Non binary LDPC codes over the binary erasure channel: density evolution analysis
In this paper we present a thorough analysis of non binary LDPC codes over the binary erasure channel. First, the decoding of non binary LDPC codes is investigated. The proposed algorithm performs on-the-fly decoding, i.e. it starts decoding as soon …
Authors: Valentin Savin
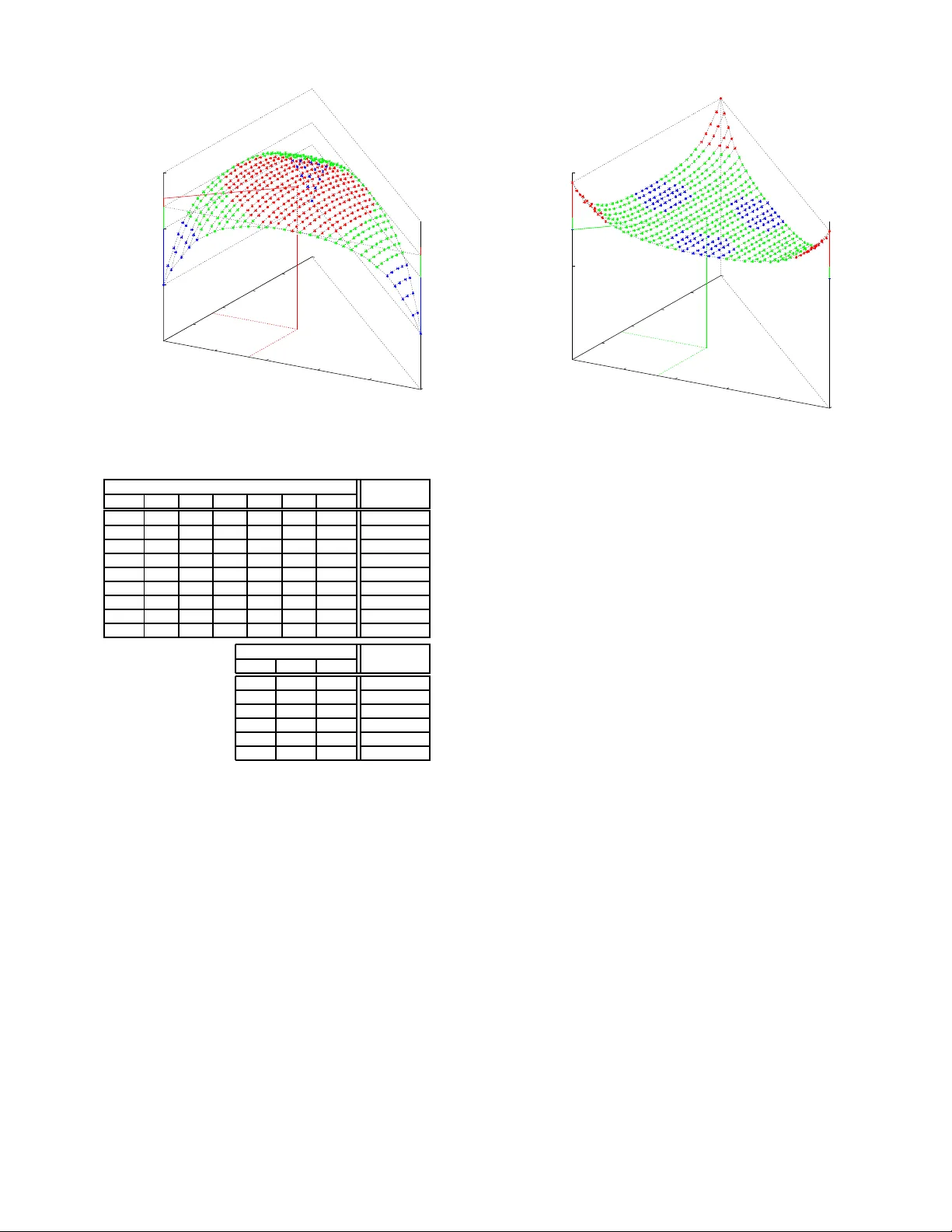
Non binary LDPC codes o v er the binary erasure channel: density e v olution analysis V alentin Savin, CEA-LETI, MIN A TEC, Grenob le, France, valentin.savin@cea.fr Abstract — In this paper we present a thorough analysis of non binary LDPC codes ov er the binary erasure channel. First, the decoding of non binary LDPC codes is inv estigated. The proposed algorithm perfo rms “on-the fly” decoding, i.e. it starts decodin g as soon as the first symbols are receiv ed, which generalizes the erasure d ecoding of bi nary LDP C codes. Next, we ev aluate the asymptotical perfo rmance of ensembles of non binary LDPC codes, by usin g the density ev olution method. Density evolution equations are d eriv ed by tak ing i nto consideration both the irregularity of the b ipartite graph and the probability distribution of th e graph edge labels . Fi nally , infi nite-length perfor mance of some ensembles of non bin ary LDP C codes for dif ferent edge label distributions ar e shown. I . I N T R O D U C T I O N Data loss recovery – for instance, for content distribution applications or for distributed storage systems – is widely addressed using FEC (Forward Er ror Correction) techniqu es based on error correcting codes. T hese co des are dealing with erasure channels, i.e. a ch annel that either transmits th e d ata unit corre ctly ( without erro r) or erases it co mpletely . In the case o f co ntent distribution ap plications, th e po tential p hysical layer CRC, or ph ysical la yer FEC codes, or transport lev el UDP check sums, may lead a receiver to d iscard erro neous data units. For distributed stor age systems, da ta lo ss may b e due to bro ken servers, Denial-of-Servic e (DoS) attacks, etc. The per formanc e of erro r co rrecting codes over er asure channels can b e an alyzed precisely , and a flurry of r esearch papers h av e alrea dy addressed this issue. Low-density parity- check (LDPC) codes [1], [2] with iterati ve decoding [3 ] proved to perform very close to the chan nel ca pacity w ith reasonable complexity [4] [5]. Moreover, “rateless” cod es that are cap able of generatin g an infin ite seq uence o f r epair symbols were pro- posed in [6] [7]. L DPC co des were ge neralized b y T anner [8], by introd ucing the sparse gr aph r epresentation and r eplacing the Sing le Parity Check (SPC) constraint n odes with error correcting b lock codes. Nowadays, th ese cod es are known as GLDPC cod es an d were recently in vestigated for the BEC [ 9], [10], [1 1]. Over the past few years th ere has been a n in creased interest in non binary LDPC codes due to their enhanc ed correction capacity , b ut at th is time on ly few w orks are d ealing with the BEC [12],[13]. In th is p aper we give a thoro ugh analysis of non binary LDPC codes o ver the BEC. The paper is organized as follows: in Section II we r evie w so me backgro und on the con struction o f no n b inary LDPC codes. The de coding of non b inary LDPC codes over the BEC is ad dressed in This w ork has been supporte d by the French ANR grant N 2006 TCOM 019 (CAPRI-FEC project) Section III. In Section IV we derive the density ev olution equations taking in to consider ation b oth the ir regularity o f the bipartite graph an d the probab ility distribution of the graph edge la bels. T hresholds of som e en sembles of no n bin ary LDPC codes for different ed ge labe l distributions are shown in Section V. I I . N O N B I N A RY L D P C C O D E S W e d enote by F q the Galois field with q elem ents. For practical reasons, we will assume that q is a power of 2 , e ven if this condition is no t always necessary . Thus, we set q = 2 p , where p is the vecto r space dime nsion of F q over F 2 (each time we r efer to F q as a vector space, we con sider its F 2 - vector sp ace structure) . W e fix once for all an iso morphism of F 2 -vector spaces: F p 2 ∼ → F q (1) and we say that ( b 0 , . . . , b p − 1 ) ∈ F p 2 are the con stituent bits of the symbol s ∈ F q , if they corre spond to each other by th e above isomorphism. Let L be a multiplica ti ve gro up actin g on the vector sp ace F q . For in stance, we may h av e: • L = F ∗ q , actin g on F q via th e inter nal field multiplication ; • L = M ∗ p ( F 2 ) , the multiplicativ e grou p of inv ertible p × p matrices, acting o n F q via the isomor phism F p 2 ∼ → F q from (1). The action o f L o n F q will a lw ays b e de noted mu ltiplicativ ely , that is: L × F q → F q : ( h, s ) 7→ hs (2) For any matrix H ∈ M M ,N ( L ) o ne can define a code: C = ker( H ) (3) = { ( s 1 , . . . , s N ) | N X n =1 h m,n s n = 0 , ∀ m = 1 , . . . , M } If L = F ∗ q acting o n F q via the internal field mu ltiplication, then C is a F q -linear code, but this d oes not h appen for g eneral L . The T anner graph associated with the code C , denoted by H , consists of N variable nodes and M check nod es r epresenting the N column s and the M lines of the matrix H . A variable node an d a check no de are connec ted by an edge if the correspo nding element of matrix H is not zero. Each ed ge of the g raph is lab eled b y the co rrespond ing no n zer o element of H . Thu s, fro m n ow on, we refer to the elemen ts of L as labels . W e also deno te H ( n ) the set of check node s conn ected to a given variable no de n ∈ { 1 , 2 , . . . , N } , and b y H ( m ) the set o f variable n odes con nected to a given c heck no de m ∈ { 1 , 2 , . . . , M } . A. The bina ry image of a non binary code Any sequence ( s 1 , . . . , s N ) ∈ F N q may be map ped into a b inary seque nce of len gth N p via the isomor phism of (1). The binary sequences associated with the codew ord s ( s 1 , . . . , s N ) ∈ C constitute a linear binar y co de C bin ⊆ F N p 2 , which is c alled the b inary image of C . Moreover , th e action (2) of th e m ultiplicative lab el g roup L on F q induces a group morph ism from L into the gro up o f vector space endomo rphisms L F 2 ( F q , F q ) , and id entifying F q and F p 2 via (1), we get a mor phism: L → L F 2 ( F q , F q ) ∼ → L F 2 ( F p 2 , F p 2 ) = M p ( F 2 ) (4) Replacing each coefficient o f the matrix H ∈ M M ,N ( L ) with its image under the above m orphism, we obtain a binary matrix H bin ∈ M M p,N p ( F 2 ) , which is simply the parity ch eck m atrix of the b inary co de C bin . While the encodin g may be p erform ed using eith er the non binar y cod e or its binary image, th e iterativ e d ecoding o f a non b inary co de on its binary image generally yie lds very po or perfor mance. I I I . D E C O D I N G N O N B I N A RY L D P C C O D E S For gener al chann els, several decoding algorithms fo r non binary LDPC co des were proposed in the literature [14], [15], [16]. Because of the BEC sp ecificity , these algorith ms are all equiv alent over the BEC, and they can be d escribed in a sligh tly different manner, as pr esented below . A. Deco ding over th e BEC In this section we assume that a non binary LDPC cod e is used over BEC( ǫ ) – the binary erasure ch annel with er asure probab ility ǫ . Thus, the length N seque nce of encod ed F q - symbols is mappe d in to the correspon ding b inary sequ ence of length N p , which is transmitted over the BEC, each bit from the binary seq uence being erased with prob ability ǫ . W e say that a F q -symbol is : • r eceived , if all of its constituent b its are r eceiv ed; • erased , if all of its constituent bits are er ased by the channel; • partially erased , if some of its constituent bits are erased by the channel and some others are received. At the receiver par t, the received bits are used to reconstru ct the co rrespond ing F q -symbols. T he recon struction may b e complete, p artial, or lacking , accordin g to wh enever the co r- respond ing symbol is receiv ed, pa rtially erased, or erased . Let n be a variable node of the T anner graph and s ∈ F q . W e say that the symbol s is eligible at the v ariab le node n , if the probab ility of the n th transmitted symbol being s is non zero. T acking into consideration the channel outpu t, the a priori set of eligible symbols , d enoted by E n , con sists of th e symbols that fit with the received co nstituent bits (if any) of the n th transmitted sym bol. Thus : • E n = F q , if the sym bol is erased, • E n F q , if the sym bol is partially erased, • card ( E n ) = 1 , if the symbol is received. These sets constitute the a priori information of the decoder . They are iteratively updated b y exchan ging extrinsic messages between variable an d c heck nodes in the graph. E ach message is a subset of F q , rep resenting a set of eligible symbols. Precisely , the me ssage sen t by a graph nod e on an outgo ing edge is a set o f eligible sy mbols, which is comp uted accordin g to messages received by the same no de on the incoming edges. W e use th e fo llowing notation: • A m,n the set of eligible symbols sent by the variable node n to the ch eck node m ; • B m,n the set o f elig ible symbols sent by the check nod e m to the variable nod e n . Finally , if S , S 1 , S 2 ⊆ F q and h ∈ L we define: h S = { hs | s ∈ S } S 1 + S 2 = { s 1 + s 2 | s 1 ∈ S 1 , s 2 ∈ S 2 } The itera ti ve decoder f or the BEC can be expressed as follows: Initialization step • variable-to-check messages initialization A m,n = E n Iteration step • check-to -variable messages B m,n = X n ′ ∈H ( m ) \{ n } h m,n ′ A m,n ′ • variable-to-check messages A m,n = E n ∩ \ m ′ ∈H ( n ) \{ m } h − 1 m ′ ,n B m ′ ,n • a p osteriori sets of eligible symbols E n = E n ∩ \ m ∈H ( n ) h − 1 m,n B m,n The d ecoder stops when all the a po steriori sets of eligib le symbols E n are of cardin ality 1 , or whe n a maximum n umber of itera tions is reach ed. It is im portant to note that any set of elig ible symb ols ( E n , A m,n , B m,n , or E n ) is a F 2 -affine sub-space of F q ; in particu lar , its card inal is a power of 2 . B. Minimu m-delay deco ding In th is section we p ropose a min imum-delay d ecoding algorithm over the BEC, in th e sense that the d ecoding starts since the reception o f th e first bits, wh ich is suited f or Uppe r- Layer Forward Erro r Correction (UL- FEC). The minimum-d elay decoding of n on binary co des consists of rem oving symbols from th e sets of eligible symb ols: • initialize E n = F q , n = 1 , . . . , N • each time a new bit is received, identify the variable node n of which th e recei ved bit is a constituent bit, and then: A( n ): remove sy mbols from E n whose corresp onding constituent b it is different from the received bit B( n ): process th e check nod es m ∈ H ( n ) , then update the sets of eligible symb ols E n ′ ← E n ′ , for each n ′ ∈ H ( m ) \ { n } C( n ): For each of the ab ove n ′ s, if by updatin g E n ′ its cardinal h as be en reduced, g o to B( n ← n ′ ). The dec oder stops when all the sets E n are of cardinality 1 . 1) D ecoding inefficiency: It follows that the minimu m- delay deco ding is actually an on-the- fly im plementation of the previous iterative decod ing. A perfo rmance metric that is often associated with on-the- fly de coding is the de coding in- efficiency , defined as the r atio b etween th e n umber of received bits be fore dec oding stop s and the n umber o f in formation b its. Let K bin be th e bin ary dimension of th e cod e, and K received be the numbe r of re ceiv ed bits befo re de coding stops. Then the inefficiency µ is define d as: µ = K received K bin (5) The expectatio n of the rand om variable µ , denoted by µ m , is called average inefficiency . In practice µ m can be estimated by Mo nte-Carlo simulation. The average inefficiency of th e on-the- fly deco ding can be related to th e failure prob ability of the iterati ve decod ing (section II I). Precisely , for any ǫ ∈ [0 , 1] , let p ( ǫ ) be th e failure probab ility of th e iterative decoding a ssuming that ǫ is the channel erasure pr obability . Assuming th at the f unction p is integrable on [0 , 1 ] , we have: µ m − 1 = Z 1 0 p ( ǫ ) dǫ (6) I V . D E N S I T Y E VO L U T I O N Density ev olutio n for non b inary LDPC co des over the BEC was alread y d eriv ed in [12], assuming an uniform distrib ution on the edge labels. In loc. cit. , the authors suggest that the distribution of the edge labels represen ts a degree of freedom that shou ld b e integrated to o ur under standing of capacity approa ching iterativ e coding schemes. T o do so, we d eriv e the d ensity ev olution o f no n binar y co des tacking into consid- eration the variable and check nod es degree distributions, b ut also the probability d istribution o f the edge lab els. W e use the following notation: • λ d is the fraction of edges con nected to variable nod es of degree d , λ ( X ) = d v X d =1 λ d X d − 1 is the po lynomial of variable node degree distribution; • ρ d is the f raction of ed ges conne cted to check nodes of degree d , ρ ( X ) = d c X d =1 ρ d X d − 1 is the po lynomial of c heck node degree distribution; • f : L → [0 , 1] the pr obability d istribution fun ction defined by f ( h ) = fr action of e dges with label h ∈ L . By extendin g the n otation, f or a giv en sequen ce h = ( h 1 , . . . , h I ) we define f ( h ) = I Y i =1 f ( h i ) . W ithout losing generality , we m ay assume th at the all-ze ro codeword is transmitted . Th us, any set of eligible sy mbols ( E n , A m,n , B m,n , or E n ) is a F 2 -linear sub- spaces of F q . T able I giv es the list of the possible values of the a pr iori sets of eligib le symbo ls E n for the ca se of a F 8 -code, acco rding to the received binary sequence 1 . T ABLE I P O S S I B L E VAL U E S O F T H E A P R I O R I S E T S O F E L I G I B L E S Y M B O L S recei ved bits ∗ E n Pr( E n ) xxx F 8 ǫ 3 0 xx { 0 , 1 , 2 , 3 } ǫ 2 (1 − ǫ ) x 0 x { 0 , 1 , 4 , 5 } ǫ 2 (1 − ǫ ) xx 0 { 0 , 2 , 4 , 6 } ǫ 2 (1 − ǫ ) x 00 { 0 , 4 } ǫ (1 − ǫ ) 2 0 x 0 { 0 , 2 } ǫ (1 − ǫ ) 2 00 x { 0 , 1 } ǫ (1 − ǫ ) 2 000 { 0 } (1 − ǫ ) 3 ∗ Symbol x denotes an erased bit Let Gr ( F q ) be the Grassmannian of F q , that is the set of all F 2 -linear subspaces of F q . For V ∈ Gr ( F q ) , we note: P ℓ ( V ) = Pr( A ( ℓ ) m,n = V ) (7) Q ℓ ( V ) = Pr( B ( ℓ ) m,n = V ) (8) where superscrip t ( ℓ ) is u sed to denote sets of eligib le symbols computed at the ℓ th iteration. Thus, the d ecoding is success- fully if and on ly if: lim ℓ → + ∞ P ℓ ( { 0 } ) = 1 (9) In or der to simplify the notation, we define: • For any V ∈ Gr ( F q ) : γ ( V ) := P 0 ( V ) = P r( E n = V ) S ( I ) V := { V = ( V 1 , . . . , V I ) | I X i =1 V i = V } ⊆ Gr ( F q ) I I ( I ) V := { ( V 0 , V ) = ( V 0 , V 1 , . . . , V I ) | I \ i =0 V i = V } ⊆ Gr ( F q ) I +1 • For any h = ( h 1 , . . . , h I ) ∈ L I and V = ( V 1 , . . . , V I ) ∈ Gr ( F q ) I : h − 1 :=( h − 1 1 , . . . , h − 1 I ) , h · V :=( h 1 V 1 , . . . , h I V I ) • For any V = ( V 1 , . . . , V I ) ∈ Gr ( F q ) I : P ℓ ( V ):= I Y i =1 P l ( V i ) , Q ℓ ( V ):= I Y i =1 Q l ( V i ) Let ( m, n ) be an edge of the tann er graph. Assume that H ( m ) = { n, n 1 , . . . , n d − 1 } , wh ere d is th e degree of the check no de m . T o simplify the notation, w e set h i = h m,n i , the non zer o label o f the ed ge ( m, n i ) , for i = 1 , . . . , d − 1 . 1 Here we identify F 8 = { 0 , 1 , 2 , . . . , 7 } , and the constituent bits of a giv en symbol correspond to the binary decomposition. The p robability o f B ( ℓ +1) m,n being equal to V , condition ed o n h = ( h 1 , . . . , h d − 1 ) , may be computed as: Pr( B ( ℓ +1) m,n = V | h ) = X V ∈S ( d − 1) V d − 1 Y i =1 P ℓ ( h − 1 i V i ) ! (10) A veraging over all possible lab el sequ ences h we ge t: Q ( d − 1) ℓ +1 ( V ) := P r( B ( ℓ +1) m,n = V ) = X h ∈ L d − 1 f ( h ) · X V ∈S ( d − 1) V P ℓ ( h − 1 · V ) (11) A veraging over all po ssible ch eck node degrees d , we obtain: Q ℓ +1 ( V ) = d c X d =1 ρ d · Q ( d − 1) ℓ +1 ( V ) (12) Now , con sider a n edge ( n, m ) of the T anner graph, and let the variable node n be o f degree d and H ( n ) = { m, m 1 , . . . , m d − 1 } . T o simplify n otation, we set h i = h m i ,n , the no n zero label o f the ed ge ( n, m i ) , for i = 1 , . . . , d − 1 . The p robability of A ( ℓ +1) m,n being equ al to V , con ditioned on h = ( h 1 , . . . , h d − 1 ) , may be computed as: Pr( A ( ℓ +1) m,n = V | h ) = X ( V 0 , V ) ∈I ( d − 1) V γ ( V 0 ) d − 1 Y i =1 Q ℓ +1 ( h i V i ) ! (13) Again, by averaging over all possible label sequence s h , it follows that: P ( d − 1) ℓ +1 ( V ) := Pr( A ( ℓ +1) m,n = V ) = X h ∈ L d − 1 f ( h ) · X ( V 0 , V ) ∈I ( d − 1) V γ ( V 0 ) Q ℓ +1 ( h · V ) (14) Finally , a veragin g over all possible variable n ode degre es d , we o btain: P ℓ +1 ( V ) = d v X d =1 λ d · P ( d − 1) ℓ +1 ( V ) (15) Pr o position 1: Let V , W ∈ Gr ( F q ) and h ∈ L such th at W = hV . Then: Q ( d − 1) ℓ +1 ( W ) = X h ∈ L d − 1 f ( h · h ) · X V ∈S ( d − 1) V P ℓ ( h − 1 · V ) (16) P ( d − 1) ℓ +1 ( W ) = X h ∈ L d − 1 f ( h · h ) · X ( V 0 , V ) ∈I ( d − 1) V γ ( V 0 ) Q ℓ +1 ( h · V ) (17) where h · ( h 1 , . . . , h d − 1 ) = ( hh 1 , . . . , hh d − 1 ) . In particular, if f is the unifor m distribution, then Q ( d − 1) ℓ +1 ( W ) = Q ( d − 1) ℓ +1 ( V ) and P ( d − 1) ℓ +1 ( W ) = P ( d − 1) ℓ +1 ( V ) . W e say th at V and W are c onjugate if th ere exists h ∈ L such that W = hV an d d enote by Gr ( F q ) / L the quotien t set of con jugation classes. Cor o llary 2: Assume th at f is the unifo rm d istribution and let V ∈ Gr ( F q ) . Th en Q ℓ ( V ) and P ℓ ( V ) depend only on the conjuga tion class of V in Gr ( F q ) / L . Cor o llary 3: Assume th at f is the unifo rm d istribution and that L = M ∗ p ( F 2 ) , the multiplicati ve g roup o f in vertible p × p matrices, acting o n F q via the isom orphism F p 2 ∼ → F q from (1). Le t V ∈ Gr ( F q ) . Then Q ℓ ( V ) an d P ℓ ( V ) d epend only on the dimen sion of the vector space V . The above coro llaries may be used to simplify the d ensity ev olution f ormulas, assum ing a unifo rm d istribution of the graph edg e labe ls. For instance, if L = M ∗ p ( F 2 ) , on e can derive th e same formulas as in [1 2]. V . T H R E S H O L D S W e den ote by E F q , L ( λ, ρ, f ) the ensemble of LDPC c odes over F q , with labels gro up L , d istribution degree polyno- mials λ and ρ , and prob ability d istribution of edge labels f . Whenever the Galo is gro up F q and the lab els g roup L are su bunderstood, we will simp ly use E ( λ, ρ, f ) . W e also denote by p th F q , L ( λ, ρ, f ) (or simp ly p th ( λ, ρ, f ) ) th e thr eshold probab ility of the a bove ensemble, that is (see also (9)): p th ( λ, ρ, f ) = max { ǫ | lim ℓ → + ∞ P ℓ ( { 0 } ) = 1 on BEC ( ǫ ) } (1 8) By fixing the poly nomials of d egree distribution λ and ρ , the prob ability thr eshold p th may be seen as a fu nction o f the probab ility distrib ution f . This is illustrated in Fig. 1 an d Fig. 2. The Galo is field is F 4 and the labels g roup L = F ∗ 4 , acting of F 4 by the in ternal field multiplica tion. The horizo ntal axes f (1) an d f (2) r epresent the prob abilities of edg e lab els being 1 and 2 , respecti vely . Thus, the probability of e dge labels being 3 is given by f (3) = 1 − f (1 ) − f (2) . W e d rawn the surface repre senting p th as fu nction o f f (1) and f (2) . The top of the sur face is plo tted in red , the mid dle in g reen, and the b ottom in b lue. T he two figu res co rrespond to two couples ( λ, ρ ) o f degree distributions that were also co nsidered in [12]. In Fig. 1 we fix λ = X and ρ = X 2 . The maximu m p th is obtained for the uniform distribution f (1) = f (2) = f (3) = 1 / 3 and its value is equal to 0 . 57 72 . The minimum p th = 0 . 5 is obtained for the three distributions concentrated in a single label (such codes are equ iv alent to binary co des). In Fig. 2 we fix λ ( X ) = X 2 and ρ ( X ) = X 3 . F or the unif orm distribution f (1) = f (2 ) = f (3) = 1 / 3 , the threshold p th = 0 . 6348 . The minimu m p th = 0 . 6 346 . The maxim um p th = 0 . 647 4 is obtained for the three distributions concentrated in one single label. These two examples h ighlight a more gener al p henom enon that we o bserved for other ensemble s of codes, as sh own for instance in Fig. 3 . For a given Galois field F q , and given polyno mials λ , and ρ , it is possible to find a prob ability distribution ˜ f of edge labels, such that: • edge lab els are equal to 1 with high pr obability ( meaning that ˜ f (1) is close to 1 ) • p th F q , F ∗ q ( λ, ρ, ˜ f ) ≈ max f p th F q , F ∗ q ( λ, ρ, f ) 0 0.2 0.4 0.6 0.8 1 0.5 0.55 0.6 p th 0.2 0.4 0.6 0.8 1 f(2) + f(1) p th Fig. 1. Probabil ity threshold of the ensemble E F 4 , F ∗ 4 ( λ = X, ρ = X 2 , f ) as functio n of labels probabil ity distri bution f . E F 8 , F ∗ 8 ( λ, ρ, f ) Labels pdf f Threshold 1 2 3 4 5 6 7 1/7 1/7 1/7 1/7 1/7 1/7 1/7 0.4353 1/5 1/5 1/5 0 0 1/5 1/5 0.4356 1/3 0 0 1/3 0 0 1/3 0.4373 1/3 1/3 1/3 0 0 0 0 0.4391 1/2 0 0 0 0 0 1/2 0.4437 0.8 0 0 0 0 0 0.2 0.4483 0.9 0 0 0 0 0 0.1 0.436 0.95 0 0 0 0 0 0.05 0.4179 1 0 0 0 0 0 0 0.4 E F 4 , F ∗ 4 ( λ, ρ, f ) Labels pdf f Threshold 1 2 3 1/3 1/3 1/3 0.4487 1/2 1/2 0 0.4489 0.8 0.1 0.1 0.4507 0.9 0.07 0.03 0.4335 0.97 0.03 0 0.4121 1 0 0 0.4 Fig. 3. Probabil ity thresholds of the ensembles E F 8 , F ∗ 8 ( λ, ρ, f ) and E F 4 , F ∗ 4 ( λ, ρ, f ) for λ = 0 . 5 X + 0 . 5 X 4 , ρ = X 5 , and diffe rent labe ls probabil ity distri butions f . For instance, conside ring th e ensemble of codes over F 8 from Fig. 3, if ˜ f is d efined b y ˜ f (1) = 0 . 8 , ˜ f (7) = 0 . 2 , and ˜ f ( i ) = 0 for 1 < i < 7 , th en p th F 8 , F ∗ 8 ( λ, ρ, ˜ f ) = 0 . 44 83 . I n this case o nly few Galois field m ultiplications a re needed , an d the d ecoder complexity is considerably redu ced. V I . C O N C L U S I O N S In th is pap er we investi gated the deco ding of n on binar y LDPC cod es over the BEC, and we introdu ced a minimu m- delay deco ding suited for UL-FEC. W e also derived the density evolution eq uations taking into conside ration both the irregula rity of the bipa rtite graph of the code and the probab ility distribution of the g raph edge labels, giving a thorou gh understand ing of the asymptotical behavior of en- sembles of n on binary LDPC codes. A non-uniform pr obability distribution of the edge labels migh t improve the decode r 0 0.2 0.4 0.6 0.8 1 0.625 0.65 p th 0.2 0.4 0.6 0.8 1 f(2) + f(1) p th Fig. 2. Probabil ity threshold of the ensemble E F 4 , F ∗ 4 ( λ = X 2 , ρ = X 3 , f ) as function of labels probabil ity dist ributio n f . perfor mance, but the mo st im portant advantage is that the decoder com plexity can b e significantly redu ced. The de sign of cap acity appro aching n on b inary LDPC codes will be addressed in future works. R E F E R E N C E S [1] R. G. Gall ager , Low Densit y P arity Che ck Codes , Ph.D. thesi s, MIT , Cambridge , Mass., September 1960. [2] R. G. Gallager , Low Density P arity Check Codes , M.I.T . Press, 1963, Monograph. [3] V . Zyablov and M. Pinsk er , “De coding comple xity of lo w-density code s for transmission in a channel with erasures, ” T ransla ted fr om Probl emy P eredac hi Informatsii , vol. 10(1), 1974. [4] T .J. Richardson, M.A. Shokrollahi, and R. L. Urbanke , “Design of capac ity-approac hing irregular lo w-density parity-ch eck codes, ” Infor- mation T heory , IEEE T ransact ions on , vol. 47, pp. 619–637, 2001. [5] M. G. Luby , M. Mitz enmacher , M. A. Shokrol lahi, and D. A. Spie lman, “Ef ficient erasure correcting code s, ” IEEE T rans. Inf . Theory , vol. 47, no. 2, pp. 569–584, 2001. [6] M. Luby , “L T codes, ” P r oc. ACM Symp. F ound. Comp. Sci. , 2002. [7] A. Shokrollahi, “Raptor codes, ” IE EE/ACM T rans. Networking (TON) , vol. 14, pp. 2551–2567, 2006. [8] R. M. T anner , “ A re cursiv e appro ach to low complexity co des, ” IEEE T rans. Inform. Theory , vol. 27, no. 5, pp. 533–547, 1981. [9] E . Paol ini, M. Fossorier , and M. Chiani, “Anal ysis of Generalize d LDPC Codes with Random Component Codes for the Binary Erasure Channel , ” Int. Symp. on Information Theory and its Applications (ISIT A) , 2006. [10] E. Paolin i, M. Fossorier , and M. Chiani, “General ized Stabil ity Con di- tion for Gener alized and Doubly -Generaliz ed LDPC Codes, ” Interna- tional Symposium on Information Theory (ISIT) , 2007. [11] N. Miladin ovic and M. Fossorie r, “Gene ralized L DPC codes and general ized stopping sets, ” IEEE T rans. on Comm. , vol. 56(2), pp. 201– 212, 2008. [12] V . Rathi and R. Urbank e, “Density Evoluti on, Thresholds and the Stabili ty Condition for Non-bina ry LDPC Codes, ” IEE Proc.-Commun. , vol. 152, no. 6, 2005. [13] V . Ra thi, “Conditi onal Entropy of Non-Binary LDPC Code s over the BEC, ” International Symposium on Information Theory (ISIT) , 2008. [14] N. W iberg, Codes and decoding on ge neral graphs , Ph.D. thesis, Likopi ng U ni versit y , 1996, Sweden. [15] D. Declerc q and M. Fossorier , “Extended min-sum algorithm for decodin g LDPC code s over GF ( q ) , ” in Information Theory , 2005. ISIT 2005. Pr oceedings. International Symposium on , 2005, pp. 464–468. [16] V . Savin, “Min-Max decoding for non binary LDPC codes, ” in Informatio n Theory , 2008 IEEE International Symposium on , 2008.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment