ARQ-Based Secret Key Sharing
This paper develops a novel framework for sharing secret keys using existing Automatic Repeat reQuest (ARQ) protocols. Our approach exploits the multi-path nature of the wireless environment to hide the key from passive eavesdroppers. The proposed framework does not assume the availability of any prior channel state information (CSI) and exploits only the one bit ACK/NACK feedback from the legitimate receiver. Compared with earlier approaches, the main innovation lies in the distribution of key bits among multiple ARQ frames. Interestingly, this idea allows for achieving a positive secrecy rate even when the eavesdropper experiences more favorable channel conditions, on average, than the legitimate receiver. In the sequel, we characterize the information theoretic limits of the proposed schemes, develop low complexity explicit implementations, and conclude with numerical results that validate our theoretical claims.
💡 Research Summary
The paper introduces a novel physical‑layer key‑sharing scheme that leverages the existing Automatic Repeat reQuest (ARQ) protocol with only a single‑bit ACK/NACK feedback from the legitimate receiver. Unlike prior work that either assumes prior channel state information (CSI) or embeds the secret message in a single transmission, the authors distribute the secret key bits across many independent ARQ frames. This distribution, together with the one‑bit feedback, creates an “erasure‑wiretap” channel: frames that are NACKed are discarded by both the legitimate parties and the eavesdropper, effectively erasing the eavesdropper’s observations for those blocks.
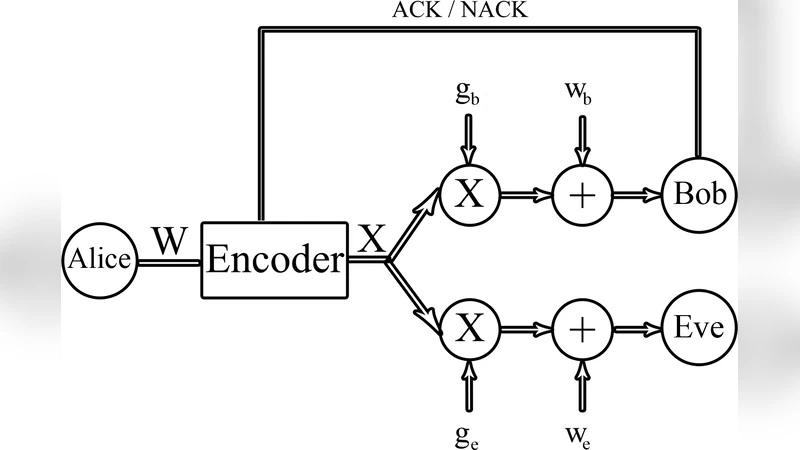
The system model consists of a transmitter (Alice), a legitimate receiver (Bob), and a passive eavesdropper (Eve), each equipped with a single antenna. The wireless links follow a block‑fading model; the channel gains for Bob ((h_b)) and Eve ((h_e)) are independent across blocks and unknown to Alice. Bob knows his own channel realization and can send a perfect ACK/NACK bit over a public, error‑free feedback channel; Eve cannot transmit. A long‑term average power constraint (\bar P) is imposed.
The core theoretical contribution is Theorem 1, which gives the perfect‑secrecy key rate for Gaussian inputs: \
Comments & Academic Discussion
Loading comments...
Leave a Comment