The Capacity of Ad hoc Networks under Random Packet Losses
We consider the problem of determining asymptotic bounds on the capacity of a random ad hoc network. Previous approaches assumed a link layer model in which if a transmitter-receiver pair can communicate with each other, i.e., the Signal to Interfere…
Authors: Vivek P. Mhatre, Catherine P. Rosenberg, Ravi R. Mazumdar
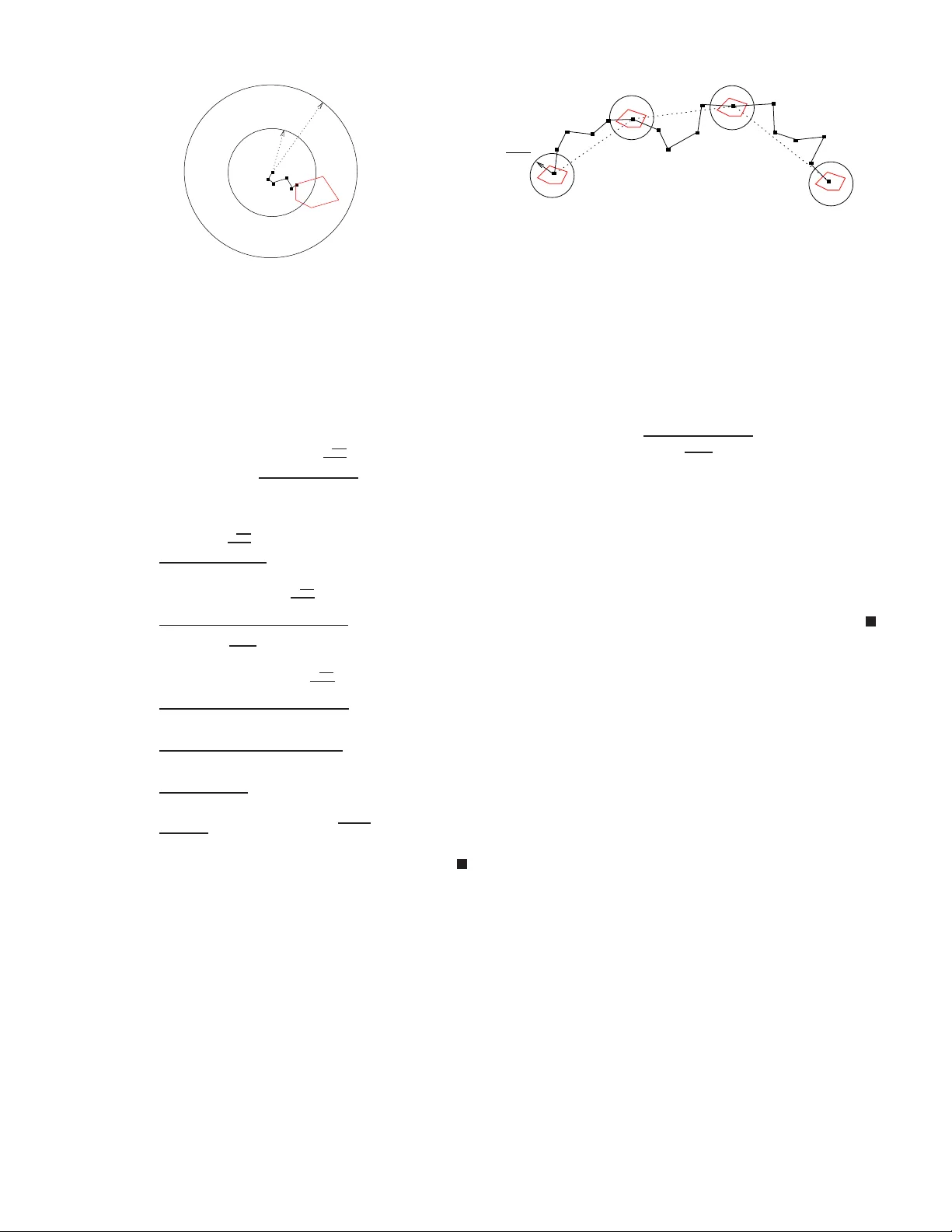
1 The Capacity of Ad hoc Netw orks under R andom P ack et L osses V i vek P . Mhatre, Catherine P . Rosenberg, Ravi R. Mazumd ar Abstract — W e consider the p roblem of determining asymptotic bounds o n the capacity of a random ad hoc network 1 . Pre vious approaches assumed a link layer model in wh ich if a transmitter - recei ver pair can communicate with each oth er , i.e., the Signal t o Interference and N oise Ratio (SINR) is above a certain threshold, then ev ery transmitted packet is r eceiv ed error -free by the recei ver thereby . Using this model, the per node capacity of the network was shown to be Θ “ 1 √ n log n ” . In reality , fo r any finite li nk SINR, th ere is a non-zero probability of erroneous reception of the packet. W e show that in a larg e n etwork, as the packet tra vels an asymptotically l arge number of h ops from source to destination, the cumulative impact of packet losses ov er intermediate links results in a p er -n ode throughput of only O ` 1 n ´ . W e then propose a new scheduling scheme to counter this effect. The proposed scheme provides tight guarantees on end-to-end packet loss probability , and improve s th e per -n ode throughput to Ω 1 √ n (log n ) α +2 2( α − 2) ! where α > 2 is the path loss exponent. K E Y W O R D S Ad hoc networks, Capacity , SINR, I nterferen ce, Sched uling I . I N T RO D U C T I O N The p roblem of th e capacity of wire less ad hoc network s was first analyzed by Gup ta an d Kumar in their seminal work [1]. Th is work was followed by sev eral studies on the capa city of wireless ad hoc netw orks [3], [9], among others. Th e authors in [1] deriv e asymptotic boun ds on the capacity of a random ad hoc network in which nodes are deployed randomly and un iformly over th e surface o f a sphere of un it area. Each node picks a rando m n ode as its destination nod e, a nd sends packets to that node by using multi-hop c ommun ication. All the nodes use a comm on tra nsmit power level. The auth ors show that eac h nod e can ach iev e a thr oughp ut of Θ 1 √ n log n packets per second. They also provide a scheduling and routing strategy that achiev es this throug hput. The authors in [1] assume a link layer mode l in which, if the Signal to Interference and Noise Ratio (SINR) at th e receiver is greater th an a certain threshold then the packet is r eceived successfully b y the r eceiver . In p ractical wireless network s, for a given modulation and codin g schem e, and for a fixed block len gth, as long as there is so me n oise an d interfer ence, i.e., as long as the SINR of a link is finite, there is a certain V iv ek P . Mhatre is with Motorola Inc., Arlington Height s, IL, USA. E mail: mhatre@gmai l.com, Catherine P . Rosenberg and Ravi R. Mazumdar are with the Department of Electri cal and Computer Engineer ing, Univ ersity of W aterloo , Canada. Em ail: { cath,mazum } @e ce.uwat erloo.ca. 1 Prelimina ry v ersions of this work appeared in [16], [15]. non-ze ro probab ility of packet error . Hence, the hypothesis of perfect p acket reception whe n the lin k SINR is above a certain threshold can be realized only when one of the following is assumed: (i) in finite block leng ths, or ( ii) infinite nu mber of retransmissions, i.e., retransmit the packet until it gets throu gh. Both these appro aches lead to u nbou nded delays, and hen ce under either (i) or (ii), a delay-capacity trad eoff study sh ould be u ndertaken instead of a c apacity stud y . I n practical systems in o rder to keep the overall dela y u nder tabs, the block leng th, as well as the maximum n umber o f retransmission attemp ts (in case retransmissions are employed) are pre-determined, and fixed. Hence, the th reshold- based packet re ception m odel u sed in [ 1] is a reasonab le ch oice for successful packet r eception in a single hop network such as a cellular n etwork. Howe ver, we argue that it needs to b e refin ed wh en app lied to a m ulti- hop network. In an ad h oc network, each packet traverses multiple h ops . When a packet is relayed ov er a large num ber of links, e ach of wh ich being likely to drop the packet with a certain probab ility (no matter how small it is), the en d-to- end throu ghput can degrade significantly due to the cumu lative packet err or pro bability . More gen erally , in this pape r , we show tha t when studying capacity scalin g problems, the u nderlyin g hypo theses have a significant impact on the results. In particular, we sh ow that when packet losses over links are taken into accoun t, we g et strikingly different results ther eby showing the sensitivity of capacity stud ies to the underlying h ypotheses. For a random ad hoc network, f or a broad range of rou ting and sche duling schemes including th e o ne propo sed in [ 1], we sh ow that the cu mulative impa ct of per link pac ket loss results in a much lower per-node th rough put of O 1 n instead of Θ 1 √ n log n . In order to counter the ab ove thro ughp ut reduction due to cu mulative p acket error effect, we propose a new scheduling po licy that uses lower spatial re use to reduce interferen ce, and ther eby imp roves the SINR of each link. Th e propo sed schedu ling p olicy im proves the en d-to-e nd packet success prob ability , a nd results in a per-node throug hput of Ω 1 √ n (log n ) α +2 2( α − 2) , whe re α > 2 is the path loss expo nent. The r est of th e pap er is organ ized a s follows. W e motiv ate the p roblem, and outline ou r appro ach in Sectio n II. The analytical models used for the p hysical and the network layer are presented in Section III. W e pr esent results on throug hput reduction du e to cumulative packet loss in Section IV and Section VII. W e p resent ou r n ew scheduling po licy , and o btain the cor respond ing cap acity re sults in Section V. W e d iscuss some of the related work in Section VI . Finally , we p resent 2 our conclusion and future directions in Section VII. I I . M OT I V A T IO N A N D A P P ROA C H The arguments in this sectio n are o nly m eant to p rovide intuitive in sights about the pro blem and ou r approac h. W e provide precisely p roved re sults for all the argumen ts in Section III. In [1], the au thors study the p roblem of de- termining the capacity of ran dom ad hoc networks. They propo se a routing and sched uling scheme to achieve a per- node throu ghpu t o f Θ 1 √ n log n . It can b e shown that for this scheme a packet tra verses Θ q n log n intermediate hops on its way from a source node to its destinatio n no de. Th us asymptotically , the number of hops that a p acket has to tra vel from source to destination goes to in finity as n scales. Th e authors assume that if the SINR over a hop is at least β , the packet tr ansmission is successful. Let us call this the id eal link m odel. Th e au thors then use a scheduling sche me wh ich ensures an SINR of at least β over all the hops. Thus, under the ideal link model, and the propo sed scheduling policy , e very packet tran smission is successful. Now co nsider anoth er lin k mod el in which a link is reliable with a pro bability p < 1 , i.e., each packet transmitted on the link is r eceiv ed successfully at th e receiver with a probab ility of p . Le t us call this the probabilistic lossy link mo del. For simplicity , assume that over each hop , if a p acket is n ot received successfully by the receiver , the transmitter d oes not retransmit the pac ket, and the packet is lost (the gen eralization to hand le re transmissions is ad dressed subseque ntly). Also assume that we use the same routing and schedu ling policy as u sed ab ove for the ideal link mod el. Since there are Θ q n log n hops from source to destination, the probab ility that the pac ket re aches its destination scales as p √ n log n . It is easy to show that this q uantity is O q log n n , since p m is O 1 m as m tends to in finity . Let u s consider two identical networks, one with the id eal link mo del, and the o ther with the pro babilistic lo ssy link model, and assume that for b oth of them, we use th e same routing an d sched uling algorithm as outlined in [ 1]. The on ly difference b etween the two n etworks is that wh ile in th e form er ca se, all the packets injec ted b y the source into the network reach the destination, in the latter case, only a fraction of the injected packets reach the destinatio n. Hence, under the p robabilistic lossy link mo del, the achievable throug hput is the p roduct of th e ach iev ab le th rough put o f the ideal link model, Θ 1 √ n log n , and an end-to -end packet delivery probability ter m th at is O q log n n . This resu lts in an end- to-end throughp ut of O 1 n for the pro babilistic lo ssy link m odel. A realistic link mod el lies somewhere between the ideal link model an d the p robabilistic lo ssy link mo del. In a r ealistic link model, the pro bability of link reliab ility , p , is a continu ous function of the SINR of the link. The SINR in turn dep ends on factors su ch as tr ansmitter-receiv er separation, power o f in - terference fro m simultane ous transmissions, and noise power . These factors are d ifferent for different links along a pa th. W e fir st show that despite ensuring a m inimum SINR of β , there is a no n-zero packet loss probab ility over each link. W e then sho w that since the scheduling approach in [1] does not take into a ccount th e cu mulative packet losses along a path , it results in a substantially lower through put ( O 1 n instead of Θ 1 √ n log n ). W e then propose a ne w s chedu ling policy under which the throug hput perf ormanc e is Θ 1 √ n (log n ) α +2 2( α − 2) ev en in the p resence of packet losses. I I I . M O D E L F O R R A N D O M N E T W O R K S W e use the standard ordering notations for O ( . ) , o ( . ) , Ω( . ) , ω ( . ) , Θ ( . ) . Scaling model: W e assume that n nodes are random ly and unifor mly de ployed over a sph ere S 2 of are a n so that the node density is kept constant. Under this model, the far -field assumption can be employed in the path lo ss mo del [1 4]. The nodes a re a ssumed to be station ary . Each node p icks a r andom node as its d estination n ode, and sends packets to this d estination node. Each node has a common transmit power level P , and uses intermediate n odes as relays to r each its destination. W e assume that as n scales, the m odulation and cod ing schem e, as well as the block length remain fixed. Furthermo re, we assume that a common frequency chunk of W Hz is av ailable to all the nodes. This m odels th e scenario in which althou gh the network size increases, the underly ing hardware and software capabilities of the nodes, as well as the av ailab le spectru m are unchan ged. Physical layer model: Th e SINR at a receiver nod e j wh en transmitter node i is tran smitting a packet to j is as follows. SINR = P | X i − X j | α N + P k ∈ T , k 6 = i P | X k − X j | α , (1) where N is the noise p ower , X i is the po sition vector o f node i , T is the set of all the nod es that are tran smitting simultaneou sly with n ode i , and α > 2 is the path lo ss exponent. As in [1 ], we assume that the transmit power of all the n odes c an b e scaled with n so that the effects of r eceiv er noise can be ign ored, and the network becomes interfer ence dominated . W e therefo re ignore the t erm N in the denominator of SINR hencefo rth. T wo n odes can com municate with each other if the SINR a t the receiver nod e is gr eater than a certain threshold, say β . I n [1] the au thors assume that if two nod es can com municate with each o ther, then all the tran smitted packets are received error-free. Thus, if ˆ φ ( · ) is the map ping between the SINR and the pro bability of su ccessful packet reception, th en the mod el used in [ 1] is equ iv alen t to th e following. ˆ φ ( SINR ) = ( 1 if SINR ≥ β , 0 otherwise. (2) The k ey contribution of our work is to derive capacity r esults under the following more accurate p hysical layer model. W e assume that the prob ability of a error-free packet reception is a continuo us in creasing functio n of SINR, φ ( · ) that ap proach es unity as the SINR appr oaches infinity . Hence, for e very finite 3 SINR value, there is a n on-zer o probab ility that th e p acket is received in error which amounts to packet lo ss. The results carry over to the case in wh ich th e nu mber o f r etransmissions allowed is finite but fixed, i.e., do not depend on n . Interference model: W e assume that the interferen ce o bserved by a packet over different hops along its path from source to destination is independ ent acro ss all the hops. Note th at the set of in terferers activ e during the transmission of a p acket over different hop s, and the actual packets th at the interfering nodes transmit du ring th ose slots are unlikely to be correlated as the packet moves a long its path. Furthermor e, th e interfering signals th emselves, i.e., the seque nces of bits in th e inte rfering packets can be assumed to be independen t of each other . Hence the assumption of independen ce of interference across multiple hops. Network connectivity and routing: In ord er to en sure con - nectivity , we use the co nnectivity result from [2]. The surface of the sph ere is covered by a V oron oi tessellation in such a way that each V oronoi cell V can be enclo sed inside a circle of radius 2 ρ n , and eac h circ le encloses a circle of r adius ρ n (all the distance s are measure d along the sur face of S 2 ). W e use such a tessellation to en sure un iform cell size. In [2], Gu pta and Kumar have d erived nec essary and sufficient cond itions for asymptotic connectivity of a r andom ad hoc n etwork fo r the case of unit network area. By using results fro m [2] in [1], the authors choo se ρ n to be the radius o f a c ircle o f area 100 log n n on a sphere of unit area . W ith this choice of ρ n , and with the co mmunica tion rad ius of each node chosen to be 8 ρ n , the authors show that all the nod es in th e network ar e connected with pr obability a pproac hing u nity as n ap proach es infinity . Since we consider a scaled up version of the network deployment in wh ich the network area is scaled by a factor n , the same conne ctivity results in [2] are applicable to ou r model with a n ormalization factor of √ n fo r all th e distan ces, and a norm alization factor o f n for all the areas. Hen ce, under ou r model, ρ n is cho sen to be the r adius of a circle of area 100 log n , thereby implying that ρ n = Θ √ log n . W e assume the straight line r outing policy from [1] in which packets are routed along straight line paths b etween sourc e- destination p airs, i. e., ev ery cell that intersects the straig ht line joining a source- destination pair , relays the p ackets of tha t pair . The generalization to handle arbitrary routing is presented subsequen tly . Scheduling Policy: W e first consider the schedu ling policy propo sed in [1], and obtain capacity results under th is policy in Section IV. W e refer to this policy as π 1 . This scheduling policy u ses a vertex-color ing algo rithm to gu arantee tha t each cell gets a transmission opp ortunity at least o nce every K slots, wher e K is a constant that is in depend ent of n . I n o ther words, th e length of the sch edule is bounde d even as n scales. In Section V, we th en pro pose a n ew improved sched uling policy , π 2 that y ields better capacity unde r our p hysical layer model. Th e length o f the schedule u nder π 2 , K n grows as a function of n , I V . C A P AC I T Y U N D E R S C H E D U L IN G P O L I C Y π 1 A N D C O N T I N U O U S φ ( · ) Recall that we assume that φ ( . ) ap proach es un ity continu - ously as the SINR g oes to infinity . Und er this model, we sh ow that the scheduling po licy π 1 used in [1] resu lts in a network capacity of O 1 n . Let L i be the line segment alon g the surface o f S 2 that connects the i - th source-destination pair (hen ceforth referr ed to as the i - th c onnectio n). W e also use L i to deno te the leng th of the line segment joining the i -th source-de stination pair . As per the straight line routing sch eme, the packets of the i -ith connection are rela yed hop-b y-hop by e very cell which intersects line L i . Over e ach h op, any no de in th e re laying cell may forward the packet. The scheduling algorithm , π 1 , and the unifor m cell sizes ensure that commu nication between any two nodes in the neig hborin g cells is possible by gu aranteeing tha t the SINR at the r eceiving n ode is greater than or equal to β (see [1] for mo re details). The following lemmas ar e pr esented without proofs. Lemma 1 : For th e straight lin e routing scheme, the n umber of h ops H i for con nection i is Θ L i ρ n . Mo re p recisely , 1 8 L i ρ n ≤ H i ≤ 16 π L i ρ n . Pr oof: See Appendix B. Lemma 2 : Fix t such tha t 0 < t < 1 . For connection i , out of H i total hops, let h i hops be such that each of these hops covers a d istance o f less than tρ n . Then H i − h i ≥ L i ρ n 1 − 16 t π 8 − t . Thus, for the above H i − h i hops, the signal received at the receiver is at the mo st P ( tρ n ) − α . Pr oof: See Appendix B. In [1], sch eduling policy π 1 was pr oposed to guarantee an SINR of at least β at the receiver of ev ery sch eduled transmission. This scheduling policy correspo nds to a graph coloring prob lem, and it was shown that the maximum numb er of colors req uired to color all the cells is upper b ound ed by 1 + c 1 , where c 1 is a fixed constant that is independen t o f n (see Lemma 4.4 in [1]). Using this schedu ling schem e, each cell gets a transmission op portun ity at least on ce every 1 + c 1 time slots. The following lemm a sho ws that under such a scheduling strategy , except for a small fraction of hops, all th e rem aining hops of a connection rece iv e a cer tain minimum a mount of interferen ce from other simultaneou s tran smissions. Lemma 3 : Fix M > 9 . Let N i be the numb er of hop s of connectio n i such tha t th ere is no simu ltaneous in terfering transmission within a circle of r adius ( M + 8) ρ n around the receivers o f tho se hops. Then, N i ≤ L i ρ n 2(1 + c 1 ) M , where c 1 is th e constant fro m Lemm a 4. 4 in [1]. Pr oof: See Appendix B. Using the above le mma, we have th e following imp ortant result. 4 Pr opo sition 1: The re exist fixed co nstants t 0 and M 0 , that do not depend on n , such that for at least L i / 16 ρ n hops of connectio n i , the SINR is less th an a fixed constant β 0 where β 0 = M 0 + 8 t 0 α . Since φ ( · ) is con tinuous, and the SI NR is upp er boun ded by a fixed constan t β 0 , the pro bability of successful packet reception for th ese ho ps is also uppe r boun ded by a fixed constant φ ( β 0 ) < 1 . Pr oof: See Appendix B. As the nu mber of h ops between sou rce and destinatio n scales to infinity , and as per the above result, a fixed fraction of tho se hop s hav e a c ertain minimu m non- zero packet loss probab ility . Hence, we can show tha t the expected en d-to-e nd throug hput o f a nod e after accoun ting for the packet losses is then gi ven by the following result. Pr opo sition 2: The expected end- to-end throug hput of ea ch node, E [Λ n ] is upper bounded by E [Λ n ] < λ n c 0 log n n , (3) where λ n is the rate at which each node injects packets into the network, and ρ n is the size of the cell (each cell in con tained in a circle o f radius 2 ρ n , and co ntains a circle of radius ρ n ). Pr oof: See Appendix B. When n nodes are distributed ran domly and uniformly over a region, and the region consists of disjoint convex cells (each of area at least 100 lo g n ) su ch that the probab ility o f a node falling in a given cell is at least log n n , then with high probab ility , the number of nodes in each cell is at least 50 log n (see Lemma 4.8 , [1]). More precisely , there exists a sequence δ n → 0 , such that Prob { Numb er of nodes in cell V ≥ 50 log n , for e very cell V in the tessellation } > 1 − δ n . Thus we have the following Lemma fo r the above choice of ρ n . Lemma 4 : If λ n is the rate in p ackets/slot at which every source node injects packets in the network und er sched uling policy π 1 , then with high p robability , λ n ≤ 1 50 log n . Pr oof: The schedu ling alg orithm proposed in [1] guar- antees each cell a time slot at least once every 1 + c 1 slots. Howe ver, since each cell contains at least 50 log n nod es with high p robab ility , e ven if each no de were to tr ansmit only its own packets, an d n ot relay packets, it would still g et no mo re than one transmission oppor tunity every 5 0 log n slots. Hen ce, the rate at which a node injects its own packets into th e network can never be mor e tha n 1 / 50 log n . Using the above Lemma to bound λ n in ( 3), and for a n approp riately defined constant c 1 , we get E [Λ n ] ≤ c 1 n . (4) Thus we have proved the f ollowing main r esult. Pr opo sition 3: Und er scheduling policy π 1 , con tinuous φ ( · ) , and with ρ n chosen to be the radius of a disk of area 100 log n , the per-node thro ughp ut that can b e achieved is O ( 1 n ) . Pr oof: See Appendix B. Remark: The above bound on the thro ughp ut also hold s for a broa d class of ro uting schemes, i.e., Propo sition 3 h olds ev en when the assump tion of straigh t-line routing is r elaxed, (see App endix A for details). V . C A P AC I T Y U N D E R A N E W S C H E D U L I N G P O L I C Y π 2 , A N D C O N T I N U O U S φ ( · ) In this section, we sh ow that if we red uce th e extent of spatial reu se via sch eduling, then we can b ound the end- to-end packet lo ss proba bility , not just the per link packet loss probab ility . This restricts the throu ghpu t re duction due to cu mulative p acket loss. Lemma 5 : For a given ǫ > 0 , if the packet loss probab ility over each lin k is upp er b ound ed by √ π ρ n ǫ 8 √ n , th en u nder straigh t line ro uting p olicy , the cumulative packet loss p robab ility for each c onnectio n is upper bou nded by ǫ . Pr oof: See Appendix B for proof. Note that the above implies that as n scales, in o rder to counter cumulative packet loss, all the links have to be pro gressiv ely more reliable. W e assum e that ρ n = 10 √ log n so that connectivity is achie ved with high pr obability [1]. Lemma 6 : For a given ǫ > 0 , if a sch eduling p olicy ensures that each transmission has an SINR of at least β n ≥ log n , and if the network is large enou gh, i.e., n > 4 5 √ π ǫ , th en each con nection has an end-to- end c umulative packet loss probab ility of n o more than ǫ . Pr oof: See Appendix B for proof. Lemma 7 : For each scheduled tr ansmission o f a cell an SINR o f at least β n = lo g n is guaranteed if all the cells that are within a d istance R n of the given ce ll ar e silent, where R n is g iv en b y: R n = 20 p log n +4 256log n ( α − 2) 1 ( α − 2) ! (5) Pr oof: See Appendix B for proof. Concurren t tran smissions that are at least R n distance apar t can th en b e scheduled using the f ollowing policy . Scheduling po licy π 2 : π 2 : π 2 : Consider the graph in which each cell is r epresented by a vertex. T wo vertices of the graph have an edge b etween th em if and only if their corr espondin g cells are within a distance of R n from each other . Sin ce the area of each c ell is lower bound ed by 50 π lo g n , the nu mber of cells within a distance R n of a cell, and correspo ndingly the maximum degree of a vertex in the correspon ding graph is upper bounded by V n giv en by V n = 8 1 + 4 256log n ( α − 2) 1 α − 2 ! 2 . (6) Since a grap h in wh ich the maximu m degree of a node is k can be vertex colore d using no more than k + 1 color s in polyno mial time [1 7], we use th is algo rithm to vertex color 5 the graph. Th us, the required n umber o f color s is n o more than K n = V n + 1 , which is a f unction of n unlike π 1 where the number of colors is a constant inde penden t of n . Under sched uling policy π 2 we showed that the received interferen ce power is boun ded. Inde ed it can be seen th at fo r a path loss exponent α > 2 a ll r -th moments of the interferen ce for r ≥ 2 are bou nded. Mo reover , sinc e all momen ts exist, the interferen ce satisfies th e large deviations prin ciple, i.e., a momen t generatin g function o f th e interfere nce is w ell defined, an d h ence the distribution function of interfer ence has exponen tially decay ing tail. Hen ce a “good” r ate functio n, I ( x ) , exists by Cramer’ s theorem, i.e. P ( Interferen ce > x ) ≤ e − I ( x ) where lim x →∞ I ( x ) x = ∞ . This implies th at the tail distribution of the interference has at least expo nential decay . This pr operty is sufficient to c onclude that the p acket loss probab ility will also ha ve a g ood rate func tion associated with it sin ce the function o f the SINR is smooth by the c ontraction principle. From th is we can conclude that the re is at least an exponential decay of th e p acket loss probability wh ich is all that we need to e stablish our results 2 . Pr opo sition 4: For a g iv en fixed ǫ > 0 with schedu ling policy π 2 , for a large ne twork, i.e., if n > 4 5 √ π ǫ , each connectio n has an en d-to-en d pac ket loss pro bability of less than ǫ . Pr oof: The pr oof fo llows follows f rom exp onential tail decay . See Appen dix B for p roof W e thus h av e the following main result. Pr opo sition 5: When random packet losses over intermedi- ate links are ta ken into acco unt, the per-node th rough put in an ad h oc network is Ω 1 √ n (log n ) α +2 2( α − 2) , and th e b ound can be achieved under Sched uling Policy π 2 . Pr oof: If ea ch co nnection ge nerates p ackets at a rate of λ n , then from Lemma 4.12 in [1], the total load of tran smitting packets on each cell is up per boun ded by c 5 λ n √ n log n with high prob ability . When the cell gets an oppo rtunity to transmit, it uses the entire b andwidth to transm it at a rate of W bits per seco nd. T hus, with high probab ility , a rate of λ n can be scheduled if the following holds. c 5 λ n p n log n ≤ W K n ⇒ λ n ≤ W c 5 √ n log n a 0 + a 1 (log n ) 1 ( α − 2) + a 2 (log n ) 2 α − 2 (7) using K n = V n + 1 , an d Eq. (6), and wher e a 0 , a 1 , an d a 2 are constants that do not d epend on n . 2 Note that if we can sho w that the moment gene rating function, M ( t ) , of the interfe rence is such that l og M ( t ) is diff erentia ble for all t , the rate functio n is strictly con vex [18], and the tail fall-of f of e − x 2 can be obta ined. In this case, we only need to ensure an SINR of √ log n instead of log n , and the capa city bound can be impro ved. Ho we ver , in order to prove that log M ( t ) is dif ferenti able it is necessar y to explici tly compute al l the r -th moments of the interferen ce term. The good put after a ccountin g fo r cumulative packet losses is th en g iv en by: E [Λ n ] = (1 − ǫ ) W c 5 √ n log n a 0 + a 1 (log n ) 1 ( α − 2) + a 2 (log n ) 2 α − 2 = Ω 1 √ n (log n ) α +2 2( α − 2) ! . (8) V I . R E L A T E D W O R K In their seminal work on the capacity o f wireless n etworks [1], Gupta and Kumar u sed a simplified link layer model in which each packet reception is successful if the rec eiv er has an SINR of at least β . For th is comm unication model a nd und er the random network m odel, th e author s prop ose a ro uting and sched uling strategy , and show that a per-node thr oughp ut of Θ 1 √ n log n can be ach iev ed. The autho rs also consider another m odel of ad ho c network s called ar bitrary ne tworks. In an arb itrary network , nod es are placed at a rbitrary loca tions in a region of fixed area, source-destinatio n p airs are chosen arbitrarily , an d each no de can transmit at an arbitrary power lev el. This is unlike a random ad hoc network wh ere no de are deployed random ly and unifor mly , source-destinatio n pairs ar e chosen at random, and all the nodes transmit at the same po wer lev el 3 . For the arbitrary network model, the authors sh ow th at a per-node th rough put of Θ 1 √ n is a chiev able. However , fo r random networks, the routing and scheduling scheme proposed in [1 ] o nly achie ves a th rough put of Θ 1 √ n log n . The gap betwee n th e ar bitrary networks a nd the ra ndom networks is closed in [ 7]. In [7], the auth ors note that the requirem ent of conn ectivity with high pr obability in random networks as required in [1], requires higher transmission po wer at all the nodes, and results in excessi ve interfer ence. This in turn lowers the thro ughp ut of rand om ne tworks fro m Θ 1 √ n to Θ 1 √ n log n . Motiv ated by this, the authors in [7] propose using a backbon e-based relay ing scheme in which instead of ensur ing connectivity with prob ability one, they allow for a small fra ction o f nodes to be disco nnected f rom the backbo ne. The nodes in the backbon e are densely con nected, and can commu nicate over each hop at a co nstant rate. Such a backb one traverses up to √ n hop s. The no des that are not a p art of the back bone, send their packets to the back bone using single h op communic ation. The authors then show that the in terferenc e caused by th ese lon g rang e transmissions d oes not imp act the traffic carryin g capacity of the b ackbon e nodes. Finally , the auth ors s how that the relaying load of the backbo ne determines the per-node thr ough put of such a scheme, and this results in an achiev ab le pe r-node thr ough put of Θ 1 √ n . Howe ver, as in [1], the author s in [7] do no t take into account the impact of cumulative packet loss . The approach of allowing a few disco nnected nod es in the n etwork has also been u sed in [8]. Capacity o f ad hoc networks und er coo perative r elaying 3 The definit ions of random networks and arbit rary networks have been tak en from [1]. 6 is studied in [14] wh ere instead of decode and fo rward m odel, node ar e clustered in MIMO configuration s. In [3], the auth ors discuss the limitations of the work in [1] b y taking a network in formatio n theoretic approach . The authors d iscuss how se veral coop erative strategies suc h as interferen ce cancellation, network co ding, etc. could b e used to improve the th roug hput. Th e authors also discu ss how the prob lem of dete rmining the network capacity from an informa tion theoretic view-point is a difficult prob lem, since ev en the capacity of a three node relay n etwork is unk nown. In Theorem 3.6 in [3], the au thors determine the same b ound on the capacity of a ra ndom network as obtained in [1]. All the above works do n ot take into acco unt the capacity r eduction due to cu mulative packet loss which is the focus of o ur work. In addition to the abov e works, the capacity of ad hoc networks has also been in vestigated under additional assumptions such as no de mo bility and capacity-de lay trade-offs [9], network informa tion theoretic vie w of network capacity [3], etc. V I I . C O N C L U S IO N Our resu lts show that idealized modeling a ssumptions c an lead to optimistic conclu sions, and h ence f or scaling tech- niques to provide u seful g uidelines it is important to u nder- stand the limitations of the underly ing assumptions. The key observation in this paper is that for a bro ad range of ro uting and sch eduling schemes ( including the one pr oposed in [1]), the num ber of hops of each co nnection scales to in finity with n . In a realistic link layer mod el, for a given modulation an d coding scheme, the probab ility of packet loss over any gi ven link is non -zero fo r finite SINR values. With the above link layer m odel, w e show that fo r a bro ad class of routing and scheduling policies we cannot achiev e a pe r-node thr ough put of mor e than O 1 n due to the cumu lativ e p robab ility o f packet loss over