x ≥ 1, and since c e ≥ B ≥ 1. Insp ecting the main loop stopping condition, i.e. line 5 in the algorithm, it follo ws t h at the algorithm had to exit t h e lo op. This implies th at the algorithm could not hav e executed the ℓ - t h iteration and thus, could n ot h ave selected ¯ p , a contradiction. Lemma 3.4. Algorithm Bounded-U FP ( ǫ ) is monotone and exact w.r. t. to the demand and value of every r e quest. Pr oof. Consider a request r selected to b e routed using path p r in the ℓ -th iteration of the alg orithm, which has a respective demand and v alue of d r and v r . No w, supp ose that r had a demand of ˜ d r ≤ d r , a v alue of ˜ v r ≥ v r , and the demands and v alues of all the other requests were fixed. F or t h e sak e of monotonicity , w e n eed to prov e that the al- gorithm w ould ha ve selected r in the latter case, i.e. when its demand and v alue were ˜ d r and ˜ v r , respectively . I f r is selected by th e algorithm in th e first ℓ − 1 iterations then we are done. Otherwise, lets consider the ℓ -th iteration. One can easily observe th at in the first ℓ − 1 iterations of the algorithm, th e same set of requests is sel ected to be routed using the same se t of paths whether the demand and v alue of r is ( d r , v r ) or ( ˜ d r , ˜ v r ). Resp ectively , the same set of un- selected requ ests remain. Note that ˜ d r ˜ v r ≤ d r v r . Hence, since the path p r minimizes d p v p P e ∈ p y e o ver an y path p , whic h corresponds to an unselected req uest, when the demand and v alue of r is ( d r , v r ), so it do es when the d emand and v alue of r is ( ˜ d r , ˜ v r ). This implies t h at r m ust b e selected b y th e algorithm in the ℓ - th iteration. The ex actn ess of the algorithm is clear, as the algorithm ma y route the exact demand of e very requ est selected, and ma y n ot route anything otherwise. Appro ximation. W e now turn to pro ve that the algorithm yields an approximatio n ratio that app roaches e e − 1 . W e b e- gin by stating th ree claims, which will b e u tilized later. Claim 3.5. An i ncr e asing se quenc e { α 0 , α 1 , . . . , α t +1 , α } satisfies P t i =0 ` α i +1 − α i α − α i ´ ≤ ln ` α − α 0 α − α t +1 ´ . Pr oof. F or every 0 ≤ i ≤ t , α i +1 − α i α − α i ≤ ln “ α − α i α − α i +1 ” = ln( α − α i ) − ln( α − α i +1 ) , where the inequalit y follo ws from ln(1 + x ) ≤ x b y substi- tuting x = α i − α i +1 α − α i . A ccordingly , this implies that t X i =0 “ α i +1 − α i α − α i ” ≤ t X i =0 ` ln( α − α i ) − ln( α − α i +1 ) ´ = ln( α − α 0 ) − ln( α − α t +1 ) = ln “ α − α 0 α − α t +1 ” . Claim 3.6. α ( i ) ≤ D 1 ( i ) D − D 2 ( i ) , in eve ry iter ation i ≥ 0 . Pr oof. Consider the ( i + 1)- th iteration. Let p denote the path th at is selected in this iteration. The path p cor- respond s to an un selected request such that d p v p P e ∈ p y i e is minimal. Namely , eve ry other path p ′ , which corresp on d s to an oth er u nselected request, satisfies d p ′ v p ′ X e ∈ p ′ y i e ≥ d p v p X e ∈ p y i e = α ( i ), thus d p ′ X e ∈ p ′ y i e α ( i ) ≥ v p ′ . This implies that if w e multiply y i e by α ( i ) − 1 , for every e ∈ E , then all th e d ual linear program constraints b ecome satisfied. Consequently , the set of v ariables ( y i α ( i ) − 1 , z i ) constitutes a feasible fractional solution to the d ual linear program and t herefore, D ≤ D 1 ( i ) α ( i ) − 1 + D 2 ( i ). Claim 3.7. D 1 ( i + 1) ≤ D 1 ( i ) + B ǫ (1 + ǫ ) · ∆ P ( i + 1) · α ( i ) , for every i ≥ 0 . Pr oof. Consider the ( i + 1)- th iteration. Let p denote the path that is selected in this iteration, and let d p and v p denote its respective demand and v alue. Insp ecting the algorithm, one can d erive that X e ∈ E c e y i +1 e = X e ∈ E e / ∈ p c e y i e + X e ∈ p c e y i e · e ǫBd p c e ≤ X e ∈ E e / ∈ p c e y i e + X e ∈ p c e y i e „ 1 + ǫB d p c e + “ ǫB d p c e ” 2 « ≤ X e ∈ E c e y i e + B ǫ (1 + ǫ ) d p X e ∈ p y i e = X e ∈ E c e y i e + B ǫ (1 + ǫ ) · ∆ P ( i + 1) · α ( i ) . The first inequality is du e to th e fact that e a ≤ 1 + a + a 2 for any a ∈ [0 , 1], and the fact that ǫBd p c e ∈ (0 , 1]. The second inequality holds since c e · „ ǫB d p c e + “ ǫB d p c e ” 2 « ≤ ǫB d p + ǫ 2 B d p = B ǫ (1 + ǫ ) d p , (1) where the inequality in (1) follo ws from the observ ations that d 2 p ≤ d p , and B c e ≤ 1. Finally , the last equality fol- lo ws from the definition of α ( i ), which ca n be rewritten as d p P e ∈ p y i e = v p α ( i ), and the observ ation th at v p is th e v alue in which the primal solution is incremented in the ( i + 1)-th iteration. Recalling that D 1 ( i ) = P e ∈ E c e y i e completes the proof. W e are n o w ready to establish the appro ximation guarantee of the algorithm. Lemma 3.8. Algorithm Boun ded-UFP ( ǫ ) r eturns an ( (1+ 6 ǫ ) e e − 1 ) -appr oximate solution for the ln m ǫ 2 -b ounde d unsplit- table flow pr oblem, for any ǫ ∈ (0 , 1 6 ] . Pr oof. One can easily notice, by insp ecting t he stoping condition of the main lo op, that when the algorithm termi- nates, ei ther L = ∅ o r P e ∈ E c e y e > e ǫ ( B − 1) . If L = ∅ then it follow s that the algorithm succeeded to satisfy all th e re- quests and thus, its outp u t is opt imal. Consequently , in the remainder of the proof, we shall assume that P e ∈ E c e y e > e ǫ ( B − 1) . F or every i ≥ 0, D 1 ( i + 1) ≤ D 1 ( i ) + B ǫ (1 + ǫ ) · ∆ P ( i + 1) · α ( i ) ≤ D 1 ( i ) + B ǫ (1 + ǫ ) · ∆ P ( i + 1) · D 1 ( i ) D − D 2 ( i ) = D 1 ( i ) “ 1 + B ǫ ( 1 + ǫ ) ∆ P ( i + 1) D − D 2 ( i ) ” ≤ D 1 ( i ) e ` Bǫ (1+ ǫ ) ∆ P ( i +1) D − D 2 ( i ) ´ , where t h e first and second inequ alities follo w from Claim 3.7 and Claim 3.6, resp ectively , and the last inequalit y is due to the fact th at 1 + a ≤ e a . This implies that D 1 ( i + 1) ≤ D 1 (0) e ` Bǫ (1+ ǫ ) P i j =0 ∆ P ( j + 1) D − D 2 ( j ) ´ ≤ e ` Bǫ 2 + B ǫ (1+ ǫ ) P i j =0 ∆ P ( j +1) D − D 2 ( j ) ´ , where th e first ineq ualit y results from the exp ansion of th e recursion, and the second one follo ws from D 1 (0) ≤ e Bǫ 2 , whic h is obtained by noticing t hat D 1 (0) = P e ∈ E c e y 0 e = m , and recalling that B ≥ ln m ǫ 2 by definition. Lets assume th at the algorithm terminates after t + 1 iterations. A ccordingly , using our p rior assumption that P e ∈ E c e y e > e ǫ ( B − 1) , we get th at e ǫ ( B − 1) < D 1 ( t + 1) ≤ e ` Bǫ 2 + B ǫ (1+ ǫ ) P t j =0 ∆ P ( j + 1) D − D 2 ( j ) ´ . One can v alidate that D 2 ( j ) = P ( j ) by insp ecting the v ari- ables alterations in line 12 of th e algorithm, and th eir af- fect on D 2 ( j ) and P ( j ). Hen ce, w e derive th at ∆ P ( j +1) D − D 2 ( j ) = P ( j +1) − P ( j ) D − P ( j ) . Consequ ently , w e can apply Claim 3.5, while recalling th at P (0) = 0 an d P ( t + 1) = P , and yield ǫ ( B − 1) < B ǫ 2 + B ǫ (1 + ǫ ) ln ` D D − P ´ . Because 1 − 2 ǫ 1+ ǫ ≤ ǫ ( B − 1) − B ǫ 2 Bǫ (1+ ǫ ) , and since 1 − 3 ǫ ≤ 1 − 2 ǫ 1+ ǫ for any positive ǫ , we attain 1 − 3 ǫ ≤ ln ` D D − P ´ . This can b e simplified further to giv e D P ≤ 1 e (1 − 3 ǫ ) − 1 + 1 ≤ (1+6 ǫ ) e e − 1 . Recall that D is the v alue of the opt imal solution for the dual linear program and thus, using the we ak LP duality completes the p roof. Proof of The orem 3.1. The correctness of the algorithm is due to Lemma 3.3 , the approximation guarantee is estab- lished in Lemma 3.8, and the monotonicity and exactness are presented in Lemma 3.4. Finally , it is clear th at t he running t ime of the algorithm is p olynomial, and in fact, if w e denote the number of requests by |R| , one can easily v alidate t h at the num b er of iterations is b ounded by |R| , and ev ery iteration ta kes time proportional to |R| shortest path compu tations. 3.3 Inappr oximability result In the follo wing, we introduce tw o input instances for the problem u nder consideration that lo w er b ound the p erfor- mance guarantee of any algorithm, which is p art of the rea- sonable iterative path minimizing algorithms family . Sp ecif- ically , the first input instance prov es that any such algo- rithm cannot yield an approximation guarantee b etter th an e e − 1 − o (1). This demonstrates that the analysis of algorithm Bounded-UFP is tight, an d that it is the “best” algorithm in the aforemen tioned f amily of algorithms. The second input instance establishes a low er b ound of 4 3 on t he appro xima- tion ratio of any such algorithm for this problem in its ut- most generality , i.e. when the underlying graph is un directed and th e minimal edge capacity is arbitrarily large. In partic- ular, th is suggests th at even if we ease t h e problem setting, e.g. assume that the minimal capacity of an edge is Ω( m ) instead of Ω(ln m ), no algorithm in the aforesaid family can ac hieve PT AS . Prior to describing t he finer details of our approach, we introduce the notion of a reasonable function, which is a key ingredient in the defi nition of a reasonable iterative p ath minimizing algorithm. Note that reasonable fun ct ions have a similar fla vor to the min functions introduced by Archer and T ardos [3]. Nevertheless, they are stil l quite different. Let S = S r ∈R { p : p is a simple path b etw een s r and t r } . Definition 3.9. L et g : S → R b e a function, which as- signs an arbitr ary priority to every p ath. Such a function is c al l e d reasonable if under t he assumption that the c ap ac- ities of al l the e dges ar e i dentic al, a nd b oth the demand and value of every r e quest ar e unit, it fol lows that g ( q ) ≤ g ( q ′ ) for any valid unsplittable flow, and any two p aths q , q ′ ∈ S that satisfy • q c onsists of k e dges, q ′ c onsists of k ′ e dges, and k ≤ k ′ . • f i ≤ f ′ i , for every 1 ≤ i ≤ k , w her e ( f 1 , f 2 , . . . , f k ) and ( f ′ 1 , f ′ 2 , . . . , f ′ k ′ ) ar e non-incr e asing ve ctors, whi ch indic ate the flow r oute d thr ough the e dges of q and q ′ with r esp e ct to the valid unsplittable flow. Definition 3.10. An algor ithm is r eferr e d to as reason- able iterative path minimizing algorithm , if i t iter atively se- le cts a p ath that minim izes a r e asonable function over al l the p aths tha t c orr esp ond to unsele cte d r e quests. One can verify that algorithm Bound ed-UFP minimizes the function h ( p ) = d p v p P e ∈ p 1 c e e ǫBf e c e , where f e denotes the flow routed through edge e . This function is reasonable since when w e assume that b oth the demand and v alue of every request are u nit, and the capacities of all the edges are iden- tical, say B , then it reduces to ˜ h ( p ) = 1 B P e ∈ p e ǫf e , which clearly satisfies ˜ h ( q ) ≤ ˜ h ( q ′ ), for any tw o p aths q an d q ′ that meet the properties ind icated in Definition 3.9. Con- sequently , a lgorithm Bounded-UFP is a reasonable iterative path minimizing algorithm. W e n ote th at reasonabilit y cap- tures a broad class of functions. F or example, th e reasonable function h 1 ( p ) = ln(1 + | p | ) · h ( p ) is similar to the func- tion used by algorithm Bounded- UFP but it is mildly biased to wa rds paths with less edges. A nother example of a rea- sonable function is h 2 ( p ) = d p v p Q e ∈ p f e c e although it is not clear why any one wo uld lik e to use it. W e are now ready to establish the main result of th is subsection. Theorem 3.11. The appr oxim ation r atio of any r e ason- able i ter ative p ath m inimizing algorithm for the uns plittable flow pr oblem when the gr aph is dir e cte d c annot b e b etter than e e − 1 − o (1) , for B = o ( m 1 / 2 ) . ... ... t v ℓ v 3 v 2 v 1 s 1 s 2 s ℓ Figure 2: A directed graph i n which every vertex s i has a directed edge to every vertex v j suc h that j ≥ i . Additional ly , the capacitie s of all the edges are identical and equal to B . Pr oof. Sup p ose we are giv en the directed graph G = ( V , E ) schematically described in Figure 2, and the set of requests is R = { ( s 1 , t , 1 , 1) | {z } B requests , ( s 2 , t , 1 , 1) | {z } B requests , . . . , ( s ℓ , t , 1 , 1) | {z } B requests } . In order to simplify th e presentation an d analysis of t h e lo w er b ound instance, we in trod uce the follo wing assump- tion, whic h will b e tackled later. W e assume that when there is mor e than one path , which minimi zes the v alue of the reasonable function used by the iterativ e path minimiz- ing algorithm, th e algorithm selects one of th em arbitrarily . Accordingly , we premise that it selects a path ( s i , v j , t ) in whic h i is minimal , and j is maximal with respect to all the minimizing paths that their source vertex is s i . F or ex- ample, in the initial B iterations of the algorithm, all the requests that th eir terminal v ertices are ( s 1 , t ) are satisfied using paths that use vertices v j such that j = ℓ, . . . , ℓ − B + 1. In th e subsequent B iterations, all t he req uests th at th eir terminal vertices are ( s 2 , t ) are satisfied using paths th at use vertices v j such th at j = ℓ − B , . . . , ℓ − 2 B + 1, a nd so on. Simulati ng the ex ecution of a reasonable iterativ e path min- imizing algori thm, while ignoring in tegralit y issues that will b e resolv ed later, we get th at • F or an y integer 1 ≤ q ≤ B , at the end of th e fi rst ℓ P q r =1 ( B B + 1 ) r iterations, all and only the requests, whose terminal vertices are ( s i , t ) such that i ≤ ℓ · (1 − ( B B + 1 ) q ), are satisfied, and all the ( v j , t ) edges such that j > ℓ · (1 − ( B B + 1 ) q ) have a flow load of q o r equiv alen tly , a residual capacity of B − q . • After ℓ P B r =1 ( B B + 1 ) r iterations, the algori thm cannot route more requ ests and thus, it stops 2 . 2 An algorithm migh t stop even so oner, e.g. algorithm Bounded-UFP stops after the while condition fails. Ho w- ever, analyzing th e case that th e algorithm stops when it cannot route more req uests just affirms the low er b oun d . Consequently , since all and only the requests, whose ter- minal vertices are ( s i , t ) such that i ≤ ℓ · (1 − ( B B + 1 ) B ), are satisfied when the algorithm stops, it follo ws that the v alue of the solution that the al gorithm outputs is a t mo st B ℓ · (1 − ( B B + 1 ) B ) = B ℓ · (1 − (1 − 1 B + 1 ) B ) ≤ B ℓ · (1 − 1 e ). On the other hand, an opt imal solution clearly has a v alue of B ℓ , e.g. route ev ery requ est of th e form ( s i , t , 1 , 1) through the directed path ( s i , v i , t ) . Thus, we get t hat the approxi- mation ratio of the algorithm cann ot b e b etter than e e − 1 . W e no w d rop the i ntegrali ty assumption. Namely , in the above analysis, we hav e assumed that ℓ P q r =1 ( B B + 1 ) r is inte- gral, for any integer q . This clearly may not be true. How- ever, one can resolve t his issue by apply ing a more care- ful analysis, and yield t hat only the requ ests, whose ter- minal vertices are ( s i , t ) such that i ≤ ℓ · (1 − ( B B + 1 ) q ) + P q − 1 k =0 ( B B + 1 ) k , may b ecome satisfied. S in ce P B − 1 k =0 ( B B + 1 ) k ≤ B , it follo ws that t h e v alue of the solution that the algorithm ac hieves mi ght increase by no more than B 2 , in res p ect to B ℓ · (1 − 1 e ). S in ce the num ber of edges in the graph is m = ℓ + P ℓ k =1 k ≤ 2 ℓ 2 , and B = o ( m 1 / 2 ), we obtain that B = o ( ℓ ). Consequently , the analysis of t h e low er b ound de- grades b y at most o (1), i.e. the approximation ratio of any algorithm cannot b e b etter than e e − 1 − o (1). Next, w e tackle the d ecisions assumption. Sp ecifically , we hav e assumed that th e decision of any algorithm b etw een same valued minimizing path s is arbitrary and hen ce, one ma y ask if a sp ecific t ie-b reaking rule can lead to b etter results. W e can resolve this matter by constructing a similar input in stance, w hich forces an y algorithm to make similar “bad” decisions. Essentially , one wa y to achiev e it is to replace every ( s i , v j ) edge by a directed path with iℓ + 1 − j edges. The reason that an algorithm makes “bad” decisions on this in stance dues to the reasonabilit y property , i.e. any reasonable algorithm “prefers” paths with less edges. Note that this instance supp orts the same lo wer bound , but has a so mewhat stricter constraint on the v alue of B , i. e. since m = O ( ℓ 4 ), B needs to satisfy B = o ( m 1 / 4 ). The next theorem demonstrates th at even if w e ea se the problem setting, no reasonable iterative path minimizing al- gorithm can achiev e PT AS. Theorem 3.12. The appr oxim ation r atio of any r e ason- able i ter ative p ath m inimizing algorithm for the unsplittable flow pr oblem c annot b e b etter than 4 3 , for any B, and even when the gr aph is undir e cte d. v 3 v 6 v 5 v 4 v 7 v 2 v 1 Figure 3: An undirected graph in whi c h the capaci- ties of all t he edges are iden tically equal to B . Pr oof. Sup p ose we are given the undirected graph G = ( V , E ) schematically described in Figure 3, and the set of requests is R = { ( v 1 , v 3 , 1 , 1) | {z } B requests , ( v 4 , v 6 , 1 , 1) | {z } B requests , ( v 1 , v 6 , 1 , 1) | {z } B requests , ( v 3 , v 4 , 1 , 1) | {z } B requests } . Clearly , an op t imal solution for th is instance has a v alue of 4 B , e.g. route every request of the form ( v 1 , v 3 , 1 , 1) th rough the p ath ( v 1 , v 2 , v 3 ), an y requ est of the form ( v 4 , v 6 , 1 , 1) through the path ( v 4 , v 5 , v 6 ), all the requests of the form ( v 1 , v 6 , 1 , 1) through the path ( v 1 , v 7 , v 6 ), and every request of the form ( v 3 , v 4 , 1 , 1) th rough th e path ( v 3 , v 7 , v 4 ). Simulati ng the execution of a reasonable iterative path minimizing algo rithm in the initial fo ur iterations, one can easily v alidate that the algorithm m ay select th e four p aths ( v 1 , v 7 , v 3 ),( v 4 , v 7 , v 6 ), ( v 1 , v 2 , v 3 ), and ( v 4 , v 5 , v 6 ) since eac h one of these paths is one of the min imizing paths in the correspondin g iteration, and by that satisfy tw o ( v 1 , v 3 , 1 , 1) requests and tw o ( v 4 , v 6 , 1 , 1) requ ests. In addition, notice that at the end of this four iterations phase, every edge has a residual capacity of B − 1. Arguments similar to those used in this initial four iterations phase can b e applied in another B 2 − 1 p hases, eac h of four iterations, to demonstrate that t he algorithm acts exactly the same. Consequently , after B 2 phases, every edge has a residual capacit y of B 2 , all the ( v 1 , v 3 , 1 , 1) requests and the ( v 4 , v 6 , 1 , 1) requests were satisfied, and t he remaining requ ests are ¯ R = { ( v 1 , v 6 , 1 , 1) | {z } B requests , ( v 3 , v 4 , 1 , 1) | {z } B requests } . In this current state, any algo rithm can satisfy at most B requests from ¯ R . This is the result of th e fact that any path from v 1 to v 6 and an y path from v 3 to v 4 must use either edge ( v 1 , v 7 ) or edge ( v 3 , v 7 ), an d the fact that the t otal residual capacit y of these edges sums to B . Thus, the solution that the algorithm outp uts has v alue of at most 3 B . Cor ollar y 3.13. No