Network Coding Capacity of Random Wireless Networks under a SINR Model
Previous work on network coding capacity for random wired and wireless networks have focused on the case where the capacities of links in the network are independent. In this paper, we consider a more realistic model, where wireless networks are mode…
Authors: Zhenning Kong, Salah A. Aly, Emina Soljanin
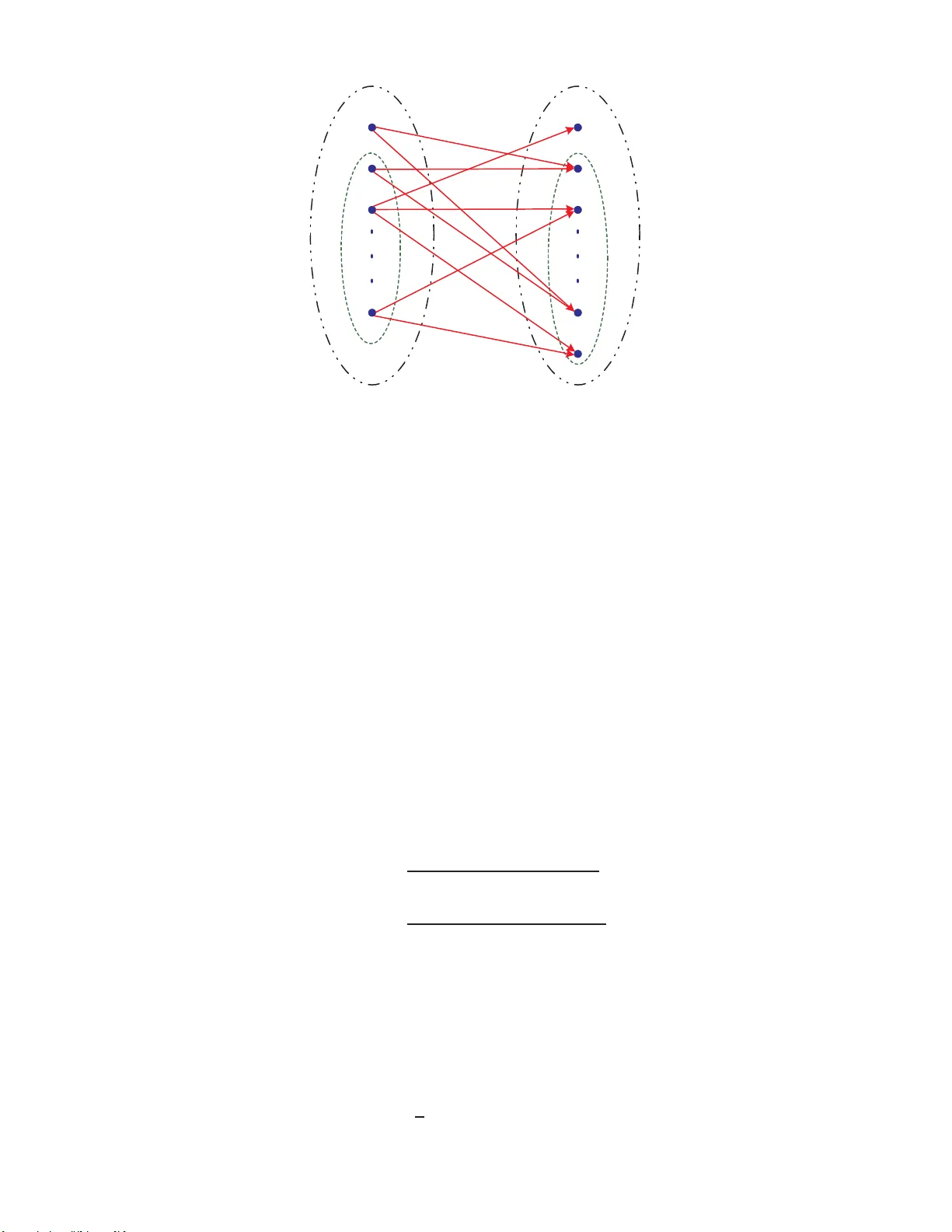
SUBMITTED TO IEEE TRANSACTION S ON INFORMATION THEORY 1 Netw ork Coding Capacity of Random W ireless Netw orks under a SINR Model Zhenning K ong , Student Member , IEEE, Salah A. Aly , Student Member , IEEE, Emina Soljanin, Senior Member , IEEE, Edmund M. Y eh, Me mber , IEEE, Andreas Klappenecker Member , IEEE Abstract Previous work o n network co ding c apacity f or random wired and wireless networks have fo cused on th e case where the capacities of links in the n etwork are indepen dent. In th is pape r , we co nsider a more realistic mo del, where wir eless networks are modelled by random g eometric gr aphs with interfer ence and noise. In th is mo del, the cap acities of links are not indep endent. By em ploying couplin g and mar tingale method s, we show th at, u nder mild cond itions, the network cod ing cap acity for ran dom wireless networks still exhibits a concentration behavior around the mean value of the minimum cut. I . I N T RO D U C T I O N T raditionally , in formation flo w in networked systems was treated like fluid t hrough pipes, and i ndepen- dent inform ation flows were processed separately . Under thi s assumptio n, for a un icast transm ission (one source node transfers information to one destination no de), t he maxi mum transm ission rate is b ounded b y the size of the mi nimum cut bet ween the source and the d estination. This result is known as the Min-Cut Max-Flow T heor em , which w as pro ved by Menger [1], F ord and Fulk erson [2] and El ias et al. [3 ]. Ho wever , for a multi cast transmission (one source node transfers information to multiple destination nodes), this maximum flow rate cannot alwa ys be achieved by tradition al store-and-forward routi ng algorit hms, eve n if each source-destin ation p air has the mini mum cut with the same size. That is because in a multicast transmissio n, some links i n the network m ay be sh ared by the routi ng paths for different source-destination pairs. In their seminal paper [4], Ahlswede et al. propos ed a network codi ng s cheme, and showed that i f we allow interm ediate nodes to encode their received messages and forward t he coded m essages to their next-hop n eighbors, the maximum flow rate can be achie ved for mutil cast t ransmissions . In addit ion t o the information t heoretic treatment of [4], network coding has also been studied in an algebraic framew ork dev eloped by Koetter and M ´ edard in [5], and a combi natorial framew ork propos ed by Fragouli and Soljanin in [6]. Code design for network coding schemes has als o attracted intense i nterest. In [7], Li et This research is supported in part by National Science Foundation (NSF) grant CNS -0626882 , Army Research Office (ARO) grant W911NF-07-1-0524 . Z. K ong and Edmund M. Y eh are with the Department of Electrical Engineering, Y ale Univ ersity , New Hav en, CT 06520, US A, (email: zhenning.k ong@y ale.edu, edmund.yeh@yale.edu). S. A. Aly and A. Klappeneck er are with the Department of Computer S cience, T exas A&M Univ ersity , College S tation, TX 77843, USA, (email: salah@cs.tamu.edu, klappi@cs.tamu.edu). E. Soljanin is with Bell Laboratories, Alcatel-Lucent, Murray Hill, NJ 07974, USA, (email: emina@lucent.com). SUBMITTED TO IE EE TRANSACTIONS ON INFORMATION THEORY 2 al. sh owed that linear codes are suffic ient to achie ve the maxi mum flow rate for a one-source mult icast transmissio n. K oetter and M ´ edard, and Jaggi et al. constructed linear multi cast codes for network coding schemes in [5] and in [8], respectively . The approach of constructi ng linear codes in a random ized way for m ulticast transmissions was proposed by Ho et al. in [9]. F or a detailed re v iew of network coding and its appl ications in many fields, e.g., wireless communi cation, content dist ribution, s ecurity , please see the book by Fragouli and Solj anin [10]. In most stu dies on network coding, network topologies are assum ed to be kn own. In [11 ], [12], Ramamoorthy et al. studied network coding capacity for weighted random graphs and random geom etric graphs. In th e random graph model, each pair of nodes are connected by a bidirectional link wit h probability p < 1 independently [13], [14]. The capacity of each link is as sumed to be i.i.d. according to some probabilit y distribution. In t he random geometric graph model, two nodes are con nected t o each other by a bidi rectional link only when their distance is less than or equal to a predefined positive v alue r , the characteristic radius [15]. Each l ink has a unit capacity . For these two types of random networks, the authors showed t hat the network coding capacity is concentrated at the (weighted) mean degree of the graph, i.e., t he (weighted) mean number o f n eighbors of each node. Es sentially , the results rev eal a concentration beha vior of the size of the minim um cut between two nodes in random graphs or random geometric graphs. Related probl ems have been studied in the literature, e.g., [16] and references therein. In [17], the authors studied a generalized random g eometric graph model, where two nodes are connected by a bidirectio nal l ink wit h probabilit y 1 if their distance d is less than or equal to r 0 > 0 , and with probability p < 1 if r 0 < d ≤ r 1 . Th ey o btained si milar concentration results. The geometric models in [11], [12], [17] assume that a link exists (possibl y wi th a probabi lity) between two no des when the nodes are wi thin each other’ s transmissi on range. Although each link has a di rection, as all links are bidirection al (i.e., the link ( i, j ) impli es the existence of the li nk ( j, i ) ), the mod el i n fact leads to an und ir ected graph and cons iderably si mplifies the resulti ng analysis. In addition, interference among wi reless termin als was not consi dered in [11], [12], [17]. Nev ertheless, in wi reless networks, due to noise, interference, and the heterogeneit y of transmission powers, significantly more s ophisticated models for link conn ectivity are needed. For instance, a widely -used model for wi reless comm unication channels is the Signal-to-Interference-and-Noise-Ratio (SINR) model [18], [19]. In t his paper , we s tudy the capacity , i.e., the size of t he minim um cut, o f random wireless networks under the SINR model. Giv en th at network coding capacity with noisy li nks is in general still an op en problem , we assume that as long as the SINR β ij of a l ink ( i, j ) is greater than or equal to a predefined threshold β , th en no de i can transmit data at rate R packets/sec to node j without error . That is, links are n oise-free once t he SINR condition is met. In other words, we view network codin g as operating on a h igher l ayer in the network communication stack, and assume there i s an error correcting code at the lower layer which corrects errors on the link s once the SINR threshold is met. Giv en thi s model, each link is indeed directional, and SUBMITTED TO IE EE TRANSACTIONS ON INFORMATION THEORY 3 the capacities of diffe rent l inks are no t independent. Nev ertheless, we will show that under some mild conditions, th e capacity still has a sharp concentratio n when the scale of the n etwork is lar ge enoug h. It is worthy mentio ning t hat the capacity we in vestigate in th is paper is diff erent from the one studied in [20]–[25]. The latter is referred to as t hroughput capacity , or t ransport capacity , for random wireless networks wit h many-to-many transm issions. In other words, it is the m aximum achiev able aver aged rate at which each node in the network can transmit (simultaneously with other nodes specified by scheduling schemes) to a randomly selected destination no de. In contrast, the network codi ng capacity that we study in this paper (as in [11], [12], [17]) is the maxim um rate that one source can achieve in a multi cast transmissio n, which is determined by the s ize o f the minim um cut between the so urce and the dest inations. This paper is organized as foll ows. In Section II, we describe the random wireless network model. In Section II I, we study the network coding ca pacity for a single source and multiple destinations. S pecifically , we in vestigate two cases. In the first case, all nodes have the same transmission power , and in the second case, the transmiss ion powers are heterogeneous . W e use different t echniques for these two cases and show that the network cod ing capacity has a concentration b eha vior in both cases. In Section IV , we present rele v ant si mulation result s, and finally , we conclude in Section V . I I . R A N D O M W I R E L E S S N E T W O R K M O D E L W e use the following model for random wireless networks. Ass ume (i) X = { X 1 , X 2 , ..., X n } is a set of n nodes which are independentl y and uniformly dis tributed at random on t he t wo-dimensional unit torus, where X i denotes the rando m location of nod e i , and n is the total number of nodes. (ii) Each nod e i has a transmis sion power P i , which fol lows a probability distribution f P ( p ) , p ∈ [ p min , p max ] , wh ere 0 < p min ≤ p max < ∞ . Here, th e existence of a link from node i to node j depends on j ’ s abi lity to decode the transmi tted signal from i , which is in turn determined by the Sig nal-to-Interference-and-Noise-Ratio (SINR) given by β ij = P i L ( d ij ) N 0 + γ P k 6 = i,j P k L ( d k j ) , (1) where P i is th e transmi ssion power of n ode i , d ij is th e distance between nodes i and j , and N 0 is th e power of background no ise. The parameter γ i s the in verse of the system processing gain. It is equal to 1 in a narrow-band system and smaller than 1 in a broadb and (e.g., CDMA) s ystem. The sign al attenuation function L ( · ) is a functio n of the dis tance d ij = || X i − X j || , where k · k i s the Eucli dean norm, and is usually g iv en by L ( d ij ) = cd − α ij for so me constants c and 2 < α < 4 . Under the SINR model, the transmitted s ignal o f node i can be decoded at j if and onl y if β ij > β , where β is s ome threshold for decoding. In thi s case, a link ( i, j ) from i to j i s said to exist. Note that e ven if β ij > β , β j i > β may not h old and t hus t he link ( j, i ) m ay not exist. Thus, the graph resulting SUBMITTED TO IE EE TRANSACTIONS ON INFORMATION THEORY 4 from the SINR model is in general di r ected. It is clear that link ( i, j ) is bidirectional if and only if min { β ij , β j i } > β . Denote by G ( X , P , γ ) the ensemb le of random wireless networks induced by the above physi cal m odel, where P = { P 1 , P 2 , ..., P n } represents the set of transmissi on powers. For transm ission power P and signal at tenuation fun ction L ( · ) , we ass ume (i) p min > β N 0 ; (ii) Pr ( P = p min ) > 0 , Pr ( P = p max ) > 0 , (iii) L ( x ) is continuous and strict ly decreasing in x for technical and practical reasons. In the remainder of thi s paper , under differe nt circumst ances, we may place further constraints on P i . The s um P k 6 = j L ( d k j ) = P k 6 = j L ( || X k − X j || ) is a random variable depending on th e lo cations of all nodes in the network. Define, for all j = 1 , ..., n , J ( j ) , X k 6 = j L ( d k j ) , (2) I ( j ) , X k 6 = j P k L ( d k j ) . (3) T o study the as ymptotic network capacity , we will let t he num ber of nodes n go to infinity . Since the region is fixed, this corresponds to a dens e network m odel [15], [20]. Another widel y used model is the extended network mod el [26 ], [27], in wh ich the num ber o f nodes and the area of t he region bo th go to in finity while the ratio between them— the density of th e network, i s kept constant. Bot h mod els are widely used in the l iterature. W e wi ll focus on the former one i n t his paper . I I I . N E T W O R K C O D I N G C A P AC I T Y F O R S I N G L E S O U R C E T RA N S M I S S I O N A. Capacity of a Cut Let C ij be the capacity of a link ( i, j ) . W e will specify t he form of C ij later for different scenarios. Consider a single-source m ultiple-desti nation transm ission problem. Let s be the source n ode. Suppose there are l desti nation nodes, t 1 , ...t l , and m relay nodes, u 1 , ...u m . Denote the s et of the destination nod es and relay nodes by T and R , respective ly . Note that { s } , T and R are all subsets o f X . In this paper , we always assum e that there are no direct links between the so urce and its destinations . Fig. 1 gives an example of single-source singl e-destination transmissi on. Let t he capacity of the link from the source s to each relay node u i be C si , i = 1 , ..., m , the capacity from relay node u i to anot her relay node u j be C ij , i 6 = j, i = 1 , ..., m, j = 1 , ..., m , and th e capacity from each relay node u i to each destinati on node t j be C it j , i = 1 , ..., m, j = 1 , ..., l . Unlike random geometric graph models studied in [11], [12], [17], the capacities in our mo del are not symmetric (i.e., C ij 6 = C j i ) nor i ndependent in general. SUBMITTED TO IE EE TRANSACTIONS ON INFORMATION THEORY 5 s t relay nodes Fig. 1. Single-source single-destination t ransmission i n directed SINR graphs In our SINR wireless network model , there are two sources of randomness: one is t he random location of each nod e and the oth er is the random transmission power of each node. W e use E X and E P to denote the expectation operatio n with respect to each probability m easure, respectively . Let ¯ C be the expected capacity o f a link ( i, j ) , defined as ¯ C = E X E P [ C ij ] = Z ∞ 0 C ij dF β ij ( τ ) , (4) where F β ij ( · ) i s the c.d.f. o f β ij , which is determi ned by f P ( · ) , the distribution of X , and th e path-loss function L ( · ) . Now define an s - t -cut of size k for a give n source s and dest ination t ∈ T as a p artition of the relay nodes int o two subsets V k and V c k , such that | V k | = k , | V c k | = m − k , V k ∪ V c k = R and V k ∩ V c k = ∅ . An example of an s - t -cut is sh own in Fig. 2. Let C k = X u i ∈ V c k C si + X u j ∈ V k X u i ∈ V c k C j i + X u j ∈ V k C j t , (5) then C k is the capacity of the corresponding s - t -cut. Although C k is a sum of dependent but i dentically distributed random variables, w e st ill have E [ C k ] = E X E P [ C k ] = X u i ∈ V c k E X E P [ C si ] + X u j ∈ V k X u i ∈ V c k E X E P [ C j i ] + X u j ∈ V k E X E P [ C j t ] = [ m + k ( m − k )] ¯ C , (6) and con sequently E [ C k ] = E [ C m − k ] for k = 0 , 1 , ..., m , and E [ C 0 ] ≤ E [ C 1 ] ≤ · · · ≤ E [ C ⌈ m/ 2 ⌉ ] . T o show that the capacity of any source-destination pair concentrates at some value, we will first show that for such a source-destination pair , the capacity of any s - t -cut of size k concentrates at its mean value. SUBMITTED TO IE EE TRANSACTIONS ON INFORMATION THEORY 6 relay nodes relay nodes s t u 1 u 2 u k u k+1 u k+2 u m- 1 u m Fig. 2. An s - t -cut for the single-source single-destination transmission in directed S INR graphs Similar resul ts were proved in [11], [12], [17], where the capacities of the links that origi nate from the same node are i.i.d. Neve rtheless, the meth ods used in [11], [12], [17] do not apply here, since in the SINR m odel, C k is a sum of dependent random l ink capacities. Ins tead, we emp loy coupl ing, martingale methods and Azuma’ s i nequality [15 ], [28] to solve the problem. Note that when γ = 0 , i.e., t here is no interference in the n etwork, the capacities C si for i = k + 1 , ..., m , are mu tually independent; so are the capacities C ij for any fixed i = 1 , ..., k with j = k + 1 , ..., m or t . In t his case, altho ugh the link capacities are still asymmetric, P u i ∈ V c k C si and P u i ∈ V c k ∪{ t } C j i for j ∈ V k become sums of ind ependent random variables. Thus we can apply methods similar to those used in [11], [12], [17 ] to obtain the same concentration result s. B. Constant T ransmission P ower Consider the scenario when all nodes t ransmit with a const ant power P 0 and denote the correspondin g model by G ( X , P 0 , γ ) . In this case, t he SINR of link ( i, j ) can be re written as β ij = L ( d ij ) N 0 /P 0 + γ P k 6 = i,j L ( d k j ) = L ( d ij ) N 0 /P 0 + γ J ( j ) − γ L ( d ij ) . (7) Assume that when β ij ≥ β , the link ( i, j ) has capacity R , i .e., nod e i can transmit data at rate R packets/sec to node j witho ut error . Then, we can d efine C ij as C ij = R β ij ≥ β , 0 β ij < β . (8) Note that when the wireless channel is an additive Gaussian channel, th e capacity of link ( i, j ) is [29] C ij = 1 2 log (1 + β ij ) β ij ≥ β , 0 β ij < β . (9) SUBMITTED TO IE EE TRANSACTIONS ON INFORMATION THEORY 7 Our results in this subsection do not depend on any particul ar form of C ij when β ij ≥ β . Nevertheless, since we consider the appl ication of network coding, it would be more appropriate to focus on (8), rather than (9) . Note that β ij and thus C ij , are determined by L ( d ij ) and J ( j ) . Because of the i .i.d. distribution of the X i ’ s, given X j , t he d ij ’ s are independent for all i 6 = j . Given node j , let E [ L ] , E X i [ L ( d ij )] , (10) then E [ J ( j )] = E " X i 6 = j L ( d ij ) # = ( n − 1) E [ L ] , E [ J ] . (11) Since our mo del is a dense n etwork m odel and the area of the region is fixed, E [ L ] = E [ L ( d ij )] is a con stant and E [ J ] = ( n − 1) E [ L ] scales wit h n . For different j ’ s, it is clear that J ( j ) ’ s are not independent. Howe ver , they have t he same sharp concentration beha vior in l ar ge-scale wireless networks. This is established in the following lemma. Lemma 1: Suppose t here are n nodes in the network, t hen Pr( J ( j ) ≤ (1 − ǫ 1 ) E [ J ]) = O 1 n 2 , (12) and Pr( J ( j ) ≥ (1 + ǫ ′ 1 ) E [ J ]) = O 1 n 2 , (13) for all j = 1 , 2 , ..., n , where ǫ 1 = q 4 ln n ( n − 1) E [ L ] and ǫ ′ 1 = q 6 ln n ( n − 1) E [ L ] . Pr oof : Given any node j , because J ( j ) = P i 6 = j L ( d ij ) , and L ( d ij ) are i.i.d . for al l i 6 = j , by the Chernof f bound [28], [30], we ha ve Pr( J ( j ) ≤ (1 − ǫ 1 ) E [ J ]) ≤ exp − E [ J ] ǫ 2 1 2 = exp − ( n − 1) E [ L ] ǫ 2 1 2 , (14) and Pr( J ( j ) ≥ (1 + ǫ ′ 1 ) E [ J ]) ≤ exp − E [ J ] ǫ ′ 2 1 3 = exp − ( n − 1 ) E [ L ] ǫ ′ 2 1 3 . (15) Substitutin g ǫ 1 = q 4 ln n ( n − 1) E [ L ] and ǫ ′ 1 = q 6 ln n ( n − 1) E [ L ] into (14) and (15), we obtain (12) and (13), respectiv ely . SUBMITTED TO IE EE TRANSACTIONS ON INFORMATION THEORY 8 Lemma 1 sho ws that when the network is large, i.e., n is suf ficiently large, J ( j ) concentrates at γ ( n − 1) E [ L ] = Θ( n ) E [ L ] . The reason for this is the uni form dis tribution of the n odes. Now define t wo other types of SINR models G ′ ( X , P 0 , γ ) and G ′′ ( X , P 0 , γ ) wh ich are coupled wit h G ( X , P 0 , γ ) su ch t hat they have the same point process X and constant powe r P 0 . Let the SINR of link ( i, j ) in G ′ ( X , P 0 , γ ) and G ′′ ( X , P 0 , γ ) be β ′ ij = L ( d ij ) N 0 /P 0 + (1 + ǫ ′ 1 ) γ E [ J ] − γ L ( d ij ) (16) and β ′′ ij = L ( d ij ) N 0 /P 0 + (1 − ǫ 1 ) γ E [ J ] − γ L ( d ij ) , (17) respectiv ely . Let C ′ ij and C ′′ ij be the capacity of li nk ( i, j ) i n G ′ ( X , P 0 , γ ) and G ′′ ( X , P 0 , γ ) , respectively . Since ǫ 1 → 0 and ǫ ′ 1 → 0 as n → ∞ , C ′ ij and C ′′ ij are asymptotically equal to C ij . The foll owing lemma establishes a concentration result for C k with constant transmiss ion power by coupling methods. Lemma 2: For any 0 < ǫ < 1 , the capacity of an s - t -cut of s ize k , k = 0 , 1 , ..., m , s atisfies Pr( C k ≤ (1 − ǫ ) E [ C ′ k ]) ≤ exp − E [ C ′ k ] ǫ 2 2 1 − O 1 n + O 1 n (18) where E [ C ′ k ] = [ m + k ( m − k )] ¯ C ′ and ¯ C ′ is the av erage link capacity in G ′ ( X , P 0 , γ ) . M oreover , Pr( C k ≥ (1 + ǫ ) E [ C ′′ k ]) ≤ exp − E [ C ′′ k ] ǫ 2 3 1 − O 1 n + O 1 n (19) where E [ C ′′ k ] = [ m + k ( m − k )] ¯ C ′′ and ¯ C ′′ is the av erage link capacity in G ′′ ( X , P 0 , γ ) . Pr oof : By Lemma 1, for all j , { J ( j ) ≥ ( 1 − ǫ 1 ) E [ J ] } and { J ( j ) ≤ (1 + ǫ ′ 1 ) E [ J ] } are both increasing e vents. 1 By the FKG inequality [15], [26], [30], we hav e Pr n \ j =1 { J ( j ) ≥ (1 − ǫ 1 ) E [ J ] } ! ≥ n Y j =1 Pr( J ( j ) ≥ (1 − ǫ 1 ) E [ J ]) = 1 − O 1 n 2 n = 1 − O 1 n , (20) 1 In the context of graph theory , an ev ent A is called increasing if I A ( G ) ≤ I A ( G ′ ) whene ver graph G is a subgraph of G ′ , where I A is the indicator function of A . An e vent A is called decreasing if A c is increasing. For details, please see [15], [26], [30]. SUBMITTED TO IE EE TRANSACTIONS ON INFORMATION THEORY 9 where the first equality i s due to Lem ma 1. Similarly , Pr n \ j =1 { J ( j ) ≤ (1 + ǫ ′ 1 ) E [ J ] } ! ≥ n Y j =1 Pr( J ( j ) ≤ (1 + ǫ ′ 1 ) E [ J ]) = 1 − O 1 n 2 n = 1 − O 1 n . (21) Inequalities (20) and (21) im ply that Pr( C k ≤ C ′′ k ) ≥ 1 − O 1 n , (22) Pr( C k ≥ C ′ k ) ≥ 1 − O 1 n . (23) Since Pr( C k ≤ (1 − ǫ ) E [ C ′ k ]) ≤ 1 − Pr( C k ≥ C ′ k ) Pr( C ′ k ≥ (1 − ǫ ) E [ C ′ k ]) , and Pr( C k ≥ (1 + ǫ ) E [ C ′′ k ]) ≤ 1 − Pr( C k ≤ C ′′ k ) Pr( C ′′ k ≤ (1 + ǫ ) E [ C ′′ k ]) , in order to show (18) and (19 ), it suffice s t o show Pr( C ′ k ≤ (1 − ǫ ) E [ C ′ k ]) ≤ exp − E [ C ′ k ] ǫ 2 2 , (24) and Pr( C ′′ k ≥ (1 + ǫ ) E [ C ′′ k ]) ≤ exp − E [ C ′′ k ] ǫ 2 3 . (25) In G ′ ( X , P 0 , γ ) and G ′′ ( X , P 0 , γ ) , the SINR of link ( i, j ) is given by (16) and (17), respectively . Because the d ij ’ s for a given i are independent, by applying the Chernof f bounds , we obt ain (24) and (25). Since C ′ ij and C ′′ ij are asymptotically equal t o C ij , E [ C ′ k ] and E [ C ′′ k ] are asymptotically equal t o E [ C k ] . Consequently , Lemma 2 shows that C k concentrates at E [ C k ] asym ptotically alm ost su rely . 2 Now , let C s,t be th e m inimum cut capacity among all s - t -cuts, i. e., C s,t = min 0 ≤ k ≤ m C k . (26) For one s ource and m ultiple destination s, the capacity of network coding depends on the mi nimum cut between the source and the destination s [11], [12], [17]. Therefore, for the given source node s and the sets of destination nodes T = { t 1 , ..., t l } and relay nodes R = { u 1 , ..., u m } , define the network codi ng capacity as C s, T = min t ∈T C s,t . (27) 2 An ev ent is said to be asymptotic almost sure (abbreviated a.a.s.) if it occurs with a probability con verging to 1 as n → ∞ . SUBMITTED TO IE EE TRANSACTIONS ON INFORMATION THEORY 10 In the following, we show th at when the nu mber of relay nodes m is sufficiently lar ge, th e network coding capacity C s, T concentrates at E [ C 0 ] = m ¯ C with high probabil ity . Theor em 3: When n is sufficiently large, with high probabili ty , th e network cod ing capacity C s, T satisfies Pr( C s, T ≥ (1 − ǫ ′ α ) E [ C 0 ]) = 1 − O l m α , (28) where ǫ ′ α = q 2 α ln m E [ C 0 ] for α > 0 and E [ C 0 ] = m ¯ C . Pr oof : Since the C ij ’ s are asymptot ically equal to the C ′ ij ’ s, in order t o show (28), it is equ iv alent to show Pr( C s, T ≥ (1 − ǫ ′ α ) E [ C ′ 0 ]) = 1 − O l m α . Since E [ C ′ k ] ≥ E [ C ′ 0 ] for any k = 1 , ..., m , Pr( C s,t ≤ (1 − ǫ ′ α ) E [ C ′ 0 ]) ≤ Pr( C s,t ≤ (1 − ǫ ′ α ) E [ C ′ k ′ ]) , for any t ∈ T , where k ′ is the s ize of the mi nimum s - t -cut. By (18) of Lemm a 2, we have for suf ficiently lar ge n , Pr( C s,t ≤ (1 − ǫ ′ α ) E [ C ′ k ′ ]) ≤ exp − ǫ ′ 2 α [ m + k ′ ( m − k ′ )] ¯ C ′ 2 ≤ exp − ǫ ′ 2 α m ¯ C ′ 2 . By choos ing ǫ ′ α = q 2 α ln m E [ C 0 ] , s ince ¯ C ′ and ¯ C are asymptoti cally equal, we hav e for any t ∈ T , Pr( C s,t ≤ (1 − ǫ ′ α ) E [ C ′ 0 ]) = O 1 m α . By the union bound, we hav e Pr( C s, T ≤ (1 − ǫ ′ α ) E [ C ′ 0 ]) ≤ X t ∈T Pr( C s,t ≤ (1 − ǫ ′ α ) E [ C ′ 0 ]) = O l m α . Theor em 4: When n is sufficiently large, with high probabili ty , th e network cod ing capacity C s, T satisfies Pr( C s, T ≤ (1 + ǫ ′′ α ) E [ C 0 ]) = 1 − O 1 m α , (29) where ǫ ′′ α = q 3 α ln m E [ C 0 ] for α > 0 and E [ C 0 ] = m ¯ C . SUBMITTED TO IE EE TRANSACTIONS ON INFORMATION THEORY 11 Pr oof : Since the C ij ’ s are asymptot ically equal to the C ′′ ij ’ s, in order t o show (29), it is equ iv alent to show Pr( C s, T ≤ (1 + ǫ ′′ α ) E [ C ′′ 0 ]) = 1 − O 1 m α . T o show this , it is suffic ient to cons ider a parti cular cut for a sou rce-destination pair , e.g., an s - t -cut with capacity P m i =1 C si separating the source s from all the other nodes. Pr( C s, T ≥ (1 + ǫ ′′ α ) E [ C ′′ 0 ]) ≤ Pr ( C s,t ≥ (1 + ǫ ′′ α ) E [ C ′′ 0 ]) ≤ Pr m X i =1 C si ≥ (1 + ǫ ′′ α ) E [ C ′′ 0 ] ! = Pr( C 0 ≥ (1 + ǫ ′′ α ) E [ C ′′ 0 ]) ≤ exp − ǫ ′′ 2 α m ¯ C ′′ 3 = O 1 m α . where the last inequality follows from (19). C. Het er ogeneous T ransmission P o wers In this subsection, we con sider the case where the transmission power of each node is randomly chos en rather than being constant. W e continue to assume that the capacity of a link ( i, j ) is a constant R , which is independ ent of the SINR β ij , wh en β ij ≥ β . In this case, β ij can be rewritten as β ij = P i L ( d ij ) N 0 + γ P k 6 = i,j P k L ( d k j ) = P i L ( d ij ) N 0 + γ I ( j ) − γ P i L ( d ij ) . (30) Because the P i ’ s and X i ’ s are bot h i.i.d ., using the same technique as that for Lemm a 1, we can prove the fo llowing lemma. Lemma 5: Suppose t here are n nodes in the network, t hen Pr( I ( j ) ≤ (1 − ǫ 2 ) E [ I ]) = O 1 n 2 , (31) and Pr( I ( j ) ≥ (1 + ǫ ′ 2 ) E [ I ]) = O 1 n 2 , (32) for all j = 1 , 2 , ..., n , where ǫ 2 = q 4 ln n ( n − 1) E [ P ] E [ L ] and ǫ ′ 2 = q 6 ln n ( n − 1) E [ P ] E [ L ] . Even though we have concentration results for I ( j ) , we cannot em ploy the same coupling methods as in t he previous s ection. In G ′ ( X , P 0 , γ ) (or G ′′ ( X , P 0 , γ ) ) as described in Section III-B, the C ′ ij ’ s (or C ′′ ij ’ s) are independent for all j 6 = i for a given i . In our new case, howe ver , this independence does not SUBMITTED TO IE EE TRANSACTIONS ON INFORMATION THEORY 12 hold because all the C ij ’ s depend on the transmi ssion power P i . T o deal wit h this d ependence, we use martingale methods and Azuma’ s inequalit y to sol ve o ur prob lem. Theor em 6 (Azuma’ s Inequality [30 ]): Let Z 0 , Z 1 , ..., be a martingale sequence such th at for each i = 1 , 2 , ..., , | Z i − Z i − 1 | ≤ c i almost surely , where c i may depend on i . Then for all n > 0 and any λ > 0 , Pr( Z n ≥ Z 0 + λ ) ≤ exp − λ 2 2 P n i =1 c 2 i , (33) and Pr( Z n ≤ Z 0 − λ ) ≤ exp − λ 2 2 P n i =1 c 2 i . (34) Pr oof : Please see e.g. [30]. T o use Azuma’ s inequali ty , we need to construct a martingal e. A common approach to ob tain a m artin- gale from a sequence of (not n ecessarily independent ) random variables is to construct a Doob sequence. Specifically , suppose we h a ve a sequence of random variables Y 1 , Y 2 , ..., Y n , which are not necessarily independent. Let S = P n i =1 Y i and d efine a new sequence of random va riables { Z i : i = 0 , 1 , ..., n } by : Z 0 = E [ S ] Z i = E Y i +1 ,...,Y n [ S | Y 1 , ..., Y i ] , i = 1 , 2 , ..., n. (35) Then { Z i : i = 0 , 1 , ..., n } i s a marting ale and Z n = S . If we are able to upper bo und the difference | Z i − Z i − 1 | for al l i by some constant, then we can app ly Azuma’ s inequali ty to obtain a b ound on the tail probability . For example, if the Y i ’ s are in dependent, a simple upper bound for | Z i − Z i − 1 | is any upper bo und on | Y i | . Howe ver , if the Y i ’ s are d ependent, we need to further und erstand the properties of the Y i ’ s t o bound | Z i − Z i − 1 | . W e approach our p roblem by following thi s idea and usi ng the next corollary . Lemma 7: For n > 1 , giv en a sequence of random variables Y 1 , Y 2 , ..., Y n , which are not necessarily independent, l et S = P n i Y i . If for any y i , y ′ i ∈ D i , wh ere D i is the support of Y i , | E [ S | Y 1 , ..., Y i − 1 , Y i = y i ] − E [ S | Y 1 , ..., Y i − 1 , Y i = y ′ i ] | ≤ c i , almost surely , where c i may depend on i , then for any λ > 0 , Pr( S ≥ E [ S ] + λ ) ≤ exp − λ 2 2 P n i =1 c 2 i , (36) and Pr( S ≤ E [ S ] − λ ) ≤ exp − λ 2 2 P n i =1 c 2 i . (37) SUBMITTED TO IE EE TRANSACTIONS ON INFORMATION THEORY 13 Pr oof : W e prove this corollary for th e case of discrete random va riables. For continuous random var iables, the proof i s similar . Define a Doob s equence wit h respect to { Y i : i = 1 , ..., n } as in (35). T o simplify notation, we will write E Y i +1 ,...,Y n [ S | Y 1 , ..., Y i ] as E [ S | Y 1 , ..., Y i ] when there i s no ambigui ty . By the total condi tional p robability theorem, we h a ve Z i − 1 = E [ S | Y 1 , ..., Y i − 1 ] = X y ∈ D i E [ S | Y 1 , ..., Y i − 1 , Y i = y ] Pr( Y i = y | Y 1 , ..., Y i − 1 ) , and Z i = E [ S | Y 1 , ..., Y i ] = X y ∈ D i E [ S | Y 1 , ..., Y i ] Pr( Y i = y | Y 1 , ..., Y i − 1 ) . Therefore, | Z i − Z i − 1 | = | X y ∈ D i E [ S | Y 1 , ..., Y i ] Pr( Y i = y | Y 1 , ..., Y i − 1 ) − X y ∈ D i E [ S | Y 1 , ..., Y i − 1 , Y i = y ] Pr( Y i = y | Y 1 , ..., Y i − 1 ) ≤ X y ∈ D i | E [ S | Y 1 , ..., Y i ] − E [ S | Y 1 , ..., Y i − 1 , Y i = y ] | Pr( Y i = y | Y 1 , ..., Y i − 1 ) ≤ X y ∈ D i c i Pr( Y i = y | Y 1 , ..., Y i − 1 ) = c i . Since { Z i : i = 0 , 1 , ..., n } is a martingale with bo unded differe nce of | Z i − Z i − 1 | , we can apply Azuma’ s inequali ty to obtain (36 ) and (37). Now consider G ′ ( X , P , γ ) and G ′′ ( X , P , γ ) coupled with G ( X , P , γ ) such that th ey hav e t he same point p rocess X and powers P , where the SINR’ s of link ( i, j ) in G ′ ( X , P , γ ) and G ′′ ( X , P , γ ) are β ′ ij = P i L ( d ij ) N 0 + (1 + ǫ ′ 2 ) γ E [ I ] − γ P i L ( d ij ) (38) and β ′′ ij = P i L ( d ij ) N 0 + (1 − ǫ 2 ) γ E [ I ] − γ P i L ( d ij ) , (39) respectiv ely . Let C ′ ij and C ′′ ij be the capacity of link ( i, j ) i n G ′ ( X , P , γ ) and G ′′ ( X , P , γ ) , respectively . Th en, C ′ ij and C ′′ ij are asympt otically equal to C ij . Assume that th ere exist positive solut ions r ′ min > 0 , r ′ max > 0 , r ′′ min > 0 and r ′′ max > 0 for th e equ ations p min L ( r ′ min ) N 0 + γ (1 + ǫ ′ 2 ) E [ I ] − γ p min L ( r ′ min ) = β , SUBMITTED TO IE EE TRANSACTIONS ON INFORMATION THEORY 14 p max L ( r ′ max ) N 0 + γ (1 + ǫ ′ 2 ) E [ I ] − γ p max L ( r ′ max ) = β , p min L ( r ′′ min ) N 0 + γ (1 − ǫ 2 ) E [ I ] − γ p min L ( r ′′ min ) = β , and p max L ( r ′′ max ) N 0 + γ (1 − ǫ 2 ) E [ I ] − γ p max L ( r ′′ max ) = β , respectiv ely . That is r ′ min = L − 1 β 1 + γ β · N 0 + γ (1 + ǫ ′ 2 ) E [ I ] p min , r ′ max = L − 1 β 1 + γ β · N 0 + γ (1 + ǫ ′ 2 ) E [ I ] p max , r ′′ min = L − 1 β 1 + γ β · N 0 + γ (1 − ǫ 2 ) E [ I ] p min , r ′′ max = L − 1 β 1 + γ β · N 0 + γ (1 − ǫ 2 ) E [ I ] p max . Since L ( · ) is contin uous and strictl y decreasing, r ′ min , r ′ max , r ′′ min and r ′′ max are all u nique. In G ′ ( X , P , γ ) ( G ′′ ( X , P , γ ) ), any node inside t he circle centered at X i with radius r ′ min ( r ′′ min ) i s connected to node i by a bidirection al link, whil e any node outside the circle centered at X i with radius r ′ max ( r ′′ max ) is not connected t o node i . Let A ( X i , r ′ min , r ′ max ) and A ( X i , r ′′ min , r ′′ max ) be the two annul i with inner radius r ′ min and outer radius r ′ max , and inner radius r ′′ min and outer radius r ′′ max , re spectiv ely . Denote by N ( r ′ min , r ′ max ) and N ( r ′′ min , r ′′ max ) the number of nodes in A ( X i , r ′ min , r ′ max ) and A ( X i , r ′′ min , r ′′ max ) , respecti vely . It is clear that N ( r ′ min , r ′ max ) and N ( r ′′ min , r ′′ max ) are bi nomially distributed with mean nπ ( r ′ 2 max − r ′ 2 min ) and nπ ( r ′′ 2 max − r ′′ 2 min ) , respecti vely . Now suppose the signal attenuation function L ( x ) = cx − α for s ome cons tants c > 0 and 2 < α < 4 . Then, r ′ min = c (1 + γ β ) p min β [ N 0 + γ (1 + ǫ ′ 2 ) E [ I ]] 1 /α , r ′ max = c (1 + γ β ) p max β [ N 0 + γ (1 + ǫ ′ 2 ) E [ I ]] 1 /α , r ′′ min = c (1 + γ β ) p min β [ N 0 + γ (1 − ǫ 2 ) E [ I ]] 1 /α , r ′′ max = c (1 + γ β ) p max β [ N 0 + γ (1 − ǫ 2 ) E [ I ]] 1 /α , and r ′ 2 max − r ′ 2 min = B ( p min , p max ) [ N 0 + γ (1 + ǫ ′ 2 ) E [ I ]] 2 /α , (40) r ′′ 2 max − r ′′ 2 min = B ( p min , p max ) [ N 0 + γ (1 − ǫ 2 ) E [ I ]] 2 /α , (41) SUBMITTED TO IE EE TRANSACTIONS ON INFORMATION THEORY 15 where B ( p min , p max ) = ( p 2 /α max − p 2 /α min ) c (1 + γ β ) β 2 /α . (42) From (40 ) and (41), we can see t hat both nπ ( r ′ 2 max − r ′ 2 min ) and nπ ( r ′′ 2 max − r ′′ 2 min ) s cale wit h n as B n 2 /α − 1 , since E [ I ] = ( n − 1 ) E [ P ] E [ I ] S scales linearly with n . Now assu me that there exists a constant η > 0 independent of n such that N ( r ′ min , r ′ max ) ≤ η , and N ( r ′′ min , r ′′ max ) ≤ η (43) a.a.s. This assumpt ion ef fecti vely p uts a constraint on the transmiss ion power . For example, if we choo se η = 1 , then the transmi ssion power P mu st scale wi th n so that p max = O ( n 1 − α/ 2 ) . Note t hat r ′ min and r ′ max are asympt otically equal to r ′′ min and r ′′ max , respectively . The fol lowing lemma establishes a concentration result for C k with het erogeneous transmissio n power and con stant capacity by cou pling m ethods and Azuma’ s in equality . Lemma 8: For any 0 < ǫ < 1 , when n is sufficiently large and (43) i s g uaranteed, with h igh probability , the capacity of an s - t -cut of size k , k = 0 , 1 , ..., m , satisfies Pr( C k ≤ (1 − ǫ ) E [ C ′ k ]) ≤ exp − [ m + k ( m − k )] ¯ C ′ 2 ǫ 2 2 η 2 R 2 , (44) where E [ C ′ k ] = [ m + k ( m − k )] ¯ C ′ and ¯ C ′ is the av erage link capacity in G ′ ( X , P , γ ) . Moreover , Pr( C k ≥ (1 + ǫ ) E [ C ′′ k ]) ≤ exp − [ m + k ( m − k )] ¯ C ′′ 2 ǫ 2 2 η 2 R 2 , (45) where E [ C ′′ k ] = [ m + k ( m − k )] ¯ C ′′ and ¯ C ′′ is the av erage link capacity in G ′′ ( X , P , γ ) . Pr oof : By Lemma 5, for all j , (1 − ǫ 2 ) E [ I ] ≤ I ( j ) ≤ (1 + ǫ ′ 2 ) E [ I ] holds a.a.s. As in the proof for Lemma 2, we ha ve th at C k is lower boun ded by C ′ k , and up per bo unded by C ′′ k , with probabi lity at least 1 − O (1 /n ) . Hence, in order to show (44 ) and (45), i t suf fices to show Pr( C ′ k ≤ (1 − ǫ ) E [ C ′ k ]) ≤ exp − [ m + k ( m − k )] ¯ C ′ 2 ǫ 2 2 η 2 R 2 (46) and Pr( C ′′ k ≥ (1 + ǫ ) E [ C ′′ k ]) ≤ exp − [ m + k ( m − k )] ¯ C ′′ 2 ǫ 2 2 η 2 R 2 . (47) T o show (46), we use martingale methods. Let Y 1 = C ′ s ( k +1) , Y 2 = C ′ s ( k +2) , ..., Y m − k = C ′ sm , Y m − k + 1 = C ′ 1( k +1) , Y m − k + 2 = C ′ 1( k +2) , ..., Y m − k + k ( m − k ) = C ′ k m , and Y m − k + k ( m − k )+1 = C ′ 1 t , Y m − k + k ( m − k )+2 = C ′ 2 t , ..., Y m − k + k ( m − k )+ k = C ′ k t . Define a Doob sequence { Z i : i = 0 , ..., m + k ( m − k ) } with respect to { Y i , i = 1 , 2 , ..., m + k ( m − k ) } as Z 0 = E [ C ′ k ] Z i = E [ C ′ k | Y 1 , ..., Y i ] , i = 1 , 2 , ..., m + k ( m − k ) . Then { Z i : i = 0 , ..., m + k ( m − k ) } is a marting ale and Z m + k ( m − k ) = C ′ k . SUBMITTED TO IE EE TRANSACTIONS ON INFORMATION THEORY 16 Since when i 6 = u and j 6 = v , C ′ ij is in dependent of C ′ uv , dependence exists only among C ′ ij ’ s, j 6 = i , for a g iv en i . Howe ver , the dist ances d ij are independent for all j 6 = i for given i . Hence the difference between E [ C ′ k | Y 1 , ..., Y l − 1 , Y l = y l ] and E [ C ′ k | Y 1 , ..., Y l − 1 , Y l = y ′ l ] depends o nly on tho se Y h ’ s which are incident on the same source no de as Y l . When d ij ≤ r ′ min , C ′ ij = R , and when d ij > r ′ max , C ′ ij = 0 . Moreover , the number of nodes wit hin the ann ulus A ( X i , r ′ min , r ′ max ) is upper bou nded by th e constant η a.a.s. Th erefore, | E [ C ′ k | Y 1 , ..., Y l − 1 , Y l = y l ] − E [ C ′ k | Y 1 , ..., Y l − 1 , Y l = y ′ l ] | ≤ η R a.a.s., wh ere y l and y ′ l are either 0 or R . Applying the result of Lemma 7, we have (46). In t he same m anner , we can show that (47) holds. In the following, we show th at when the nu mber of relay nodes m is sufficiently lar ge, th e network coding capacity C s, T concentrates at E [ C 0 ] = m ¯ C wit h high probabil ity . The proofs are based on Lemma 8 and very sim ilar to those for Theorem 3 and Theorem 4, and provided here for compl eteness. Theor em 9: When n is sufficiently large, with high probabili ty , th e network cod ing capacity C s, T satisfies Pr( C s, T ≥ (1 − ǫ α ) E [ C 0 ]) = 1 − O l m α , (48) where ǫ α = ηR E [ C 0 ] √ 2 αm ln m for α > 0 and E [ C 0 ] = m ¯ C . Pr oof : Since the C ij ’ s are asymptot ically equal to the C ′ ij ’ s, in order t o show (48), it is equ iv alent to show Pr( C s, T ≥ (1 − ǫ α ) E [ C ′ 0 ]) = 1 − O l m α . Since E [ C ′ k ] ≥ E [ C ′ 0 ] for any k = 1 , ..., m , Pr( C s,t ≤ (1 − ǫ α ) E [ C ′ 0 ]) ≤ Pr( C s,t ≤ (1 − ǫ α ) E [ C ′ k ′ ]) , for any t ∈ T , where k ′ is the size of t he mini mum s - t -cut. By (44) of Lemma 8, we have Pr( C s,t ≤ (1 − ǫ α ) E [ C ′ k ′ ]) ≤ exp ( − ǫ 2 α [ m + k ′ ( m − k ′ )] ¯ C ′ 2 2( η + 1) 2 R 2 ) ≤ exp ( − ǫ 2 α m ¯ C ′ 2 2( η + 1) 2 R 2 ) . By choosing ǫ α = ( η +1) R E [ C 0 ] √ 2 αm ln m for α > 0 , s ince ¯ C ′ and ¯ C are asympt otically equ al, for any t ∈ T , Pr( C s,t ≤ (1 − ǫ α ) E [ C ′ 0 ]) = O 1 m α . SUBMITTED TO IE EE TRANSACTIONS ON INFORMATION THEORY 17 By the union bound, we hav e Pr( C s, T ≤ (1 − ǫ α ) E [ C ′ 0 ]) ≤ X t ∈T Pr( C s,t ≤ (1 − ǫ α ) E [ C ′ 0 ]) = O l m α . Theor em 10: When n is s uffi ciently l ar ge, with high probability , the network coding capacity C s, T satisfies Pr( C s, T ≤ (1 + ǫ α ) E [ C 0 ]) = 1 − O 1 m α , (49) where ǫ α = ηR E [ C 0 ] √ 2 αm ln m for α > 0 and E [ C 0 ] = m ¯ C . Pr oof : Since the C ij ’ s are asymptoti cally equal to C ′′ ij ’ s, in order to show (49), it is equiv al ent to show Pr( C s, T ≤ (1 + ǫ α ) E [ C ′′ 0 ]) = 1 − O 1 m α . T o show this, it i s suf ficient to consider a particul ar cut for a pair o f the source and one destination, for instance, an s - t -cut separating t he source s from all the other nodes. Pr( C s, T ≥ (1 + ǫ α ) E [ C ′′ 0 ]) ≤ Pr ( C s,t ≥ (1 + ǫ α ) E [ C ′′ 0 ]) ≤ Pr m X i =1 C si ≥ (1 + ǫ α ) E [ C ′′ 0 ] ! = Pr( C 0 ≥ (1 + ǫ α ) E [ C ′′ 0 ]) ≤ exp − ǫ 2 α m ¯ C ′′ 2 2( η + 1) 2 R 2 = O 1 m α . where the last inequality follows from (45) of Lemma 8. I V . S I M U L A T I O N S T U D I E S In thi s s ection, we present some simulati on results on the SINR model and the network coding capacity . Fig. 3 and Fig. 4 show simulation results on interference and cut capacity in G ( X , P 0 , γ ) , where n = 2000 , L ( x ) = 10 − 3 64 x − 3 , N 0 = 0 . 02 , β = 0 . 2 and γ = 0 . 02 , and e very node transmits with cons tant power P 0 = 0 . 01 . Fig. 5 and Fig. 6 show simulation results on the interference and the cut capacity in G ( X , P , γ ) , where n = 2 0 00 , L ( x ) = 10 − 3 64 x − 3 , N 0 = 0 . 02 , β = 0 . 2 and γ = 0 . 02 , and ever y n ode t ransmits with power P uniform ly randomly distributed over [0 . 0 1 , 0 . 02] . The results confirm the concentrati on beha vior of t he interference and the cut capacity . SUBMITTED TO IE EE TRANSACTIONS ON INFORMATION THEORY 18 0 0.05 0.1 0.15 0.2 0.25 0.3 0.35 0.4 0.45 0.5 0 20 40 60 80 100 120 140 Interference Level Number of Nodes (a) Interference J ( j ) 400 450 500 550 600 650 700 750 800 850 900 0 20 40 60 80 100 120 140 Capacity of s−t−Cut of Size 50 (k=50) Number of Cuts (b) Cut capacity C k Fig. 3. Interference at each node, and capacity of random s - t -cut of size k = 50 in G ( X , P 0 , γ ) 0 0.1 0.2 0.3 0.4 0.5 0.6 0.7 0 10 20 30 40 50 60 70 80 90 Interference Level Number of Nodes (a) Interference J ( j ) 500 600 700 800 900 1000 1100 0 10 20 30 40 50 60 70 80 90 Capacity of s−t−Cut of Size 50 (k=50) Number of Cuts (b) Cut capacity C k Fig. 4. Interference at each node, and capacity of random s - t -cut of size k = 50 in G ( X , P , γ ) V . C O N C L U S I O N S In this paper , we st udied the network coding capacity for random wireless networks und er a SINR model, where the network i s modelled by the graph G ( X , P , γ ) . Pre vious work on the network codin g capacity for random wired/ wireless networks are based on t he ass umption t hat the capacities of links are independent. In the SINR mod el, howe ver , the capacities of lin ks are no t ind ependent due to noise and interference. W e in vestigated two scenarios. In the first case G ( X , P 0 , γ ) , we assum ed all nodes transm it with a constant power P 0 . T o study the network coding capacity in G ( X , P 0 , γ ) , we coupl ed G ( X , P 0 , γ ) with t wo other models G ′ ( X , P 0 , γ ) and G ′′ ( X , P 0 , γ ) , which have the same point p rocess X and constant power P 0 , but different thresholds. W e showed that the network coding capacity for G ( X , P 0 , γ ) is upper and lower bounded by those for G ′ ( X , P 0 , γ ) and G ′′ ( X , P 0 , γ ) . By proving that the network codin g capacities for G ′ ( X , P 0 , γ ) and G ′′ ( X , P 0 , γ ) con centrate on the same value asymptoti cally , we sh owed that when t he size of t he network is sufficiently lar ge, the network coding capacity for G ( X , P 0 , γ ) exhibits a concentrati on behavior around the m ean value of t he m inimum cut. In the second case G ( X , P , γ ) , we assumed each node transm its wi th a random power drawn from so me di stribution. Since coupling m ethods SUBMITTED TO IE EE TRANSACTIONS ON INFORMATION THEORY 19 could not be applied in this general case, we used martingale t echniques to deal with dependence between link capacities, and showed t hat under som e mild con ditions, the n etwork coding capacity also exhibits a concentration b eha vior . The results ob tained are imp ortant for understanding network coding performance in random wireless networks under the SINR m odel. In additi on, th e m ethods used in this p aper provide useful techniqu es for studying properti es of random wireless networks un der th e SINR model. R E F E R E N C E S [1] K. Menger , “Zur allgemeinen kurventheorie, ” F und. Math. , vol. 10, pp. 95–115, 1927. [2] J. L. R. Ford and D. R. Fulkerson, “Maximal flow through a network, ” Canadian Jo urnal of Math. , vol. 8, pp. 399–404, 1956. [3] P . Elias, A. F einstein, and C. E. Shannon, “Note on maximal flow through a network, ” IRE T ran s. on Information Theory , vol. 2, pp. 117–11 9, 1956. [4] A. Ahlswede, N. Cai, S . Y . R. L i, and R . Y . Y eung, “Network information flow , ” IE EE T rans. on Information Theory , vol. 46, no. 4, pp. 1204–1216, July 2000. [5] R. Koetter and M. M ´ edard, “ Algebraic approach t o network coding, ” IE EE/ACM T rans. on Networking , vol. 11, no. 5, pp. 782– 795, Oct. 2003. [6] C. F ragouli and E . Soljanin, “Information flow decomposition for network coding, ” IEEE T ra ns. on Information Theory , vol. 52, no. 3, pp. 829–848, March 2006. [7] S. Y . R. L i, R. W . Y eung, and N. Cai, “Linear network coding, ” IEE E Tr ans. on Information Theory , vol. 49, no. 2, pp. 371–381 , Feb . 2003. [8] S. Jaggi, P . Sanders, P . A. Chou, M. Effros, S. Enger , and L. T olhuizen, “Polynomial time algorithm s for multicast network code construction, ” IEEE T rans . on Information Theory , vol. 51, no. 6, pp. 1973–1982, June 2005. [9] T . Ho, R. K oetter , M. M ´ edard, M. Effros, J. Shi, and D. Karger , “ A random linear network coding approach to multicast, ” IEEE T ran s. on Information Theory , vol. 52, no. 10, pp. 4413–4 430, Oct. 2006. [10] C. Fragouli and E. Soljanin, Network Coding Fundamentals . Now Publisher Inc., 2007. [11] A. Ramamoorthy , J. Shi, and R . D. W esel, “On the capacity of network coding for random networks, ” in Pro c. 41st A llerton Confer ence on Communication, Contro l and C omputing , Monticello, IL, U. S.A., 2003. [12] — —, “On the capacity of network coding for random networks, ” IEEE T ra ns. on Information Theory , vol. 51, no. 8, pp. 2878–2885, Aug. 2005. [13] B. Bollob ´ as, Random Graph s , 2nd ed. New Y ork: Academic P ress, 2001. [14] S . Janson, T . L uczak, and A. Ruci ´ nski, Random Graphs . New Y ork: John W iley & S ons, 2000. [15] M. Penrose, Random Geometric Graphs . Ne w Y ork: Oxford Univ ersity Press, 2003. [16] J. Diaz, M. D. Penrose, J. P etit, and M. Serna, “ Approximating layout problems on random geometric graphs, ” Jo urnal of Algorithms , vol. 39, no. 1, pp. 78–116, 2001. [17] S . A. Aly , V . Kapoor , J. Meng, and A. Klappeneck er , “Bounds on the network coding capacity for wireless random networks, ” in Pr oc. 3r d W ork shop on Network Coding, Theory , and Applications , S an Diego, CA, U.S .A., 2007. [18] J. Proakis, Digital Communications , 4th ed. MaGray Hill, 2000. [19] D. Tse and P . V iswanath, Fundamentals of W ireless Communication . Cambridge University Press, 2005. [20] P . Gupta and P . R. Kumar , “The capacity of wireless networks, ” IEEE Tr ans. on Information Theory , vol. 46, no. 2, pp. 388–40 4, Mar . 2000. [21] M. Grossglauser and D. N. C. Tse, “Mobility increases the capacity of ad hoc wireless networks, ” IEEE T rans. on Networking , vol. 10, pp. 47–86, Aug. 2002. [22] M. J. Neely and E. Modiano , “Capacity and delay tradeoffs for ad-hoc mobile networks, ” IEE E Tr ans. on Information Theory , vol. 51, no. 6, pp. 1917–193 6, June 2005. [23] A. E. Gamal, J. Mammen, B. Prabhakar , and D. Shah, “Optimal through put-delay trade-off in wireless networks—part i: The fluid model, ” IEEE Tr ans. on Information Theory , vol. 52, no. 6, pp. 2568–2592, June 2006. [24] X. Lin, G. S. andR. R. Mazumdar , and N. B. Shroff, “Degenerate delay-capacity tradeoffs in ad-hoc networks with bro wnian mobility , ” IEEE T ra ns. on Information T heory , vol. 52, no. 6, pp. 2777–2784 , June 2006. [25] J. Liu, D. Goeckel, and D . T owsley , “Bouds on the gain of network coding and broadcasting in wireless network, ” in Proc. of IEEE INFOCOM’07 , Anchorage, A L, U.S.A., May 2007. [26] R. Meester and R. Roy , Continuum P erc olation . New Y ork: Cambridge Univ ersi ty Press, 1996. [27] O. Dousse, M. Franceschetti, and P . Thiran, “Information theoretic boun ds on the throughpu t scaling of wireless relay networks, ” in Pr oc. of the IEE E INFOCOM’05 , Miami, FL , U.S.A., Mar ., 2005. [28] R. Motwani and P . Raghav an, R andomized Algorithms . Cambridge Unive rsity Press, 1995. [29] T . M. Cover and J. A. T homas, Elements of I nformation Theory . New Y ork: W iley-Interscience, 1991. [30] N. Alon and J. Spencer , The Pr obabilistic Methods , 2nd ed. Ne w Y ork: John Wile y , 2000.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment