Transmission Techniques for Relay-Interference Networks
In this paper we study the relay-interference wireless network, in which relay (helper) nodes are to facilitate competing information flows over a wireless network. We examine this in the context of a deterministic wireless interaction model, which e…
Authors: ** *논문 저자 정보는 제공되지 않았으나, 해당 연구는 무선 통신 이론 분야의 전문가들(예: Avestimehr, Diggavi
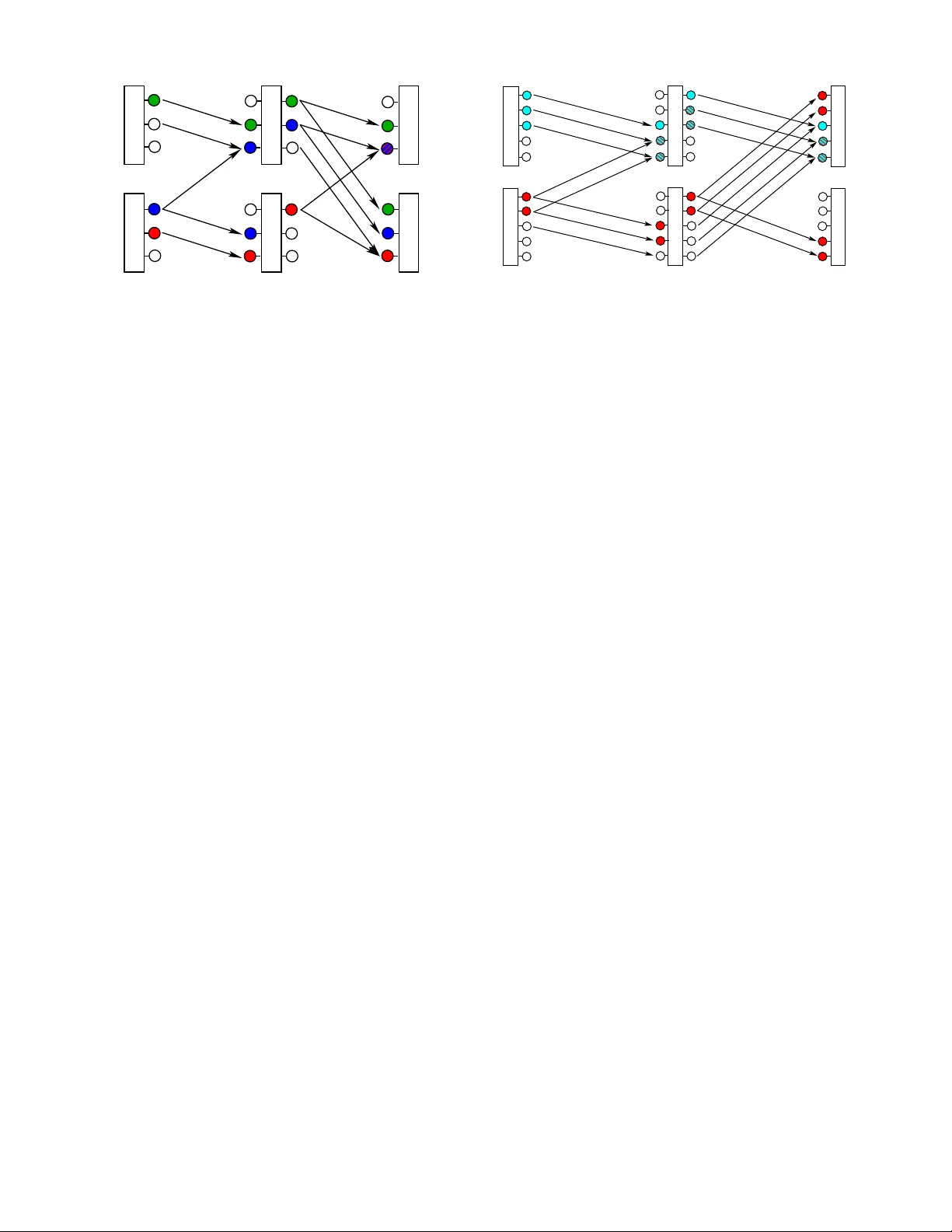
T ransmission T echniques f or Relay-Interfer en ce Networks Soheil Mohajer ∗ , Suhas N. Diggavi ∗ , Christina Fragouli ∗ , David Tse † ∗ School of C o mputer and Communica tion Sciences ´ Ecole Polytech nique F ´ ed ´ eral de Lausanne, Lau sanne, Switzerland. Email: { soheil .mohajer, suhas.diggavi, christina.fragouli } @epfl.ch † W ireless Found ations, UC Berkeley , Berkele y , California, USA. Email: dts e@eecs.berke ley.edu Abstract — In this p aper we study th e relay-interference wireless network, in which relay (helper) n odes are to facilitate competing i nform ation flows ov er a wireless network. W e ex- amine t his in the context of a d eterministic wireless in teraction model, which eliminates the channel n oise and focuses on t he signal interactions. Using this model, we show that almost all the known schemes such as interference supp ression, interference alignment and interference separation ar e necessary for relay- interference networks. In addition, we discov er a new interfer- ence management techn ique, wh ich we call interference neu - tralization, which allows f or over -the-air interference rem oval, without the transmitters having complete access the i nterfering signals. W e show that interference separation, supp ression, and neutralization arise in a fundamental manner , since we sh ow complete characterizations for special configurations of t he relay-interfer ence network. Index T erms — Interference chann el, wireless relay networks, multiple unicast, deterministic chan nel, i nterference neu traliza- tion. I . I N T RO D U C T I O N Inform ation transmission in a shared me dium is one o f th e fundam ental problem s in wireless commun ication. I n such situation a wireless channel is shared between se vera l sources and receivers, and several inform ation flo w are competing for resources. Here, a fu ndamen tal qu estion is how to manage interferen ce in a wireless network . In the multiple access channel prob lem, introduced by Ahlswede and Liao in early 70’ s, a single receiver is inter- ested in deco ding the messages sent b y different transmitters. Sev er al techn iques, in cluding multi-user d etection, ortho go- nal source allocation , and taking interference as a part of noise have been devised for this p roblem . In a m ore general setu p, not all th e sour ce are of in terest for all the r eceiv e rs. Th e in terferenc e chann el pr oblem [1] is the very b asic example of su ch situation which has been open for 30 y ears. The best known a chiev able region for this pro blem is du e to Han and Kobayashi [1] . Over the past few d ecades several techn iques have bee n devised for transm ission on the interf erence ch annels; am ong them, superpo sition of in formatio n, power allocation, an d in ter- ference supp ression (partly c ommon in formatio n) are the most well-known ones. Recen tly , the cap acity region o f the This wo rk was supported in part by the Swiss Natio nal Science Foun- dation through NCCR-MICS under gran t number 51NF40-111400 and the FNSF award number 200021-103 836/1. interferen ce channel has been characterized for some regimes by building o n an ap proxim ate characterization (within 1 bit) giv e n fo r the whole regime in [2 ]. However , it is not clear whether the known tech niques are enough to achieve the capacity wh en we also h ave relays in th e ne twork facilitating the flow of mor e than on e unicast session. The determin istic appro ach, studied b y A vestimehr, Dig- gavi, and Tse [3 ], [4], simp lifies the wireless network in- teraction m odel by eliminating the noise. Th is app roach was successfully ap plied to the relay network in [ 4], and resulted in in sight in ter ms of tran smission techniques. These insights also led to an ap proxim ate character ization o f the noisy wireless relay network pr oblem [5 ]. This model is also applied to th e interf erence channel pro blem in [6], wh ere it is shown that the capacity r egion of the determin istic interferen ce channel is with in co nstant bit g ap of the Gaus- sian in terferenc e chan nel, and an a lternative appro ximate characterizatio n for the cap acity region is pr ovided. In this p aper, we apply the deter ministic mode l to a two- stage interference channel, where the goal is to accommod ate multiple unicast flows over th e network. The simple layered structure of th e networks helps us to focus more on th e trans- mission technique s, rather than synchronization issues, raised in a n on-lay ered network. W e hav e com plete characterizatio n for two special cases, called the ZS and the ZZ n