r e asonable i ter ative p ath minimiz- ing algorithm for the unsplittable flow pr oblem c an yield a PT AS. 4. SINGLE-MINDED MUL TI-UNIT COMBINA TORIAL A UCTION 4.1 The algorithm In this su bsection, we design a det erministic monotone algorithm for the Ω(ln m )-b ounded multi-unit combinato- rial auction problem, whose appro ximation ratio approaches e e − 1 . W e b egin by demonstrating th at the single-minded multi-unit com binatorial auction problem can b e form ulated as a simplified sp ecial ca se of the integer linear p rogram o f the unsplittable flow problem, a nd then we turn to s p ecial- ize algorithm Bound ed-UFP for the problem under consider- ation. The single-minded multi-unit com binatorial auction prob- lem can b e form ulated as a sp ecial case of the integ er linear program of the unsplittable flow problem by letting S r to denote the singleton set of U r , i.e. S r = { U r } , and rep lacing e , E and d s in the integer linear program of the un sp lit- table fl o w problem with u , U and 1, resp ectively . Similarly , the relaxation of the integer linear program of the single- minded multi-unit combinatorial auction problem, and its dual can also b e form ulated as sp ecial cases of the corre- sp on d ing linear programs. Consequently , the primal-dual algorithm Bound ed-MUCA , formally describ ed b elow , is a sp ecialized version of algorithm Bounded -UFP , in which the path selection pro cedure, i.e. lines 6-8 in algorithm Bound ed- UFP , w as neglected, and th e d emand terms were omitted. Algorithm 2 Bounded-MUCA ( ǫ ) Input: An accuracy parameter ǫ ∈ (0 , 1] Output: A set W of requests to b e satisfied 1: Let L b e a list of all th e requests, and let W b e an empty set 2: for all u ∈ U do y u = 1 c u end for 3: while ` L 6 = ∅ and P u ∈ U c u y u ≤ e ǫ ( B − 1) ´ do 4: Let ˆ r be the request, whic h minimizes 1 v r P u ∈ U r y u with resp ect to every r ∈ L 5: for all u ∈ U ˆ r do y u = y u · e ǫB/c u end for 6: Add ˆ r to W , and remove ˆ r from L 7: end while 8: return W Theorem 4.1. The algorithm Bounded- MUCA ( ǫ 6 ) r eturns a f e asible ( (1+ ǫ ) e e − 1 ) -appr oximate solution f or the Ω( ln m ǫ 2 ) - b ounde d multi-unit c ombinatorial auction pr oblem, for any ǫ ∈ (0 , 1] , runs in p olynomial-time, and i s monotone and exact w.r. t. the value of e ach r e quest. Pr oof. Since algorithm Boun ded-MUCA is a simplified versi on of algo rithm Bounded-UFP , the analysis of Theo- rem 3.1 also app lies in this case. It is w orth noting that th e algorithm can even b e em- plo yed to a generalized version of the problem in which th e demand of every request, i.e. the desired bundle of items, is part of the type of th e request and t herefore, agents may b e d ishonest about it. Note that in this case, monotonic- it y can b e easily established by arguments similar to th ose used in Theorem 3.4, and the additional observ ation that P u ∈ ˜ U r y u ≤ P u ∈ U r y u , for any ˜ U r ⊆ U r . Remark that this setting is referred to as the unknown single-mind ed case [14]. Cor ollar y 4.2. F or al l values ǫ ∈ (0 , 1] , ther e exists a p olynomial-time truthful ( (1+ ǫ ) e e − 1 ) -appr oximation me cha- nism for the Ω(ln m ) -b ounde d multi-unit c ombinatorial auc- tion pr oblem among unknown single-minde d agents. 4.2 Inappr oximability result W e demonstrate that any reasonable iterative bundle min- imizing algorithm cannot achiev e an appro ximation ratio b etter than 4 3 . Essentia lly , this suggests that no algorithm in the aforesaid family can achiev e PT AS. W e start by formally defining the notion of a reasonable iterativ e bu ndle minimizing algorithm. W e remark that th e follo wing definitions are just a refin ement of the definitions made for the un splittable flow problem. Let S = S r ∈R { U r } . Definition 4.3. L et g : S → R b e a function, which as- signs an arbitr ary priority to every bund l e. Such a function is c al le d reasonable if under the assumption that the multi- plicities of al l the items ar e identic al, and the value of every r e quest i s uni t, i t fol lows that g ( T ) ≤ g ( T ′ ) for any valid multi-unit al lo c ation 3 , and any two bund les T , T ′ ∈ S that satisfy 3 A valid mul ti-unit al lo c ation can b e succinctly describ ed as an allocation of non-identical items to requ ests suc h that the number of allocated copies of every item do es not exceed its multiplicit y . • T c onsists of k items, T ′ c onsists of k ′ items, and k ≤ k ′ . • f i ≤ f ′ i , for every 1 ≤ i ≤ k , wher e ( f 1 , f 2 , . . . , f k ) and ( f ′ 1 , f ′ 2 , . . . , f ′ k ′ ) ar e non-incr e asing ve ctors, which indic ate the numb er of al lo c ate d c opies of the items of T and T ′ with r esp e ct to the vali d multi-unit al lo c ation. Definition 4.4. An al gorithm is r eferr e d to as reason- able iterative b undle minimizing algorithm , if it iter atively sele cts a bund l e that minim izes a r e asonable function over al l the bund les that c orr esp ond to unsele cte d r e quests. Note that algorithm Bounded-MUCA minimizes the func- tion h ( s ) = 1 v s P u ∈ s 1 c u e ǫBf u c u , where f u denotes the number of allocated copies of item u . One can easily argue th at th is function is reasonable and thus, algorithm Bounded-MUCA is a reasonable iterative bun d le minimizing algorithm. W e are now ready to prove t h e core result of this sub section. Theorem 4.5. The appr oxim ation r atio of any r e ason- able iter ative bund le minimi zing algorithm for the single- minde d multi-unit c ombi natorial auction pr oblem c annot b e b etter than 4 3 . Pr oof. Let m b e a multiple of p · ( p + 1), where p ≥ 3 is a constant od d integ er. S u pp ose we are given a set U of m items such that the multiplicities of all the items are identical and equ al to B , and let S p i =1 S p +1 j =1 U i,j b e a partition of U into p · ( p + 1) disjoin t sets, each consists of m p · ( p +1) items. Ad ditionally , sup p ose that R consists of u nit v alue requests of tw o typ es: 1. B 2 requests that consist of the items U ℓ = S p +1 j =1 U ℓ,j , for every ℓ = 1 , . . . , p . 2. B 2 requests that consist of the items U 1 , 2 ℓ − 1 ∪ U 1 , 2 ℓ ∪ S p i =2 U i, 2 ℓ − 1 , for every ℓ = 1 , . . . , p +1 2 , and B 2 requests that consist of the items U 1 , 2 ℓ − 1 ∪ U 1 , 2 ℓ ∪ S p i =2 U i, 2 ℓ , for every ℓ = 1 , . . . , p +1 2 . Figure 4 sc hematically describ es a concrete input instance. One can verify that the an optimal solution for this in- stance has a v alue of pB , for example by selecting all the requests except for the B 2 requests that consist of U 1 . Simulati ng the execution of a reasonable iterative bu n- dle minimizing algorithm, one can easily v alidate that t h e algorithm ma y incrementally select all the req uests of the first typ e, e.g. it may rep eatedly select a request that con- sists of U 1 , then a req uest that consists of U 2 and so on until U p . Consequently , after B 2 phases, each of p steps, all th e requests of the first typ e are satisfied, the va lue of the current solution is p 2 B , and every item h as a residual multipli city of B 2 . Notice that U 1 consists of m p items, and any request of th e second type consists of 2 m p · ( p +1) items of U 1 . Hence, by simple counting arguments it follo ws th at in the current state, any algorithm cannot satisfy more than ( B 2 · m p ) / 2 m p · ( p +1) = p +1 4 B requests of t he second type. There- fore, we obtain that the va lue of the solution t hat any rea- sonable iterative bun dle minimizing algorithm outpu ts is no more th an 3 p +1 4 B and thus, as p tends to infinity , the inap- proximabil ity ratio approac hes 4 3 . Cor ollar y 4.6. No r e asonable iter ative bund l e minimiz- ing algorithm for the single-minde d multi-unit c ombinatorial auction pr oblem yields a PT AS. 0 1 0 0 0 0 0 1 1 1 1 1 00 00 00 00 00 11 11 11 11 11 0 0 0 0 0 1 1 1 1 1 0 0 0 1 1 1 0 1 0 1 0 0 0 1 1 1 0 1 0 0 0 0 1 1 1 1 00 00 00 00 11 11 11 11 0 0 1 1 00 11 0 0 1 1 00 11 U 2 , 3 U 1 , 2 U 1 , 3 U 1 , 4 U 2 , 1 U 2 , 2 U 1 , 1 U 2 , 4 U 3 , 1 U 3 , 2 U 3 , 3 U 3 , 4 Figure 4: The i nput instance i n the case of p = 3 , and m = 12 . Note that the set of item s S 3 i =1 S 4 j =1 U i,j are represented by the black dots on the le ft of the figure, and every collection of B 2 requests is repre- sented by a vertical group of rectangles s uch that each rectangle consists of the s et of items, whose representing dots are in the left-pro jection zone of the rectangle. Also note that the first type of re- quests are located l eft of the dotted line, whereas the se cond type of reque sts app ear on i ts right. 5. UNSPLITT ABLE FLO W WITH REPETITIONS PR OBLEM In this section, w e study the Ω(ln m )- b ounded unsplit- table flow with rep etitions problem. This problem is a v ari- ant of the corresp onding u n splittable flow problem in which w e are allo w ed to satisfy every req uest multiple times using p ossibly multiple paths, and th e profit gained is prop or- tional to the num b er of times that every request is satisfied. In sharp contrast with our prior results, we d emonstrate that this version admits a deterministic primal-dual based algorithm, which yields an ( 1 + ǫ )-app ro ximation. 5.1 The algorithm In the fo llo wing, w e contrive an ( 1 + ǫ )-approximation algorithm, named Bound ed-UFP-Rep eat , for the Ω(ln m )- b ounded unsplittable flow with rep etitions problem, which is based on a primal-dual approach. The follo wing theorem digests the p roperties of th e algorithm. Theorem 5.1. Algorithm Bounded-UFP- Rep eat ( ǫ 6 ) i s an (1 + ǫ ) -appr oximation for the Ω( ln m ǫ 2 ) -b ounde d unsplittable flow with r ep etitions pr oblem, for any ǫ ∈ (0 , 1] , with running time p olynomial in m and max e { c e } min r { d r } . In Figure 5, we present the p rimal-dual formulation of the underlying problem. W e now t urn to analyze algorithm Boun ded-UFP-R ep eat . F or th e sake of simplicit y , we shall u se th e same notation, whic h was introd uced in Subsection 3.1, with one ex cep tion. Namely , since there are no z -typ e v ariables in the dual linear program, we let D ( i ) = P e ∈ E c e y i e denote the va lue of the dual solution at the end of the i -th iteration, and neglect D 1 ( i ) and D 2 ( i ). Notice th at Lemma 3.3 is applicable also in this case and thus, the correctness of the algorithm follow s. Consequently , in the sequel, w e prov e that the algorithm under consideration achiev es an approximation ratio of (1 + Algorithm 3 Bounded- UFP-Rep eat ( ǫ ) Input: An accuracy p arameter ǫ ∈ (0 , 1] Output: A (request, path) pairs multiset W , whic h holds the requ ests to b e allocated 1: Let L b e a list of all th e requests, and let W b e an empty multis et 2: for a l l e ∈ E do y e = 1 c e end for 3: while ` P e ∈ E c e y e ≤ e ǫ ( B − 1) ´ do 4: for e very r ∈ L do 5: Let p r b e the shortest path b etw een s r and t r in G with resp ect to the weigh ts y e , and let | p r | = P e ∈ p r y e b e its length 6: end for 7: Let ˆ r b e t he request, which minimizes d r v r | p r | with respect to every r ∈ L 8: for all e ∈ p ˆ r do y e = y e · e ǫBd ˆ r /c e end for 9: Add ( ˆ r , p ˆ r ) to W 10: end while 11: return W max X r ∈R v r · “ X s ∈ S r x s ” s.t. X s ∈ S | e ∈ s x s d s ≤ c e ∀ e ∈ E x s ∈ N ∀ s ∈ S min X e ∈ E c e y e s.t. d r X e ∈ s y e ≥ v r ∀ r ∈ R , ∀ s ∈ S r y e ≥ 0 ∀ e ∈ E Figure 5: The integer line ar program of the unsplit- table flow with rep etitions problem (top), and the dual of its rel axation (b ottom). Note that S r denotes the se t of all the simple paths b etw een s r and t r in G , S = S r ∈R S r , and d s and v s denote the resp ective demand and v al ue of path s . ǫ ). W e b egin by establishing a analogous claim to Claim 3.6, whic h upp er b ounds α ( i ). Claim 5.2. α ( i ) ≤ D ( i ) D , in every iter ation i ≥ 0 . Pr oof. Consider the ( i + 1)-th iteration, and let p d enote the path, which is selected in this iteration. The path p corresponds to a req uest su c h that d p v p P e ∈ p y i e is minimal. Namely , every other path p ′ , which correspond s to a request, satisfies d p ′ v p ′ X e ∈ p ′ y i e ≥ d p v p X e ∈ p y i e = α ( i ), thus d p ′ X e ∈ p ′ y i e α ( i ) ≥ v p ′ . This implies that if w e multiply y i e by α ( i ) − 1 , for ev ery e ∈ E , th en all the dual linear program constraints b e- come satisfied, i.e. th e mo dified vari ables constitute a fea- sible fractional solution to th e dual linear program. Hence, D ≤ D ( i ) α ( i ) − 1 . Next, we prov e th at th e algorithm achiev es th e claimed (1 + ǫ )-approximatio n for t he problem un der consideration. Lemma 5.3. Bounded -UFP-Rep eat ( ǫ ) r eturns an (1 + 6 ǫ ) - appr oximate solution for the ln m ǫ 2 -b ounde d unsplittable flow with r ep etitions pr oblem, for any ǫ ∈ (0 , 1 6 ] . Pr oof. F or every i ≥ 0, one can d erive t hat D ( i + 1) ≤ D ( i ) + B ǫ (1 + ǫ ) · ∆ P ( i + 1) · α ( i ) ≤ D ( i ) + B ǫ (1 + ǫ ) · ∆ P ( i + 1) · D ( i ) D = D ( i ) “ 1 + B ǫ (1 + ǫ ) ∆ P ( i + 1) D ” ≤ D ( i ) e ` Bǫ (1+ ǫ ) ∆ P ( i +1) D ´ . The first inequality follo ws from Claim 3.7, while noticing that D ( i ) may rep lace D 1 ( i ). The second inequ alit y is d u e to Claim 5.2. Finally , t he last inequalit y results from th e fact that 1 + a ≤ e a . This implies that D 1 ( i + 1) ≤ D 1 (0) e ` Bǫ (1+ ǫ ) P i j =0 ∆ P ( j +1) D ´ ≤ e ` Bǫ 2 + B ǫ (1+ ǫ ) P i j =0 ∆ P ( j +1) D ´ , where th e first ineq ualit y results from the ex p ansion of th e recursion, and the second ineq u alit y follo ws from D 1 (0) ≤ e Bǫ 2 , whic h dues to D 1 (0) = m , and B ≥ ln m ǫ 2 . Lets assume that the algorithm terminates after t + 1 iterations. Accord- ingly , insp ecting t he stoping condition of th e main lo op, we attain t hat e ǫ ( B − 1) < D 1 ( t + 1) ≤ e ` Bǫ 2 + B ǫ (1+ ǫ ) P t j =0 ∆ P ( j +1) D ´ . This can b e simplified to ǫ ( B − 1) − B ǫ 2 Bǫ (1+ ǫ ) < P t j =0 ∆ P ( j +1) D . N o- tice that P t j =0 ∆ P ( j + 1) is a telescopic sum that is eq ual to P ( t + 1) − P (0) = P , where th e equality d ues to P ( t + 1) = P and P (0) = 0. In addition, notice that 1 − 3 ǫ ≤ ǫ ( B − 1) − B ǫ 2 Bǫ (1+ ǫ ) for any positive ǫ . Consequently , we obtain 1 − 3 ǫ ≤ P D . Sim- plifying this ex p ression even further yields D P ≤ 1 1 − 3 ǫ ≤ 1 + 6 ǫ , which by th e weak LP duality establishes the lemma. W e are now ready to prov e the main theorem of this sub- section. Proof of Theorem 5.1. As n oted b efore, the correctness of the algorithm directly follo ws from Lemma 3.3. I n addi- tion, the app ro ximation guarantee is prov ed in Lemma 5.3 . W e now turn to argue t h at the running time of the algo- rithm is p olynomial in m and c max d min , where c max = max e { c e } , and d min = min r { d r } . Consider some edge e ∈ E . R ecall that y 0 e = 1 c e and y t e ≤ 1 c e e ǫB , where t denotes the index of the last iteration of the algorithm. In ad d ition, notice that every time th at the algorithm increments y e , it is by a m ul- tiplicativ e factor of at least e ǫBd min /c max . Consequently , the num b er of iterations in which y e is incremented is at most c max d min . This implies that the run ning time of the algorithm is b ounded by m c max d min , as there are m edges. 6. REFERENCES [1] M . Andr e ws, J. Ch uzhoy , S . Khanna, and L. Zhang. Hardn ess of the undirect e d e dge-disjoint path s proble m with c ongestion. In Pro c e e dings 46th An nual IEEE Symp osium on F oundations of Computer Science , page s 226–244, 2005. [2] A. Archer, C. H. Papadimitriou, K. T alwar, and ´ E. T ardos. An approximate truthful mechanism f or combinatorial au ctions with single paramete r agents. In Pr oc ee dings 14th annual A CM-SIAM Symposium on Discr ete Algorithms , p ages 205–214, 2003. [3] A. Archer and ´ E. T ardos. F rugal path mechanisms. In Pr oc ee dings 13th annual ACM-SIAM Symposium on Discr ete A lgorithms , pages 991–999, 2002. [4] B. Aw erbuch, Y. Azar, and A. Meyerson. Reduc ing truth-tellin g onli n e mechanisms to on line optim ization. In Pr oc ee dings 35th Ann ual ACM Symp osium on Theory of Computing , page s 503–510, 2003. [5] Y. Azar an d O. Regev. Combinatorial algorithm s for the unsplittable flow prob lem. Algorithmic a , 44(1):49–66, 2006. [6] Y. Bartal, R. Gonen, an d N. Nisan . Incentive c om patible multi unit combinatorial auctions. In Pr o ce edings 9th Confer enc e on The or etic al Aspe cts of Rationali ty and Know ledge , pages 72–87, 2003. [7] P . Briest, P . Krysta, and B. V¨ ocking. Approximation techniques for util itarian mechanism design. In Pr o ce edings 37th A CM Sympos ium on Theory of Computing , pages 39–48, 2005. [8] L. Fleischer. Approximating fractional multicom mo dity fl ow indep e ndent of the n umbe r of com mo dities. In Pro ce edi ngs 40th Ann ual IEEE Symp osium on F oundations of C om puter Scienc e , pages 24–31, 1999. [9] N. Garg an d J. K¨ oneman n . F aste r and sim pler algorithm s for multicommo dity flow and other f ractional packing prob l ems. In Pr oc ee dings 39th Ann ual IEEE Sympo sium on F oundations of Computer Scienc e , page s 300–309, 1998. [10] V. Guruswami, S. Kh anna, R. Ra jaram an, F. B. Shephe rd, and M. Y annak akis. Near-optimal hardness results and approximation algorithms for edge-disjoint paths and related problems. In Pr o c e e dings 31th annual ACM symp osium on The ory of Computing , pages 19–28, 1999. [11] V. Guruswami and K. T alw ar. Hardness of low congestion routing in directe d graph s. Electr onic Col loquium on Computational Comple xity (ECCC) T echnic al Rep ort , TR06-141, 2006. [12] R. Lavi and C. Swam y . T ruthful an d near-optim al mechanism design via linear p rogramming. In Pr oc ee dings 46th Ann ual IEEE Symp osium on F oundations of Compute r Science , pages 595–604, 2005. [13] D. J. Le hmann, L. O’Callaghan, and Y. Shoh am. T ruth revelation in app roximately efficie nt combinatorial auc tions. Journal of the ACM , 49(5):577–602, 2002. [14] A. Mu’alem and N. Nisan. T ruthfu l app roximation mechanisms for restri c ted combinatorial auctions. In Pr o c e e dings 18th National Confer e nc e on Artificial Intel ligenc e , pages 379–384, 2002. [15] N. Nisan and A. Rone n. Algorit h mic mechanism design. In Pr oc ee dings 31th ACM Symp osium on The ory of Computing , pages 129–140, 1999. [16] P . Raghav an. Prob abilistic construc tion of d etermin istic algorithms: Approximating packing i nteger p rograms. Journal of Computer and System Sciences , 37(2):130–143, 1988. [17] P . Raghav an and C. D. Thompson. Random ized roundi n g: a technique for prov ably go o d algorithm s and algorith mic pro ofs. Combinatoric a , 7(4):365–374, 1987. [18] A. Sriniv asan. Im p rov ed approximation gu arantees for packing and c o vering i nteger p rograms. SIAM Journal on Computing , 29(2):648–670, 1999.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment