Securing U-Healthcare Sensor Networks using Public Key Based Scheme
Recent emergence of electronic culture uplifts healthcare facilities to a new era with the aid of wireless sensor network (WSN) technology. Due to the sensitiveness of medical data, austere privacy and security are inevitable for all parts of healthcare systems. However, the constantly evolving nature and constrained resources of sensors in WSN inflict unavailability of a lucid line of defense to ensure perfect security. In order to provide holistic security, protections must be incorporated in every component of healthcare sensor networks. This paper proposes an efficient security scheme for healthcare applications of WSN which uses the notion of public key cryptosystem. Our entire security scheme comprises basically of two parts; a key handshaking scheme based on simple linear operations and the derivation of decryption key by a receiver node for a particular sender in the network. Our architecture allows both base station to node or node to base station secure communications, and node-to-node secure communications. We consider both the issues of stringent security and network performance to propose our security scheme.
💡 Research Summary
The paper addresses the pressing need for robust security in pervasive healthcare systems that rely on wireless sensor networks (WSNs). Because medical data are highly sensitive, any compromise can have severe consequences, yet the limited computational power, memory, and energy of sensor nodes make traditional public‑key cryptography (PKC) impractical. To bridge this gap, the authors propose a lightweight, PKC‑inspired scheme that combines a novel key‑handshake protocol based on pseudo‑inverse matrices with a central key‑generation component located at the base station (BS).
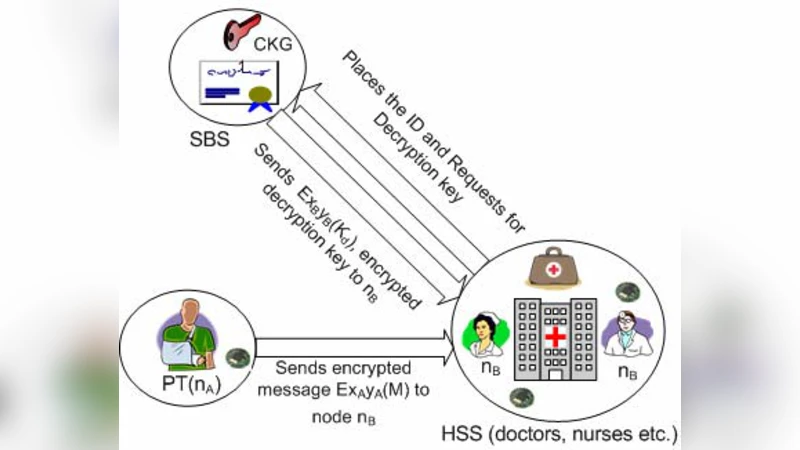
The network model consists of three entity types: patients (PT), healthcare service systems (HSS), and secure base stations (SBS). All SBSs are assumed to have ample power and connectivity, while PTs and HSSs are resource‑constrained sensors. The core of the handshake is the use of a pseudo‑inverse matrix A⁺ of a randomly generated matrix A. For an n×m matrix A, the pseudo‑inverse satisfies A·A⁺·A = A and A⁺·A·A⁺ = A⁺, allowing two parties to derive a common secret without expensive modular exponentiation.
The handshake proceeds as follows: (1) a sensor generates a random n×m matrix X and its pseudo‑inverse X⁺, then sends X·X⁺ to the nearest SBS; (2) the SBS generates its own m×k matrix Y and pseudo‑inverse Y⁺, computes XY·X⁺ and Y·Y⁺·X·Y·X⁺, and returns these to the sensor; (3) both sides perform a few additional linear multiplications, arriving at the identical matrix XY, which serves as the shared secret key. All operations are simple matrix multiplications and additions, making them feasible on 8‑bit microcontrollers.
After the shared key is established, a Central Key Generator (CKG) residing in the SBS manages encryption and decryption keys for all nodes. When node A wishes to send a message to node B, it encrypts the payload with a session key derived from its own shared key (XA·YA) and B’s shared key (XB·YB). The CKG supplies a decryption key (Kd) to B, which uses its own shared key to recover the original message. This architecture centralizes key management, simplifies revocation (the BS can invalidate a compromised node’s key and trigger a new handshake), and prevents intermediate nodes from learning decryption keys, thereby mitigating man‑in‑the‑middle attacks.
Performance evaluation uses the MICA2dot platform (ATmega128L MCU, 4 MHz, 128 KB flash, CC1000 radio). Energy costs are measured as 59.2 µJ per transmitted byte and 28.6 µJ per received byte. The complete handshake (two transmissions, one reception) consumes roughly 7.2 mJ, while a single node‑to‑node message exchange costs about 5.7 mJ. Compared with two other PKC‑based schemes—C4W and SSSL—the proposed method has higher communication energy but dramatically lower memory usage because it does not require pre‑stored public‑key parameters. The authors argue that the one‑time energy expense of the handshake is acceptable, as the derived key can be reused for the node’s entire lifetime unless compromised.
The paper also discusses limitations: the security strength of pseudo‑inverse matrices has not been formally proven to match that of conventional PKC; the base station remains a single point of failure; and the scheme does not address higher‑level authentication or access‑control policies required in real healthcare deployments. Future work includes optimizing matrix dimensions for security versus performance, introducing multiple redundant base stations, and integrating the protocol with existing healthcare authentication frameworks.
In summary, the authors present a feasible, low‑resource public‑key‑like security solution for U‑Healthcare sensor networks, demonstrating that linear algebraic operations can replace heavyweight cryptography while still providing acceptable confidentiality, integrity, and key management capabilities.
Comments & Academic Discussion
Loading comments...
Leave a Comment