LACK - a VoIP Steganographic Method
The paper presents a new steganographic method called LACK (Lost Audio PaCKets Steganography) which is intended mainly for VoIP. The method is presented in a broader context of network steganography and of VoIP steganography in particular. The analytical results presented in the paper concern the influence of LACK’s hidden data insertion procedure on the method’s impact on quality of voice transmission and its resistance to steganalysis.
💡 Research Summary
The paper introduces LACK (Lost Audio PaCKets), a novel steganographic technique designed for Voice over IP (VoIP) communications. LACK exploits the fact that RTP packets arriving later than a receiver’s jitter buffer are discarded as “lost.” By intentionally delaying selected audio packets and replacing their payloads with hidden data, LACK creates a covert channel without generating additional traffic. The authors place LACK within a broader taxonomy of network steganography: S1 methods modify header or payload fields, S2 methods alter timing (e.g., packet order, inter‑packet delay, intentional loss), and S3 methods combine both. LACK belongs to S3, offering high steganographic capacity while remaining relatively simple to implement because RTP is typically accessible at the application layer in soft‑phones.
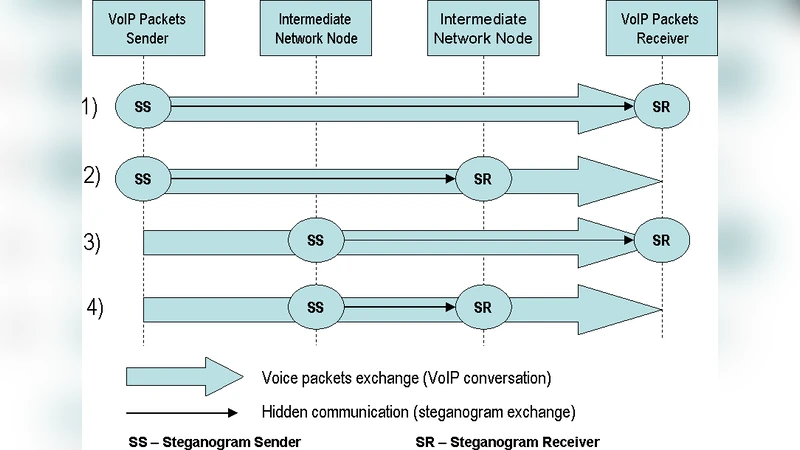
Four operational scenarios are described: (1) direct payload substitution, (2) intentional delay before transmission, (3) discarding delayed packets by an unaware receiver, and (4) extraction of hidden data by a receiver that knows the scheme. The performance of LACK depends on codec characteristics (e.g., G.711, G.729A, G.723.1), frame size, jitter‑buffer size, and network QoS parameters such as delay, loss probability, and jitter. Each codec tolerates a certain packet‑loss ceiling (1 % for G.723.1, 2 % for G.729A, 3 % for G.711, up to 5 % with packet‑loss concealment). If LACK introduces loss beyond these thresholds, perceived voice quality degrades noticeably.
The authors derive a theoretical hidden‑data rate: for G.711 (64 kbps, 20 ms frames) and a 0.5 % induced loss, the covert bandwidth is about 320 bits/s. To guarantee that a delayed packet is treated as lost, the induced delay must exceed the receiver’s jitter buffer, typically 30–70 ms. Consequently, LACK users must exchange jitter‑buffer size information beforehand and keep induced delays as low as possible to avoid detection.
Steganalysis of LACK is challenging because packet loss is a natural phenomenon in IP networks. The paper outlines three detection strategies: (a) passive monitoring of RTP/RTCP loss counters to spot statistically higher loss rates, (b) statistical analysis of call‑duration distributions (LACK‑enabled calls may be longer due to hidden‑data transmission), and (c) active wardens that drop any packet arriving later than a predefined threshold. The latter, however, risks degrading legitimate traffic because the warden cannot know the exact jitter‑buffer size of each receiver.
A key contribution is the proposal of a time‑varying hidden‑data insertion rate (IR). Fixed IR leads to a constant loss proportion throughout a call, making detection easier, especially for long calls. By decreasing IR as the call progresses, LACK reduces its impact on QoS and becomes less distinguishable from normal traffic. To model realistic VoIP call durations, the authors analyze a large dataset (≈150 000 calls) from an Italian operator (FastWeb). The empirical distribution shows a mean of 117 seconds, standard deviation of 278 seconds, and a coefficient of variation (CV) of 2.37—far from the exponential distribution (CV = 1) traditionally assumed for PSTN calls. The authors fit the data using a Weibull distribution, varying the shape parameter k and scale λ to achieve a wide range of CV values (e.g., k = 3.4, λ = 130.57 for CV ≈ 0.5; k = 0.6, λ = 77.9 for CV ≈ 2.5). This flexible model allows the IR to be adapted according to the statistical properties of the call‑duration distribution, thereby minimizing the probability that LACK‑enabled calls deviate from the expected pattern.
The paper concludes that LACK offers a practical balance between implementation simplicity and steganographic capacity, but its safe deployment requires careful management of induced packet loss, dynamic adjustment of insertion rates, and awareness of network QoS conditions. Future work suggested includes real‑time adaptive IR algorithms, support for multiple codecs and multi‑stream scenarios, development of counter‑measures that avoid harming legitimate traffic, and extensive field testing in operational VoIP environments.
Comments & Academic Discussion
Loading comments...
Leave a Comment