A Basic Framework for the Cryptanalysis of Digital Chaos-Based Cryptography
Chaotic cryptography is based on the properties of chaos as source of entropy. Many different schemes have been proposed to take advantage of those properties and to design new strategies to encrypt information. However, the right and efficient use of chaos in the context of cryptography requires a thorough knowledge about the dynamics of the selected chaotic system. Indeed, if the final encryption system reveals enough information about the underlying chaotic system it could be possible for a cryptanalyst to get the key, part of the key or some information somehow equivalent to the key just analyzing those dynamical properties leaked by the cryptosystem. This paper shows what those dynamical properties are and how a cryptanalyst can use them to prove the inadequacy of an encryption system for the secure exchange of information. This study is performed through the introduction of a series of mathematical tools which should be the basic framework of cryptanalysis in the context of digital chaos-based cryptography.
💡 Research Summary
The paper “A Basic Framework for the Cryptanalysis of Digital Chaos‑Based Cryptography” presents a systematic set of analytical tools that can be used to evaluate the security of digital cryptosystems built on chaotic maps. The authors begin by noting that chaotic dynamics naturally provide the two fundamental cryptographic properties—confusion (statistical independence of ciphertext from plaintext and key) and diffusion (high sensitivity to small changes in input). However, they caution that chaotic systems also possess underlying regularities, such as dense unstable periodic orbits, which can leak information about the secret key if the cryptosystem does not conceal them properly.
The work focuses exclusively on digital (discrete‑time) chaotic systems, i.e., maps defined by a difference equation x_{k+1}=g(μ,x_k). The authors propose a “basic framework” consisting of several mathematical diagnostics:
-
Bifurcation Diagram – By plotting the asymptotic orbit values for a wide range of control parameters μ and random initial conditions, one can visually identify parameter intervals that do not lead to chaotic behavior. The authors illustrate this with the logistic map, showing that non‑chaotic μ values would degrade cryptographic performance and could be exploited by an attacker.
-
Lyapunov Exponent (LE) – The largest LE quantifies local divergence; a positive value guarantees chaos. The paper stresses that a well‑defined key space must consist only of parameter vectors that produce a positive LE. The two‑dimensional Hénon map is used as an example, with a contour plot indicating the region of positive LE.
-
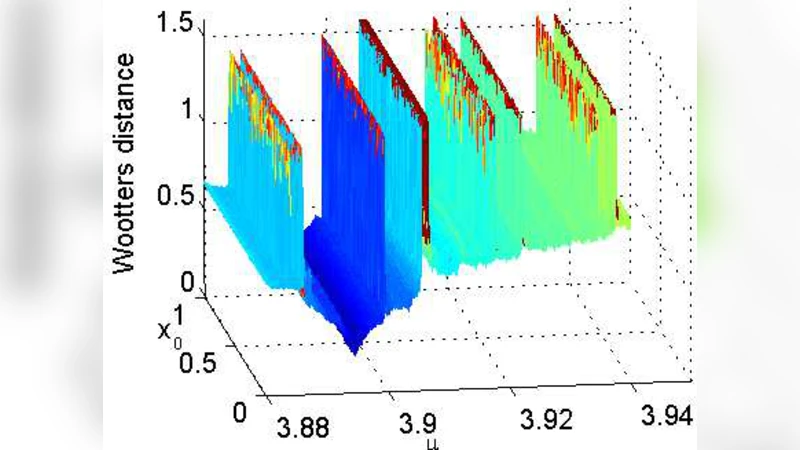
Histogram and Return‑Map Analysis – When a ciphertext is directly derived from a chaotic orbit, consecutive orbit values can be used to estimate the control parameter. Even when the orbit is sampled, statistical treatments (e.g., comparing histograms via the Wasserstein distance) can reveal parameter dependence. The authors demonstrate successful estimation of the logistic map’s μ by matching sampled‑orbit histograms to a pre‑computed library.
-
Entropy Measures – The authors argue that the entropy of ciphertexts (Shannon, Tsallis, multi‑resolution wavelet entropy) must be insensitive to the underlying chaotic parameters. If entropy varies with μ, an attacker could infer key information. They provide experimental results on the Hénon map showing how entropy changes when control parameters are varied.
-
Statistical Complexity – Using Jensen‑Tsallis complexity, the paper shows that complexity curves can have distinct features for specific μ intervals, enabling parameter estimation. The logistic map’s complexity curve is plotted to illustrate this effect.
-
Symbolic Dynamics – By partitioning the phase space and assigning symbols to intervals, one can reconstruct the symbolic sequence of a chaotic orbit. The presence of unstable periodic orbits in the symbolic sequence allows reconstruction of both the initial condition and control parameters. The authors cite several prior works where this technique successfully broke chaos‑based ciphers.
The paper emphasizes that each of these tools can be applied independently or in combination to detect design flaws. A robust chaos‑based cipher must therefore:
- Define a key space that lies entirely within the chaotic region (verified by bifurcation diagrams and Lyapunov exponents).
- Ensure that ciphertexts do not reveal statistical fingerprints (entropy, histograms, complexity) that correlate with secret parameters.
- Conceal the underlying regularity of the chaotic map, for example by using parameter ranges that guarantee continuous chaotic behavior.
In the concluding section, the authors assert that traditional cryptographic security tests (e.g., NIST randomness tests) are insufficient for chaos‑based schemes. A thorough understanding of the dynamical system’s behavior is mandatory; otherwise, the resulting encryption algorithm may suffer from severe security and efficiency problems.
Overall, the paper provides a concise yet comprehensive “cryptanalysis toolbox” for digital chaos‑based cryptography, offering practical guidelines for both designers and analysts to assess and improve the security of such systems.
Comments & Academic Discussion
Loading comments...
Leave a Comment