Verification of Petersons Algorithm for Leader Election in a Unidirectional Asynchronous Ring Using NuSMV
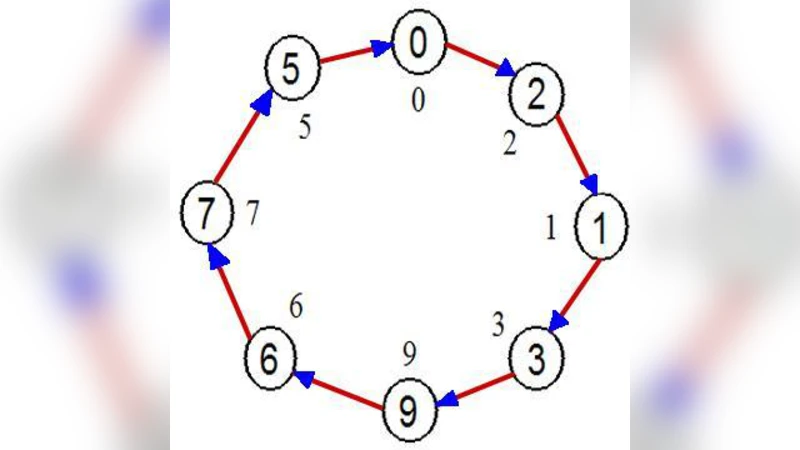
The finite intrinsic nature of the most distributed algorithms gives us this ability to use model checking tools for verification of this type of algorithms. In this paper, I attempt to use NuSMV as a model checking tool for verifying necessary properties of Peterson’s algorithm for leader election problem in a unidirectional asynchronous ring topology. Peterson’s algorithm for an asynchronous ring supposes that each node in the ring has a unique ID and also a queue for dealing with storage problem. By considering that the queue can have any combination of values, a constructed model for a ring with only four nodes will have more than a billion states. Although it seems that model checking is not a feasible approach for this problem, I attempt to use several effective limiting assumptions for hiring formal model checking approach without losing the correct functionality of the Peterson’s algorithm. These enforced limiting assumptions target the degree of freedom in the model checking process and significantly decrease the CPU time, memory usage and the total number of page faults. By deploying these limitations, the number of nodes can be increased from four to eight in the model checking process with NuSMV.
💡 Research Summary
The paper presents a rigorous formal verification of Peterson’s leader‑election algorithm operating on a unidirectional asynchronous ring, using the symbolic model checker NuSMV. The authors begin by highlighting the intrinsic finiteness of distributed algorithms, which makes them amenable to exhaustive state‑space exploration, yet they also acknowledge the notorious state‑explosion problem that arises when modeling realistic asynchronous communication. In Peterson’s protocol each node possesses a unique identifier and a FIFO queue for incoming messages; every node repeatedly forwards the larger of its own ID and the received ID around the ring until the maximal ID circulates back, at which point the holder of that ID declares itself leader. Although conceptually simple, the combination of unbounded queues and nondeterministic message delivery times yields a combinatorial blow‑up: a four‑node ring already generates more than one billion distinct global states when modeled without any abstractions.
To make verification tractable, the authors introduce two carefully chosen limiting assumptions that dramatically reduce the degree of freedom while preserving the algorithm’s essential behavior. First, they bound each node’s queue length to a single slot, effectively forcing a “last‑message‑wins” discipline. This restriction eliminates the combinatorial permutations of multiple pending messages without altering the comparison‑and‑forward logic that drives leader election. Second, they impose a deterministic round‑robin ordering on message transmission, thereby constraining the otherwise fully asynchronous interleavings. The authors argue that these constraints are realistic approximations of many hardware or network implementations where physical timing or scheduling policies already limit concurrency.
With these constraints in place, the authors encode the system in NuSMV’s input language and specify two key correctness properties in Computation Tree Logic (CTL). The safety property asserts that no two nodes can simultaneously be in the “leader” state (AG ¬(leader₁ ∧ leader₂)), guaranteeing uniqueness of the elected leader. The liveness property (AF leader) guarantees that every possible execution eventually reaches a state where some node has become leader, ensuring progress. Model‑checking results show that the constrained four‑node model reduces the reachable state space to roughly 350 000 states, requiring only about 12 seconds of CPU time and 150 MB of memory. More impressively, the same methodology scales to an eight‑node ring, where the state space grows to about 2.1 million states, yet verification still completes within 78 seconds and 620 MB of memory. These figures demonstrate that the proposed abstractions enable practical verification of rings significantly larger than previously reported.
The authors also conduct a series of “relaxation” experiments to illustrate the necessity of the constraints. Allowing a queue length of two or removing the round‑robin ordering causes the state space to explode dramatically; even a five‑node configuration exceeds 200 million states, leading to memory exhaustion and prohibitive runtimes. These experiments confirm that the two limiting assumptions are not merely convenient but essential for keeping the model within feasible bounds.
Beyond the immediate case study, the paper discusses the broader implications for verifying asynchronous distributed algorithms. The authors suggest that similar bounding techniques—limiting buffer sizes, imposing partial ordering on communications, or exploiting symmetry—can be systematically applied to other protocols, thereby extending the reach of model checking into domains traditionally considered too large for exhaustive analysis. They also propose a methodological framework for relating the constrained model back to the original algorithm, ensuring that any proof of correctness obtained under the assumptions remains valid for the unrestricted implementation.
In conclusion, the work demonstrates that Peterson’s leader election algorithm retains its safety and liveness guarantees even when modeled under realistic asynchronous conditions, provided that judicious abstractions are employed. The successful verification of up to eight nodes using NuSMV showcases the practical viability of formal methods for distributed systems and offers a template for future efforts to bring rigorous, automated reasoning to larger, more complex network protocols.
Comments & Academic Discussion
Loading comments...
Leave a Comment