all the ho ps of the c onnection . However , it is p ossible to improve the link SINR b y using a more conservati ve scheduling p olicy with a lower spatial reuse. I n this case the per -nod e th rough put is Ω 1 √ n (log n ) α +2 2( α − 2) . This bound is achievable under the prop osed scheduling policy . A C K N OW L E D G ME N T S This w ork was s uppo rted in part by the Natural S ciences and Engineer ing Research Council of Canada (NSERC), the Na- tional Science Foundation (NSF), and a grant from Research in Motion ( RIM). W e would also like to th ank Prof . Ness Shroff (Ohio State University , USA) f or his valuable su ggestions that greatly helped us improve the q uality of this manuscript. A P P E N D I X A : C A P A C I T Y U N D E R S C H E D U L I N G P O L I C Y π 1 , C O N T I N U O U S φ ( · ) A N D A R B I T R A RY RO U T I N G In Section IV, w e saw that when straigh t line rou ting (prop osed in [1]) is u sed, the p er-node throughp ut is O 1 n . In this section, we show that this bound on the through put also holds f or a broad class of routing sche mes, i.e., Pro position 3 holds even when th e a ssumption of straight-line rou ting is relaxed. In this section, our goal is to inv estigate if a higher per-node throug hput can be achieved if we choo se routing paths intelligently , i. e., n ot necessarily straight lin e paths between source-de stination p airs. W e only consider those routing paths in which multi- hop commu nication takes place throug h packet-relaying be tween ad jacent cells, and there are no loo ps in the routin g path. The first condition is to ensur e that co mmunica tion is not possible betwee n two no des if they do not belo ng to adjacent cells, while the second condition ensures that a packet does not v isit a cell more than once on its path from source to de stination. Note that even with this restriction, we can account for a vas t range of routing schemes. Let us assum e that a packet of con nection i takes a certain path (not necessarily straight lin e pa th) f rom the source node to the destination node. Let ˆ L i be the length of this path, i.e., the actu al distance traveled by the packet a long the surface of S 2 . Then we have the following Le mma which is essentially a gen eralization of Lemma 2 . In this Lemma, we show that at least a fixed fraction of hops for any routing scheme are ov er a distance of tρ n or lo nger for a fixed t > 0 . Lemma 8 : Fix W = 40 , and t = 0 . 01 . Assume any arbitrary routing path such th at R1 Each hop is between nodes of two adjac ent cells, R2 There are no loops in the routing path . Then, under scheduling policy π 1 , and R1 and R2, we cannot have W consecu tiv e hop s of distanc e tρ n or less . In other words, for any rou ting scheme that satisfies R1 and R2, at least one out o f every W con secutive hops is at least tρ n long. Pr oof: See Appendix B. In the n ext L emma, we show that except f or a small fraction of hops, all other hop s have at least one conc urrent transmission within a distance of ( M + 8) ρ n of the receiver , and this f raction c an b e m ade arb itrarily small by cho osing M large enoug h. Lemma 9 : Fix M > 16 . Consider an arbitrary routing path between sou rce a nd de stination no des such that R1 and R2 ar e satisfied. Under sch eduling policy π 1 , let N i be the n umber of hops of connectio n i such that ther e is no concurr ent transmission within a circle of r adius ( M + 8) ρ n around the receivers of th ose h ops. T o avoid tedious b ound ary conditio ns, let us no t count the h ops containing the source an d th e destination n odes in N i . Then, N i ≤ ˆ L i ρ n 2(1 + c 1 ) M , where ˆ L i is the length of the routing path and c 1 is the constant from Le mma 4.4 in [1]. Pr oof: See Appendix B. Analogou s to Propo sition 1 in Section IV, we have the following result f or the arb itrary routin g mod el. Pr opo sition 6: The re exists a fixed constant M 0 , that do es not dep end on n , such that for at least ˆ L i / 640 ρ n hops of connectio n i , the SINR is less than a fixed constant β 1 giv en by β 1 = 1 00 α ( M 0 + 8) α . Since the SINR is u pper boun ded by a fixed constant β 1 , the probab ility of successful packet reception is also up per bound ed by a fixed constant φ ( β 1 ) < 1 . 7 L i 4 ρ n 4 ρ n 8 ρ n S D Fig. 1. Bounding the number of hops H i for connection i . Pr oof: See Appendix B. W e can now u se the ab ove Propo sition, an d procee d as in Section IV to determin e th e en d-to-en d thro ughp ut of a connectio n. For this, we note that a t least ˆ L i / 640 ρ n hops of connectio n i ha ve an S INR that is upper boun ded by a constant β 1 , i.e., a packet success pr obability that is upp er bou nded by a constant φ ( β 1 ) . Hence, replacing L i by ˆ L i in (13) to (1 6) we obtain the through put a co nnection as E [Λ n ] ≤ λ n E L h δ ˆ L i i . Recall that L i denotes th e length of th e straig ht line joining the source-d estination n ode pair of con nection i , and hen ce ˆ L i ≥ L i . Also, since δ ≤ 1 , we get E [Λ n ] ≤ λ n E L δ L i . After this stage, we u se (17), an d pro ceed along the sam e lines as Section IV, an d obtain the same asy mptotic upp er bound of O 1 n as in Prop ositions 3. Pr opo sition 7: For any choic e of ρ n that satisfies the con- nectivity r equirem ents in [2], and for any routin g sch eme that satisfies R1 and R2, the per-node th rough put that c an be achieved under sched uling po licy π 1 is O ( 1 n ) . Thus the asym ptotic per-node thro ughpu t is O 1 n ev en with arbitr ary r outing, demo nstrating that the impact of cu- mulative p acket loss out-weighs in telligent r outing. A P P E N D I X B : D E TA I L E D P RO O F S Pr oof of Lem ma 1 Since each V oronoi cell is co ntained in a circle of radius 2 ρ n , th e m aximum d istance betwee n a poin t in a g iv en cell, and a point in a neighb oring cell is 8 ρ n (see Fig . 1). T hus, over each hop, the maximum d istance that a p acket can cover is u pper bounded by 8 ρ n . Hence the lower boun d. For the up per boun d, if we lo ok at a strip that is 4 ρ n wide on eith er sides of L i (see Fig . 1), we observe that if a cell is used as a r elay cell, then it mu st lie entir ely within this strip. This is because each cell is completely c ontained inside a circle of diam eter 4 ρ n . Th e area of this strip is 8 ρ n L i . Each cell contains a circle o f radius ρ n , and hence the area o f each cell is at least π ρ n 2 / 2 (see Lemma 1 1 in Append ix). T hus, the m aximum nu mber of cells th at lie entirely within this strip is u pper bounded by 16 L i /π ρ n . Hen ce the upp er bou nd. The lower b ound is actually max L i 8 ρ n , 1 , but with L i = Θ( √ n ) , an d ρ n = Θ √ log n , an d we can ignore on e. In any case, we requ ire the upper bound , and not so much the lower bound in our subseq uent ana lysis. Also note, that for a more exact u pper bound, we should consider a strip of length L i + 4 ρ n + 4 ρ n instead of L i , since the so urce and d estination nodes cou ld be loca ted at the periph eries o f their respective cells. Howe ver, since L i is Θ ( √ n ) , and ρ n = Θ √ log n , we can safely ignore the two ter ms cor respond ing to the sizes of th e source and destination cells. Pr oof of Lem ma 2 Since h i hops each cover less than tρ n distance, the leftover distance, which is at least L i − h i tρ n has to be covered by the rest o f the H i − h i hops. Eac h of these H i − h i hops can cover a distance of at the most 8 ρ n . Hen ce, we have ( H i − h i ) 8 ρ n ≥ L i − h i ( tρ n ) ⇒ h i ≤ H i 8 8 − t − L i ρ n 1 8 − t ⇒ H i − h i ≥ H i − t 8 − t + L i ρ n 1 8 − t ≥ L i ρ n 16 π − t 8 − t + L i ρ n 1 8 − t , where we have used Lemma 1 to up per b ound H i on the righ t hand side in the last step. Thus, H i − h i ≥ L i ρ n 1 − 16 t π 8 − t . Pr oof of Lem ma 3 T o av oid tedious boun dary cond itions, let us not count the hops contain ing th e sour ce and the d estination nodes in N i . There are at the most 1 + c 1 colors, i.e., ea ch cell gets a transmission opportu nity a t least once every 1 + c 1 time slots. Let u s in dex these 1 + c 1 colors, an d c onsider a ny on e of these colors, say color j . W e would like to determine the nu mber of c olor- j cells of conn ection i that ar e at least M ρ n distance away from o ther color- j cells. For this, let U j i be the set o f all the cells of color j that a packet of conne ction i trav erses. W e refer to a circle as a “surroun ding c ircle of a c ell” if its center lies within th e cell . Consider all th e su rroun ding circles o f radius M ρ n around each of the ce lls in set U j i . For each cell, th ere are many such circles, since the o nly re quiremen t is that th e cen ter of th e circle lie w ithin the cell. A sub set V j i of U j i is then formed as follows. A cell from set U j i is added to set V j i if none o f its surroun ding cir cles of rad ius M ρ n contains any other colo r- j cell eith er par tially or fully . Th us e very cell in set V j i is at least M ρ n distance a way fro m any other colo r- j cell. Hence, any surround ing circle of radius M ρ n 2 around a cell in set V j i does not overlap with any surro undin g cir cle of ra- dius M ρ n 2 around an other cell in set V j i . Let th ere be N j i cells in set V j i . The total length of the path is L i (referrin g to Fig. 2). W e would like to determ ine the maximum n umber of non - overlapping surr ound ing circles o f radius M ρ n 2 around color- j cells th at can b e accommodated alo ng L i . This number is an 8 4 ρ n L i S D M ρ n 2 Fig. 2. Bounding the number of hops N j i of connec tion i with color j for which there is no interfer er withi n a distance ( M + 8) ρ n from the recei ver . upper boun d for N j i . Each cell along L i can be enclosed inside a circ le of diam eter 4 ρ n . Refer ring to Fig. 2, maximal p acking of the n on-overlappin g circles of ra dius M ρ n 2 occurs wh en the chord for med by the inter section of L i with the se circles is of minimal len gth. If the diam eter of th e circle encom passing the cell lies above ( below) L i , the cell ca n be shifted up (down) by at most 2 ρ n and still in tersect L i . Maximal p acking occurs when each cell tange ntially touches L i , so that we select a point in that cell 4 ρ n away fr om L i , and draw a circle of radius M ρ n 2 centered at that po int. Th e length of each chord formed b y the in tersection o f L i and the su rroun ding circle of radiu s M ρ n 2 is at least 2 r M ρ n 2 2 − (4 ρ n ) 2 ! , which in turn is at lea st M ρ n 2 if M > 9 . Since N j i such chord s are to be acc ommod ated along the length of the path, N j i M ρ n 2 ≤ L i ⇒ N j i ≤ 2 L i M ρ n . Therefo re for all the colors, N i = 1+ c 1 X j =1 N j i ≤ L i ρ n 2(1 + c 1 ) M . Thus except for these N i hops, ea ch o f th e h ops of con nection i has at least one cell th at has a simultaneous ongoing transmission within a rad ius o f M ρ n of the given cell. Or equiv alently , within a r adius of ( M + 4 + 4 ) ρ n = ( M + 8) ρ n of the r eceivers of these hops, there is at least one more node that is transmitting simultaneo usly . This is bec ause the maximum size o f a cell is 4 ρ n . And this proves the result. Pr oof of P r opo sition 1 Let A i be the set of hop s of conn ection i for wh ich the received signal is at the most P ( tρ n ) − α . Th en, given ǫ 1 > 0 , we can find t > 0 small e nough so that using Lemma 2, | A i | ≥ L i ρ n 1 8 − ǫ 1 . (9) Let B i be the set of hops of c onnection i for which there is no simultan eous tran smissions with in a d istance of ( M + 8) ρ n of the receiver . Using Lemma 3, | B i | = N i , and g iv en ǫ 2 > 0 , we can choo se M large eno ugh so that | B i | ≤ L i ρ n 2(1 + c 1 ) M ≤ L i ρ n ǫ 2 . (10) Thus using (9) and ( 10), | A i ∩ B i c | ≥ | A i | − | B i | ≥ L i ρ n 1 8 − ǫ 1 − L i ρ n ǫ 2 = L i ρ n 1 8 − ǫ 1 − ǫ 2 . If we pick ǫ 1 = ǫ 2 = 1 / 32 , a nd choose t = t 0 and M = M 0 correspo nding to this choice of ǫ 1 , ǫ 2 , then | A i ∩ B i c | ≥ L i 16 ρ n . (11 ) Note that A i ∩ B i c is the set of hops over wh ich the received signal is n o mo re than P ( t 0 ρ n ) − α , and there is at least one simultaneou s tr ansmission within a distance o f ( M 0 + 8) ρ n of the receiv er . This in tur n m eans that for th ese hops, the SINR is u pper b ound ed by S I N R ≤ P ( t 0 ρ n ) − α P (( M 0 + 8) ρ n ) − α = M 0 + 8 t 0 α = β 0 . (12) Pr oof of P r opo sition 2 Let λ n be the r ate in packets/slot a t wh ich e very source node in jects packets in the network . Altho ugh the so urce node injects p ackets at a rate of λ n packets per slot, n ot all the packets m ake it to the destination node. This is becau se, at each h op, th e SI NR is finite, and hence th ere is a non- zero probab ility o f the packet getting drop ped. The actual end -to- end throug hput of the conn ection, d enoted by Λ n is given by , Λ n = λ n Prob { packet is received successfully over all the ho ps of connectio n i } = λ n Π H i j =1 Prob { packet is received successfully over the j th hop of conn ection i } , where we assum e that the in terference and no ise observed by a packet at each of the ho ps are indep endent. W e know from Proposition 1 that, a mong the H i hops of conn ection i , at least L i / 16 ρ n hops h av e a probab ility of p acket success o f no m ore than φ ( β 0 ) . Thus, Λ n ≤ λ n { φ ( β 0 ) } L i 16 ρ n . (13) Note th at L i are i.i. d. random variables. Hen ce if we remove the cond itioning o n L i by takin g the expectation with respect to L i , the end- to-end thro ughp ut E [Λ n ] is, E [Λ n ] = E L [Λ n ] (14) ≤ λ n E L { φ ( β 0 ) } 1 16 ρ n L i (15) = λ n E L δ L i . (16) where we have substituted δ = { φ ( β 0 ) } 1 16 ρ n . Note th at in determinin g the average end- to-end th roug hput E [Λ n ] , we take expectation s at two levels ; once to take into acco unt 9 ( W t + 4) ρ n P W tρ n C 2 C 1 Fig. 3. Bounding the number of hops of length tρ n or less. the ra ndomn ess due to the po ssibility of packet error on each link, and once to take into accoun t the rand omness du e to the locations of the source and destination nodes. Also n ote that 0 < δ < 1 . Since L i is a line conn ecting two po ints picked at random on the surface o f S 2 , we can show that (See Lemma 10 in App endix). E L δ L i = 2 π 1 + δ √ πn 2 4 π + n (log δ ) 2 . (17) Using ( 16) and (1 7), E [Λ n ] ≤ λ n 2 π 1 + δ √ πn 2 (4 π + n (log δ ) 2 ) = λ n 2 π 1 + { φ ( β 0 ) } √ πn 32 ρ n 4 π + n 1 16 ρ n log φ ( β 0 ) 2 = λ n 512 π ρ n 2 1 + { φ ( β 0 ) } √ πn 32 ρ n (102 4 π ρ n 2 + n (log φ ( β 0 )) 2 ) < λ n 1024 π ρ n 2 (1024 π ρ n 2 + n (log φ ( β 0 )) 2 ) , since φ ( β 0 ) < 1 . < λ n 1024 π ρ n 2 n (log φ ( β 0 )) 2 ≤ λ n c 0 log n n , sinc e ρ n = Θ p log n . Pr oof of Lem ma 8 By way of contrad iction, assume that there exists some routing scheme th at satisfies the co nnectivity requirem ents in [2], along with R1 and R2, and has W consecutive h ops, each of length tρ n or less. Referr ing to Fig. 3, let point P be th e initial location of the pac ket, and assume that th e packet traverses W ho ps from this position. Sin ce each of these hops is less than tρ n , the final location of the packet after traversing these W hops is insid e a cir cle of ra dius W tρ n centered at P . Let C 1 be this circle. Clearly , ev ery cell th at the packet traversed during these W hop s must intersect c ircle C 1 . Otherwise, the p acket could not hav e traversed that cell. W e can easily find an upp er b ound on the nu mber of ce lls that intersect C 1 as follows. Con sider anoth er circ le C 2 of radius l i, 2 ( j ) M ρ n 2 l i, 1 ( j ) l i, 3 ( j ) Fig. 4. Arbitrary routing path. ( W t + 4 ) ρ n centered at P . If a cell intersects C 1 , it should lie completely in side circle C 2 . This is because the distance between any two po ints of a cell canno t exceed 4 ρ n , and if a cell has at least one point inside C 1 , its other point cannot be more than 4 ρ n farther fr om the circum ference of circle C 1 . The nu mber of cells that lie co mpletely inside C 2 , de noted by n 2 is u pper b ound ed as follows n 2 ≤ π (( W t + 4) ρ n ) 2 π ρ n 2 2 = 2 ( W t + 4) 2 , (18) where we have used Lemma 11 in the first step. For W = 40 and t = 0 . 01 , we have n 2 ≤ 38 . 72 . Since 40 hop s req uire at least 41 u nique cells, and ther e are only up to 38 unique cells that th e packet can visit, we c learly have a contradiction. Thus, there doe s n ot exist a routing sch eme that satisfies, R1 and R2, a nd that has W con secutiv e hops of tρ n or less, w here W = 40 , and t = 0 . 01 . Note that the arguments in the above Lemma are easier to understan d in case of simp le tessellation s such a s triangular, square, hexagonal, e tc. For example , con sider a squ are tessel- lation ( square-sh aped cells), su ch that each side of the cell is 2 ρ n long. Thus, each cell co ntains a circle of radius ρ n , and is contained in a circle of radiu s 2 ρ n . In this case, it is easy to see that circle C 1 defined in Lemma 8 cannot intersect more than 4 circles, and this hap pens in th e neig hborh ood of one of the vertices of the tessellation. Consequently , for a square tessellation, we cannot have 4 consecutive hops, each of len gth 0 . 01 ρ n or less. In fact, th e u pper bo und could b e made tigh ter by noting th at ther e cannot b e m ore than 4 consecutive h ops that are strictly less than 0 . 5 ρ n . Sim ilarly , for a hexagon al tessellation such tha t each cell h as side s of length 2 ρ n , we cannot h av e 3 consecu ti ve hops, each of leng th strictly less than 0 . 5 ρ n . Thus th e value o f W is m uch smaller, and the value of t is much larger fo r simp le tessellations. Howe ver when we con sider genera l tessellations that satisfy the co nnectivity requirem ents, we note that the tessellation need n ot be as well-behaved as square or hexagona l. Y et, we ca n obtain an upper bound on the maximum num ber of successiv e hop s of arbitra rily small len gths. T o do this, we need to c hoose a fairly large (but fin ite and fixed) W , and a fairly small (but positive and fixed) t . Pr oof of Lem ma 9 W e use an app roach iden tical to th e o ne used to prove Lemma 3. L et U j i be the set of a ll th e cells of color j that a 10 M ρ n 2 − 4 ρ n 4 ρ n Fig. 5. Bounding the number of hops N i of connect ion i for whic h there is no interferer within a distance ( M + 8) ρ n from the recei ver with arbitrary (not straight line) routing. packet of connection i trav erses. Consider all the surroun ding circles of radius M ρ n around each of th e cells in set U j i . For each cell, th ere are many such circles, since the only requirem ent is tha t the center of the circle lie within the cell. A subset V j i of U j i is then f ormed as follows. A cell fro m set U j i is added to set V j i if none of its sur round ing circles of radius M ρ n contains any o ther colo r- j cell either partially o r fully . Th us every cell in set V j i is at least M ρ n distance away from any other colo r- j cell. Hence, any su rroun ding circle of radius M ρ n 2 around a cell in set V j i does no t overlap with any surro unding circle of radius M ρ n 2 around another cell in set V j i . Let th ere be N j i cells in set V j i , a nd let N i be the sum o f the number of cells in V j i for all j . W e w ould like to determine an upper bound o n N i . Referring to Fig. 4, consider the path taken b y a p acket of connectio n i (solid line in the figure). The p ath is piece -wise linear, with the lo cations o f th e relaying node o f each hop as points of discontinuity . Let ˆ L i be th e length of this ro uting path. Le t us rearran ge the cells in set V j i in th e or der in which a pack et of connec tion i traverses the m , and join them in this order (dotted lines in Fig. 4). Let l i,k ( j ) be the length of the k th do tted line segment. Define ˆ L ′ i ( j ) to be the total length o f the dotted path. Then we have ˆ L ′ i ( j ) = X k l i,k ( j ) ≤ ˆ L i . (19) Consider a typical cell in set V j i as shown in Fig. 5. As in the proof of Lemma 3 , we first determine th e length of the minimum po ssible section of the r outing path (in this case the dotted path ) that lies inside the surr oundin g cir cle. Since we know the to tal leng th o f th e d otted path , th is g iv es us an u pper bound on the nu mber su rroun ding circles of radius M ρ n 2 that can b e accommodated along the do tted p ath. Referring to Fig. 5, the dotted path has its smallest sectio n inside the surrou nding circ le of radius M ρ n 2 when the relaying node of th e cell, i. e., the po int of discon tinuity of the dotted path is located as close as possible to the circumferen ce of the circle. Howev er, sinc e this po int belongs to th e cell, it cannot be farther than 4 ρ n from any other point in the cell. But the center of the surro unding c ircle must also lie inside the cell. Hence the point of discontin uity can be at the most 4 ρ n away from the ce nter of the circle . Hence the each po rtion of the dotted path tha t lies within the circle can be no shor ter than M ρ n 2 − 4 ρ n . Thus, f or each c ell in V j i , a t least ( M − 8) ρ n portion of the do tted path mu st lie insid e the surroun ding circle. Let M − 8 > M 2 , i.e., M > 16 . Then the maximum number o f such sur round ing circles that ca n b e accomm odated along the dotted path, i.e., the max imum number of cells in set V j i is: N j i M ρ n 2 ≤ ˆ L ′ i ⇒ N j i ≤ 2 ˆ L ′ i M ρ n . Therefo re for all the colors, N i = 1+ c 1 X j =1 N j i ≤ ˆ L ′ i ρ n 2(1 + c 1 ) M ≤ ˆ L i ρ n 2(1 + c 1 ) M using (19). Thus except for these N i hops, each o f the h ops of co nnection i h as at least on e cell th at ha s a simultaneous on -going transmission within a rad ius o f M ρ n of the given cell. Or equiv alently , within a r adius of ( M + 4 + 4 ) ρ n = ( M + 8 ) ρ n of the r eceivers of these hops, there is at least one more node that is transmitting simultaneously . This is because the maximu m size o f a cell is 4 ρ n . And this proves the result. Pr oof of P r opo sition 6 For any routing p ath, th e number of hops is lower bo unded by ˆ L i 8 ρ n , since each hop can trav erse a d istance of at the most 8 ρ n . Lemma 8 shows that at least 1 40 th of these ho ps, i.e. , at least ˆ L i 320 ρ n hops of conn ection i ha ve tran smitter-recei ver pair separated by 0 . 01 ρ n or mor e. As in Section IV, let A i be the set of h ops of connec tion i for which the received sig nal is at the m ost P (0 . 01 ρ n ) − α . Then, | A i | ≥ ˆ L i 320 ρ n . (20) Let B i be the set of ho ps of co nnection i for which th ere is no simultan eous tran smissions within a distance of ( M + 8) ρ n of th e recei ver . Using Lemm a 9, given ǫ > 0 , we can cho ose M large enough so that | B i | ≤ ˆ L i ρ n 2(1 + c 1 ) M ≤ ˆ L i ρ n ǫ. (21) Then usin g (2 0) and (21), | A i ∩ B i c | ≥ | A i | − | B i | ≥ ˆ L i ρ n 1 320 − ˆ L i ρ n ǫ = ˆ L i ρ n 1 320 − ǫ . If we pick ǫ = 1 / 6 40 , and choose M = M 0 correspo nding to this choice of ǫ , | A i ∩ B i c | ≥ ˆ L i 640 ρ n . (22) 11 Note that A i ∩ B i c is the set of hops over which the r eceived signal is no m ore than P (0 . 01 ρ n ) − α , and there is at least one simultaneou s tr ansmission within a d istance of ( M 0 + 8) ρ n of the receiv er . This in tur n m eans that for these hops, th e SINR is u pper bounded by S I N R ≤ P (0 . 01 ρ n ) − α P (( M 0 + 8) ρ n ) − α (23) = 100 α ( M 0 + 8) α = β 1 . The above up per bound on SINR may seem large du e to the 100 α term. Howe ver, this ter m appears because we picked u p a co nservati ve hop length of 0 . 01 ρ n in proving Lemma 8 to account for all possible tessellations. For simple tessellations such as square and hexagon al, we can use a minimum hop length of ρ n , and obtain a tigh ter boun d o n SINR. Howev er , as far as the asymptotic nature of the solution is concern ed, the v alues o f th ese con stants do not matter . Pr oof of Lem ma 5 P ( { End-to -end packet loss on co nnection j } ) = P ( ∪ i { Packet loss on link i o f c onnection j } ) ≤ X i P ( { Packet loss on link i of connection j } ) ≤ X i √ π ρ n ǫ 8 √ n = √ π ρ n ǫ 8 √ n · H j ≤ √ π ρ n ǫ 8 √ n · 16 π L j ρ n , using Lemma 1. ≤ ǫ , since L j is upper bound ed by √ π n 2 , half the circumferen ce o f the sphere of area n . Pr oof of Lem ma 6 Assuming that the inter ference observed at a node has tail error pro bability , P e that falls of expon entially with SI NR, for a giv en ǫ > 0 , using L emma 5 we require a minimum SINR of β n for all the links su ch that P e ( β n ) ≤ √ π 8 √ n ρ n ǫ = 5 √ π 4 r log n n ǫ. Since for large x , P e ( x ) can be upper bounded by e − x , we have for x = β n = lo g n , P e (log n ) = e − log n = 1 n ≤ 5 √ π 4 r log n n ǫ, for n large. Thus, if a scheduling p olicy en sures an SINR of at lea st β n = log n , then an end-to-e nd packet loss proba bility of ǫ can be guaran teed for a given ǫ > 0 using Le mma 5. Pr oof of Lem ma 7 Consider an arb itrary c ell C i . Fix the o rigin to be the center of this cell, i.e., the co mmon center of the circles of r adii 20 √ log n and 10 √ log n that respectively contain, and are contained in the cell. Con sider a rin g of thickne ss dr a t a distance r from the center . Since th e area of each cell is lower bound ed by 50 π log n , the n umber of cells within this r ing can be no more than r dr 25 log n . Even if all these cells are tran smitting concur rently , the total inter ference received at the center o f C i , and denoted by I i is u pper b ound ed as follows. I i ≤ ∞ Z R n rdr 25 log n · P r − α = P R − α +2 n 25 log n ( α − 2) . Since each cell is con tained inside a circle o f radiu s 20 √ log n , the maximu m sep aration between a transmitter and a receiv er that lie in adjacent cells is 80 √ log n . Hence the SINR in cell C i is g reater than log n if R n satisfies the following. P · 80 √ log n − α P R − α +2 n ( α − 2)25 log n ≥ lo g n ⇒ R n ≥ 8 0 256 ( α − 2) 1 α − 2 (log n ) α 2( α − 2) . The above ensu res that SINR at the cen ter o f c ell C i is g reater than lo g n . T o ensure an SINR of at least log n ev erywher e in C i , we note th at the farthest distance to th e cell edge from center is 20 √ log n . Thus, we require R n ≥ 2 0 p log n + 80 256 ( α − 2) 1 ( α − 2) · (log n ) α 2( α − 2) = 2 0 p log n 1 + 4 256log n ( α − 2) 1 ( α − 2) ! Lemma 1 0: I f we pick tw o poin ts randomly and unifo rmly on the surface of sph ere S 2 of a rea n , and connect them by a line (drawn alon g the su rface of S 2 ), and if L is the r andom variable co rrespon ding to the length of this line, then fo r 0 < δ < 1 , E δ L = 2 π 1 + δ √ πn 2 4 π + n (log δ ) 2 . Pr oof: Since both the points are picked randomly and unifor mly on the surface of S 2 , without loss o f gener ality , assume that one point is located at the north pole of the sphere. Then, we can find the pro bability that the other point is located within a distance of l fr om th e north pole. This is the sam e as the event A = { L ≤ l } , and its pro bability equals the ratio of the ar ea of the shaded region in Fig. 6 to the area of the sphere, wh ich is o ne. Note that all the distances are measu red along th e surface of the sphere. W e hav e, Area { Shad ed region } = n 2 1 − cos 2 √ π l √ n . (24) Therefo re the distrib ution f unction of L , i.e., F L ( l ) is F L ( l ) = 1 2 1 − cos 2 √ π l √ n . 12 l { L ≤ l } √ n 2 √ π Fig. 6. Probability distrib ution of L . Note th at 0 ≤ L ≤ √ π n/ 2 . Th e den sity fu nction of L is given by , f L ( l ) = √ π √ n sin 2 √ π l n . Now we can co mpute E [ δ L ] as fo llows. E δ L = √ πn 2 Z 0 δ l √ π √ n sin 2 √ π l √ n dl = 1 2 π Z 0 γ x sin xdx , where γ = δ √ n 2 √ π = 1 2 I . (25) Solving f or I using integration by parts, I = 1 + γ π 1 + (log γ ) 2 . Replacing γ b y δ 1 2 √ π , and substitutin g th e above in (25), E δ L = 2 π 1 + δ √ πn 2 4 π + n (log δ ) 2 . (26) Using (24) f rom the above Lemma, we also have the following lemma for the area of a disk of radius ρ n on S 2 . Lemma 1 1: If ρ n is the ra dius of a d isk (measured along the surface of S 2 ), th en π ρ n 2 2 ≤ a n ≤ π ρ n 2 . (27) Pr oof: Using (24) with l = ρ n giv es a n = n 2 1 − cos 2 √ π ρ n √ n = sin 2 r π n ρ n . For θ ≤ π / 4 , θ √ 2 ≤ s in θ ≤ θ . From this, (27) follows if n is large e nough so that ρ n ≤ √ π n/ 4 . T he latter is always true, since the √ π n/ 4 is the radius of a hem isphere on S 2 (measured alon g the surface of S 2 ), an d h ence the rad ius of the largest disk o n S 2 . R E F E R E N C E S [1] P . Gupta and P . R. Kumar , “The capacity of wireless netw orks, ” IEEE T ransaction s on Information Theory , vol. IT -46, no. 2, pp. 388-404, March 2000. [2] P . Gupta and P . R. Kumar , “Critica l power for asymptotic connecti vity in wireless networks, ” in Stoc hastic A nalysis, Contr ol, Optimizat ion and Applicat ions: A V olume in Honor of W . H. Fleming , W . M. McEneaney , G. Yi n, and Q. Z hang (Eds.), Birkhauser , Boston, 1998. [3] Liang-Liang Xie and P . R. Kumar , “ A netw ork information theory for wireless communicat ion: Scaling laws and optimal operation , ” IEEE T ransaction s on Information Theory , V ol. 50, No. 5, May 2004. [4] M. Grossglauser and D. Tse, “Mobility increa ses the capacity of adhoc wireless networks, ” IEEE /AC M T ransacti ons on Networking , vol. 10, no. 4, August, 2002, pp. 477-486. [5] B. Liu, Z. Liu, and D. T owsle y , “On the capacity of hybrid wireless netw orks, ” in Proceeding s of IEE E INFOCOM’03, , V ol. 2, pp.1543- 1552, April 2003. [6] A. E . Gamal, J. Mammen, B. Prabhakar , and D. Shah, “Optimal throughput -delay scali ng in wireless netwo rks: part I: the fluid model, ” IEEE/ACM T ransact ions on Network ing , Specia l issue on Networ k- ing and Informati on Theory , V olume 14, pp.2568-2592, June 2006. “Throughput -delay trade-of f in wireless netw orks, ” IEEE INFOCOM’04 , March 2004. [7] M. Franceschetti , O. Dousse, D. Tse and P . Thiran, “Cl osing the gap in the capac ity of wireless networks via percolati on theory , ” IEEE T ransaction s on Informat ion Theory , 53(3), pp. 1009-1018, March 2007. [8] O. Dousse, M. Francesche tti and P . Thiran, “Information theoreti c bounds on the throughput scalin g of wireless relay network s, ” IEEE INFOCOM’05 , Miami, March 2005. [9] G. Sharma, R. R. Mazumdar , and N. B. Shroff “Dela y and Capac- ity Trade -of fs in Mobile Ad Hoc Networks: A Globa l Perspect i ve, ” IEEE/ACM T ransacti ons on Networking , 2007, V ol. 15 (1), 2007, pp.981-992. [10] S. T oumpis and A. J. Goldsmith, “Large wireless networks under fading, mobility , and delay constraint s, ” in Proc. IEEE INFOCOM 2004 . [11] S. Kulkarni and P . V iswanath, “ A deterministic approach to throughput scaling in wi reless netw orks, ” IEEE T ransact ions on Informat ion Theory , vol. 50, pp. 10411049, 2004. [12] A. Jovicic , P . V iswanath, and S. R. Kulkarn i, “Upper bounds to transport capac ity of wireless networks, ” IEEE T ransact ions on Informatio n Theory , vol. 50, pp. 25552565, 2004. [13] A. Karnik, A. Iyer and C. Rosenber g; “Throughput -optimal Configurat ion of Fi xed W irele ss Network s, ” to appear in IEEE/ACM T ransaction in Networking , av ailab le at http://www.ece .uwaterloo.ca/ ˜ cath/ton07.pdf . [14] A. Ozgur , O. Le veque, and Da vid Tse “ How does the Informat ion Capac- ity of Ad Hoc Networ ks Scale?, ” in proc. of F orty-fourt h Annual Allerton Confer ence on Communication, Contr ol and Computing , September 27 - 29, 2006. [15] V . Mhatre and C. Rosenbe rg, “The capac ity of ad hoc netwo rks under a realisti c link layer m odel, ” Online preprint , April 2005, av ailab le at http://arxiv.o rg/abs/cs/05040 99 . [16] V . Mhatre and C. Rosenber g, “The Impact of Link Layer Model on the Capaci ty of a Random Ad Hoc Network, ” Internatio nal Symposium on Informatio n Theory (ISIT 2006) , July 2006, Seattle , W A, USA. [17] J. .A . Bondy and U. Murthy Graph T heory with Applic ations, New Y ork: E lse vier , 1976. [18] R. Ellis, Entropy , Large De viations, and Statistic al Mecha nics, Springer , 2006.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment