This paper presents a new procedure of generating hash functions which can be evaluated using some mathematical tools. This procedure is based on discrete chaotic iterations. First, it is mathematically proven, that these discrete chaotic iterations can be considered as a \linebreak particular case of topological chaos. Then, the process of generating hash function based on the \linebreak topological chaos is detailed. Finally it is shown how some tools coming from the domain of \linebreak topological chaos can be used to measure quantitatively and qualitatively some desirable properties for hash functions. An illustration example is detailed in order to show how one can create hash functions using our theoretical study. Key-words : Discrete chaotic iterations. Topological chaos. Hash function
Deep Dive into A topological chaos framework for hash functions.
This paper presents a new procedure of generating hash functions which can be evaluated using some mathematical tools. This procedure is based on discrete chaotic iterations. First, it is mathematically proven, that these discrete chaotic iterations can be considered as a \linebreak particular case of topological chaos. Then, the process of generating hash function based on the \linebreak topological chaos is detailed. Finally it is shown how some tools coming from the domain of \linebreak topological chaos can be used to measure quantitatively and qualitatively some desirable properties for hash functions. An illustration example is detailed in order to show how one can create hash functions using our theoretical study. Key-words : Discrete chaotic iterations. Topological chaos. Hash function
arXiv:0810.4711v2 [cs.CR] 18 Nov 2008
A topological chaos framework for hash functions
Abstract
This paper presents a new procedure of generating hash functions which can be evaluated using some
mathematical tools. This procedure is based on discrete chaotic iterations.
First, it is mathematically proven, that these discrete chaotic iterations can be considered as a
particular case of topological chaos.
Then, the process of generating hash function based on the
topological chaos is detailed.
Finally it is shown how some tools coming from the domain of
topological chaos can be used to measure quantitatively and qualitatively some desirable properties for
hash functions. An illustration example is detailed in order to show how one can create hash functions
using our theoretical study.
Key-words : Discrete chaotic iterations. Topological chaos. Hash function
I.
Introduction
Hash functions, such as MD5 or SHA-256, can be described by discrete iterations on a finite set. In this
paper, the elements of this finite set are called cells. These cells represent the blocks of the text to which the
hash function will be applied. The origin of this study goes up with the idea of using the concept of discrete
chaotic iterations for generating new hash functions. This idea gave then quickly rise to the question of
knowing if discrete chaotic iterations really generate chaos.
This article presents the research results related to this question.
First, we prove that under some conditions, discrete chaotic iterations produce chaos, precisely, they produce
topological chaos in the sense of Devaney. This topological chaos is a rigorous framework well studied in the
field of mathematical theory of chaos. Thanks to this result we give a process of generating hash functions.
Behind the theoretical interest connecting the field of the chaotic discrete iterations and the one of
topological chaos, our study gives a framework making it possible to create hash functions that can be
mathematically evaluated and compared.
Indeed, some required qualities for hash functions such as strong sensitivity to the original text, resistance
to collisions and unpredictability can be mathematically described by notions from the theory of topological
chaos, namely, sensitivity, transitivity, entropy and expansivity. These concepts are approached but non
deepened in this article. More detailed studies will be carried out in forthcoming articles.
This study is the first of a series we intend to carry out. We think that the mathematical framework in
which we are placed offers interesting new tools allowing the conception, the comparison and the evaluation
of new methods of encryption in general, not only hash functions.
The rest of the paper is organized as follows.
The first next section is devoted to some recalls on two distinct domains, the domain of topological chaos
and the domain of discrete chaotic iterations.
Third and fourth sections constitute the theoretical study of the present paper.
Section III defines the
1
topological framework in which we are placed while section IV shows that the chaotic iterations produce a
topological chaos.
The following section details, using an illustration example, the procedure to build hash functions based on
our theoretical results. Section VI explains how quantitative measures could be obtained for hash functions.
The paper ends by some discussions and future work.
II.
Basic recalls
This section is devoted to basic definitions and terminologies in the field of topological chaos and in the one
of chaotic iterations.
1
Devaney’s chaotic dynamical systems
Consider a metric space (X, d), and a continuous function f : X −→X.
Definition 1 f is said to be topologically transitive if, for any pair of open sets U, V ⊂X, there exists
k > 0 such that f k(U) ∩V ̸= ∅.
Definition 2 An element (a point) x is a periodic element (point) for f of period n ∈N, if f n(x) = x. The
set of periodic points of f is denoted Per(f).
Definition 3 (X, f) is said to be regular if the set of periodic points is dense in X,
∀x ∈X, ∀ε > 0, ∃p ∈Per(f), d(x, p) ⩽ε.
Definition 4 f has sensitive dependence on initial conditions if there exists δ > 0 such that, for any x ∈X
and any neighborhood V of x, there exists y ∈V and n ⩾0 such that |f n(x) −f n(y)| > δ.
δ is called the constant of sensitivity of f.
Let us now recall the definition of a chaotic topological system, in the sense of Devaney [4] :
Definition 5 f : X −→X is said to be chaotic on X if,
1. f has sensitive dependence on initial conditions,
2. f is topologically transitive,
3. (X, f) is regular.
Therefore, quoting Robert Devaney: “A chaotic map possesses three ingredients: unpredictability, in-
decomposability, and an element of regularity. A chaotic system is unpredictable because of the sensitive
dependence on initial conditions. It cannot be broken down or decomposed into two subsystems, because
of topological transitivity. And, in the midst of this random behavior, we nevertheless have an ele
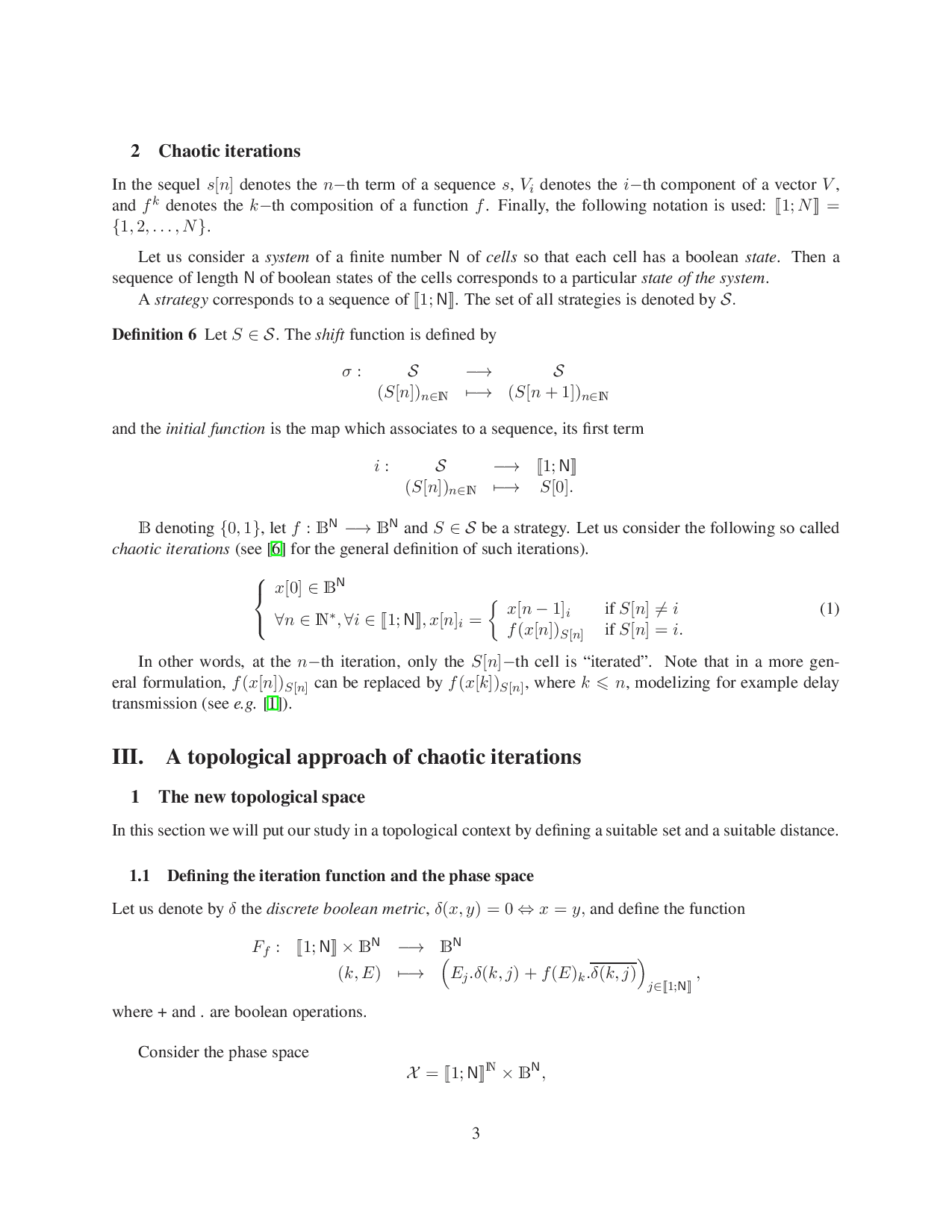
…(Full text truncated)…
This content is AI-processed based on ArXiv data.