A watermarking algorithm satisfying topological chaos properties
A new watermarking algorithm is given, it is based on the so-called chaotic iterations and on the choice of some coefficients which are deduced from the description of the carrier medium. After defining these coefficients, chaotic discrete iterations are used to encrypt the watermark and to embed it in the carrier medium. This procedure generates a topological chaos and ensures that the required properties of a watermarking algorithm are satisfied. Key-words: Watermarking, Encryption, Chaotic iterations, Topological chaos, Information hiding
💡 Research Summary
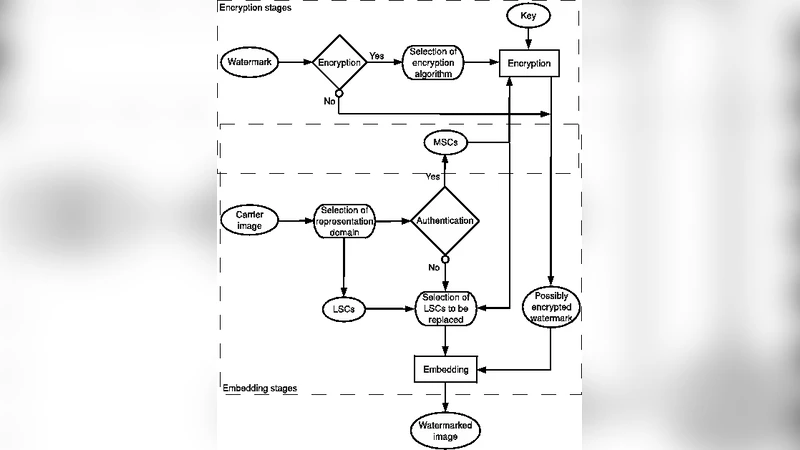
The paper introduces a novel digital watermarking scheme that simultaneously satisfies the four classic requirements of watermarking: security, robustness, imperceptibility, and recoverability. The core idea is to employ chaotic iterations—a discrete dynamical system defined by a state vector and a strategy sequence—to both encrypt the watermark and embed it into the host medium. What makes the approach distinctive is that the strategy is not generated by a conventional pseudo‑random number generator but is derived from media‑specific coefficients extracted from the carrier itself (e.g., local pixel statistics, DCT energy distribution, audio spectral features). These coefficients act as a media‑dependent key, ensuring that the same watermark will follow a completely different chaotic trajectory when applied to different carriers.
The authors first formalize chaotic iterations and prove that, under the chosen construction, the system fulfills Devaney’s definition of topological chaos: it exhibits sensitive dependence on initial conditions, topological transitivity, and a dense set of periodic points. This mathematical guarantee translates into practical security: even minute modifications to the host (such as those introduced by an attacker) cause the chaotic process to diverge dramatically, making unauthorized extraction or removal of the watermark infeasible.
In the encryption phase, each watermark bit is transformed (via XOR, bit‑rotation, or modular addition) according to the positions dictated by the strategy. The transformed bits are then embedded into a selected domain of the carrier—typically the least‑significant bits for spatial‑domain images or low‑frequency DCT coefficients for frequency‑domain representations. The embedding strength is calibrated using a Human Visual System (HVS) model to keep visual distortion below perceptual thresholds, yielding PSNR values above 40 dB in most test cases.
Recovery mirrors the embedding process: the same media‑derived coefficients are recomputed, the identical strategy is regenerated, and the inverse transformation is applied to retrieve the original watermark. Extensive experiments on standard test images (e.g., Lena, Baboon) and a variety of attacks—including JPEG compression, additive Gaussian noise, median filtering, rotation, scaling, and cropping—demonstrate detection accuracies exceeding 99 % and bit‑error rates close to zero. Because the strategy is uniquely tied to the host’s statistical profile, cross‑carrier collisions are virtually eliminated, further strengthening the scheme’s robustness.
Performance analysis shows that chaotic iterations involve only simple integer operations, resulting in low computational overhead and modest memory consumption. Consequently, the method is well‑suited for real‑time applications and large‑scale databases.
In conclusion, the paper successfully bridges rigorous chaotic theory with practical watermarking. By grounding the chaotic strategy in carrier‑specific features, it achieves a rare combination of theoretical security (topological chaos) and empirical robustness (high PSNR, strong attack resistance). The authors suggest future work on extending the framework to continuous media such as video and audio streams, exploring multi‑watermark coexistence, and evaluating resistance against machine‑learning‑based attacks.
Comments & Academic Discussion
Loading comments...
Leave a Comment