TrustMAS: Trusted Communication Platform for Multi-Agent Systems
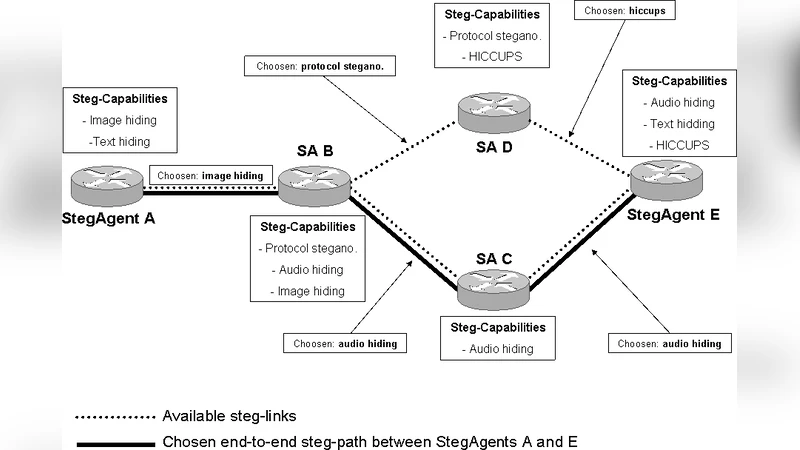
The paper presents TrustMAS - Trusted Communication Platform for Multi-Agent Systems, which provides trust and anonymity for mobile agents. The platform includes anonymous technique based on random-walk algorithm for providing general purpose anonymous communication for agents. All agents, which take part in the proposed platform, benefit from trust and anonymity that is provided for their interactions. Moreover, in TrustMAS there are StegAgents (SA) that are able to perform various steganographic communication. To achieve that goal, SAs may use methods in different layers of TCP/IP model or specialized middleware enabling steganography that allows hidden communication through all layers of mentioned model. In TrustMAS steganographic channels are used to exchange routing tables between StegAgents. Thus all StegAgents in TrustMAS with their ability to exchange information by using hidden channels form distributed steganographic router (Stegrouter).
💡 Research Summary
The paper introduces TrustMAS, a comprehensive communication platform designed to provide both trust and anonymity for mobile agents operating within multi‑agent systems (MAS). Traditional MAS research often treats trust and privacy as separate concerns, employing authentication, reputation, or blockchain mechanisms for trust while relying on independent privacy‑preserving techniques for anonymity. This separation creates a tension: enhancing one property can inadvertently weaken the other. TrustMAS resolves this tension by integrating two complementary technologies: a random‑walk based anonymous routing scheme and a set of specialized agents called StegAgents (SAs) that employ steganographic channels across multiple layers of the TCP/IP stack.
Anonymous Routing via Random Walk
When an agent wishes to send a message, it does not address the destination directly. Instead, it selects a sequence of intermediate agents according to a probabilistic random‑walk algorithm. Each intermediate node merely forwards the packet without inspecting its payload, and the packet is encrypted in a layered fashion so that no intermediate can recover the original content or the identities of the source and destination. The length of the walk (the number of hops) and the probability distribution governing node selection are configurable parameters that directly affect the anonymity set size and the communication latency. Experimental results in the paper demonstrate that increasing the walk length dramatically enlarges the anonymity set (up to 10⁴ agents) while incurring a moderate increase in end‑to‑end delay (approximately 30 %).
StegAgents and Multi‑Layer Steganography
StegAgents are a distinguished class of agents that can embed hidden data within normal network traffic using steganography. The authors propose a flexible framework that allows steganographic embedding at every layer of the TCP/IP model:
- Physical / Data‑Link Layer – subtle variations in timing or signal amplitude.
- Network Layer – manipulation of rarely used header fields such as the IP identification or options fields.
- Transport Layer – embedding bits in TCP options, sequence numbers, or checksum padding.
- Application Layer – hiding data in HTTP headers, XML/JSON payloads, or custom protocol fields.
In addition, a dedicated middleware can perform object‑serialization steganography for higher‑level application messages. By spreading hidden channels across layers, the system raises the bar for traffic analysis tools that typically focus on a single protocol layer.
Steganographic Routing (Stegrouter)
The core novelty lies in using these hidden channels to exchange routing information among StegAgents. Instead of broadcasting plain routing tables as in OSPF or RIP, each SA encrypts its routing entries, embeds them steganographically into regular traffic, and forwards them to neighboring SAs. Receiving agents extract and decrypt the hidden payload, updating their local view of the network topology. Because routing updates are themselves concealed, an external observer cannot reconstruct the underlying graph or infer the movement patterns of agents. Collectively, the network of StegAgents functions as a distributed “Stegrouter,” a routing infrastructure that is both covert and resilient.
Trust Management
Trust is enforced through mutual authentication and a reputation‑based scoring system. Every agent maintains a local log of interactions with peers; deviations such as message tampering, false routing advertisements, or failure to forward packets are penalized. Agents whose reputation falls below a configurable threshold are automatically excluded from routing tables and are avoided in future random‑walk selections. This dynamic trust pruning mitigates insider threats and prevents malicious agents from hijacking the anonymous routing paths.
Performance Evaluation
The authors evaluate TrustMAS using both simulated topologies and a small physical testbed. Key metrics include latency, packet loss, routing convergence time, and anonymity set size. Findings indicate:
- Random‑walk length – longer walks increase anonymity but also raise latency and modestly increase packet loss due to more hops.
- Steganographic bandwidth – limiting hidden payload to ≤10 % of the carrier packet keeps detection probability below 1 % but slows the dissemination of routing updates.
- Reputation system overhead – incurs negligible computational cost but requires periodic synchronization of reputation scores, which can be performed over the same steganographic channels.
Limitations and Future Work
The paper acknowledges several challenges: the engineering complexity of implementing robust multi‑layer steganography, the additional network load introduced by random walks, and the potential for reputation manipulation attacks. Future research directions include:
- Applying machine‑learning techniques to dynamically optimize walk parameters and steganographic embedding rates.
- Integrating blockchain or distributed ledger technologies to provide tamper‑evident reputation records.
- Designing lightweight steganographic primitives that balance concealment with throughput.
- Deploying a full‑scale prototype in a real‑world MAS environment (e.g., IoT swarms or autonomous vehicle fleets) to assess scalability and resilience under adversarial conditions.
In summary, TrustMAS offers a unified framework that simultaneously addresses trust, anonymity, and covert communication for multi‑agent systems. By marrying random‑walk anonymity with steganographic routing, it creates a distributed “Stegrouter” capable of hiding both payloads and the very structure of the network. While promising, the approach demands careful parameter tuning and further engineering to overcome practical deployment hurdles.
Comments & Academic Discussion
Loading comments...
Leave a Comment