etworks. In vestigatio n of these networks, sugg est a new insight about the tran smission tech niques, which can be applied in any network. It is shown that the in terference separatio n and interferen ce sup pression ar e usefu l to a void or remove in- terference in different regimes. W e will also show that using interferen ce align ment is essential for some cases, even with two messages transmitted thro ugh the n etwork. The o ther contribution of th is pap er is to introd uce a n ew tran smission technique , interfer ence neutralization , to remove (decr ease) the inter ference in a network. The p aper is o rganized as fo llows. Sec tion I I states th e precise definition of the problem , and intro duces the nota - tions. Before stating the m ain results, we review th e known technique s and explain the ne w techniques that we will use later in Section III. W e will present our ma in resu lts, the exact characteriza tion o f the ZS and ZZ ne tworks in Sections IV and V. Finally , we w ill co nclude an d d iscuss about fu ture extensions in Section V I. I I . N OTA T I O N S A N D P RO B L E M S TA T E M E N T W ireless interaction model: In this standard model [ 7], transmitted sign als get attenuated by (complex) gain s to which indep endent (Gaussian) receiver n oise is ad ded. More formally , the r eceiv e d signa l y i at no de i ∈ V at time t is giv e n by , y i ( t ) = X j ∈N i h ij x j ( t ) + z i ( t ) , (1) where h ij is the com plex channel gain between no de j and i , x j is the signal transmitted by node j , and N i are the set of nod es that have non- zero chann el gains to i . W e a ssume that the average tr ansmit power co nstraints for all n odes is 1 and the ad ditiv e receiver Gaussian n oise is of un it variance. W e u se the ter minolog y Gaussian wir eless network whe n th e signal interactio n model is governed b y (1). Deterministic interaction mod el: In [4 ], a simp ler de- terministic m odel wh ich cap tures th e essence of wireless interaction was developed. T he a dvantage of this mo del is its simplicity , which gives insight to strategies f or the n oisy wireless network model in (1). W e will u tilize this m odel to develop techniq ues f or the relay -interfer ence network. Our main resu lts are dev elo ped for this determin istic m odel. T he deterministic mod el of [ 4] simplifies the wireless in teraction model in ( 1) by e liminating the noise and discretizin g the channel gains th rough a b inary expansion of q bits. There- fore, the received signa l Y i which is a binar y vector of size q is mo deled as Y i ( t ) = X j ∈N i M ij X j ( t ) , (2) where M ij is a q × q binary matrix rep resenting the (dis- cretized) chann el tra nsformatio n between no des j and i and X j is the (discretized ) transmitted signal. All operatio ns in (2 ) are don e over the binary field , F 2 . W e u se th e terminolo gy deterministic wir eless network when the signal interaction model is g overned by (2). Shift m atrix is a special matrix rep resentation for a Gaussian fading channel. This matrix captures the attenuation effect of the sign al caused by the chan nel gain by perfo rming a shift on the b inary representatio n of the inp ut, x j , and ignoring the b its below the average n oise level. Mor e precisely , this mo del assigns a matrix J q − n ij to the Ga ussian gain h ij , wher e J = 0 0 0 · · · 0 1 0 0 · · · 0 0 1 0 · · · 0 . . . . . . . . . . . . . . . 0 · · · 0 1 0 q × q , (3) is the shift matrix, and n ij = ⌈ 1 2 log | h ij | 2 ⌉ , f or real channel gains. An illustration o f th is deterministic model is g iv en in Fig. 1 for the broadcast and multiple access networks. Fig. 1(a) shows a deter ministic model o f the broadca st channel, where the channel fro m th e transmitter to Receiver 1 is strong er than that to Receiv er 2. Th is is represented by the deter ministic model d ev elo ped in [4] with 4 mo st significant bits (MSB) of the transmitted signal captur ed by D 1 and only 2 MSBs o f th e transmitted signa l ca ptured b y D 2 . The deterministic mode l of the multiple access channel shown in Fig. 1(b) adds on e m ore ing redient, which is how the b its from two transmitting nodes interact at a recei ver . In Fig. 1 (b) the channel f rom S 1 to D is stronger than that of S 2 . Therefo re, the inter action is b etween the 2 MSBs o f the message sent by S 2 with the lower 2 significan t b its of the m essage sen t b y S 1 , and the interaction is modeled with an add ition over the bin ary field ( i.e., xor ). This intera ction captures th e dyn amic rang e of the signal in teractions. It was shown in [4], that this model appr o ximately 1 captures the wireless interaction model o f ( 1) for the br oadcast and mu l- tiple access channe ls. For g eneral networks the d eterministic model yields insights which, when tr anslated to the noisy wireless network, lead one to develop coo perative strategies for the m odel in (1), which are ( provably) a pprox imately 2 optimal [5 ]. P S f r a g r e p l a c e m e n t s S D 1 D 2 (a) Broadc ast cha nnel P S f r a g r e p l a c e m e n t s S 1 S 2 D (b) Multip le acc ess channel Fig. 1. The linear det erministic model for a Gaussian broadcast channel (BC) is sho w n in (a) and for a Gaussian multiple access channel (MA C) is sho wn in (b). A. Multi-unica st Deterministic Network Our goal is to characterize the capacity re g ion of a network with two unicast sessions under the determin istic shift model. A simple example of such network is a two stage layered interferen ce network s h own in Fig. 2, which we call i t the XX network. Th ere are two tran smitters S 1 and S 2 which enco de 1 The approximati on is in the sense that the capacit y regi on of the determin istic model is within 1 bit of the ca pacity reg ion of the Gaussian counter parts. 2 It has been sho wn for single unicast there is an approx imate max-flow , min-cut result where the dif ference is within a constant number of bits, which dep ends on the topology of the netw ork, but not the val ues of the channe l gains [5]. their m essages W 1 and W 2 of rates r 1 and r 2 , respe cti vely , and bro adcast the obtained vectors to the re lay no des, R 1 and R 2 . P S f r a g r e p l a c e m e n t s S 1 S 2 R 1 R 2 D 1 D 2 m 11 n 11 m 22 n 22 m 21 m 12 n 21 n 12 Fig. 2. Tra nsm ission model W e assume that the messages are en coded u sing a code o f length n , and deno te the transmitted vector s in time block T (time instants { ( T − 1) n + 1 , ( T − 1) n + 2 . . . , T n } ) by X n 1 ( T ) and X n 2 ( T ) . Th e relay node R 1 ( R 2 ) receives a signal Y ′ n 1 ( T ) ( Y ′ n 2 ( T ) ) wh ich is d eterministic function of the vectors sent b y the transmitter s, a s in a m ultiple access channel. Here, m ij denotes th e channel ga in from S j to R i , for i, j ∈ { 1 , 2 } . T he transmission m odel of the first stage of the network could b e summarized by Y ′ 1 = Y ′ 11 + Y ′ 12 = M 11 X 1 + M 12 X 2 , (4) Y ′ 2 = Y ′ 21 + Y ′ 22 = M 21 X 1 + M 22 X 2 , (5) where M ij = J n − m ij is a power of the shift matrix, and Y ′ ij is th e m essage received by rela y nod e R i from th e source S j when ther e is no in terference . The r elay n odes wait until the end of the time block and apply a prop er functio n on the set of vectors rece i ved in time block T , and broad cast the re sulting vectors in time block T + 1 . W e d enote b y X ′ n 1 ( T + 1) and X ′ n 2 ( T + 1) the vectors transmitted by relays in this time block. In time block T + 1 , d estination no des D 1 and D 2 receive interfered sig nal Y n 1 ( T + 1) and Y n 2 ( T + 1) which d epend on bo th X ′ n 1 ( T + 1) and X ′ n 1 ( T + 1) . The channe l g ain from relay no de R j to destination no de D i is denoted by n ij , for i, j ∈ { 1 , 2 } . More pre cisely , Y 1 = Y 11 + Y 12 = N 11 X ′ 1 + N 12 X ′ 2 , (6) Y 2 = Y 21 + Y 22 = N 21 X ′ 1 + N 22 X ′ 2 , (7) and N ij = J n − n ij . Getting all the n vectors in tim e b lock T + 1 , the destination n odes d ecode the messages sent by the source nodes in time block T . Desti n ation node D i is only interested in d ecoding messag e W i . W e may dr op the time b lock indicators ( T o r T + 1 ) whenever it is clear from the context, and do es not cause confu sion. A rate pa ir ( r 1 , r 2 ) is called admissible if there exist a scheme for a large enoug h n , where D 1 and D 2 can decode W 1 and W 2 , respectiv ely . It is worth mentioning that this network acts like a two stage cascaded interfer ence network . Howe ver , the important dif f erence h ere is th at, unlike in th e interferen ce n etwork, the messages sent by the re lays at the P S f r a g r e p l a c e m e n t s S 1 S 2 R 1 R 2 D 1 D 2 Fig. 3. Interfer ence separa tion; ( r 1 , r 2 ) = (1 , 2) is achie vabl e. second phase of tran smission are not indepen dent. This fact affects on the cap acity region of the n etwork. In this paper, instead of studying the admissible rate region of th e general network, the main focus is on two specific realization o f the n etwork, namely , the capac ity regions o f the ZS and the ZZ ne tworks. Our m ain goal is to illu strate the transmission techniques utilized in order to achieve su ch capacity regions and we illustrate some o f the more gener al networks. I I I . T R A N S M I S S I O N T E C H N I Q U E S In th is section we illustrate som e examples, e ach o f wh ich benefits from one of the tech niques we have mentioned in the last section. A. Interfer en ce Sepa ration Consider the network shown in Fig. 3. It is easy to see that the su m-rate of this network is upp erboun ded by r 1 + r 2 ≤ 3 , (8) by study ing the cu t-set wh ich separates the destination no des from the rest of the ne twork. Assume we wish to transmit a t r ate pair ( r 1 , r 2 ) = (1 , 2 ) from the source nod es to the destination nodes. I t turns o ut that this ca n be done only using an o pportu nistic encodin g which avoid inter ference. Sin ce D 1 receives only one bit from R 1 , th is b it sho uld be the clear d ata about W 1 . Hen ce, R 1 should h av e recei ved the message from S 1 , witho ut interferen ce. Therefore, the message W 2 should be enco ded such that it does not cause interference at R 1 . More precisely , in o rder to to c ommun icate at this rate, the transm itters should encod e their messages as X 1 = x 1 (1) 0 0 , X 2 = x 2 (1) 0 x 2 (2) , (9) and the relay nod e ha ve to perfor m p roper linear operation s on their r eceiv e d signal bef ore broadca sting th em. X ′ 1 = x 1 (1) x 2 (1) 0 , X ′ 2 = x 2 (2) 0 0 . (10) It is clear this encoding scheme m akes th e interfere nce separable fr om the sign al at the nodes R 1 and D 2 . It can be seen that this is necessary as well for this example. P S f r a g r e p l a c e m e n t s S 1 S 2 R 1 R 2 D 1 D 2 Fig. 4. Interfer ence alig nment; ( r 1 , r 2 ) = (1 , 2) is achie vabl e. B. Interfer en ce Alignmen t Interfer ence alignm ent is a transmission techniq ue to put all the inter ference into a small dimen sion. T he intu ition behind this techniq ue is th e fact that w hatever sche me one uses to deal with interferenc e, it occu pies a certain numbe r of degrees of free dom of the network. Therefo re, one could expect to minim ize suc h lo ss by aligning the foo tprints of all inter ferences so that the total interfer ence is the smallest. Such phenom enon has been observed in a X channel [8] wherein two transmitters attempt to commun icate to two receivers, over an interfere nce channe l. Each transmitter has two messages, each to be deco ded at one receiv er . It has been shown th at in or der to achieve the c apacity of this network, it is ne cessary to align the two sig nals carryin g information about the irrelevant inter fering messages at the receivers. I n [8], this pheno menon has been o bserved for the case wh ere there are m ore than two messages have to be transmitted in the network. Howe ver, in this subsection, we show throug h an examp le tha t in terferen ce alignmen t mig ht b e an essential strategy ev en with two messages in our relay- interferen ce network. Consider the network sho wn in Fig. 4. W e wish to com mu- nicate at rate pair ( r 1 , r 2 ) = (1 , 2) . Since there is on ly one link from R 2 to D 2 , it is clear that the relay nod e R 1 should help them by send ing information bits abou t X 2 . Therefore, the d estination node D 1 receives two interferin g signal (fro m R 1 and R 2 ) which describe X 2 . Henc e, it would b e able to resolve X 1 if an d only if th e occ upied sub-n ode by the se two interferen ce coincide. More precisely , encoding the messages as X 1 = x 1 (1) 0 0 , X 2 = x 2 (1) x 2 (2) 0 , (11) the receiv ed signal at th e destination nodes usin g th e shown transmission strategy would be Y 1 = 0 x 1 (1) x 2 (1) + x 2 (2) , Y 2 = x 1 (1) x 2 (1) x 2 (2) . (12) This shows that the interfe ring bits x 2 (1) an d x 2 (2) are aligned at th e destinatio n node D 1 . P S f r a g r e p l a c e m e n t s S 1 S 2 R 1 R 2 D 1 D 2 Fig. 5. Interfer ence suppression : ( r 1 , r 2 ) = (3 , 2) is achie vabl e. C. Interference Su ppres sio n Dependin g on the p arameters of the network, there are cases in which ne ither interferenc e separation no r in terfer- ence alignment are optimal to achieve a transmission rate pair . Namely , there is no way to av oid interferen ce at th e receivers. Howe ver, it might be possible to r eceive a clean copy o f the in terference beside the co py who interfe red the signal. Therefo re, one could use the clean copy to remove the interferen ce. T his is exactly th e situation can be be o bserved in the Z Z network shown in Fig. 5. In this network the sign al observed at R 1 is interfer ed by S 2 , and there is no way f or R 1 to deco de W 1 when th e transmission rate is ( r 1 , r 2 ) = (3 , 2) . In or der to achiev e this rate pair, the deco der D 1 has to first (p artially) decode W 2 using the message receiv e d fr om R 2 , and then use th is message to remove th e inte rference fr om the signal received from R 1 . This is th e only strategy we can use to decode W 1 at D 1 . No te that here ther e are two in terfering p aths f rom S 2 to D 1 . Howe ver, the second path (throug h R 2 ) helps the decoder to remove th e inter ference caused by th e first path (throu gh R 1 ). D. Interfer en ce Neutralization This technique can b e used in network s which contain more than one disjoint path from S i to D j for i 6 = j , where D j is not interested in decod ing the m essage sent by the source node S i , and therefor e it r eceives the interferen ce throug h mor e tha n one link . The pr oposed techniqu e is to tune these inter fering signals such tha t they neutr alize each other at th e destination node. I n words, the inte rfering signal should be re ceiv ed at th e same power lev el a nd with different sign such that the effective interference , obtain ed by adding them, occup ies a smaller numb er of degrees of freedom. This technique is new and has not been considered in the literature up to best o f our knowledge. Fig. 6 shows a network in which interf erence neutraliza- tion is essen tial to achieve th e d esired rate p air ( r 1 , r 2 ) = (2 , 3) . He re D 1 has on ly two degrees o f freed om, and receives in formatio n bits fr om both R 1 and R 2 over these sub-nod es. Howe ver, notice that there are two disjoint paths ( S 2 , R 1 , D 1 ) and ( S 2 , R 2 , D 1 ), which conn ect S 2 to D 1 . Using a p roper m apping (permutation ) at the relay nodes, one can m ake the inter ference neutr alized at the destination P S f r a g r e p l a c e m e n t s S 1 S 2 R 1 R 2 D 1 D 2 + − Fig. 6. Interfer ence neutr alization; ( r 1 , r 2 ) = (2 , 3) is achie vabl e. P S f r a g r e p l a c e m e n t s S 1 S 2 R 1 R 2 D 1 D 2 m 11 n 11 m 22 n 22 m 2 1 m 12 n 21 m 1 2 Fig. 7. The ZS network node D 1 , an d provid e two n on-in terfered link s from S 1 to D 2 . Note that this per mutation do es not effect the ad missible rate of the other un icast from S 2 to D 2 , the co st we pay , is to re- permute the received b its at D 2 . I V . T H E ZS N E T W O R K In this sectio n, we r estrict o ur attentio n on a specific network by assuming zero gain for two of th e cro ss links. This assump tion leads us to the network shown in Fig. 7. In th e following we obta in the admissible rate region of this n etwork und er the determin istic mo del an d re strict our analysis to th e shiftin g matrices. The f ollowing th eorem gives a complete char acterization of the capacity region of the ZS network. Theor em 1 : The admissible r ate region of th e ZS network is the set of all ra te pairs ( r 1 , r 2 ) which satisfy r 1 ≤ m 11 , ( ZS -1) r 1 ≤ n 11 , ( ZS -2) r 2 ≤ max( m 12 , m 22 ) , ( ZS -3) r 2 ≤ max( n 21 , n 22 ) , ( ZS -4) r 2 ≤ m 12 + n 22 , ( ZS -5) r 2 ≤ m 22 + n 21 , ( ZS -6) r 1 + r 2 ≤ max( m 11 , m 12 ) + n 22 , ( ZS -7) r 1 + r 2 ≤ m 22 + max( n 11 , n 21 ) , ( ZS -8) r 1 + r 2 ≤ max( m 11 , m 12 ) + ( m 22 − m 12 ) + , ( ZS -9) r 1 + r 2 ≤ max( n 21 , n 22 ) + ( n 11 − n 21 ) + ( ZS -10) In the fo llowing subsections we br iefly state the outlin e of the p roof of the o ptimality as well as the achiev ab ility of this rate region. A. Necessity: The Pr oof o f the Convers e In this sub section we show th at any achiev ab le rate p air ( r 1 , r 2 ) satisfies ( ZS -1)-( ZS -10). All the ineq ualities in the theorem above, are essentially ob tained using the maxim um- flow m in-cut theorem. Clearly , the inequalities ( ZS -1) and ( ZS -2) bound the flow of inf ormation from S 1 and to D 1 , respectively . The inequality given by ( ZS -3) is simply the bound for broadcasting data f rom S 2 . Similarly , ( ZS -4) is the multiple access sum -rate boun d f or the destination no de D 2 . In order to pr ove ( ZS -5), we consider the cut which partitions the network into Ω s = { S 2 , R 2 } and Ω d = { S 1 , R 1 , D 1 , D 2 } . W e have nr 2 ≤ I ( Y ′ n 1 ( T ) , Y n 2 ( T + 1); X ′ n 2 ( T + 1) , X n 2 ( T )) = I ( Y ′ n 1 ; X ′ n 2 , X n 2 ) + I ( Y n 2 ; X ′ n 2 , X n 2 | Y ′ n 1 ) = I ( Y ′ n 1 ; X n 2 ) + H ( Y n 2 | Y ′ n 1 ) (13) ≤ I ( Y ′ n 1 ; X n 2 | X n 1 ) + H ( Y n 2 | X ′ n 1 ) (14) = H ( Y ′ n 1 | X n 1 ) + H ( Y n 2 | X ′ n 1 ) = H ( Y ′ n 12 ) + H ( Y n 21 ) ≤ rank ( M 12 ) + rank ( N 22 ) = m 12 + n 22 , (15) where in (13) we used the fact th at X ′ n 2 ( T + 1) is a function of X n 2 ( T ) , an d (14) h olds sinc e X n 2 ( T ) is independen t of X n 1 ( T ) , and X ′ 1 ( T + 1) is a fu nction of Y ′ 1 ( T ) . The inequality ( ZS -6) can be similar ly ob tained by bound ing the informa tion flow throu gh the cut Ω s = { S 1 , S 2 , R 1 , D 1 } and Ω d = { R 2 , D 2 } . The ine quality ( ZS -7) captures the inf ormation flow throug h the cut which par titions the network in to Ω s = { S 1 , S 2 , R 2 } and Ω d = { R 1 , D 1 , D 2 } . Th e maximum flow of info rmation through this cut can b e ev a luated as n ( r 1 + r 2 ) ≤ I ( Y ′ n 1 ( T ) , Y n 2 ( T + 1); X n 1 ( T ) , X n 2 ( T ) , X ′ n 2 ( T + 1)) = I ( Y ′ n 1 ; X n 1 , X n 2 , X ′ n 2 ) + I ( Y n 2 ; X n 1 , X n 2 , X ′ n 2 | Y ′ n 1 ) ≤ H ( Y ′ n 1 ) + H ( Y n 2 | Y ′ n 1 ) ≤ H ( Y ′ n 1 ) + H ( Y n 2 | X ′ n 1 ) ≤ H ( Y ′ n 1 ) + H ( Y n 22 ) ≤ n rank M 11 M 12 + n rank ( N 22 ) = n max( m 11 , m 12 ) + nn 22 (16) Similarly , we can pr ove ( ZS -8) by bundin g the informa - tion flow th rough the cut Ω s = { S 1 , S 2 , R 1 } and Ω d = { R 2 , D 1 , D 2 } . It remains to show prove the upper bound s ( ZS -9) and ( ZS -10). Consider th e cut Ω s = { S 1 , S 2 } and Ω d = { R 1 , R 2 , D 1 , D 2 } . The flow of inform ation thr ough this cut can be upper bo unded as n ( r 1 + r 2 ) ≤ I ( Y ′ n 1 ( T ) , Y ′ n 2 ( T ); X n 1 ( T ) , X n 2 ( T )) = I ( Y ′ n 1 ; X n 1 , X n 2 ) + I ( Y ′ n 2 ; X n 1 , X n 2 | Y ′ n 1 ) ≤ I ( Y ′ n 1 ; X n 1 , X n 2 ) + H ( Y ′ n 2 | Y ′ n 1 ) − H ( Y ′ n 2 | X n 1 , X n 2 , Y ′ n 1 ) ≤ n max( m 11 , m 12 ) + H ( Y ′ 2 | Y ′ 1 ) (17) Note tha t D 1 receives inf ormation on ly thr ough R 1 . There- fore since D 1 is able to decode W 1 , so R 1 is. Hence, using Fano’ s in equality we can write H ( Y ′ n 2 | Y ′ n 1 ) ≤ H ( Y ′ n 2 | Y ′ n 1 , W 1 ) + nε = H ( Y ′ n 2 | Y ′ n 11 , Y ′ n 12 ) + nε ≤ H ( Y ′ n 2 | Y ′ n 12 ) = n ( m 22 − m 12 ) + . (18) The proof of inequality ( ZS - 10) follo ws a similar ar g ument by bou nding the inform ation flow thro ugh the cut Ω s = { S 1 , S 2 , R 1 , R 2 } an d Ω d = { D 1 , D 2 } . n ( r 1 + r 2 ) ≤ I ( Y n 1 ( T + 1) , Y n 2 ( T + 1); X ′ n 1 ( T + 1); X ′ n 2 ( T + 1)) = H ( Y n 1 , Y n 2 ) = H ( Y n 2 ) + H ( Y n 1 | Y n 2 ) ≤ n ma x( n 21 , n 22 ) + H ( Y n 1 | Y n 2 ) . (19) Now , we ca n use the facts tha t having Y n 2 ( T + 1 ) , D 2 is assumed to be ab le to decod e W 2 . Also it is clear th at X ′ n ( T + 1) is a deterministic fun ction o f W 2 , and theref ore that of Y n 2 ( T + 1) . H ( Y n 1 | Y n 2 ) ≤ H ( Y n 1 | Y n 2 , W 2 ) + nε ≤ H ( Y n 1 | Y n 2 , Y n 22 ) + nε ≤ H ( Y n 1 | Y n 21 ) ≤ ( n 11 − n 21 ) + (20) B. Achievability Here we on ly give the o utline of the transmission schem e that can be used to achiev e the rates given in Theo rem 1. This scheme work s by dec omposition of th e network into two isolated compo nents, namely N 1 and N 2 , wher e each p air o f source/destinatio n u ses one compon ent f or com munication . Here by two isolated network we mean two networks which are completely disjoint and and no me ssage can be transmit- ted f rom o ne to an other . The fact that th e co mponen ts ar e isolated, guarantees that the signals do not cause interferen ce. Such deco mposition is based on the desired transmission rate pair . W e denote by S 1 ( N i ) the set of subn odes at S 1 which are inc luded in th e network c ompon ent, N i , and use similar notation for partitioning th e other sub nodes of th e network. In order to comm unicate at rate ( r 1 , r 2 ) , which satisfies ( Z S -1)-( ZS -10), we fo rm the compo nents o f the network as follows. S 1 ( N 1 ) includes the top ( m 11 − m 12 ) + as well as the lowest ( r 1 − ( m 11 − m 12 ) + ) + subnod es of S 1 . Th is comp onent also include s any receiver node from R 1 which is connected to a n ode in S 1 ( N 1 ) , and any n ode in D 2 P S f r a g r e p l a c e m e n t s S 1 S 2 R 1 R 2 D 1 D 2 m 11 n 11 m 22 n 22 m 2 1 m 12 n 12 n 1 2 Fig. 8. The ZZ netwo rk. which is con nected to a n ode in R 1 ( N 1 ) . Clearly the r eceiv e r nodes in R 2 which are co nnected to a n ode in D 2 ( N 1 ) are also inclu ded in N 1 . Similarly , th e transm itter part of R 1 in the fir st comp o- nent includes the top ( n 11 − n 21 ) + as well as the lowest ( r 1 − ( n 11 − n 21 ) + ) + nodes of the tran smitter side of R 1 . In consequ ence, all the correspo nding sub nodes in D 1 , R 2 and D 2 are also includ ed in N 1 . The second compo nent of the ne twork is for med by all the rem aining subno des in th e network. It is clear the this decomposition is isolated by its construc- tion, and the S 1 / D 1 can use the first compo nent to commu- nicate at r 1 as a line network. On e can also characterize the second n etwork N 2 , as network with two relays a nd show that S 2 / D 2 can commun icate ov er this network at rate r 2 . W e deligate the proof details of this p art to the jo urnal version because of lack of space. V . T H E ZZ N E T W O R K In this section we con sider another special case o f the XX network. Here, we assume that the cross-links fro m S 1 to R 2 , and also the cro ss link fro m R 1 to D 2 have zero gain . Therefo re, th e remaining network would be two Z network which are cascad ed as shown in Fig. 8. In the following we will o btain th e ad missible ra te region of a Z Z network. Th e capacity of a single Z chan nel und er deterministic shift model has been computed in [6]. Howe ver , it tu rns out tha t the rate r egion of a ZZ network cou ld be a strict super set of the rate region of the single Z n etwork. It is not surpr ising, since the messages broadca sted by the relay nodes in the secand stage of the network are not independen t, while in a Z network they are. The key observation of this enlargemen t o f th e cap acity region is the inter ference neutra lization. In fact, in a single Z network the cro ss link ac ts as an in terferenc e for one of the receivers. I n a ZZ network as shown in Fig. 8, the signal received at D 1 is effected b y two interferen ce ( throug h link s S 2 to R 1 and R 2 to D 1 ) which car ry informatio n about the same message X 2 . Therefo re, it is possible that to enco de them such th e total effectiv e inte rference be weaker than the original o ne. I n o ther word s, the interfer ence caused by the link S 2 to R 1 can be (par tially) neutralized by the oth er cross link in the seco nd stage of the network. Mor e precisely , the signals sent by the relays can be am plified pro perly suc h that they hav e oppo site effect on the effecti ve in terferenc e at D 1 , and there fore partially neutra lize each othe r . In the following theor em, we character ize the admissible rate region of a ZZ n etwork. Theor em 2 : The capacity of r egion o f a determ inistic ZZ network shown in Fig. 8 is given b e the set of all ( r 1 , r 2 ) which satisfy r 1 ≤ m 11 , ( ZZ -1) r 2 ≤ m 22 , ( ZZ -2) r 1 ≤ n 11 , ( ZZ -3) r 2 ≤ n 22 , ( ZZ -4) r 1 + r 2 ≤ max( m 11 , m 12 ) + ( m 22 − m 12 ) + + n 12 , ( ZZ -5) r 1 + r 2 ≤ max( n 11 , n 12 ) + ( n 22 − n 12 ) + + m 12 } . ( ZZ -6) A. Necessity: The Pr oof o f the Convers e In this section we briefly state the pro of of the op ti- mality of the rate region intr oduced in Th eorem 2. Th e first inequality ( ZZ -1) is simply obtained by the maxim um informa tion flow th rough the cut Ω s = { S 1 } and Ω d = { S 2 , R 1 , R 2 , D 1 , D 2 } . nr 1 ≤ I ( X n 1 ; Y ′ n 1 | Y ′ n 12 ) = H ( Y ′ n 1 | Y ′ n 12 ) ≤ H ( Y ′ n 11 ) ≤ n rank ( M 11 ) = nm 11 . (21) Similarly r 2 can b e upper boun ded by the infor mation flo w throug h th e cut set Ω s = { S 1 , S 2 , R 1 , R 2 , D 1 } an d Ω d = { D 2 } as in ( Z Z -4). Note th at ( ZZ -2) is tighter than the cut-set bo und. In fact, D 2 receives info rmation only fro m R 2 . So whate ver D 2 can decode is also deco dable by R 2 . This can be seen thr ough the Markov chain X n 2 ( T ) ↔ Y ′ n 2 ( T ) ↔ X ′ n 2 ( T + 1) ↔ Y n 2 ( T + 1) . nr 2 ≤ H ( W 2 ) ≤ I ( W 2 ; Y n 2 ) + H ( W 2 | Y n 2 ) ≤ I ( X n 2 ; Y n 2 ) + nε n (22) ≤ I ( X n 2 ; Y ′ n 2 ) + nε n = H ( Y ′ n 2 ) + nε ≤ n rank ( M 22 ) = nm 22 + nε, (23) where (22) f ollows from the Fano’ s inequality . W e can a lso up per bou nd r 1 as in ( ZZ -3) by noting the fact that the o nly path in the network which conn ects S 1 to D 1 passes th rough R 1 . Ther efore, the Markov c hain Y 2 ↔ ( X ′ 1 , X ′ 2 ) ↔ ( X 1 , X ′ 2 ) hold s. nr 1 ≤ I ( Y n 1 ; X 1 ) ≤ I ( Y n 1 ; X 1 | X ′ n 2 ) (24) = H ( Y n 1 | X ′ n 2 ) − H ( Y n 1 | X 1 , X ′ 2 ) = H ( Y n 1 | X ′ n 2 ) − H ( Y n 1 | X ′ 1 , X ′ 2 ) ≤ nH ( Y 1 | X ′ 2 ) , (25) where (2 4) hold s since th e message sent by R 2 only de pends on X n 2 and is in depend ent of X n 1 . Finally , we h av e r 1 ≤ H ( Y 1 | X ′ 2 ) ≤ rank ( N 11 ) = n 11 . (26) The proof of the sum- rate bounds are more tec hnical. For each ineq uality we start with the informatio n flow thr ough a cut-set, and then we use a key ob servation in ev alu ating the cut-set value. Consider the cut- set Ω s = { S 1 , S 2 } and Ω d = { R 1 , R 2 , D 1 , D 2 } . In o rder to prove ( ZZ -5), we provide the informa tion sen t by R 2 to D 1 for R 1 as side in formatio n. In such conditio n, th e informatio n R 1 has abou t W 1 is stronger than the inform ation D 1 has, and therefo re R 1 can decode W 1 . By removin g the interference from S 1 , R 1 can also get partial info rmation about W 2 . Mor e precisely , we can wr ite n ( r 1 + r 2 ) ≤ I ( X n 1 ( T ) , X n 2 ( T ); Y ′ n 1 ( T ) , Y ′ n 2 ( T )) = H ( Y ′ n 1 , Y ′ n 2 ) ≤ H ( Y ′ n 1 , Y ′ n 2 , Y n 12 ( T + 1)) = H ( Y ′ n 1 , Y n 12 ) + H ( Y ′ n 2 | Y ′ n 1 , Y n 12 ) ≤ H ( Y ′ n 1 ) + H ( Y n 12 ) + H ( Y ′ n 2 | Y ′ n 1 , Y n 12 ) ≤ max( m 11 , m 12 ) + n 12 + H ( Y ′ n 2 | Y ′ n 1 , Y n 12 ) (27) Note that H ( Y ′ n 12 | Y ′ n 1 , Y n 12 ) = H ( Y ′ n 1 − Y ′ n 11 | Y ′ n 1 , Y n 12 ) ≤ H ( Y ′ n 1 , Y ′ n 11 | Y ′ n 1 , Y n 12 ) = H ( Y ′ n 11 | Y ′ n 1 , Y n 12 ) ≤ H ( W 1 | Y ′ n 1 , Y n 12 ) ≤ H ( W 1 | Y n 11 , Y n 12 ) ≤ H ( W 1 | Y n 11 + Y n 12 )) = H ( W 1 | Y n 1 ) ≤ nε n (28) where ε n → 0 as n grows. Note that (28) follows from the Fano’ s ine quality , and the fact that D 1 can decode the message sent b y S 1 . Henc e, H ( Y ′ 2 | Y ′ 1 , Y 12 ) ≤ H ( Y ′ 2 , Y ′ 12 | Y ′ 1 , Y 12 ) = H ( Y ′ 2 | Y ′ 12 , Y ′ 1 , Y 12 ) + H ( Y ′ 12 | Y ′ 1 , Y 12 ) ≤ H ( Y ′ 2 | Y ′ 12 ) + ε n ≤ ( m 22 − m 12 ) + + ε n . (29) Continuing fro m 27 we h ave r 1 + r 2 ≤ H ( Y ′ 1 ) + H ( Y 12 ) + H ( Y ′ 2 | Y ′ 1 , Y 12 ) ≤ max( m 11 , m 12 ) + n 12 + ( m 22 − m 12 ) + . (30 ) The last in equality ( ZZ -6), intu iti vely mean s that the num- ber of neutralized sub links at D 1 cannot exceed th e minimum of m 12 and n 12 . W e can similarly prove it by co nsidering the information flow through the cut Ω s = { S 1 , S 2 , R 1 , R 2 } and Ω d = { D 1 , D 2 } , an d pr oviding D 1 by th e info rmation sent by S 2 to R 1 as side informa tion. n ( r 1 + r 2 ) ≤ I ( Y n 1 ( T + 1) , Y n 2 ( T + 1); X ′ n 1 ( T + 1); X ′ n 2 ( T + 1)) = H ( Y n 1 , Y n 2 ) ≤ H ( Y n 1 , Y n 2 , Y ′ n 12 ( T )) ≤ H ( Y n 1 ) + H ( Y ′ n 12 ) + H ( Y n 2 | Y n 1 , Y ′ n 12 ) Similar to proof o f ( ZZ -5), we u se th e following b ound ing technique . H ( Y n 12 | Y n 1 , Y ′ n 12 ) = H ( Y n 1 − Y n 11 | Y n 1 , Y ′ n 12 ) ≤ H ( Y n 1 , Y n 11 | Y n 1 , Y ′ n 12 ) = H ( Y n 11 | Y n 1 , Y ′ n 12 ) ≤ H ( Y ′ n 1 | Y n 1 , Y ′ n 12 ) = H ( Y ′ n 11 + Y ′ n 12 | Y n 1 , Y ′ n 12 ) = H ( Y ′ n 11 | Y n 1 , Y ′ n 12 ) ≤ H ( Y ′ n 11 | Y n 1 ) ≤ H ( W 1 | Y n 1 ) ≤ nε n , (31) where we have used the Fano’ s inequality in (31). Th erefor e, H ( Y n 2 | Y n 1 , Y ′ n 12 ) ≤ H ( Y n 2 , Y n 12 | Y n 1 , Y ′ n 12 ) = H ( Y n 2 | Y n 12 , Y n 1 , Y ′ n 12 ) + H ( Y n 12 | Y n 1 , Y ′ n 12 ) ≤ H ( Y n 2 | Y n 12 ) + ε n ≤ ( n 22 − n 12 ) + + ε n . (32) Therefo re, we have r 1 + r 2 ≤ max ( n 11 , n 12 ) + m 12 + ( n 22 − n 12 ) + . (33) B. Achievability In this subsection we briefly state the transmission tech - nique that can be used to achieve the capacity region of a ZZ netw o rk. The keypoint here is to use the ca pability of interfer ence n eutralization and interferen ce supp ression suggested by the two d isjoint paths from S 2 to D 1 to overcome the interference effects. Our scheme is based on a ne twork decomposin g. W e say that four subn odes a ∈ S 1 , b ∈ R 1 , c ∈ S 2 , and d ∈ R 2 form a full Z path if c broadcasts to b and d , an d b r eceives info mation from a and c as in a multiple ac cess channel. It can b e shown that the nu mber o f fu ll Z paths in first layer of the network is given by δ S R = min( m 11 , m 12 , m 22 , ( m 11 + m 22 − m 12 ) + ) . (34) Similarly we form the full Z path s in the second lay er of the network. The nu mber of such p aths would be δ RD = min( n 11 , n 12 , n 22 , ( n 11 + n 22 − n 12 ) + ) . (35) Therefo re, we have δ = min( δ S R , δ RD ) full ZZ pairs , in the network. The dec omposing of the network, fo rms two c ompon ents, one c ontaining the max imum nu mber of fu ll ZZ pairs, and the oth er o ne which is the rest o f the network. It is easy to show that these two networks are isolated and do not c ause interferen ce to each oth er . Moreover, the first com ponen t, the full ZZ pairs, form two p aths from S 1 to D 1 and from S 2 to D 2 , with δ degrees of freedom . The inter ference in this compon ent is natural neutralizatio n b y the stru cture of the network, and therefore, it f orms δ clean lin ks for each pair of source /destination. Dependin g on th e parameters of th e network, N 2 , the second co mpon ent can be eith er a cascade of a Z chann el with two par allel link s, a n etwork with on ly one tran smit- ter (re ceiv er ), or a ZZ network wh erein no m ore f ull ZZ pair exists. It is easy to study this com ponen t and obtain an op timal transmission strategy in the two f ormer cases. Howe ver , it req uires m ore tec hnical d etails to investigate the second co mpon ent if the r emaining is a ZZ network. It ca n b e sh own th at in this situa tion we n eet to apply either interferen ce n eutralization or interference suppression to co n vey maximu m amou nt of informatio n thro ugh th e network. Using such strategies we can show that in any o f the me ntioned c ase, any rate pair satisfying Theo rem 2 is achiev ab le. V I . C O N C L U S I O N In this paper we e x amined the relay-interfere nce n etwork, which is a n atural com bination of the relay network alo ng with the interf erence chan nel. This can also be thou ght of as the multiple-unicast problem in the co ntext of wireless networks. The b roadcast natur e o f wireless commun ication makes signal interactions more co mplicated, leading to a challengin g pro blem. W e make progress on this question by studying it u sing the d eterministic model intr oduced in [4]. W e show th at besides the k nown interferen ce managem ent technique s such as in terference suppr ession, align ment and separation, we a lso need a ne w tech nique we ter m inter- ference n eutralization . The characterization f or tw o -stage ZZ and ZS netw o rks demonstrate that this new technique arises in a fund amental manner . In ongo ing work, we have made progress on app roximate c haracterizatio ns of the noisy (Gaussian) version of the relay-interf erence networks. W e hope to co mpletely answer this and questions related to arbitrary co nfiguratio ns for the two-unicast p roblem in a future work. R E F E R E N C E S [1] T . S. Han and K. Kobayashi , “ A new achie vabl e rate region for the interfe rence channel, ” IEEE T rans. Inform. Theory , vol. 27, no. 1, pp. 49–60, Jan. 1981. [2] R. Etkin, D. Tse, and H. W ang, “Gaussia n interfer ence channel capac ity to within one bit, ” submitted to the IEEE T rans. Inform. Theory , Feb . 2007. [3] S. A vestimeh r, S. N. Diggavi, and D. N. C. Tse, “W ireless netw ork informati on flow , ” Proc eedings of Allerton Confer ence on Communi- cation, Contr ol, and Computi ng , Illinoi s, Septe m ber 2007. [4] S. A vesti mehr, S. N. Digga vi, and D. N. C. Tse, “ A Determini stic approac h to wirel ess relay networks, ” Pr oceedings of Allerton Confer- ence on Communic ation, Contr ol, and Computing , Illi nois, September 2007. [5] S. A vestimeh r, S. N. Digga vi, and D. N. C. T se, “ Approximate ca- pacit y of Gaussian rela y networks, ” P r oceeding of IEEE International Symposium on Information Theory , T oronto, July 2008. [6] G. Bresler and D. N. C. T se, “The two-user Gaussian inter ference channe l: a deterministi c vie w , ” arXi v:0807.3222 v1. [7] D. Tse and P . V iswana th, Fundamentals of wi reless communi cation , Cambridge Unive rsity Press, May 2005. [8] M. A. Maddah -Ali, A. S. Motahari, and A. K. Khanda ni, “Communi- catio n o ver MIMO X channels: interfere nce alignme nt, decomposition, and performance analysis, ” IEEE T rans. Inform. T heory , vol. 54, no. 8, pp. 3457–3470, Aug. 2008.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment