Unified Quantum Convolutional Coding
We outline a quantum convolutional coding technique for protecting a stream of classical bits and qubits. Our goal is to provide a framework for designing codes that approach the ``grandfather'' capacity of an entanglement-assisted quantum channel fo…
Authors: Mark M. Wilde, Todd A. Brun
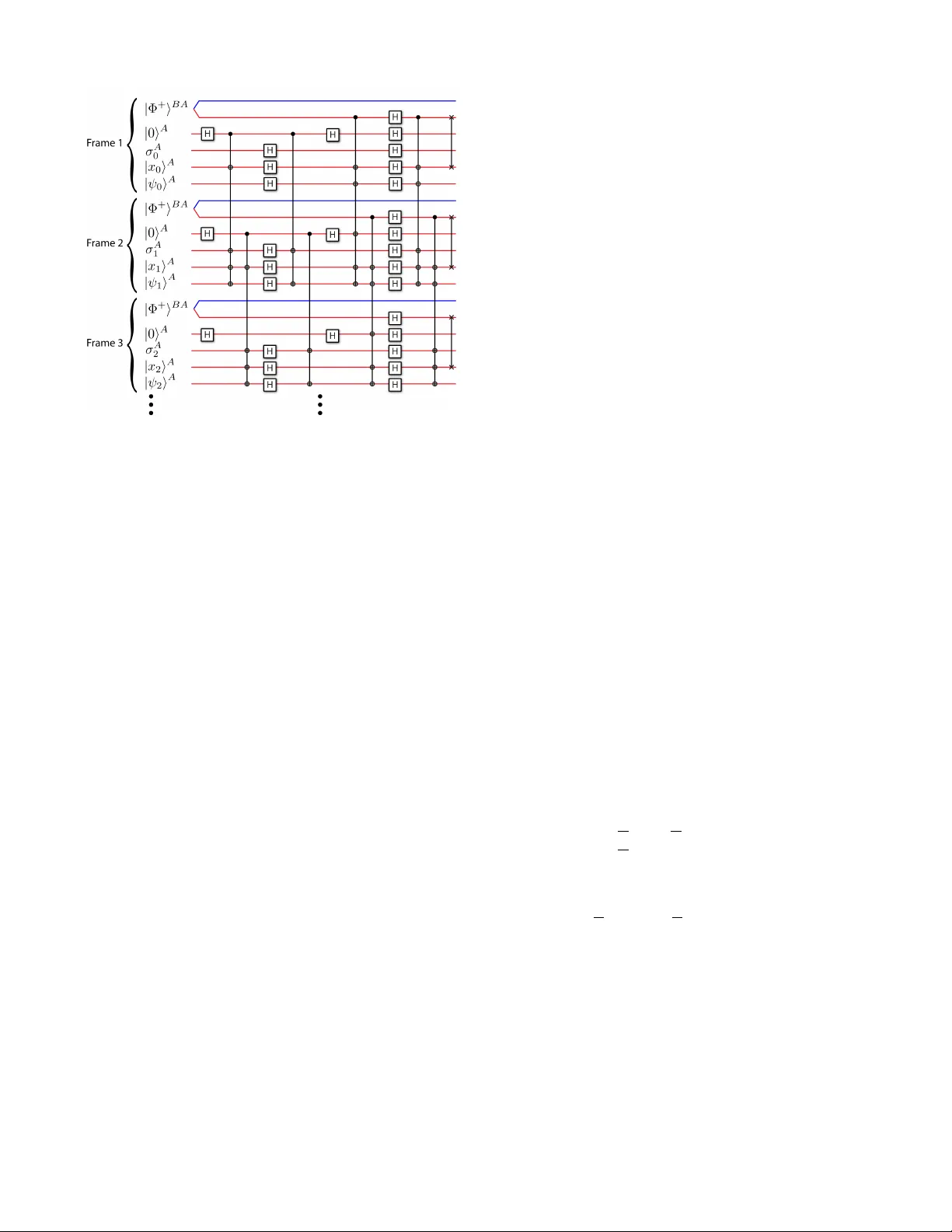
1 Unified Quantum Con v olutional Coding Mark M. W ilde and T odd A. Brun Abstract —W e outline a quantum convolutional coding tech- nique for pr otecting a stream of classical bits and qubits. Our goal is to provide a framework for designing codes that approach the “grandfather” capacity of an entanglement-assisted quantum channel for sending classical and quantum information simultaneously . Our method incorporates several resources for quantum redundancy: fresh ancilla qubits, entangled bits, and gauge qubits. The use of these diverse r esources gives our technique the benefits of both active and passive quantum err or correction. W e can encode a classical-quantum bit stream with periodic quantum gates because our codes possess a con volutional structure. W e end with an example of a “grandfather” quantum con volutional code that pr otects one qubit and one classical bit per frame by encoding them with one fresh ancilla qubit, one entangled bit, and one gauge qubit per frame. W e explicitly pro vide the encoding and decoding circuits for this example and discuss its error -correcting capability . Index T erms —grandfather quantum conv olutional codes, entanglement-assisted quantum con volutional codes I . I N T RO D U C T I O N The goal of quantum Shannon theory is to quantify the amount of quantum communication, classical communication, and entanglement required for v arious information processing tasks [1], [2], [3], [4]. Quantum teleportation and superdense coding [5] provided the initial impetus for quantum Shannon theory because these protocols demonstrate that we can com- bine entanglement, noiseless quantum communication, and noiseless classical communication to transmit quantum or classical information. In practice, the above resources are not noiseless because quantum systems decohere by interacting with their surrounding en vironment. Quantum Shannon theory is a collection of capacity theorems that determine the ultimate limits for noisy quantum communication channels. Essentially all quantum protocols have been unified as special cases of a handful of abstract protocols [4]. The techniques in quantum Shannon theory determine the asymptotic limits for communication, but these techniques do not produce practical ways of realizing these limits. This same practical problem exists with classical Shannon theory because the proofs that the channel capacities for classical communication are achie vable use random coding techniques that are too inef ficient in practice [6]. An example of an important capacity theorem from quan- tum Shannon theory results fr om the “father” protocol [4]. The f ather capacity theorem determines the optimal trade-off between the rate E of ebits (entangled qubits in the state | Φ + i AB ≡ ( | 00 i AB + | 11 i AB ) / √ 2 ) and the rate Q of qubits in Mark M. Wilde and T odd A. Brun are with the Center for Quantum Information Science and T echnology and the Communication Sciences In- stitute of the Ming Hsieh Department of Electrical Engineering at the Univ ersity of Southern California, Los Angeles, California 90089 USA (E- mail: mark.wilde@usc.edu; tbrun@usc.edu). entanglement-assisted quantum communication. 1 These rates for quantum communication and entanglement consumption (or generation if E is negati ve) fall within a two-dimensional capacity region. Suppose that a noisy quantum channel N connects a sender to a recei ver . Let [ q → q ] denote one qubit of noiseless quantum communication and let [ q q ] denote one ebit of entanglement. The following resource inequality is a statement of the capability of the father protocol: hN i + E [ q q ] ≥ Q [ q → q ] . (1) The above resource inequality states that n uses of the noisy quantum channel N and nE noiseless ebits are suf ficient to communicate nQ noiseless qubits in the limit of lar ge n . The rates E and Q are related to the noisy channel N and there is a mutual dependence between them so that they form a capacity region. The father capacity theorem gives the optimal limits on the resources, b ut it does not pro vide a useful quantum coding technique for approaching the above limits. Another important capacity theorem determines the ability of a noisy quantum channel to send “classical-quantum” states [7]. Let [ c → c ] denote one classical bit of noiseless classical communication. The result of the classical-quantum capacity theorem is also a resource inequality: hN i ≥ Q [ q → q ] + R [ c → c ] . (2) The resource inequality states that n uses of the noisy quantum channel N are suf ficient to communicate nQ noiseless qubits and nR noiseless classical bits in the limit of large n . The capacity theorem associated to the abov e resource inequality , in some cases, pro ves that we can de vise cle ver classical- quantum codes that perform better than time-sharing a noisy quantum channel N between purely quantum codes and purely classical codes. The “grandfather” capacity theorem determines the optimal triple trade-of f between qubits, ebits, and classical bits for si- multaneous transmission of classical and quantum information using an entanglement-assisted noisy quantum channel N [8]. The grandfather resource inequality is as follows: hN i + E [ q q ] ≥ Q [ q → q ] + R [ c → c ] . (3) The abov e resource inequality is again an asymptotic state- ment and its meaning is similar to that in (1) and (2). The optimal rates in the above resource inequality coincide with the father inequality (1) when R = 0 , with the classical- quantum inequality (2) when E = 0 , and with the quantum capacity [1], [2], [3] when both R = 0 and E = 0 . The 1 This protocol is the “father” protocol because it generates many of the protocols in the family tree of quantum information theory [4]. The nickname “father” is a useful shorthand for classifying the protocol—there exists a mother , grandmother , and grandfather protocol as well [8]. 2 optimal strate gy for the grandfather protocol is not time- sharing the channel between father codes and entanglement- assisted classical codes. It remains to be pro ven whether this optimal strategy outperforms time-sharing [8]. The goal of quantum error correction [5] is to find efficient and practical ways of coding quantum information to protect it against decoherence. One aspiration for this theory is to find quantum codes that approach the rates given by quantum Shannon theory in the limit of large block size. The entanglement-assisted stabilizer formalism is a method for building a quantum block code using entanglement [9]. This theory has several benefits, such as the ability to produce a quantum code from an arbitrary classical linear block code, and has several generalizations [10], [11], [12]. Entanglement- assisted codes are “father” codes, in the sense that a good entanglement-assisted coding strategy should approach the optimal rates in (1). In this Proceeding, we design a frame work for “grandfather” quantum codes. Our grandfather codes are useful for the si- multaneous transmission of classical and quantum information. Rather than using block codes for this purpose, we design quantum conv olutional codes. 2 Quantum conv olutional coding is a recent e xtension of the stabilizer formalism [14], [15], [16]. One of the benefits of a con volutional code is that it encodes a stream of information with an online periodic encoding circuit. Our technique incorporates many of the known techniques for quantum coding: subsystem codes [17], [18], entanglement-assisted codes [9], con volutional codes [14], [15], [16], and classical-quantum coding [7], [19], [13]. The goal of our technique is to provide a formalism for designing codes that approach the optimal triple trade-off rates in the grandf ather resource inequality in (3). W e are not claiming that codes in our frame work will reach capacity , but we are instead providing a frame work that one might later incorporate in a larger theory , such as a quantum turbo coding theory [21]. W e structure this proceeding as follows. Section II details our “grandfather” quantum con volutional codes. W e detail the finite-depth operations that quantum conv olutional circuits employ when encoding and decoding a stream of quantum information. W e explicitly show how to encode a stream of classical-quantum information using finite-depth operations and discuss the error-correcting properties of our codes. W e end with an example of a grandfather quantum conv olutional code. W e discuss errors that the code corrects acti vely and others that it corrects passi vely . I I . G R A N D FA T H E R Q UA N T U M C O N VO L U T I O N A L C O D E S W e no w detail the stabilizer formalism for our grandfather quantum con volutional codes and describe how these codes operate. These codes are a significant extension of the existing entanglement-assisted quantum conv olutional codes [12]. An [ n, k , l ; r , c ] grandfather quantum con volutional code encodes k information qubits and l information classical bits 2 Kremsky , Hsieh, and Brun address the formulation of grandfather block codes in a recent article [13]. with the help of c ebits, a = n − k − l − c − r ancilla qubits, and r gauge qubits. Each input frame includes the follo wing: 1) The sender Alice’ s half of c ebits in the state | Φ + i . 2) a = n − k − c − l − r ancilla qubits in the state | 0 i . 3) r gauge qubits (which can be in any arbitrary state σ ). 4) l classical information bits x 1 · · · x l , gi ven by a compu- tational basis state | x i = X x 1 ⊗ · · · ⊗ X x l | 0 i ⊗ l . 5) k information qubits in an arbitrary pure state | ψ i . 3 The left side of Figure 1 sho ws an example initial qubit stream before an encoding circuit operates on it. The stabilizer matrix S 0 ( D ) for the initial qubit stream is as follows: S 0 ( D ) = I I 0 0 0 0 0 0 0 0 0 0 0 0 I 0 0 0 0 0 0 0 0 0 I I 0 0 0 0 0 0 0 0 0 0 , (4) where all identity matrices in the first two sets of ro ws are c × c , the identity matrix in the last row is a × a , the three columns of all zeros in both the “Z” and “X” matrices are respectiv ely ( a + 2 c ) × r , ( a + 2 c ) × l , and ( a + 2 c ) × k . The matrices on the left of the v ertical bar form the “Z” matrix and those on the right form the “X” matrix according to the Pauli-to-binary-polynomial isomorphism (see Ref. ’ s [10], [12] for a revie w of this isomorphism from the set of Pauli sequences to vectors of binary polynomials). The first two sets of ro ws stabilize a set of c ebits and the last set of ro ws stabilizes a set of a ancilla qubits. The first c columns of both the “Z” and “X” matrix correspond to halv es of ebits that the recei ver Bob possesses and the last n columns in both matrices correspond to the qubits that Alice possesses. The global generators (including both Alice and Bob’ s qubits) form a commuting set of generators for all shifts, b ut Alice’ s local generators do not necessarily form a commuting set. Different sets of generators for the grandfather code are important in activ e error correction, in passive error correction, and for the identification of the l classical information bits. W e first write the unencoded generators that act on the initial qubit stream. The first subgroup of generators is the entanglement subgroup S E , 0 with the following generators: S E , 0 ( D ) = I 0 0 0 0 0 0 0 0 0 0 0 0 0 0 I 0 0 0 0 . (5) The abov e generators are equiv alent to the first two sets of rows in (4) acting on Alice’ s n qubits. The next subgroup is the isotropic subgroup S I , 0 with the following generators: S I , 0 ( D ) = 0 I 0 0 0 0 0 0 0 0 . (6) The abov e generators are equiv alent to the last set of rows in (4) acting on Alice’ s n qubits. The encoded versions of both of the above two matrices are important for the acti ve correction of errors. The next subgroup is the gauge subgroup S G, 0 whose generators are as follo ws: S G, 0 ( D ) = 0 0 I 0 0 0 0 0 0 0 0 0 0 0 0 0 0 I 0 0 . (7) 3 This statement is not entirely true because the information qubits can be entangled across multiple frames, or with an external system, b ut we use it to illustrate the idea. 3 The generators in S G, 0 correspond to quantum operations that have no effect on the encoded quantum information and therefore represent a set of errors to which the code is immune. The last subgroup is the classical subgroup S C, 0 with generators S C, 0 ( D ) = 0 0 0 I 0 0 0 0 0 0 . (8) The grandfather code passiv ely corrects errors corresponding to the encoded version of the above generators because the initial qubit stream is immune to the action of operators in S C, 0 (up to a global phase). Alice could measure the generators in S C, 0 to determine the classical information in each frame. Unlike quantum information, it is possible to measure classical information without disturbing it. Alice performs a periodic encoding circuit on her qubits to encode the initial set of ebits, ancilla qubits, and information qubits in each frame. She performs encoding operations only on her qubits because the channel spatially separates her qubits from Bob’ s qubits. The periodic encoding circuit encodes the information qubits and transforms the initial set of generators in (5-8) to a more general set of encoded generators. W e use three types of operations in the example code in Section III: 1) Let H ( i ) denote a Hadamard gate acting on qubit i of ev ery frame. The effect of H ( i ) is to swap column i in the “Z” matrix with column i in the “X” matrix. 2) Let C i, j, D k denote a CNOT gate from qubit i in ev ery frame to qubit j in a frame delayed by k where i 6 = j . This gate af fects both the “X” and “Z” matrices. In the “X” matrix, it multiplies column i by D k and adds the result to column j . In the “Z” matrix, it multiplies column j by D − k and adds the result to column i . Let f ( D ) be an arbitrary finite binary polynomial. Let C ( i, j, f ( D )) denote the sequence of CNO T gates corresponding to the polynomial f ( D ) . 3) Let S ( i, j ) sw ap qubits i and j in every frame and column i and column j in both “X” and “Z. ” Quantum con volutional circuits can employ other operations besides the above three [15], b ut we need only these three operations for the purposes of the current paper . The abov e operations and the others in the above references are finite- depth , because they transform any Pauli sequence with a finite number of non-identity entries to a Pauli sequence with a finite number of non-identity entries [12]. Finite-depth operations are desirable because they do not propagate uncorrected errors into the qubit stream when encoding or decoding. The three gates used in this paper are all their o wn in verses. Therefore, the operations of the decoding circuit are the encoding operations performed in reverse order . The online nature of the decoding circuit follows directly from the online nature of the encoding circuit. Alice performs an encoding circuit with finite-depth opera- tions to encode her stream of qubits before sending them o ver the noisy quantum channel. The encoding circuit transforms the initial stabilizer S 0 ( D ) to the encoded stabilizer S ( D ) as follows: S ( D ) = I Z E 1 ( D ) 0 Z E 2 ( D ) 0 Z I ( D ) 0 X E 1 ( D ) I X E 2 ( D ) 0 X I ( D ) , (9) where Z E 1 ( D ) , X E 1 ( D ) , Z E 2 ( D ) and X E 2 ( D ) are each c × n -dimensional, and Z I ( D ) and X I ( D ) are both a × n - dimensional. The encoding circuit affects only the rightmost n entries in both the “Z” and “X” matrix of S 0 ( D ) because these are the qubits in Alice’ s possession. It transforms S E , 0 ( D ) , S I , 0 ( D ) , S G, 0 ( D ) , and S C, 0 ( D ) as follows: S E ( D ) = Z E 1 ( D ) Z E 2 ( D ) X E 1 ( D ) X E 2 ( D ) , (10) S I ( D ) = Z I ( D ) X I ( D ) , (11) S G ( D ) = Z G 1 ( D ) Z G 2 ( D ) X G 1 ( D ) X G 2 ( D ) , (12) S C ( D ) = Z C ( D ) X C ( D ) , (13) where Z G 1 ( D ) , X G 1 ( D ) , Z G 2 ( D ) and X G 2 ( D ) are each r × n -dimensional and Z C ( D ) and X C ( D ) are each l × n - dimensional. The above polynomial matrices ha ve the same commutation relations as their corresponding unencoded poly- nomial matrices in (5-8) and respecti vely generate the entan- glement subgroup S E , the isotropic subgroup S I , the gauge subgroup S G , and the classical subgroup S C . The condition for a set of generators to form a commuting stabilizer is equiv alent to orthogonality of each row in S ( D ) with respect to the shifted symplectic product [14], [10]. This is equiv alent to the condition Z D − 1 X T ( D ) + X D − 1 Z T ( D ) = 0 , (14) where + represents binary addition of polynomials and the abov e matrix on the right of the equality is an ( n − k ) × ( n − k ) null matrix. The original generators in (4) obey this condition, and the periodic encoding circuit preserves the con- dition because any encoding circuit preserves the commutation relations of the original generators. A grandfather quantum conv olutional code operates as fol- lows. Alice begins with an initial qubit stream as above. She performs the finite-depth encoding operations corresponding to a specific grandfather quantum conv olutional code. She sends the encoded qubits online over the noisy quantum communication channel. Bob combines the recei ved qubits with his half of the ebits in each frame. He obtains the error syndrome by measuring the generators in (9). He processes these syndrome bits with a classical error estimation algorithm to diagnose errors and applies recov ery operations to re verse the errors. He then performs the inv erse of the encoding circuit to recov er the initial qubit stream with the information qubits and the classical information bits. He recov ers the classical information bits either by measuring the generators in S C before decoding or the generators in S C, 0 after decoding. A grandfather quantum con volutional code corrects errors in a P auli error set E that obey one of the follo wing conditions ∀ E a , E b ∈ E : ∃ g ∈ hS I , S E i : g , E † a E b = 0 or E † a E b ∈ hS I , S G , S C i , where h·i denotes the larger group generated by a set of subgroups and { A, B } denotes the anticomutator for tw o op- erators A and B so that { A, B } ≡ AB + B A . It corrects errors that anticommute with generators in hS I , S E i by employing a classical error estimation algorithm, such as the V iterbi 4 Fig. 1. The encoding circuit for the grandfather quantum conv olutional code in our example. Each frame i has an ebit ˛ ˛ Φ + ¸ B A shared between Bob and Alice, a fresh ancilla qubit | 0 i A , a gauge qubit σ A i , an information classical bit | x i i A , and an information qubit | ψ i i A . Bob’ s qubits are blue and Alice’s qubits are red. Including the ebit and an ancilla qubit implies that the code incorporates acti ve quantum error correction. Including the gauge qubit implies that the code has passiv e quantum error correction. The code provides passi ve error correction of phase errors on the classical bit. Alice encodes her classical bits and qubits using the encoding circuit above. The decoding circuit consists of the above operations in reverse order . algorithm [20]. The code passiv ely protects against errors in the group hS I , S G , S C i . Our scheme for quantum con v olutional coding incorporates many of the known techniques for quantum error correction. It can tak e full adv antage of the benefits of these different techniques. I I I . E X A M P L E W e present an example of a grandfather quantum con volu- tional code in this section. The code protects one information qubit and one classical bit with the help of an ebit, an ancilla qubit, and a gauge qubit. The first frame of input qubits has the state ρ 0 = Φ + Φ + ⊗ | 0 i h 0 | ⊗ σ 0 ⊗ | x 0 i h x 0 | ⊗ | ψ 0 i h ψ 0 | , (15) where | Φ + i is the ebit, | 0 i is the ancilla qubit, σ 0 is an arbitrary state for the gauge qubit, | x 0 i is a classical bit represented by state | 0 i or | 1 i , and | ψ 0 i is one information qubit equal to α 0 | 0 i + β 0 | 1 i . The states of the other input frames ha ve a similar form though recall that information qubits can be entangled across multiple frames. The initial unencoded stabilizer for the code is as follows: S 0 ( D ) = 1 1 0 0 0 0 0 0 0 0 0 0 0 0 1 0 0 0 0 0 0 0 0 0 1 1 0 0 0 0 0 0 0 0 0 0 . The first two ro ws stabilize the ebit shared between Alice and Bob . Bob possesses the half of the ebit in column one and Alice possesses the half of the ebit in column two in both the left and right matrix. The third row stabilizes the ancilla qubit. The generators for the initial entanglement subgroup S E , 0 , isotropic subgroup S I , 0 , gauge subgroup S G, 0 , and classical subgroup S C, 0 are respectiv ely as follo ws: S E , 0 ( D ) = 1 0 0 0 0 0 0 0 0 0 0 0 0 0 0 1 0 0 0 0 , S I , 0 ( D ) = 0 1 0 0 0 0 0 0 0 0 , S G, 0 ( D ) = 0 0 1 0 0 0 0 0 0 0 0 0 0 0 0 0 0 1 0 0 , S C, 0 ( D ) = 0 0 0 1 0 0 0 0 0 0 . The sender performs the following finite-depth operations (order is from left to right and top to bottom): H (2) C (2 , 3 , D ) C (2 , 4 , 1 + D ) C (2 , 5 , D ) H (3 , 4 , 5) C (2 , 3 , D ) C (2 , 5 , D ) H (2) C (1 , 2 , D ) C (1 , 4 , 1 + D ) C (1 , 5 , 1 + D ) H (1 , 2 , 3 , 4 , 5) C (1 , 3 , D ) C (1 , 4 , 1 + D ) C (1 , 5 , 1 + D ) S (1 , 4) . Figure 1 details these operations on the initial qubit stream. The initial stabilizer matrix S 0 ( D ) transforms to S ( D ) = Z ( D ) X ( D ) under these encoding operations, where Z ( D ) = 1 0 0 0 0 0 0 h ( D ) D 0 1 h ( D ) 0 0 0 D D D , (16) X ( D ) = 0 h ( D ) 0 D 1 h ( D ) 1 0 0 0 0 0 0 0 1 0 1 1 , (17) and h ( D ) = 1 + D . The generators for the different subgroups transform respectiv ely as follo ws: S E ( D ) = 0 0 0 0 0 h ( D ) D 0 1 h ( D ) h ( D ) 0 D 1 h ( D ) 0 0 0 0 0 , S I ( D ) = 0 0 D D D 0 1 0 1 1 , S G ( D ) = 0 1 D 1 1 D 0 0 1 D 0 0 0 0 0 0 0 0 0 0 1 0 0 , S C ( D ) = 1 h 1 D 0 h 1 D 0 0 0 0 0 0 . The code acti vely protects against an arbitrary single-qubit error in ev ery other frame. One can check that the syndromes of the stabilizer in S ( D ) satisfy this property . Consider the P auli generators corresponding to the generators in the entanglement subgroup and the isotropic subgroup: · · · X I I X X Z I I Z Z I X I X X X I X I X Z Z I I Z I I Z Z Z · · · , (18) where all other entries in the left and right directions are tensor products of the identity . W e can use a table-lookup syndrome-based algorithm to determine the error-correcting 5 Error Syndrome Error Syndrome Error Syndrome X 1 001100 X 3 000001 X 5 001101 Y 1 111100 Y 3 010001 Y 5 111111 Z 1 110000 Z 3 010000 Z 5 110010 X 2 000100 X 4 001001 Y 2 000110 Y 4 101011 Z 2 000010 Z 4 100010 T ABLE I A L I S T O F P O S SI B L E S I NG L E - QU B I T E R RO RS I N A PA RT IC U L AR F RA M E A N D T HE C O RR E S PO N D I NG S YN D RO M E V E C TO R . T H E S Y ND RO M E C O RE S P O ND I N G T O A N Y S IN G L E - Q U B IT E RR O R I S U N IQ U E . T H E C O D E T H ER E F O RE C OR R E CT S A N A RB I T R ARY S IN G L E - Q U B IT E RR OR I N E V ERY OT H E R F R AM E . capability of the code. The method is similar to the technique originally outlined in detail in Ref. [16]. The syndrome vector s consists of six bits where s = s 1 · · · s 6 . The first bit s 1 is one if the error anticommutes with the operator X I I X X in the first part of the first generator above and zero otherwise. The second bit s 2 is one if the error anticommutes with the operator X I X I X in the delayed part of the first generator abo ve and zero otherwise. The third through sixth bits follow a similar pattern for the second and third generators abo ve. T able I lists all single-qubit errors o ver fiv e qubits and their corresponding syndromes. The code corrects an arbitrary single-qubit error in ev ery other frame using this algorithm because the syndromes are all unique. A syndrome-based V iterbi algorithm might achiev e better performance than the simple syndrome table- lookup algorithm outlined abo ve. This code also has passi ve protection against errors in hS I , S G , S C i . The Pauli form of the errors in this group span ov er three frames and are as follo ws: · · · I I I I I I Z I Z I I Z I I I I Z I Z I I X I X X I I Z I I I I X I I Z Z I Z I I I Z Z Z I I I I I I I I I I I I I I I · · · (19) The smallest weight errors in this group ha ve weight two and three. The code passi vely corrects the abov e errors or any product of them or any fi ve-qubit shift of them. There is a trade-off between passiv e error correction and the ability to encode quantum information as discussed in Ref. [11]. One can encode more quantum information by dropping the gauge group and instead encoding an extra qubit. The gauge generators then become logical X and Z operators for the extra encoded qubits. One can also turn the classical bit into a qubit by dropping the generators in the classical subgroup. These generators then become logical Z operators for the extra encoded qubits. I V . C O N C L U S I O N W e ha ve presented a framework and a representative ex- ample for grandfather quantum con v olutional codes. W e ha ve