Our Brothers Keepers: Secure Routing with High Performance
The Trinity (Brodsky et al., 2007) spam classification system is based on a distributed hash table that is implemented using a structured peer-to-peer overlay. Such an overlay must be capable of processing hundreds of messages per second, and must be able to route messages to their destination even in the presence of failures and malicious peers that misroute packets or inject fraudulent routing information into the system. Typically there is tension between the requirements to route messages securely and efficiently in the overlay. We describe a secure and efficient routing extension that we developed within the I3 (Stoica et al. 2004) implementation of the Chord (Stoica et al. 2001) overlay. Secure routing is accomplished through several complementary approaches: First, peers in close proximity form overlapping groups that police themselves to identify and mitigate fraudulent routing information. Second, a form of random routing solves the problem of entire packet flows passing through a malicious peer. Third, a message authentication mechanism links each message to it sender, preventing spoofing. Fourth, each peer’s identifier links the peer to its network address, and at the same time uniformly distributes the peers in the key-space. Lastly, we present our initial evaluation of the system, comprising a 255 peer overlay running on a local cluster. We describe our methodology and show that the overhead of our secure implementation is quite reasonable.
💡 Research Summary
The paper presents a comprehensive design, implementation, and evaluation of a secure routing extension for a closed peer‑to‑peer overlay used by the Trinity spam‑classification system. The underlying overlay is based on the Chord distributed hash table (DHT) as implemented in the I3 framework, which provides O(log N) lookup performance but, in its original form, is vulnerable to a range of attacks when operating over an unreliable UDP transport and allowing unrestricted peer admission.
To address these vulnerabilities the authors introduce five complementary mechanisms.
- Key Assignment – Each peer’s 160‑bit identifier is derived from its IP address and port number. The IP/port bytes are concatenated, hashed with SHA‑1, and the lower six bytes of the hash are replaced by the original IP/port. The resulting key appears uniformly random in the key space while still encoding the network address, preventing malicious peers from choosing keys that would cluster them together.
- Distributed Identification, Authentication, and Authorization – The overlay is closed: a peer must be authorized before joining. Authorization is performed via DNS TXT records. Each authorized peer publishes a certificate containing its public key under a domain name that identifies the ring. When a peer receives a message from an unknown sender it performs a DNS lookup to retrieve the sender’s public key; the result is cached locally. Revocation is achieved by removing the TXT entry and broadcasting a notice. This leverages the robustness of the existing DNS infrastructure and limits the cost of public‑key distribution.
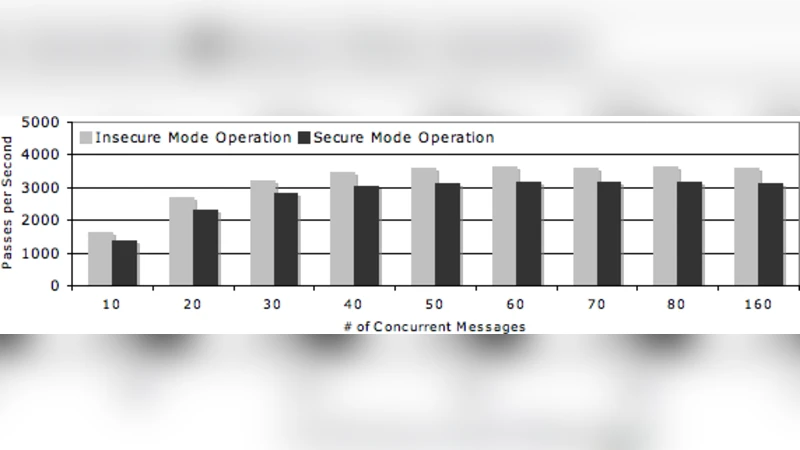
- Message Authentication – Public‑key signatures on every message proved too expensive (throughput dropped from ~4000 pings/s to 15 pings/s). The authors therefore adopt a hybrid approach: the first interaction between two peers uses public‑key encryption to exchange a shared secret, after which all subsequent messages are authenticated with a HMAC (HMA‑C). This restores throughput to roughly 3500 pings/s while still providing strong source authentication.
- Self‑Policing Peer Groups – Each peer belongs to an overlapping group of size g (odd, e.g., 5, 7, 9). The group consists of the peer itself, ⌊g/2⌋ closest predecessors, and ⌊g/2⌋ closest successors. Group members exchange and continuously verify each other’s membership lists and finger‑table entries. Because keys are uniformly distributed, the probability that a group contains multiple malicious peers is low. Inconsistent group lists or contradictory “find_successor” replies trigger immediate ex‑communication of the offending peer. This mechanism limits the ability of malicious nodes to inject false routing information or create partitions.
- Random Routing – To avoid any single node becoming a choke‑point between two honest peers, the routing algorithm deliberately randomizes the path taken for a given lookup, spreading traffic across multiple possible routes. This reduces the impact of a compromised node that might otherwise drop or tamper with all traffic passing through it.
The implementation integrates these components into the I3 code base and is evaluated on a 255‑node local cluster. Experiments compare “secure” and “insecure” modes. In secure mode, the system sustains roughly 3500 pings per second (≈7000 messages per second), only about a 10 % performance penalty relative to the insecure baseline. Latency increases modestly, and the system successfully detects and isolates simulated malicious behavior (e.g., forged “find_successor” replies, dropped messages).
Overall, the work demonstrates that a closed DHT overlay can be hardened against spoofing, denial‑of‑service, and routing‑information attacks without sacrificing the high throughput required for real‑time spam filtering. The authors suggest future directions such as adaptive group sizing, defenses against DNS‑targeted attacks, and scaling the evaluation to larger, geographically distributed deployments.
Comments & Academic Discussion
Loading comments...
Leave a Comment