A Tiered Security System for Mobile Devices
We have designed a tiered security system for mobile devices where each security tier holds user-defined security triggers and actions. It has a friendly interface that allows users to easily define and configure the different circumstances and actions they need according to context. The system can be set up and activated from any browser or directly on the mobile device itself. When the security system is operated from a Web site or server, its configuration can be readily shared across multiple devices. When operated directly from the mobile device, no server is needed for activation. Many different types of security circumstances and actions can be set up and employed from its tiers. Security circumstances can range from temporary misplacement of a mobile device at home to malicious theft in a hostile region. Security actions can range from ringing a simple alarm to automatically erasing, overwriting, and re-erasing drives.
💡 Research Summary
The paper presents a novel “tiered” security architecture for mobile devices that lets end‑users define context‑specific triggers and corresponding protective actions, and organize them into hierarchical security levels (tiers). The authors argue that current mobile security tools suffer from poor usability and low adoption, partly due to the psychological bias described by Prospect Theory—people prefer certain modest losses over uncertain larger losses, which makes them reluctant to invest in strong security measures.
The proposed system addresses this by providing a friendly graphical user interface (GUI) where users can create, edit, and assign triggers (e.g., password entry, incoming call, received email or SMS, time‑of‑day, GPS location, detection of sensitive data) to actions (e.g., sounding an alarm, initiating GPS or base‑station triangulation, placing a remote call with a recorded message, enabling password‑only or digital‑signature access, disabling functions such as calling or browsing, partitioning data, encrypting files, securely deleting or overwriting data multiple times). Each tier represents a different severity level: low‑risk situations (misplaced at home) might only activate an audible ringer or GPS ping, while high‑risk scenarios (theft in a hostile region) could automatically encrypt the device and repeatedly overwrite the storage to make data recovery impossible.
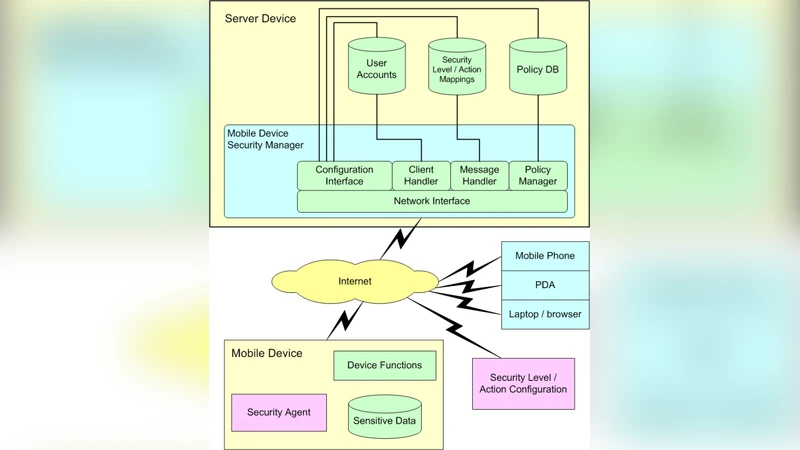
Two deployment modes are supported. In the “server‑based” mode, a central Security Manager runs on a network server, exposing a standard browser‑based configuration interface. Policies are stored in a security database and can be pushed to many devices across platforms, enabling corporate or agency‑wide policy consistency, group‑based access control, and audit trails. In the “device‑based” mode, the security engine resides entirely on the mobile device, allowing it to react autonomously when network connectivity is unavailable or the device is offline. This dual‑mode design ensures that protection is available both in connected environments and in isolated, high‑risk contexts.
The authors map the classic CIA triad (Confidentiality, Integrity, Availability) plus Authentication onto concrete toolsets. Confidentiality is enforced through passwords, digital signatures, data partitioning, encryption, and secure deletion/over‑writing. Integrity is protected by monitoring configuration files, logging device usage (calls, web visits, messages) and reporting to a remote manager, as well as by employing antivirus and firewall mechanisms. Availability is addressed through physical protection (cases, surge protectors), automated backup and recovery, and “threat‑prevention” tools such as alarms and tracking. Authentication is supported via multi‑factor methods (PINs, biometrics, watermarks) and is treated as a separate security dimension.
A detailed table (Table 1) illustrates how each security tool can be linked to a tier, showing the breadth of possible configurations. The system’s flexibility allows organizations to tailor policies to regulatory requirements, risk appetite, or specific operational contexts.
The paper also discusses limitations. Trigger detection may generate false positives, leading to unnecessary data erasure or device lockout. Cryptographic operations and repeated overwriting can degrade device performance and battery life, and key management remains a critical vulnerability if not handled securely. The server‑based approach depends on reliable network connectivity; outages could delay policy updates or remote wipe commands.
In conclusion, the tiered security system offers a pragmatic way to lower the barrier to strong mobile protection by translating abstract security goals into concrete, context‑driven actions that users can manage without deep technical expertise. Future work suggested includes integrating machine‑learning risk assessment to adjust tiers dynamically, expanding cross‑platform compatibility (Android, iOS, Windows), and automating secure key lifecycle management. The authors contend that such a system could significantly improve adoption of robust mobile security practices in both consumer and enterprise environments.
Comments & Academic Discussion
Loading comments...
Leave a Comment