explicitly shown how these codes operate, and how to encode and decode a classical-quantum information stream by using ebits, ancilla qubits, and gauge qubits for redundanc y . The ultimate goal for this theory is to find quantum con volutional codes that might play an integral part in larger quantum codes that approach the grandfather capacity [8]. One useful line of in vestigation may be to combine this theory with the recent quantum turbo-coding theory [21]. The authors thank Isaac Kremsky , Min-Hsiu Hsieh, and Igor Dev etak for useful discussions. MMW and T AB ackno wledge support from NSF Grants CCF-0545845 and CCF-0448658. R E F E R E N C E S [1] S. Lloyd, “Capacity of the noisy quantum channel, ” Phys. Rev . A , v ol. 55, no. 3, pp. 1613–1622, Mar 1997. [2] P . W . Shor , “The quantum channel capacity and coherent information, ” in Lecture Notes, MSRI W orkshop on Quantum Computation , 2002. [3] I. De vetak, “The private classical capacity and quantum capacity of a quantum channel, ” IEEE T rans. Inf. Theory , vol. 51, pp. 44–55, 2005. [4] I. De vetak, A. W . Harrow , and A. W inter , “ A resource framew ork for quantum shannon theory , ” arXiv:quant-ph/0512015 , 2005. [5] M. A. Nielsen and I. L. Chuang, Quantum Computation and Quantum Information . Cambridge Univ ersity Press, 2000. [6] C. E. Shannon, “ A mathematical theory of communication, ” Bell System T echnical Journal , vol. 27, pp. 379–423, 1948. [7] I. De vetak and P . W . Shor, “The capacity of a quantum channel for simultaneous transmission of classical and quantum information, ” Communications in Mathematical Physics , vol. 256, pp. 287–303, 2005. [8] I. Devetak, P . Hayden, D. Leung, and P . Shor , “Triple trade-of fs in quantum shannon theory , ” In prepar ation , 2008. [9] T . A. Brun, I. Devetak, and M.-H. Hsieh, “Correcting quantum errors with entanglement, ” Science , vol. 314, no. 5798, pp. pp. 436 – 439, October 2006. [10] M. M. Wilde, H. Kro vi, and T . A. Brun, “Con volutional entanglement distillation, ” , 2007. [11] M.-H. Hsieh, I. Devetak, and T . Brun, “General entanglement-assisted quantum error-correcting codes, ” Phys. Rev . A , vol. 76, p. 062313, 2007. [12] M. M. Wilde and T . A. Brun, “Entanglement-assisted quantum con vo- lutional coding, ” , 2007. [13] I. Kremsky , M.-H. Hsieh, and T . A. Brun, , 2008. [14] H. Ollivier and J.-P . T illich, “Quantum con volutional codes: fundamen- tals, ” arXiv:quant-ph/0401134 , 2004. [15] M. Grassl and M. R ¨ otteler , “Noncatastrophic encoders and encoder in verses for quantum con volutional codes, ” in IEEE International Sym- posium on Information Theory (quant-ph/0602129) , 2006. [16] G. D. Forne y , M. Grassl, and S. Guha, “Con volutional and tail-biting quantum error-correcting codes, ” IEEE T r ans. Inf . Theory , vol. 53, pp. 865–880, 2007. [17] D. Kribs, R. Laflamme, and D. Poulin, “Unified and generalized ap- proach to quantum error correction, ” Physical Review Letters , vol. 94, no. 18, p. 180501, 2005. [18] D. Poulin, “Stabilizer formalism for operator quantum error correction, ” Physical Review Letters , vol. 95, no. 23, p. 230504, 2005. [19] C. B ´ eny , A. Ke mpf, and D. W . Kribs, “Generalization of quantum error correction via the heisenberg picture, ” Physical Review Letters , vol. 98, no. 10, p. 100502, 2007. [20] A. J. V iterbi, “Error bounds for convolutional codes and an asymptot- ically optimum decoding algorithm, ” IEEE Tr ans. Inf. Theory , vol. 13, pp. 260–269, 1967. [21] D. Poulin, J.-P . Tillich, and H. Ollivier , “Quantum serial turbo-codes, ” arXiv:0712.2888 , 2007.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment