Network Motifs in Object-Oriented Software Systems
Nowadays, software has become a complex piece of work that may be beyond our control. Understanding how software evolves over time plays an important role in controlling software development processes. Recently, a few researchers found the quantitative evidence of structural duplication in software systems or web applications, which is similar to the evolutionary trend found in biological systems. To investigate the principles or rules of software evolution, we introduce the relevant theories and methods of complex networks into structural evolution and change of software systems. According to the results of our experiment on network motifs, we find that the stability of a motif shows positive correlation with its abundance and a motif with high Z score tends to have stable structure. These findings imply that the evolution of software systems is based on functional cloning as well as structural duplication and tends to be structurally stable. So, the work presented in this paper will be useful for the analysis of structural changes of software systems in reverse engineering.
💡 Research Summary
The paper “Network Motifs in Object‑Oriented Software Systems” investigates whether concepts from complex‑network science can illuminate the structural evolution of large object‑oriented (OO) code bases. The authors begin by treating a software system as a directed graph whose vertices are classes and whose edges encode static relationships such as inheritance, interface implementation, method calls, and field accesses. By normalising multi‑inheritance and interface edges into single‑direction links, they obtain a uniform class‑dependency network that can be analysed with standard graph‑theoretic tools.
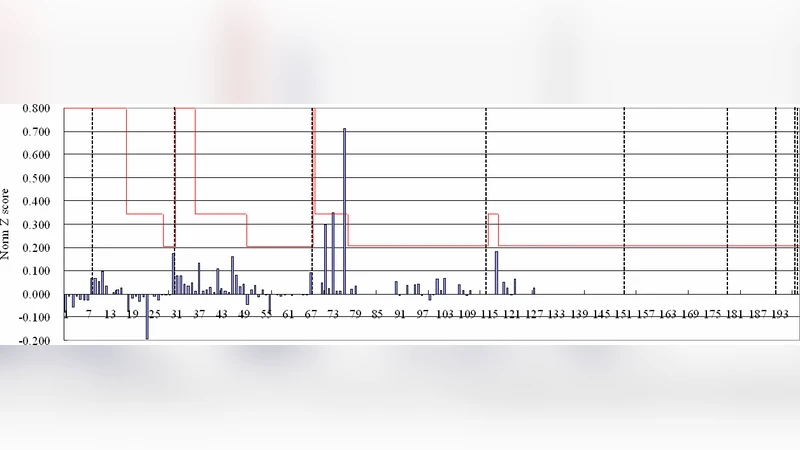
The core of the study is a motif‑analysis pipeline. First, all three‑node and four‑node induced sub‑graphs are enumerated in the real software networks. Then, a large ensemble of Erdős‑Rényi random graphs with the same number of vertices and edges is generated, and the expected frequency of each sub‑graph type is computed. The statistical significance of each sub‑graph is expressed as a Z‑score, defined as the difference between the observed count and the random‑graph mean, divided by the standard deviation. Sub‑graphs with high positive Z‑scores are identified as “significant motifs” because they appear far more often than chance would predict.
Next, the authors introduce a stability metric for each motif. Stability is measured by perturbing the original network (adding, deleting, or rewiring edges) and observing how often the motif survives the perturbation. The experiments reveal a robust positive correlation between a motif’s stability and its abundance: motifs that are structurally resilient tend to be the most frequent in the software networks. Moreover, motifs with the highest Z‑scores are precisely those that exhibit the greatest stability. Typical examples include linear call chains (A → B → C), multi‑inheritance combined with interface implementation, and small patterns that resemble classic design patterns such as Facade or Adapter.
These empirical findings support two theoretical claims. First, software evolution appears to be driven by functional cloning (creating new classes that provide the same service) together with structural duplication (reusing the same dependency pattern). When a developer copies a functional module, the associated dependency sub‑graph is also copied, leading to the proliferation of the same motif across the code base. Second, the system tends toward structural stability: configurations that minimise the propagation of changes (i.e., have low coupling and high cohesion) are preferentially retained because they are more robust under incremental modifications.
From a practical standpoint, the authors argue that motif analysis can become a valuable instrument for reverse engineering and quality assurance. By continuously monitoring the Z‑score distribution of motifs in a project, one can detect anomalous events: a sudden drop in a previously dominant motif may signal a major refactoring, while the emergence of a previously unseen high‑Z motif could indicate an architectural anti‑pattern or a design flaw. Consequently, motif‑based metrics could be integrated into automated tools that flag risky structural changes, predict maintenance effort, or guide developers toward more stable design alternatives.
The paper also acknowledges limitations. The current work relies exclusively on static dependency information; dynamic call graphs, runtime polymorphism, and reflection are not captured, potentially omitting important motifs. The random‑graph baseline is a simple Erdős‑Rényi model, which does not reflect the heavy‑tailed degree distributions typical of software networks; using a configuration model or a small‑world model might yield more nuanced Z‑scores. Finally, the study is limited to a handful of Java projects; extending the analysis to other languages, micro‑service architectures, and longitudinal data across multiple releases would strengthen the generality of the conclusions.
In summary, the authors successfully transplant a well‑established method from network science into software engineering, demonstrating that the prevalence and stability of network motifs provide quantitative evidence for functional cloning, structural duplication, and an overall bias toward structurally stable designs in OO software. Their work opens a promising avenue for using motif‑based diagnostics in reverse engineering, maintenance planning, and automated quality control.
Comments & Academic Discussion
Loading comments...
Leave a Comment