Bits through ARQs
A fundamental problem in dynamic frequency reuse is that the cognitive radio is ignorant of the amount of interference it inflicts on the primary license holder. A model for such a situation is proposed and analyzed. The primary sends packets across …
Authors: Krishnan Eswaran, Michael Gastpar, Kannan Ramch
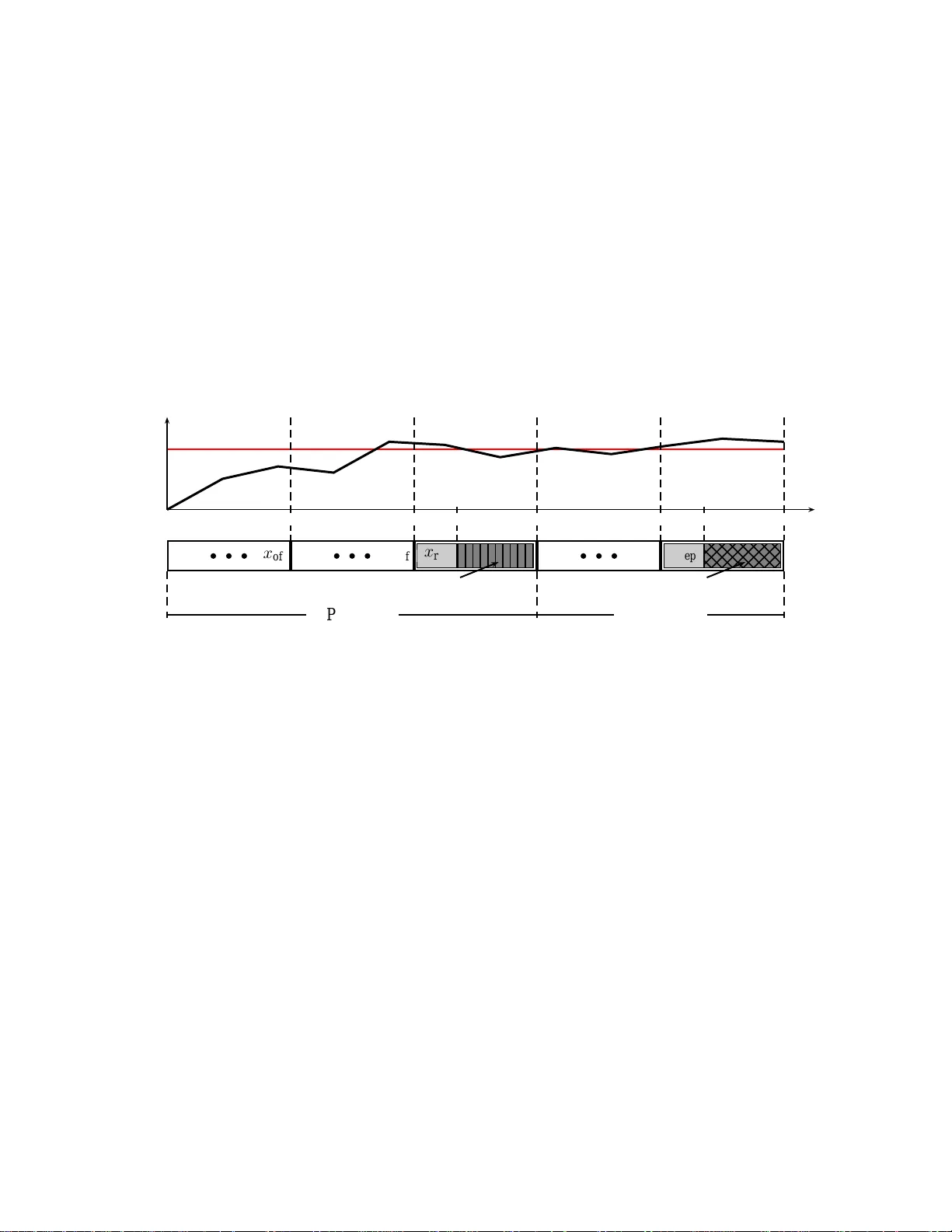
1 Bits through ARQs Krishnan Eswaran, Michael Gastpar , Kannan Ramchandran Dept. of Electrical Engineering and Computer Sciences Univ ersity of California, Berkele y Berkele y , CA 94720 E-mail: { keswara n, gastpar, kannanr } @eecs.berkeley .edu Abstract A fund amental prob lem in d ynamic f requen cy reuse is that the co gnitive radio is ign orant o f the amount of interferen ce it inflicts on the primar y license h older . A model for su ch a situation is pro posed and analyzed. The primary sends packets across an erasure channel and employs simple A CK/N AK feedback (ARQs) to retransmit erased packets. Furthermore, its erasure probab ilities are influenced b y the cogn iti ve rad io’ s activity . While th e cognitive radio does n ot know these in terferenc e ch aracteristics, it can e av esdrop on the primar y’ s ARQs. Th e model leads to strategies in which the c ognitive radio adaptively ad justs its input based on the primary ’ s ARQs thereby g uaranteein g the p rimary exceeds a target packet rate. A relatively simp le strategy whe reby the cognitive radio transmits only when the primary ’ s e mpirical packet r ate exceeds a th reshold is shown to h av e interesting u niversal prop erties in the sense th at f or u nknown time-varying interfere nce character istics, the primar y is guaran teed to meet its target rate. Fur thermor e, a m ore in tricate version of this strategy is shown to be capac ity-achieving for the cog nitive ra dio w hen the interferen ce character istics are time-inv a riant. I . I N T RO D U C T I O N Systems often ne ed to be de signed s o tha t they do not disrupt pre-existing systems with which they interact. This ba ckwards c ompatibility problem is a c entral issue in the study of c ognitiv e radio systems. A c ognitiv e radio is a device that can se nse and adjus t its power , frequency ban d, e tc. to peac efully coexist with other radios with wh ich it s hares sp ectrum [1]. The FCC and international regulatory bo dies are c onsidering modifying their rules to allow for su ch sy stems to o ccupy unlicens ed ban ds or to sha re bands with licensed, predes igned communica tion systems. Th ese licensed us ers are o ften ca lled primaries, legacy systems , o r incumb ents. October 29, 2018 DRAFT 2 The aim of this paper is to s tudy sharing spectrum with legacy systems, in which the ba ckwards compatibility p roblem arises. One p otential solution is to transmit on a ba nd tha t is cu rrently u noccup ied and to leave that band o nce a primary is detected. For thes e “ detect-and-avoid” systems, on e research aim is to understa nd the feasibility of d etecting the presence of a primary system subjec t to no ise u ncertainty and qu antization effects [2], [3], [4]. A different ap proach is for the cogn iti ve radio to occ upy bands on which the p rimary is already active but in such a way as to mitigate the interference generated on the primary system. T w o such information- theoretic models h av e be en introduced to s tudy cogn iti ve radio and spe ctrum sharing systems . T he first is sometimes called the cognitiv e radio channel [5], [6], [7], [8], [9], [10], [11]. This chan nel is a v a riation on the two-user interference c hanne l [12], [13 ], [14], [15 ] with the mo dification that the cognitive radio (one of the trans mitters) kn ows the mes sage that the primary (the other transmitter) will s end. Among thes e papers, Devro ye, Mi tran, and T arokh [5] as well as Jovi ˘ ci ´ c and V iswanath [6] consider a Gaussian scen ario in which the primary’ s s trategy can be thought of as a fixed, prede signed legacy s ystem. Specifically , they s how that for the ir setup, there is an optimal achiev able strategy that ena bles the p rimary to continue using a point to p oint Gaussian cod ebook. The res ult h ighlights the fact that in cognitiv e radio problems, one may not hav e the flexibili ty to modify the primary’ s design and must instea d design the cogniti ve radio in such a way that the p rimary co ntinues to meet its tar g et performance. The secon d approach is to consider the capacity of systems with a constraint on the interference power generate d a t c ertain locations. The assump tion is that the primary systems that occu py the se loc ations will be able to hand le this level of interference [16], [17]. W e take ins piration from thes e two models in the following example, which forms the starting point of the cu rrent in vestigation. It is a model of the practically mos t interes ting ca se, whe re the cogn iti ve transmitter is close to t he primary recei ver , thus creating substantial interference. For simplicit y , we assume the cogniti ve r adio’ s receiv er i s shadowed from the primary transmitter , the reby a voiding interference from that sy stem. An illustration o f the s etup is given in Figure 1 . Example 1 : Suppose the primary send s pa ckets across an erasure ch annel and rec eiv es feedba ck from its receiver to retransmit the p acket o r send the n ext one . Th e c ognitiv e radio, on the othe r h and, h as a noiseless c hanne l to its receiver w ith P + 1 channe l inputs divided into two classe s: a silent symbo l x of f results in a succes sful receipt of the primary’ s trans mitted packet, and the remaining P transmit s ymbols cause the primary’ s p acket to be eras ed. Suppo se the primary wants a gua ranteed rate of 1 2 ; tha t is, one packet should be suc cess fully received per two transmissions on average. By simply alternating cha nnel October 29, 2018 DRAFT 3 uses betwee n the silent symbol and sending information with the P transmit symbols, the cognitiv e rad io guarantees the primary ra te 1 / 2 target and c an itself ach iev e a rate of 1 2 log P , (1) where P + 1 is the nu mber of channe l inpu t sy mbols av a ilable to the cogn iti ve radio. In the spirit of the previous work, Exa mple 1 considers a primary that is unaware of the c ogniti ve radio. Howev er , Example 1 makes the more dubious as sumption that the cogniti ve rad io knows what the primary’ s erasure p robabilities are for its two clas ses of inp uts. As a res ult, the strategy prese nted is not robust to deviations from the erasu re probabilities provided in the examp le. For instance, if the primary’ s eras ure p robability for a silent symbol x of f is ǫ 0 > 0 , the s trategy outlined will not allow the primary to mee t its rate 1 / 2 tar get. The issue is that the cogniti ve radio will no t be able to directly estimate the interference it creates for the primary . Such estimates are generally o btained by training via pilot symb ols, but the primary receiver is unlikely to train with the cog niti ve radio transmitter . Howev er , certain kinds of 1-bit feedbac k have been shown to be sufficient for b eamforming [18], [19]. W e a dopt this insight as we build on Ex ample 1 by introducing both an unc ertainty a nd s ensing compone nt to the problem. ENC W s ENC W p DEC ˆ W s DEC ARQ ˆ W p Erasure Fig. 1. An example of the type of channel model for our cognitiv e radio system in which the primary has message W p and the cognitiv e radio has message W s . T he cognitiv e r adio transmitter can listen to the ARQ feedback the primary receiv er sends to its transmitter to adapt its transmission rate and reduce interference on the primary system. Example 1, continued : The cognitive rad io’ s silent s ymbol no w induces an erasure probability ǫ 0 < 1 / 2 , and its transmit symbols induce a n e rasure probability of ǫ 1 > 1 / 2 , both of which are unkn own to the cognitiv e radio. However , the cognitive radio trans mitter can sen se the primary’ s ARQs, wh ich we will denote with the indicator rand om variables A k when the primary’ s k -th transmission is received. Figure 1 s hows a s chematic block diagram o f this setup. October 29, 2018 DRAFT 4 The cognitiv e radio’ s strategy is as follows. If the primary is exceed ing its rate tar ge t a t time k , the cognitiv e radio s ends o ne of its transmit symbols based on its message . This happe ns when 1 k P k i =1 A k ≥ 1 2 . Otherwise, the cogn iti ve radio sends its silent s ymbol. Let τ k be the indica tor function that the cognitive radio s ends a transmit symbol at time k . Thus , P ( A k = 1 | τ k ) = 1 − ǫ τ k . Th en the cog niti ve radio’ s rate at time n is 1 n n X k =1 τ k log P . (2) Note that for ǫ 0 = 0 , ǫ 1 = 1 , this strategy is as go od as the on e outlined in Exa mple 1. What can we s ay about the rate for the primary a nd cognitiv e radio in Exa mple 1 ? Let S 0 = 0 and S k = S k − 1 + ( A k − 1 / 2) rep resent the dif fere nce between the number of packets the primary has rec eiv ed by time k and its targeted number of pac kets b y time k based on a target packet rate of 1 2 . Su ppose the A k are ind epende nt in k . Then S k is a pos iti ve rec urrent Markov cha in and is non negati ve if a nd only if τ k = 1 , w hich ca n be verified by c onfirming that its s tationary distribution is π i/ 2 = (2 ǫ 1 − 1)(1 − 2 ǫ 0 ) 2 ǫ 1 ( ǫ 1 − ǫ 0 ) 1 − ǫ 1 ǫ 1 i i ≥ 0 (2 ǫ 1 − 1)(1 − 2 ǫ 0 ) 2(1 − ǫ 0 )( ǫ 1 − ǫ 0 ) ǫ 0 1 − ǫ 0 − i +1 i ≤ 0 . (3) W e can make the following state ment. F act: S uppose S 0 is distributed ac cording to π . Then for a ll k ≥ 1 , P ( τ k = 1) = ∞ X i =0 π i/ 2 = 1 / 2 − ǫ 0 ǫ 1 − ǫ 0 . (4) The fact allows u s to get a hand le on the cog niti ve radio’ s rate. Furthermore, the primary’ s expected rate is k − 1 k X i =1 X j =0 , 1 P ( A i = 1 | τ i = j ) P ( τ i = j ) = 1 2 . (5) Note that this strategy does not depend on the cogniti ve radio knowing the values ǫ 0 and ǫ 1 a priori. Howe ver , the cog niti ve radio does kn ow the p rimary’ s rate target, wh ich is 1 / 2 in this exa mple. In the remainder of the paper , we as sume the primary’ s rate target is known in advance to the c ognitiv e radio, but the primary’ s e rasure prob abilities are unknown. In this work, we cons ider optimal coding strategies for the case in which the primary is a packet erasure s ystem as desc ribed in Example 1. 1 For the chann el of the cogn iti ve rad io, we cons ider a more 1 This formulation lends itself well to many spectrum sharing problems in which the primary i s a separately designed system and whose exact implementation is partially obscured from the cognitiv e radio. October 29, 2018 DRAFT 5 general class of (noisy) chan nels. As w e show , the primary ca n meet its target ra te even if the c ogniti ve radio is activ e for a ce rtain fraction of c hanne l uses. This interference budget av ailable to the c ognitiv e radio, while u nknown a priori, can be es timated via the primary ARQs and rate target, which are known at the cogniti ve rad io encode r . One can determine the ca pacity o f the co gniti ve radio in terms of this interference budget, which we ca ll the rate-interference budget (RIB) tradeoff function. W e show an achiev able s trategy for the gen eral cas e in which the primary’ s pac ket erasure probabilities can fluctuate and fin d a ma tching conv erse for the RIB function whe n they do not. In Section II, we d efine the problem we are conside ring precisely , includ ing the c hannel mod el for the cognitiv e rad io and the allo wable coding strategies that the cognitiv e radio c an ad opt. Thes e strategies force the cognitive radio to provide gu arantees about the primary’ s rate that do not dep end on the time horizon that the cogn iti ve radio use s to mea sure its own rate ( horz ion-independ ence condition) and force it to be robust to fluctua tions in the primary’ s packet eras ure probabilities ( rob us tness condition). In Section III, we show how to refine the strategy from Example 1 to provide s uch g uarantees that also allo w positi ve rate for the co gniti ve radio, which leads to two new strategies: the fix ed-code book pr otoc ol and the c odebo ok-adaptive pr otocol . In Section IV , we present a con verse when the erasure probabilities are time-in variant, wh ich matches the rates achiev ab le by the c odeboo k-adaptive protoco l proposed in Section III. S ection V revisit s Example 1 in the introduction and considers new ones . Se ction VI con cludes the paper with a discus sion of our contributions and future work. I I . P R O B L E M S E T U P A N D M A I N R E S U L T Capital letters X , Y , Z repres ent rando m variables and ca lligraphic letters X , Y , Z denote finite sets. W e will focus on discrete me moryless channe ls i n this work, but potential extensions t o Gauss ian channels will be discusse d in Section VI. For co n venienc e, p ( x ) is the probability distribution o f X at x . Similarly , p ( y | x ) is the cond itional probability distribution of Y at y g i ven X = x . Notation for entropy H ( X ) , mutual information I ( X ; Y ) , etc. are co nsistent with the no tation of Cover and Thomas [20 ]. A i − 1 P ( Y , A | X ) X i Y i A i ENC W S DEC ˆ W S Fig. 2. E qui v alent channel model f rom the cogniti ve radio’ s perspecti ve. A i is an indicator random variable: A i = 1 means that the packet sent by the primary at time i was successfully receiv ed. October 29, 2018 DRAFT 6 A. Eq uivalent Cha nnel Model As a legacy ARQ s ystem, the primary is as sumed to have the following fixed strategy . At time i , it sends a packet to its receiver and recei ves feedback A i to indicate whe ther the pa cket was erased or succe ssfully receiv e d ( A i = 0 or 1 , respectively). If the packet is erased, the primary retransmits the same packet a t time i + 1 . If the pa cket is suc cess fully receiv ed, the primary transmits a n ew packet at time i + 1 . Thus, we will refer to A i as the primary’ s ARQ fee dback . Since the p rimary’ s strategy is fixed, we now have to des ign the cogniti ve radio’ s strategy . Figu re 2 illustrates this problem; the primary mere ly appea rs a s a co nstraint on the cogniti ve rad io in the sh ape of A i . That is, in addition to communicating, the cognitiv e radio must a lso control its chan nel inputs to guarantee the primary’ s rate, i.e. suc h that to the first-order 2 , k − 1 k X i =1 A i ≥ R p , (6) where R p is the des ired and prespecifie d performanc e of the p rimary sys tem. Furthermore, this control must b e robust to fluctuations in the chan nel between the cognitiv e radio transmitter and p rimary receiv er . Thus, the primary’ s ARQ feed back provides a means for the c ognitiv e rad io to apply this c ontrol. B. Ch annel Mod el and Coding W e now c onsider the DMC with feedbac k from Figure 2 in mo re de tail. L et X = { x of f , 1 , . . . , |X | − 1 } be the c hannel inputs. Then at time i , the co nditional distrib ution of the chan nel ou tput Y i and primary’ s ARQ A i giv e n X i = x ca n be expressed as p ( y i , a i | x i = x ) = p ( y i | x i = x ) · ǫ x,i · exp a i · log 1 − ǫ x,i ǫ x,i . (7) W e ass ume that the sequ ences { ǫ x,i } ∞ i =1 , for x ∈ X are unknown at the encode r and dec oder . For simplicity , we assume ǫ x off ,i = ǫ 0 (8) does not de pend on i , which a ssumes that the primary’ s c hanne l is fi xed when the co gniti ve rad io is silent. Howe ver , allo wing ǫ x,i to vary with i for x 6 = x of f reflects unc ertainty about the amoun t of interferenc e the c ognitiv e rad io is g enerating o n the primary . W e will as sume that for all x 6 = x of f and i = 1 , 2 , . . . , ǫ x,i > ǫ 0 (9) 2 Second order issues and tight delay constraints are discussed in Section VI. October 29, 2018 DRAFT 7 In the remainde r of this paper , we make the technica l assumption tha t there is a known c onstant ν > 0 such that for all i , R p < 1 − ǫ 0 − ν . Th is a ssumption enables the primary to tolerate some interferenc e from the cogn iti ve radio while guarantee ing the cogn iti ve radio achieves a p ositi ve rate. The de finition of the rate an d capa city for the seco ndary a re complicate d by the fact that the number of cha nnel uses de pends on the realizations of ǫ x,i . Therefore, we need to be p recise on wh at is mea nt by messag es. W e de fine the set of po ssible messa ges to b e the set o f b inary seq uence s { 0 , 1 } nC max , where C max = log min {|X | , |Y |} . Le t W k be the first k bits o f the mess age a nd W = W nC max . An ( n, f n , g ) c ode (we c all n the blocklen gth) c onsists of a set of enco ding functions f i : { 0 , 1 } i − 1 × { 0 , 1 } nC max → X for i = 1 , 2 , . . . , n , X i = f i ( A i − 1 , W ) , (10) and de coding function g : Y n → { 0 , 1 } nC max ˆ W = g ( Y n ) . (11) A strate gy is a se quenc e of ( n, f n , g ) c odes indexed by n on the pos iti ve integers n = 1 , 2 , . . . . Strategies must respec t the primary’ s rate tar g et, so the followi ng defin ition res tricts the type o f strategies we allow . A strategy is va lid if for all ν > 0 and for k ≤ n in eac h ( n, f n , g ) c ode, P k − 1 k X i =1 A i ≤ R p ! ≤ K 1 ,R p ,ν,k e − k · K 2 ,R p ,ν , (12) where the constan ts K 1 ,R p ,ν,k < ∞ , 0 < K 2 ,R p ,ν < ∞ de pend on ly on the fat in the sys tem ν and target rate R p , a nd the right s ide of (12) go es to 0 a s k → ∞ . Note that a valid s trategy impos es two res trictions. First, the c on vergence of the primary’ s rate should not depen d on the block length of a strategy ( horizon -independe nce c ondition). Seco nd, the conv e rgence of the primary’ s rate s hould be the same irrespective o f ǫ 0 , { ǫ x,i } ∞ i =1 , x ∈ X − { x of f } ( r obustness cond ition). For a given valid s trategy , we will use the notation ˆ W n to denote the d ecode d output for its code of blocklength n . A rate R is achievable if for all δ > 0 , there exists a valid strategy and n 0 ( δ, ǫ 0 , { ǫ x,i } ∞ i =1 , R p ) suc h that for the strategy’ s code s with block length n ≥ n 0 , P ( ˆ W n ⌊ n ( R − δ ) ⌋ 6 = W ⌊ n ( R − δ ) ⌋ ) ≤ δ . (13) The se t of a chiev a ble R is de noted as R ( ǫ 0 , { ǫ x,i } ∞ i =1 , R p ) . October 29, 2018 DRAFT 8 The rate-interference budget (RIB) function R IB ( ǫ 0 , { ǫ x,i } ∞ i =1 , R p ) is define d as R IB ( ǫ 0 , { ǫ x,i } ∞ i =1 , R p ) = sup R ∈R ( ǫ 0 , { ǫ x,i } ∞ i =1 ,R p ) R. (14) For the spec ial c ase in which ǫ x,i = ǫ x for all i , it w ill be co n venient to use the shorthan d ~ ǫ , where ~ ǫ is a len gth |X | vector , and we w ill us e the s horthand R IB ( ~ ǫ, R p ) . C. Con tributi ons W e now state the main contributions of this p aper . First, we fin d a valid strategy tha t a chieves po siti ve rates for the cogn iti ve radio. From the definition o f a valid strategy , this implies that there exists a sequen ce o f cod es such tha t the p rimary meets its target rate irrespe cti ve of ǫ 0 , { ǫ x,i } ∞ i =1 . Pr op osition 1 : For a ll ν > 0 and co rresponding ǫ 0 , { ǫ x,i } ∞ i =1 , R p , a lower -bound to the RIB func tion is at least R IB ( ǫ 0 , { ǫ x,i } ∞ i =1 , R p ) ≥ (1 − R p / (1 − ǫ 0 )) · C ∗ , (15) where C ∗ = max p ( x ) I ( X ; Y ) . Moreover , there exists a valid strategy that ac hieves the above rates for all ( ǫ 0 , { ǫ x,i } ∞ i =1 , R p ) sa tisfying ν > 0 . Proposition 1 follows immediately from Theorem 1. Furthermore, we can precisely cha racterize the capac ity of the cogniti ve radio f or the case of t ime-in variant interf erence on the primary , in which ǫ x,i = ǫ x for all x ∈ X . Pr op osition 2 : For all ν > 0 and case s in which ǫ x,i = ǫ x for a ll i , the RIB function is R IB ( ~ ǫ, R p ) = max p ( x ): P x ǫ x p ( x ) ≤ 1 − R p I ( X ; Y ) . (16) Moreover , there exists a valid s trategy that ac hieves the above rates for all ( ~ ǫ, R p ) sa tisfying ν > 0 . For this setting, we will refer to the c onstraint P x ǫ x p ( x ) ≤ 1 − R p as the inter fer ence b u dget . Note that the c onstraint is base d on h ow muc h interference each of the cognitive radio’ s chan nel inputs gen erates on the primary compared to how much is tolerable for the primary’ s d esired pe rformance. Proposition 2 follows immediately from Theorem 2, wh ich provides achievabili ty , and Theo rem 3, which provides the con verse . These are stated in Se ctions III and IV , respectively . W e note that Theorem 2 relies on a more intricate valid strategy than the one in the proof o f Theo rem 1. October 29, 2018 DRAFT 9 I I I . A C H I E V A B L E S T R A T E G I E S In this s ection, we pres ent two achiev able strategies a nd state resu lts on the rates the co gniti ve radio can achieve while gua ranteeing rate to the primary und er various interference conditions. The first of these– the fixed-co debook protocol– is a gene ralization of the a pproach considered in Example 1, in which the c ognitiv e radio be comes active on ly when the primary is me eting its target rate. W e show that this s trategy is valid, i.e. the primary meets its rate target under u nknown time-varying interferenc e characteristics, a nd can gi ve equally gen eral rate guarantee s for the cognitive radio. The s econd strategy– the codebook-ad aptiv e protocol– b uilds on the first strategy to pred ict the amoun t of interference the cognitiv e rad io will ge nerate on the primary and o ptimize its co debook to maximize its own rate. Like the first strategy , this strategy is also valid, so the primary meets its rate tar g et under unknown time- varying interference characteristics. W e p rovide rate guarantees for the cognitiv e radio under the more limited set of unk nown time-in variant interference charac teristics, an d in Section IV, we s how that the codebo ok-adaptive protocol provides the optimum rate for the cognitive radio within this set. A. Fi xed-Codeb ook P r otoco l Recall the app roach co nsidered in Example 1 over the noise less c hanne l. The silent symb ol x of f is used for ea ch ch annel use when the primary is n ot me eting its target rate. Otherwise, one of the remaining P symbols is used to se nd information a bout the mess age. As demon strated in that example, this lead s to a rate proportional to log P . Howe ver , this strategy ap pears to be wasteful in tha t x of f is no t being used to se nd information about the mess age. One way to overcome this limitati on is to group multiple channel uses into fr ames . Ea ch frame is either silent – c onsisting of only silent sy mbols x of f – o r activ e – consisting of a ny combinations of all P + 1 symbo ls, including x of f . Clearly , over the active frames, this increases the rate since the av ailable channe l inpu t alpha bet is larger . The main issues a re: • T o find a rule by wh ich the c ognitiv e transmitter d ecides before each frame whethe r the frame will be silent or a cti ve. The cognitive transmitter then also need s s ome way of indicating its choice to the c ognitiv e rec eiv er . • T o ap propriately s elect the frame length. If the frame length is too short, the n no rate ga in is attained. Con versely , if the frame leng th is too lar ge, then the n on-interference gu arantee g i ven in (12) can no longer be respec ted. W e now illustrate the approa ch in the context of Example 1. For the sa ke of con creteness , c onsider the case in which the frame len gth K n = 3 chann el uses . For this illustration, we will assu me the d ecision October 29, 2018 DRAFT 10 to become ac ti ve is governed by the threshold rule P 3 ⌊ ( i − 1) / 3 ⌋ j =1 ( A j − 1 2 ) > 0 . Then a sample run ma y look as follo ws: i 1 2 3 4 5 6 7 · · · P i − 1 j =1 A j − 1 2 0 1 2 1 1 2 0 − 1 2 − 1 · · · X i x of f x of f x of f x on,1 x of f x on,P x of f · · · T imes i = 4 , 5 , 6 repres ent an ac ti ve frame, where the cha nnel inpu t a t time i = 4 is simply a beaco n to indicate to the dec oder that the frame is activ e; the messa ge information is s ent over i = 5 , 6 . Despite the fact that the primary me ets the rate target R p = 1 2 over ch annel u ses 2 a nd 3 , the cognitiv e radio send s the s ilent symbol x of f for the d uration of the frame. Thu s, one ha s to be careful to set the frame length K n and trans mission thres hold to make sure the cognitiv e radio can a chieve a signific ant rate. Likewise, the c ogniti ve radio sends the message information ( x of f , x on,P ) over chan nel uses 5 and 6 even tho ugh the primary no longe r exceeds the rate target 1 2 . Thus, one has to be ca reful to se t the frame length K n and transmis sion thresho ld s o that the primary’ s rate sa tisfies (12), s o the strategy is valid. R p + γ k − 1 P k j =1 A j K n 2 K n 2 K n + κ n 3 K n 4 K n 4 K n + κ n 5 K n k X k x of f b b b x of f x of f b b b x of f x rep x of f b b b x of f x rep silent frame a cti ve frame repetition co de codeword Fig. 3. In the fixed-codeboo k protocol, channel uses are grouped into units kno wn as frames. At the start of a frame, the cogniti ve radio encoder chooses to become active if the primary’ s pack et rate k − 1 P j =1 A j is abo ve a threshold R p + γ + o (1) . Otherwise, it stays silent for the frame, i.e. sends the symbol x off . On an active frame, t he encoder uses a length κ n repetition code to si gnal to the decoder that i t is active and sends a codew ord ove r the remaining channel uses to con vey additional bits of the message. W e now u se the intuition from the illustration above to c onstruct the fi xed-cod ebook pr o tocol , which we will the n p rove is a v alid strategy , as define d in Sec tion II. Figure 3 provides a n illustration of the fixed-codebo ok protocol. For co n venienc e, we define S k = k X i =1 ( A i − R p ) , (17) which is positive at time k if and only if the primary is excee ding its target rate. October 29, 2018 DRAFT 11 1) Determining S ilent F rames : As before, the c ognitiv e radio makes a decision to b e silent or active over frames of length K n channe l use s. Specifica lly , the follo wing con dition specifie s the frames over which the cog niti ve radio is silent: X j = x of f if S i j − i j γ < K n , (18) where i j = ⌊ ( j − 1) /K n ⌋ · K n , and γ is an a dditional parame ter for s etting the threshold along with K n to sa tisfy condition (12). 2) Active F rames: It remains to define what the c ognitiv e trans mitter doe s over an activ e frame. As in the n oiseless cas e, we want to inform the d ecode r that the frame is active, but in the noisy c ase, it cannot be don e with a single channe l us e. a) Rep etition Coding: The cognitiv e transmitter uses a length κ n repetition co de to inform the cognitiv e receiv er that the frame is active. W e will ass ume without loss of gene rality there exists a channe l input x rep 6 = x of f such tha t P ( Y = y | X = x of f ) 6 = P ( Y = y | X = x rep ) for s ome y . (Note: we can ass ume this without loss of generality since if it were not true for a ny symbol, the cogn iti ve radio’ s channe l inputs X i would be independ ent o f the cha nnel outputs Y i , an d the chan nel could not b e u sed for co mmunicating in the first place. ) Then the repetition c ode over the first κ n channe l uses of an a ctiv e frame is spe cified b y the followi ng condition: X j = x rep if S i j − i j γ ≥ K n , i j < j ≤ i j + κ n , (19) where i j = ⌊ ( j − 1) /K n ⌋ · K n . b) Mes sage Information: For the remaining channel uses o f an a ctiv e frame, the encode r sends information abo ut the me ssage to the dec oder . It do es so with a bloc klength K n − κ n codebo ok C fixed of rate C ∗ − ˜ δ , whe re C ∗ = m ax p ( x ) I ( X ; Y ) . W e will den ote codewor d m as ˜ X K n − κ n ( m ) , where m ∈ { 1 , . . . , exp { ( K n − κ n )( C ∗ − ˜ δ ) } . The following notation will be useful for understand ing the c hannel inputs d uring the remainde r of an activ e frame. Let V 1 denote the c hannel index preced ing the start of the first a cti ve frame, V 2 the secon d, V 3 the the third, and so on . That is, V 1 = in f { i ≥ 0 : S i − iγ ≥ K n , i = mK n for some m ∈ Z } , (20) V k = in f { i > V k − 1 : S i − iγ ≥ K n , i = mK n for s ome m ∈ Z } . (21) W e now charac terize the remaining c hanne l inputs. For the ℓ -th active frame and letting m ℓ be bits ℓ ( K n − κ n )( C ∗ − ˜ δ ) log 2 e + 1 through ( ℓ + 1)( K n − κ n )( C ∗ − ˜ δ ) log 2 e of messa ge W , X j = ˜ X j − V ℓ − κ n ( m ℓ ) if V ℓ + K n ≥ j > V ℓ + κ n . (22) October 29, 2018 DRAFT 12 A su mmary of the fixed-codebo ok p rotocol is given in T able I. T ABLE I S U M M A R Y O F T H E FI X E D - C O D E B O O K P R O T O C O L . X j Conditions Description ˜ X j − V ℓ − κ n ( m ℓ ) V ℓ + K n ≥ j > V ℓ + κ n , ℓ ∈ Z + Activ e frame: ˜ X K n − κ n ( m ℓ ) ∈ C fixed to send fragment m ℓ . x rep V ℓ + κ n ≥ j > V ℓ , ℓ ∈ Z + Repetition code: notify decoder of activ e frame x off all other j Silent frame 3) P erforma nce of the F ixed-Cod ebook Pr o tocol: For this strategy , we h av e the following result. Theorem 1: For all R p , ν > 0 , the re exist ch oices of κ n , K n , γ , ˜ δ su ch that the fixed-codeboo k protocol is a vali d strategy , i.e. primary’ s p acket rate s atisfies the condition in (12 ) for a ll { ǫ x,i } ∞ i =1 , x ∈ X − { x of f } . Furthermore, for these p arameter cho ices, the rate 1 − R p 1 − ǫ 0 · C ∗ (23) is ac hiev a ble for the cognitiv e ra dio, where C ∗ = m ax p ( x ) I ( X ; Y ) . Pr oo f: W hile othe r cho ices will work, for the purpos es of the proof, we will let K n = ⌊ n 1 / 8 ⌋ ,κ n = ⌊ n 1 / 16 ⌋ , (24) and any γ satisfying 0 < γ < min { ˜ δ / 2 , ν / 2 } . W e will ass ume that ˜ δ > 0 , but a detailed prescription is giv e n in Le mma 6 below to allow the rate loss to b ecome arbitrarily small. The proof of the theorem is divided into three parts. 1) The primary’ s rate satisfies con dition (12), s o the strategy is valid. (Le mma 3) 2) There exists a c odeboo k su ch that cognitiv e rad io dec oder error probability is small, thu s satisfying (13) for some R . (Lemma 4) 3) By app ropriately choos ing ˜ δ , the R in (13) can be made a rbitrarily close to 1 − R p 1 − ǫ 0 · C ∗ . (Lemma 6 ) These resu lts are proved in the App endix I. B. Co debook -Adaptive P r otoco l Let us return to Ex ample 1. Theorem 1 implies that whe n the fixed-code book p rotocol is a pplied to the n oiseless chann el, the c ognitiv e rad io is g uaranteed to ach iev e rates R ≥ (1 − R p / (1 − ǫ 0 )) · log(1 + P ) . (25) October 29, 2018 DRAFT 13 Hence, the fixed-codeb ook protoc ol only adapts the duty-cycle to the actual degree o f interferenc e. In equation (25), when P is large, this is not a good strategy . A better strategy would be to also ad apt the cod ebook to the actual degree of interference, thereby gu aranteeing a high er duty-cycle. Clearly , to still meet the interference guarantee the rate of the ada pted cod ebook will typically be smaller , b ut with respe ct to e quation (25), this pe nalty will app ear in the logarithm. In this s ection, we propo se the codebo ok-adaptive pr o tocol , which first ob tains a c oarse me asuremen t of the actual interference (Phase I), us es this to se lect a cod ebook appropriately and communicates its c hoice to the decod er (Phase II), and then runs the s tandard fixed-code book protoco l described in Section III-A (Phase III). R p + γ k − 1 P k j =1 A j K n 2 K n 2 K n + κ n 3 K n 4 K n 4 K n + κ n 5 K n k X k x of f b b b x of f x of f b b b x of f x rep x of f b b b x of f x rep Phase I Phase II estimate interference selected co debook Fig. 4. The codebook-ad aptiv e protocol is like the fixed-cod ebook protocol except the fir st two activ e frames are used to select a codebook to use and inform the decoder about it. In P hase I, the cognitiv e radio sends pilots of each of its channel inputs and uses the AR Qs to create estimates of the interference it generates on the primary . In Phase II, the cognitiv e radio notifies the decoder which among a polynomial sized set of codebooks it has selected based on its estimates from P hase I. P hase III, which immediately follows the end of P hase II abov e, i s almost identical to the fixed-co debook protocol, except the code words are no w from the codebook selected during Phase I and Phase II. The codeb ook-ada pti ve protocol is su mmarized in F igure 4. The strategy is quite similar to the fixed- codebo ok protocol. In fact, it us es the same threshold rule and the s ame repetition cod e to signify a n activ e frame. Tha t is, the c odeboo k-adaptive protocol follows the rules: X j = x of f if S i j − i j γ < K n , (26) X j = x rep if S i j − i j γ ≥ K n , i j < j ≤ i j + κ n , (27) where i j = ⌊ ( j − 1) /K n ⌋ · K n , a re iden tical to c onditions (18) and (19) in the fixed -rate protocol. The dif ference b etween the two s trategies is thus in wh at follows the repetition code in a n acti ve frame. In particular , the encoder us es the first a cti ve frame to es timate the chann el, the sec ond to inform the October 29, 2018 DRAFT 14 decode r which codeb ook it w ill us e base d on those rates , and the third a nd greater a cti ve frames to s end messag e information us ing the s elected code book. As before, let V 1 denote the cha nnel index preced ing the start of the fi rst ac ti ve frame, V 2 the second , V 3 the the third, and s o o n. That is, V 1 = inf { i ≥ 0 : S i − iγ ≥ K n , i = mK n for some m ∈ Z } and V k = in f { i > V k − 1 : S i − iγ ≥ K n , i = mK n for some m ∈ Z } . 1) Phase I: During the first ac ti ve frame, the cog niti ve radio e stimates the interferenc e p roduced by each cha nnel input. Let µ = ⌊ K n − κ n |X | ⌋ . Then for x ∈ { 0 , . . . , |X | − 1 } , the c hannel inp uts for the fi rst frame ca n be described a s X j = x , if V 1 + κ n + ( x + 1) µ ≥ j > V 1 + κ n + xµ . (28) Using these chann el inpu ts, the encode r ca n use the ARQs to es timate the primary’ s erasu re p robabilities. ˆ ǫ x = µ − 1 V 1 + κ n +( x +1) µ X i = V 1 + κ n + xµ +1 A i . (29) W ith these estimates, the end of this first activ e frame marks the end o f Pha se I. 2) Phase II : B ased on the estimates ˆ ǫ x , the encod er cho oses a codeb ook amon g a set of co debook s; it informs the d ecoder of this c hoice in Pha se II. Each c odeboo k in the se t has a diff erent input distributi on corresp onding unique ly to eac h length- C n type p x C n of X , i.e. p x C n is a proba bility distribution with the prope rty that for all x ∈ X , p x C n ( x ) = n x /C n such that n x is a nonnegative integer an d P x ∈X n x = C n . Thu s, there are a t most ( C n + 1) |X | codebo oks in the s et. The c odebo ok C x C n of type p x C n is a random co debook with codewords gene rated i.i.d. ac cording to Q K n − κ n k =1 p x C n ( x k ) and ha s ˜ M x C n = exp { ( K n − κ n )( R x C n − ˜ δ ) + } , (30) where R x C n is the mutua l information I ( X ; Y ) with X having input p robability distrib ution p x C n ( x ) . One then selects the cod ebook acco rding to the following rule: χ = argmax x C n : P x ˆ ǫ x p x C n ( x ) ≤ 1 − R p − 2 γ − ˜ δ ˜ M x C n . (31) The encod er us es the co debook from the fixed-cod ebook protocol in the se cond activ e frame to inform the de coder of its c odeboo k selected code book. (Note: Based on the pa rameter ch oices cons idered in this work, ( C n + 1) |X | is small enou gh to on ly require a mes sages from fixed-co debook protocol’ s code book, so the en coder simply use s the messag es tha t result in the lowest p robability of error .) Su ppose the October 29, 2018 DRAFT 15 selected co debook correspo nds to mes sage m χ . Then for the sec ond active frame, X j = ˜ X j − V 2 − κ n ( m χ ) if V 2 + K n ≥ j > V 2 + κ n . (32) W ith the de coder informed of whic h cod ebook has been s elected, the end o f this activ e frame ma rks the end of Phas e II. 3) Phase III: In Phase III, the ac ti ve frames are now used to send messag e information. Thu s, they resemble the activ e frames in the fixed-cod ebook protocol, with the ma in difference that the codebook χ is use d. Let m ℓ be bits ℓ ( K n − κ n )( R χ − ˜ δ ) log 2 e + 1 through ( ℓ + 1)( K n − κ n )( R χ − ˜ δ ) log 2 e of mes sage W . For the ( ℓ + 2) -th ac ti ve frame, we c an expres s the mess age information s egment of the frame as X j = ˜ X j − V ℓ +2 − κ n ( m ℓ ) if V ℓ +2 + K n ≥ j > V ℓ +2 + κ n , (33) where ˜ X K n − κ n ( m ℓ ) ∈ C χ . A su mmary of the codebo ok-adaptive protocol is given in T able II. T ABLE II S U M M A R Y O F T H E C O D E B O O K - A DA P T I V E P R O T O C O L . X j Conditions De scription x V 1 + κ n + ( x + 1) µ ≥ j > V 1 + κ n + xµ Phase I: estimate x ’ s interference wi th primary’ s ARQs. ˜ X j − V ℓ − κ n ( m χ ) V 2 + K n ≥ j > V 2 + κ n Phase II: ˜ X K n − κ n ( m χ ) ∈ C fixed for selection C χ . ˜ X j − V ℓ − κ n ( m ℓ ) V ℓ +2 + K n ≥ j > V ℓ +2 + κ n , ℓ ∈ Z + Phase III: ˜ X K n − κ n ( m ℓ ) ∈ C χ to send fragment m ℓ . x rep V ℓ + κ n ≥ j > V ℓ , ℓ ∈ Z + Repetition code: notify decoder of activ e frame x off all other j Silent frame W e n ow state the result for the co debook -adaptiv e protocol. Theorem 2: For all R p , ν > 0 , there exists a cho ice of K n , κ n , C n , γ , ˜ δ such that the codeb ook-adap ti ve protocol is a valid strategy , i.e. the primary’ s p acket ra te sa tisfies the co ndition in (12) for all { ǫ x,i } ∞ i =1 , x ∈ X − { x of f } . Furthermore, when the interference on the primary is time-in variant, i.e. ǫ x,i = ǫ x for x ∈ X − { x of f } , the rate max p ( x ): P x ǫ x p ( x ) ≤ 1 − R p I ( X ; Y ) (34) is ac hiev a ble for the cognitiv e ra dio u nder the s ame pa rameter settings. October 29, 2018 DRAFT 16 Pr oo f: The pa rameters K n , κ n will be set a s in (24 ), C n = √ κ n , an d any γ satisfying 0 < γ < min { ˜ δ / 2 , ν / 2 } . W e will as sume ˜ δ > 0 , but a detailed presc ription is given in L emma 12 below to ge t arbitrarily clos e to the rate in the s tatement of the theorem. The proof of the theorem is divided into three parts. 1) As in the fixed-rate protocol, we can ap ply Lemma 3 since (18) and (26) are identical c onditions. Thus, the primary’ s rate sa tisfies the condition (12), so the strategy is valid. 2) The cogn iti ve radio de coder error probability is small, thus satisfying (13) for some R . (Le mma 7) 3) By appropriately c hoosing ˜ δ , the R in (13) ca n b e made arbitrarily clos e to R IB ( ~ ǫ, R p ) with probability go ing to 1 as n → ∞ . (Lemma 12) W ith the exception o f Lemma 3, these resu lts are proved in the Append ix II. I V . C O N V E R S E T o show the co n verse, we will relax the c onditions stipulated in the p roblem setup, thereb y a llowi ng a lar g er class of strategies. It turns out that in some cas es, this larger class does n ot increase the rate region. Theorem 3: For all ν > 0 and for ǫ x,i = ǫ x for all i , R IB ( ~ ǫ, R p ) ≤ max p ( x ): P x ǫ x p ( x ) ≤ 1 − R p I ( X ; Y ) (35) Pr oo f: Fr om the definition o f ac hiev ab le rate, nR ≤ H ( W ⌊ n ( R − δ ) ⌋ ) − nδ + 1 (36) ≤ I ( W ⌊ n ( R − δ ) ⌋ ; Y n ) + 2 nδ + 1 (37) = n X i =1 H ( Y i | Y i − 1 ) − H ( Y i | Y i − 1 , W ⌊ n ( R − δ ) ⌋ ) + 2 nδ + 1 (38) ≤ n X i =1 H ( Y i ) − H ( Y i | Y i − 1 , W, A i − 1 , X i ) + 2 nδ + 1 (39) = n X i =1 H ( Y i ) − H ( Y i | X i ) + 2 nδ + 1 (40) = n X i =1 I ( X i ; Y i ) + 2 nδ + 1 , (41) where (37) follows from Fano ’ s ineq uality , (38) from the ch ain rule, (39) since conditioning c annot increase entropy , (40) b y the Markov chain ( W, A i − 1 , Y i − 1 , X i − 1 ) ↔ X i ↔ Y i , a nd (41) by de finition. October 29, 2018 DRAFT 17 W e ha ve yet to place a restriction on the strategies. Recall that v alid strategies need to satisfy the condition in (12). If c ondition (12) is s atisfied, then the c ode of blockleng th n sa tisfies n − 1 n X i =1 E [ A i ] ≥ R p − K 1 ,R p ,ν,n e − n · K 2 ,R p ,ν . (42) W e now co nsider only this w eaker condition on the channe l inputs a s oppo sed to the stronger o ne g i ven by (12). By the c oncavity of mutual information with respec t to its input distrib ution, we ca n c ombine (41) an d (42) to yield that for all δ > 0 , there exists large e nough n such that R ≤ max p ( x ): P x ǫ x p ( x ) ≤ 1 − R p + δ I ( X ; Y ) + 3 δ (43) Since δ can b e made arbitrarily small, we ca n conclude the res ult. V . E X A M P L E S Propositions 1 and 2 provide a lower boun d and an exact result for the RIB function under different interference cond itions, resp ectiv ely . In this s ection, w e ev a luate the RIB function given in Propos ition 2 for ca ses in wh ich the interference c haracteristics on the primary are time-in variant. W e then ev aluate the RIB function lower bo und g i ven in Prop osition 1 for these examples when the interference chara cteristics are time-varying. A. Ev aluation of the RIB Fu nction for T ime-In varian t Interference Character istics W e first explore the se tting in which the interference pa rameters ǫ x,i are time-in variant, i.e. ǫ x,i = ǫ x for all i, x . In this setting, Proposition 2 giv es an exact expression for the RIB fun ction R IB ( ~ ǫ, R p ) . W e fi rst evaluate the RIB function for Ex ample 1. W e first rewrite the express ion in Propo sition 2 as R IB ( ~ ǫ, R p ) = max p ( x ): P x ǫ x p ( x ) ≤ 1 − R p I ( X ; Y ) (44) = max p ( x ): p ( x 6 = x off ) ǫ 1 + p ( x = x off ) ǫ 0 ≤ 1 − R p H ( X ) = max p ≤ 1 − R p − ǫ 0 ǫ 1 − ǫ 0 h ( p ) + p log P = log( P + 1) , b ≥ P P +1 h ( b ) + b log P , otherwise , (45) where b = 1 − R p − ǫ 0 ǫ 1 − ǫ 0 . Figure 5 shows (45) in terms of b , wh ich we can think of as a summary of the interference budget. October 29, 2018 DRAFT 18 rate 1 R IB 1 / 2 1 − R p − ǫ 0 ǫ 1 − ǫ 0 interference budget Fig. 5. A schematic plot of t he RIB function for Example 1 when P = 1 . Example 2 : Consider a DMC with |X | = 1 + P chann el inp ut symbols an d |Y | = P o utput s ymbols with the following property: P ( Y = y | X = x ) = 1 , y = x, x ∈ { 1 , . . . , P } 1 P , y ∈ Y , x = x of f . . (46) If ǫ 0 = 0 , ǫ x = 1 for x ∈ { 1 , . . . , P } , the n ev aluating the RIB function from Propos ition 2 y ields R IB ( ~ ǫ, R p ) = (1 − R p ) log 2 P , (47) where the units a re in bits per ch annel use. W e now co nsider a ca se in which the se condary has an alternative to x of f to control interference. Th e channe l mod el resembles the on e in Example 2, excep t there are now ad ditional chan nel inputs. Example 3 : Let P be e ven and consider a DMC with |X | = 1 + 3 P / 2 cha nnel input sy mbols a nd |Y | = P ou tput symbols with the following p roperty: P ( Y = y | X = x ) = 1 , y = x, x ∈ { 1 , . . . , P } 1 P , y ∈ Y , x = x of f 1 2 , y = 2( x − P ) − 1 , x ∈ { P + 1 , . . . , P + P / 2 } 1 2 , y = 2( x − P ) , x ∈ { P + 1 , . . . , P + P / 2 } . (48) An illustration of the se transition proba bilities a re given in Figure 6. W e now cons ider the case in which ǫ 0 = 0 , 0 < R p < 1 , ǫ x = 1 for x ∈ { 1 , . . . , P } , and ǫ x = ǫ 1 / 2 < 1 − R p for x ∈ { P + 1 , . . . , P + P / 2 } . October 29, 2018 DRAFT 19 1 1 6 1 2 1 2 3 3 x of f 2 2 5 1 2 1 2 4 4 1 4 1 4 1 4 1 4 X Y Fig. 6. Illustration of transition probabilities for Example 3 when P = 4 . Under thes e ass umptions, ev alua ting the RIB function from Prop osition 2 yields R IB ( ~ ǫ, R p ) = max p ( x ): P x ǫ x p ( x ) ≤ 1 − R p I ( X ; Y ) (49) = 1 − R p − ǫ 1 / 2 1 − ǫ 1 / 2 log 2 P + R p 1 − ǫ 1 / 2 log 2 ( P / 2) (50) = log 2 P − R p 1 − ǫ 1 / 2 , (51) where the units a re in b its pe r channe l us e. Note that the rate los s due to the p rimary c an be a t most 1 bit in this setting. Moreover , this can be arbitrarily b etter than the cas e in Example 2 by mak ing P large and R p close to 1 , for which the tar get rate R p induced a mu ltiplicati ve penalty on the log 2 P term in (47). B. Fu rther Cons iderations for T ime-V arying Inter fer ence Characteristics The mos t interesting and realistic sc enarios c oncern the case when the interferenc e characteristics are time-v arying. The codebo ok-adap ti ve p rotocol introduce d in Section III c an de al with this as long as it is well be haved. Howe ver , for some “maliciously chose n” time-varying cha racteristics, the proposed startegy ca n be fooled into choo sing a low rate code book in Phase II when the interference c onditions are les s severe in Phase III. The eff ect o f su ch a possibility is illustrated in F igure 7 . One o ption migh t be to conside r a strategy that p eriodically re adapts the code book, which, while poten tially bene ficial, is outside the scop e of this work. Instead, we co nsider the simpler s trategy giv en by the fixed-codebook protocol. October 29, 2018 DRAFT 20 rate 1 R IB 1 / 2 1 − R p − ǫ 0 ǫ 1 − ǫ 0 interference budget Fig. 7. A schematic plot of the RIB function for Example 1 when P = 1 . The dashed line suggests ho w maliciously chosen time-v arying characteristics can cause the encoder to select a “low rate” codeboo k, which saturates well below the actual RIB function when the interference budget is large. For Examp le 1, Proposition 1 implies the fixed-codeb ook protoco l lets the cog niti ve radio ac hieve the rate R IB ( ǫ 0 , { ǫ x,i } ∞ i =1 , R p ) ≥ (1 − R p / (1 − ǫ 0 )) log (1 + P ) (52) for a ll { ǫ x,i } ∞ i =1 , x 6 = x of f . For the re stricted time-i n variant interferenc e s etting of Exa mple 1, can us e b = 1 − R p − ǫ 0 ǫ 1 − ǫ 0 to compare its performance against the RIB function. It turns out that for b > b ∗ , the codebo ok c hosen by the co debook -adaptive protocol has the same asymptotic rate a nd produc es the same interference on the p rimary as that in the fixed-c odeboo k protocol. Thu s, depend ing on one’ s a ssumptions about the interference e n vironmen t, there are instanc es in which the fixed-codeb ook protoco l ma y be preferable to the codeb ook-adap ti ve protocol. Despite these gua rantees, there a re situations in which the fixed-codebo ok protocol ca n be arbitrarily worse. Re call Ex amples 2 an d 3 . It turns out tha t in both ca ses w hen ǫ 0 = 0 , Propo sition 1 implies the fixed-codebo ok protocol gu arantees rates giv en by R IB (0 , { ǫ x,i } ∞ i =1 , R p ) ≥ (1 − R p ) log 2 P , (53) which matche s the RIB function in (47) for E xample 2. Howev er , a s already illustrated, by making P lar ge a nd R p close to 1 , the RIB function in Example 3 , given in (51), can be made arbitraril y lar ger than the one in Exa mple 2. This implies that the loss for applying the fi xed-codeboo k protoco l can be significant. Thus , one’ s choice b etween these two p rotocols dep ends jointly on the c ogniti ve radio’ s October 29, 2018 DRAFT 21 channe l and the interference gene rated on the primary . Indeed, there may exist s trategies that c an trade off the competing desires of optimality an d robustness be tter tha n the one s p roposed. The se a re discuss ed further in the next section. V I . D I S C U S S I O N In this pape r , a novel mod el was propo sed for a co gniti ve rad io problem. The ba sic problem is that the cognitiv e radio must not disturb the primary user (i .e., the license holder). The specific aspect of our model is that the cogn iti ve radio is igno rant of the cha nnel ch aracteristics a ccording to which it interferes with the primary . T o mitigate this unce rtainty , the cognitive radio may e avesdrop on the primary system’ s AR Q feedback s ignal. W e sh ow h ow this can be exploited to design two adap ti ve cog niti ve radio strategies, each of which provides a fixed rate guarantee to the primary and variable rate guarantee to the co gniti ve radio tha t de pends on its interference budget, the amount of interference it is allowed to g enerate on the primary us er . The problem statement an d results provide a starting point for n ew resea rch directions and problems, s ome of wh ich we briefly o utline in the sequ el. A. Ga ussian Chan nels In this work, the cognitiv e radio’ s cha nnel is a DMC with each symbol aff ecting the primary’ s erasure probability . An an alogous mode l an d res ult for the Gau ssian setting would be desirable to gain further intuitions about the d esign o f a cog niti ve radio sys tem. For instance , if the primary employs a Gaus sian codebo ok that assu mes a ce rtain level of interference, the cogn iti ve rad io may use the ARQs to ch oose the h ighest power c odeboo k that maintains tha t level of interference on the primary . B. Pr imary with a F ixed De lay Cons traint In ou r model, the cognitiv e radio must ope rate such that ev entually , the p rimary attains its prespecfi ed tar get rate. A mo re restrictiv e s etting would b e to also e nforce a delay cons traint. That is , the co gniti ve radio must operate such a s to not delay packets by more than a certain prespe cified bou nd. Alternativ ely , this can be formulated as a “s liding window” rate c onstraint: over any w indow of a prespe cified len gth, the primary mu st attain its pre specified rate. It would be interesting to un derstand by how much this lowers the “interference budget” of the cognitive radio, a nd thus , its c apacity . C. Impro ved Strate gies The cog niti ve rad io’ s rate guaran tees for the fixed-co debook protocol are somewhat pessimistic, and the rate guarantee s for the codeb ook-adap ti ve protocol a re restricted to the smaller clas s of time-in variant October 29, 2018 DRAFT 22 interference parameters o n the primary . Th e p roblem is that since the codeb ook-ada pti ve protoco l only selects the codebook once, v arying the interference conditions in the time can lea d to suboptimal performance. For instance , the interference con ditions in Pha se I ca n be suc h that the primary se lects a codebo ok with negligible rate in P hase II only to discover tha t the re is no interference to the p rimary in Pha se III. Thus, its pe rformance ca n be significantly worse than the fixed-codeb ook protocol in the time-v arying setting. An obvious alternati ve would be a strategy that periodically rea dapts the code book, which, if done properly , may be able to provide stronger rate gua rantees than thos e already p rovided in the time-varying setting. On e ma y a lso wish to restrict the set of codebook s s o tha t all codeboo ks have a rate above a certain thresh old. Then , arguments similar to those used for the fixed-codebo ok protocol can provide rate guarantees for the time-varying case , and on e can also exploit the advantage afforded b y adap ting one’ s codebo ok for the time-in variant cas e. D. Multiple Cognitive Ra dios In our mod el, there is on ly a single cog niti ve radio interfering with the primary . A more interes ting situation will inv olve multiple cognitiv e rad ios all c ompeting for the same interferenc e budget. C learly , this significa ntly change s the dynamics of the problem. Are there e f ficient strategies that gi ve g ood rates for the co gniti ve radios wh ile respe cting the primary us er? First of a ll, if all the c ognitiv e radios ha ve acces s to A k with diff erent delays, then the arguments in this work would need to be extended . Th e existence o f multiple u sers also leads to the iss ue that a ny individual cogniti ve radio may n ot cause significant interference to the p rimary by itself, but the aggregate interferenc e from a ll cogn iti ve radios can still be quite lar ge. An other issue to cons ider is how the cog niti ve radios might divide their rate in an equitable way base d not o nly on the ir own cha nnels but also on how much interference ea ch generate s on the primary . E. No isy feedb ack In our mo del, the cog niti ve radio h as a pe rfect observation of the ARQ sign al of the primary , i.e., of the values of A k . Howev er , in practice there may b e no ise that corrupts the e ncode r’ s knowledge o f A k . This ma y also play a cruc ial role for the c ase o f multiple cogn iti ve rad ios, in which the noise may be dif ferent for different terminals in the s ystem. October 29, 2018 DRAFT 23 A C K N O W L E D G M E N T S W e would lik e to ackn owledge comments a nd sug gestions from Anant Sah ai and S ourav Chatterjee (Stat, UC Berkeley). Stimulating discussions with Mubaraq Mishra a re also gratefully acknowledged. This work was supported by the NSF under award CNS-032650 3. A P P E N D I X I P RO O F O F T H E O R E M 1 A. Pr imary Me ets Rate T arget Lemma 1: Le t S k be defi ned as in (17). The seque nce of rando m variables M k = e λS k − k ( f λ ( ǫ 0 ) − λR p ) − P k j =1 τ j ( f λ ( ǫ j, 1 ) − f λ ( ǫ 0 ) , (54) where f λ ( ǫ ) = log ((1 − ǫ ) e λ + ǫ ) and τ k = I { S ⌊ k/K n ⌋ K n − K n −⌊ k/K n ⌋ K n γ ≥ 0 } , forms a ma rtingale. Pr oo f: Fi rst obs erve tha t we can expres s M k in terms of the rec urrence equ ation M k = M k − 1 e λA k − τ k ( f λ ( ǫ k, 1 ) − f λ ( ǫ 0 )) . (55) From this, we find that E [ M k | M 0 , . . . , M k − 1 ] = E [ M k | S 0 , . . . , S k − 1 ] (56) = M k − 1 e − τ k ( f λ ( ǫ k, 1 ) − f λ ( ǫ 0 )) E [ e λA k | S 0 , . . . , S k − 1 ] (57) = M k − 1 . (58) Lemma 2: Le t S k be defi ned as in (17) and r be a positiv e integer and define the stopping time N = r · inf { i > 0 : S ir − ir γ − r ≥ 0 } . (59) Then for R p + γ ≤ 1 − ǫ 0 and s ≤ 0 , P ( N ≥ t | S 0 = s ) ≤ (1 − R p − γ )(1 − ǫ 0 ) ( R p + γ ) ǫ 0 2 r − s e − tD (1 − R p − γ k ǫ 0 ) . (60) Pr oo f: Consider the martingale (se e Lemma 1) M k = e λS k − k ( f λ ( ǫ 0 ) − λR p ) − P k j =1 τ j ( f λ ( ǫ j, 1 ) − f λ ( ǫ 0 ) , (61) where f λ ( ǫ ) = log ((1 − ǫ ) e λ + ǫ ) and τ k = I { S ⌊ k/K n ⌋ K n − K n −⌊ k/K n ⌋ K n γ ≥ 0 } . Th e o ptional s topping the orem [21, T hm. 4.7.4 , p . 2 70] implies e λs = E [ M N ∧ m | S 0 = s ] , (62) October 29, 2018 DRAFT 24 where N ∧ m den otes their minimum. W e can s ubstitute λ = log ( R p + γ ) ǫ 0 (1 − R p − γ )(1 − ǫ 0 ) , which is nonn egati ve by ass umption, into e quation (62) to get that ( R p + γ ) ǫ 0 (1 − R p − γ )(1 − ǫ 0 ) s ≥ ( R p + γ ) ǫ 0 (1 − R p − γ )(1 − ǫ 0 ) 2 r E [ e ( N ∧ m ) D (1 − R p − γ k ǫ 0 ) | S 0 = s ] , (63) where the inequ ality follo ws since S k has bounde d inc rements that are less tha n 1 almost surely a nd the s topping time that inc reases in multiples of r increments . By the mono tone con ver g ence [21, p. 15, Theorem 1 .3.6], letting m → ∞ giv es E [ e N D (1 − R p − γ k ǫ 0 ) | S 0 = s ] ≤ (1 − R p − γ )(1 − ǫ 0 ) ( R p + γ ) ǫ 0 2 r − s . (64) Using this moment ine quality , we can a pply a Chernoff boun d to conclud e P ( N ≥ t | S 0 = s ) ≤ (1 − R p − γ )(1 − ǫ 0 ) ( R p + γ ) ǫ 0 2 r − s e − tD (1 − R p − γ k ǫ 0 ) . (65) Lemma 3: Given a strategy in which for all n , every code of bloc klength n s atisfies (18), if γ > 0 is chosen s o that γ < ν 2 , then the strategy is valid. That is, for all { ǫ k , 1 } ∞ i =1 , P ǫ 0 , { ǫ k, 1 } ∞ i =1 ℓ − 1 ℓ X k =1 A k < R p ! ≤ K 1 ,R p ,ν,ℓ e − ℓK 2 ,R p ,ν , (66) where 0 < K 2 ,R p ,ν < ∞ , K 1 ,R p ,ν,ℓ < ∞ , an d K 1 ,R p ,ν,ℓ e − ℓK 2 ,R p ,ν → 0 a s ℓ → ∞ . Pr oo f: When S ℓ > 0 , the p rimary is me eting its rate target. Furthermore, if S iK n − K n − iK n γ > 0 , then the primary will b e guarantee d to meet its rate tar get over the next p rimary frame. T hus, it s uffices to con sider frames when S iK n − K n − iK n γ ≤ 0 , which co rrespond direc tly to s ilent frames. T o c onsider what happ ens in these settings, we define s topping times to thresh old S ℓ − ℓγ . N 2 k − 1 = in f { ℓ > N 2 k − 2 : S ℓ − ℓγ ≥ 1 } , (67) N 2 k = in f { ℓ > N 2 k − 1 : S ℓ − ℓγ < 1 } . (68) Negati ve deviations occur only when N 2 k ≤ ℓ < N 2 k + 1 , s o P ( S ℓ ≤ 0) ≤ X k P ( − S ℓ + ℓγ ≥ ℓγ | N 2 k ≤ ℓ < N 2 k + 1 ) P ( N 2 k ≤ ℓ < N 2 k + 1 ) (69) ≤ X k P ( N 2 k + 1 − N 2 k ≥ ℓ γ | N 2 k ≤ ℓ < N 2 k + 1 ) P ( N 2 k ≤ ℓ < N 2 k + 1 ) (70) ≤ X k P ( N 2 k + 1 − N 2 k ≥ ℓ γ | N 2 k < ∞ ) P ( N 2 k ≤ ℓ < N 2 k + 1 | N 2 k + 1 − N 2 k ≥ ℓ γ , N 2 k < ∞ ) (71) ≤ ℓ 2 max 1 ≤ 2 k ≤ ℓ P ( N 2 k + 1 − N 2 k ≥ ℓ γ | N 2 k < ∞ ) , (72) October 29, 2018 DRAFT 25 where (69) follows from the law of total prob ability; (70) since the bo unded increments of S ℓ imply that − S ℓ + ℓγ ≤ N 2 k + 1 − N 2 k giv e n N 2 k ≤ ℓ < N 2 k + 1 ; (71) from Baye s theorem and tha t probabilities are bounde d from a bove by 1; an d (72) since prob abilities are bou nded from above by 1 and for N 2 k ≤ ℓ , it is n eces sary for 2 k ≤ ℓ by the defi nition of N 2 k , N 2 k + 1 . Sinc e S n is a Markov chain, then for all k , Lemma 13 implies tha t we only need to cons ider P ( N 2 k + 1 − N 2 k ≥ ℓ γ | N 2 k < ∞ ) ≤ max s ∈ [ − 1 , 0] P ( N 1 ≥ ℓ γ | S 0 = s ) . (73) ≤ (1 − R p − γ )(1 − ǫ 0 ) ( R p + γ ) ǫ 0 2 e − ℓD (1 − R p − γ k ǫ 0 ) (74) where (74) follows from Lemma 2. Since the above holds for all k , substituting it into (72) gives P ( S ℓ ≤ 0) ≤ ℓ 2 (1 − R p − γ )(1 − ǫ 0 ) ( R p + γ ) ǫ 0 2 e − ℓD (1 − R p − γ k ǫ 0 ) (75) = ℓ 2 · exp 2 1 − R p − γ · D (1 − R p − γ k ǫ 0 ) − log R p + γ 1 − ǫ 0 − ℓD (1 − R p − γ k ǫ 0 ) (76) = ℓ 2 · exp − 2 1 − R p − γ · log R p + γ 1 − ǫ 0 − ( ℓ − 2 / (1 − R p − γ )) D (1 − R p − γ k ǫ 0 ) (77) ≤ ℓ 2 · exp − 2 1 − R p − γ · log R p + γ R p + ν − ( ℓ − 2 / (1 − R p − γ )) D (1 − R p − γ k ǫ 0 ) , (78) where the last line follows sinc e 1 − ǫ 0 ≥ R p + ν . For ℓ > 2 / (1 − R p − γ ) , we use the fact that D (1 − R p − γ k ǫ 0 ) ≥ (1 − R p − γ − ǫ 0 ) 2 2 to ge t that P ( S ℓ ≤ 0) ≤ ℓ 2 · exp − 2 1 − R p − γ · log R p + γ R p + ν − ( ℓ − 2 / (1 − R p − γ )) (1 − R p − γ − ǫ 0 ) 2 2 (79) ≤ ℓ 2 · exp − 2 1 − R p − γ · log R p + γ R p + ν − ( ℓ − 2 / (1 − R p − γ )) ν 2 8 , (80) where the last line follo ws by assumption. Note that this expression goes to 0 as ℓ → ∞ . By letting K 2 ,R p ,ν = ν 2 8 , and K 1 ,R p ,ν,ℓ to be (80) d i vided by e − ℓK 2 ,R p ,ν for ℓ > 2 / (1 − R p − γ ) , then we ca n write P ( S ℓ ≤ 0) ≤ K 1 ,R p ,ν,ℓ e − ℓK 2 ,R p ,ν . (81) For ℓ ≤ 2 / (1 − R p − γ ) , we simply c hoose K 1 ,R p ,ν,ℓ to make the probability uppe r bound 1 . The n we can c onclude our result by simply recalling the defin ition of S ℓ in (17). October 29, 2018 DRAFT 26 B. De coder Er r or Lemma 4: De fine error events as follows: 1) E 1 : ∃ frame in which the d ecode r misiden tifies it as a cti ve or silent. 2) E 2 : ∃ frame in which the d ecode r misiden tifies the codeword. Then, for ˜ δ > 0 , κ n = ⌊ n 1 / 16 ⌋ , K n = ⌊ n 1 / 8 ⌋ in the fixed-codebo ok p rotocol, as n → ∞ , P ( E 1 ∪ E 2 ) → 0 . (82) Pr oo f: Note that we can bound the error a s P ( E 1 ∪ E 2 ) ≤ P ( E 1 ) + P ( E 2 | E c 1 ) . (83) First c onsider the event of misiden tifying whether trans mission is tak ing p lace over a frame. There are n K n frames, and a n e rror o ccurs if miside nification ha ppens over any o ne o f them. Th us, by taking a union bound over all frames and applying Lemma 15 for the error of the repetition c ode used to distinguish these frames , the e rror prob ability is bound ed by P ( E 1 ) ≤ n K n e − κ n · r , (84) where r > 0 is indepe ndent of n . Finally , we can conside r the error correspon ding to miside ntifying the cod ew ords se nt in eac h frame. By L emma 14 and a union bound per frame, we also also have that P ( E 2 | E c 1 ) ≤ n K n · e − ( K n − κ n ) ˜ δ 2 8 /e 2 +4(log |Y | ) 2 . (85) Combining (84) and (85) with (83), we c omplete the proof. C. Ra te An alysis The rate achievable by the co gniti ve radio is directly proportional to the fraction of frames in wh ich it is activ e. Thu s, we con sider a boun d on the n umber of frames the primary is guarantee d to be a cti ve. Lemma 5: For all δ > 0 and γ < δ / 2 , the re exists an n 0 ( δ ) su ch that for n ≥ n 0 ( δ ) , P n − 1 n X k =1 τ k ≤ 1 − R p − ǫ 0 1 − ǫ 0 − δ ! ≤ exp − nD 1 + δ / 2 2 − n − 1 K n 1 2 , (86) where τ k is an indicator random variable to denote that k is in a n a cti ve frame. Tha t is, τ k = I {∃ ℓ ∈ Z + such that V ℓ 0 , ǫ 0 , { ǫ 1 ,k } ∞ k =1 , co nsider the fixed-rate protocol with κ n = o ( K n ) , K n = o ( n ) , K n → ∞ as n → ∞ , and γ < ˜ δ / 2 . Then there exists a choice of ˜ δ s uch that this strategy a ttains rates of at lea st 1 − R p 1 − ǫ 0 · C ∗ − δ , (93) with proba bility going to 1 as n → ∞ , where C ∗ = m ax p ( x ) I ( X ; Y ) . October 29, 2018 DRAFT 28 Pr oo f: By Lemma 5, we kn ow that with prob ability going to 1 as n → ∞ , at least 1 − R p − ǫ 0 1 − ǫ 0 − ˜ δ n (94) of the frames will be active frames. The rate for each activ e frame is K n − κ n K n ( C ∗ − ˜ δ ) , (95) so we have that 1 − R p − ǫ 0 1 − ǫ 0 − ˜ δ · K n − κ n K n ( C ∗ − ˜ δ ) ≥ 1 − R p − ǫ 0 1 − ǫ 0 C ∗ − ˜ δ − ( κ n /K n + ˜ δ ) · C ∗ . (96) For large e nough n, by assump tion κ n /K n ≤ ˜ δ /C ∗ , s o that rates of at least 1 − R p − ǫ 0 1 − ǫ 0 C ∗ − 2 ˜ δ − ˜ δ · C ∗ (97) are achievable with probab ility going to 1 . By cho osing ˜ δ = 1 3 min { δ , δ /C ∗ } , we can conclud e the result. A P P E N D I X I I P RO O F O F T H E O R E M 2 A. De coder Er r or Lemma 7: De fine error events as follows: 1) E 1 : ∃ frame in which the d ecode r misiden tifies whethe r a frame is a ctiv e or silent. 2) E 2 : the dec oder misidentifies the selected c odeboo k. 3) E 3 : ∃ an activ e frame in which d ecode r misiden tifies the codeword. Then, for ˜ δ > 0 , C n = ⌊ n 1 / 32 ⌋ , κ n = ⌊ n 1 / 16 ⌋ , K n = ⌊ n 1 / 8 ⌋ in the co debook -adaptiv e protoco l, as n → ∞ , P ( E 1 ∪ E 2 ∪ E 3 ) → 0 . (98) Pr oo f: Note that we can bound the error a s P ( E 1 ∪ E 2 ∪ E 3 ) ≤ P ( E 1 ) + P ( E 2 | E c 1 ) + P ( E 3 | E c 1 , E c 2 ) . (99) First c onsider the event of misiden tifying whether trans mission is tak ing p lace over a frame. There are n K n frames, and a n e rror o ccurs if miside nification ha ppens over any o ne o f them. Th us, by taking a union October 29, 2018 DRAFT 29 bound over all frames and applying Lemma 15 for the error of the repetition c ode used to distinguish these frames , the e rror prob ability is bound ed by P ( E 1 ) ≤ n K n e − κ n · r , (100) where r > 0 is inde pende nt of n . Another source of error is misidentifying the code book. For large enough n , ( C n + 1) |X | does not exceed C − δ , and we can ap ply Lemma 14 to get the error probab ility P ( E 2 | E c 1 ) ≤ e − ( K n − κ n ) · ˜ δ 2 8 /e 2 +4(log |Y | ) 2 . (101) Finally , we can con sider the error corresp onding to misidentifying the c odewords s ent in eac h frame. By Lemma 14 and a u nion bou nd per frame, we also a lso have that P ( E 3 | E c 2 , E c 1 ) ≤ n K n · e − ( K n − κ n ) ˜ δ 2 8 /e 2 +4(log |Y | ) 2 . (102) Combining (100), (101), a nd (102) with (99), we co mplete the p roof. B. Ra te An alysis The rate loss argument is the most ted ious becaus e one must ac count for a v ariety o f f actors: the length of the first two ph ases of trans mission, the gap be tween the rates of qu antized set of c odebo oks and points on the RIB func tion, and the nu mber o f active frames in Phase III. W e therefore su bdivide the res ult into several lemma s. 1) Phase I and II are sh ort: Becau se the enco der does not send mes sage information in Pha se I an d II, we want the length of the se phas es to b e sub linear in n to guarantee negligible rate loss . Lemma 8: For a ll ν > 0 , let γ < ν / 2 , κ n = ⌊ n 1 / 16 ⌋ , K n = ⌊ n 1 / 8 ⌋ in the c odeboo k-adaptive protocol. Furthermore, let T be the length of Phas es I a nd II and ˜ E 1 = { T ≥ n 1 / 4 } . Then P ( ˜ E 1 ) → 0 (103) as n → ∞ . Pr oo f: Consider the transition times from s ilent frames to ac ti ve frames and vice versa. T o do this, define the stopp ing times for k ≥ 1 , ˜ N 2 k − 1 = K n · inf { i > K − 1 n ˜ N 2 k − 2 : S i · K n − i · K n · γ − K n ≥ 0 } , (104) ˜ N 2 k = K n · inf { i > K − 1 n ˜ N 2 k − 1 : S i · K n − i · K n · γ − K n < 0 } , (105) October 29, 2018 DRAFT 30 where ˜ N 0 = 0 . Phases I and II end after the first two ac ti ve frames. W e can get a bou nd on the start of the fi rst active frame immediately from Lemma 2, which implies P ( ˜ N 1 ≥ t | S 0 = 0) ≤ (1 − R p − γ )(1 − ǫ 0 ) ( R p + γ ) ǫ 0 2 K n e − tD (1 − R p − γ k ǫ 0 ) . (106) Thus, if ˜ N 2 > ˜ N 1 + K n , then T = ˜ N 1 + 2 K n . (107) T ogether with (106), this implies P ( T ≥ n 1 / 4 | ˜ N 2 > ˜ N 1 + K n ) ≤ (1 − R p − γ )(1 − ǫ 0 ) ( R p + γ ) ǫ 0 2 K n e − ( n 1 / 4 − K n ) · D (1 − R p − γ k ǫ 0 ) (108) The remaining case to con sider is if ˜ N 2 = ˜ N 1 + K n . If this ha ppens , then Pha ses I a nd II end a t T = ˜ N 3 + K n . (109) Then (109 ) implies P ( T ≥ n 1 / 4 | ˜ N 2 = ˜ N 1 + K n ) = P ( ˜ N 3 ≥ n 1 / 4 − K n | ˜ N 2 = ˜ N 1 + K n ) (110) = P ( ˜ N 3 − ˜ N 2 ≥ n 1 / 4 − 2 K n − ˜ N 1 | ˜ N 2 = ˜ N 1 + K n ) (111) ≤ P ( ˜ N 3 − ˜ N 2 ≥ n 1 / 4 − 2 K n − ˜ N 1 or ˜ N 1 ≥ n 1 / 4 / 2 | ˜ N 2 = ˜ N 1 + K n ) (112) ≤ P ( ˜ N 1 ≥ n 1 / 4 / 2 | ˜ N 2 = ˜ N 1 + K n ) + P ( ˜ N 3 − ˜ N 2 ≥ n 1 / 4 / 2 − 2 K n | ˜ N 2 = ˜ N 1 + K n , ˜ N 1 < n 1 / 4 / 2) , (113) where (110) follo ws from (109), (111) follows b y our conditioning, (112) follows s ince we are increasing the possible events over which we a re taking the proba bility , an d (113) follo ws from P ( A or B ) = P ( A ) + P ( A c ) P ( B | A c ) . By L emma 13 and L emma 2, P ( ˜ N 3 − ˜ N 2 ≥ n 1 / 4 / 2 − 2 K n | ˜ N 2 = ˜ N 1 + K n , ˜ N 1 < n 1 / 4 / 2) ≤ (1 − R p − γ )(1 − ǫ 0 ) ( R p + γ ) ǫ 0 2 K n e − ( n 1 / 4 / 2 − 2 K n ) · D (1 − R p − γ k ǫ 0 ) . (114) October 29, 2018 DRAFT 31 By c ombining (106), and (11 3), and (114), P ( T ≥ n 1 / 4 | ˜ N 2 = ˜ N 1 + K n ) ≤ (1 − R p − γ )(1 − ǫ 0 ) ( R p + γ ) ǫ 0 2 K n e − ( n 1 / 4 / 2 − 2 K n ) · D (1 − R p − γ k ǫ 0 ) + (1 − R p − γ )(1 − ǫ 0 ) ( R p + γ ) ǫ 0 2 K n e − n 1 / 4 2 D (1 − R p − γ k ǫ 0 ) . (115) The resu lt follows immediately from (108) a nd (115). 2) Codeboo k Quantization: T o ac count for the error in the interference estimates a nd tha t the e ncode r must inform the de coder of which rate it will be tar getting, we only h av e a limited n umber o f c odeboo ks to cho ose from a t the start of Phase II. Thus, in gene ral there will be a gap between the rate of a selected codebo ok an d an actual po int on the RIB function. In this sub section, we ensure that this g ap is s mall. W e fi rst provide guaran tees on a ccurate interference estimates. Lemma 9: Le t D ℓ be the event that Phase I of the code book-ada pti ve protoc ol terminates at frame ℓ . Then P (max x | ˆ ǫ x − ǫ x | > δ |D ℓ ) ≤ 2 |X | e − µδ 2 / 2 , (116) where µ = ⌊ K n − κ n |X | ⌋ . Pr oo f: Recall the definition of the estimates given in (29). T hen D ℓ = { V 1 = ( ℓ − 1) K n } is a n equiv a lent expression for the event. By Hoeffding’ s inequ ality [22, p. 57 , Co rollary 2.4.7], we have for each x ∈ X P ( | ˆ ǫ x − ǫ x | > δ | V 1 = ( ℓ − 1) K n ) ≤ 2 e − µδ 2 / 2 . (117) The resu lt then follo ws from a union b ound on P (max x | ˆ ǫ x − ǫ x | > δ |D ℓ ) . Lemma 10 : For the s elected c odebo ok χ gi ven in (31), define ˜ E c 2 as the event wh ere the follo wing two conditions are met: X x ǫ x p χ ( x ) ≤ 1 − R p − 2 γ (118) 6 |X | C n log 2 C n · |Y | + 3 ˜ δ 2 |X | log ˜ δ 2 |X | 2 · |Y | ≤ R χ − R IB ( ~ ǫ, R p + 2 γ + ˜ δ ) ≤ (119) − 3 ˜ δ 2 |X | log ˜ δ 2 |X | 2 · |Y | . October 29, 2018 DRAFT 32 Then for all 1 > ˜ δ > 0 , C n ≥ 4 |X | , and a s n → ∞ , P ( ˜ E 2 | ˜ E c 1 ) → 0 , (120) where ˜ E 1 is define d in Le mma 8. Pr oo f: Gi ven ˜ E c 1 , we ca n guarantee by s etting δ = ˜ δ 4 |X | in Lemma 9 that X x | ˆ ǫ x − ǫ x | ≤ ˜ δ 4 (121) with proba bility going to 1 as n → ∞ . Furthermore, we kn ow that by de finition X x ˆ ǫ x p χ ( x ) ≤ 1 − R p − 2 γ − ˜ δ (122) From (121 ) and (122 ), we have that X x ǫ x p χ ( x ) ≤ X x ˆ ǫ x p χ ( x ) + ˜ δ (123) ≤ 1 − R p − 2 γ . (124) It remains to verify the other c ondition. Note tha t for a ny p ( x ) , there is a cod ebook in the se t with input distrib ution type p x C n ( x ) suc h tha t P x | p ( x ) − p x C n ( x ) | ≤ |X | C n . The n by the continuity o f entropy [23, Lemma 2.7 , p. 3 3], we know that R IB ( ~ ˆ ǫ, R p + 2 γ + ˜ δ ) + 6 |X | C n log 2 C n · |Y | ≤ R χ ≤ R IB ( ~ ˆ ǫ, R p + 2 γ + ˜ δ ) , (125) where the inequ ality on the right follows from (122) an d the d efinition of the R IB function. Lemma 18 and (121 ) imply that | R IB ( ~ ǫ, R p + 2 γ + ˜ δ ) − R IB ( ~ ˆ ǫ, R p + 2 γ + ˜ δ ) | ≤ − 3 ˜ δ 2 |X | log ˜ δ 2 |X | 2 · |Y | . (126) Combining (125) and (126) yield the result. 3) Always On: Our next lemma shows that all frames are active after time √ n with probability go ing to 1 as n → ∞ . Lemma 11 : Let ˜ E 1 and ˜ E 2 be d efined as in Lemmas 8 and 10, respec ti vely . Define ˜ E 3 to b e the event that for some j > √ n , the condition in (26) is met, resulting in a silent frame. Then for all ν > 0 and ǫ x,i = ǫ x for x 6 = x of f , the codeb ook-adap ti ve protoc ol with pa rameters ( γ , C n , κ n , K n , ˜ δ ) s atisfying 0 < γ < ν / 2 , C n = ⌊ n 1 / 32 ⌋ , κ n = ⌊ n 1 / 16 ⌋ , K n = ⌊ n 1 / 8 ⌋ , 1 > ˜ δ > 0 , has the property that as n → ∞ , P ( ˜ E 3 | ˜ E c 1 , ˜ E c 2 ) → 0 . (127) October 29, 2018 DRAFT 33 Pr oo f: W e start by defining ˜ S j = ˜ S j − 1 + A j − E [ A j | ˜ S 0 , . . . , ˜ S j − 1 ] , ˜ S 0 = 0 , (128) and it is easy to verify that ˜ S j is a boun ded martingale. From the d efinition of ˜ E c 2 in Le mma 10 and for ν > 0 , (118), (26), and (33) imply that for j sa tisfying j > V 2 + K n and ℓK n ≥ j > ( ℓ − 1) K n + κ n for some integer ℓ ≥ 1 , E [ A j | ˜ S 0 , . . . , ˜ S j − 1 ] ≥ R p + 2 γ . (129) Then for k ≥ n 1 / 2 and un der ˜ E c 1 , P k − 1 k X i =1 A i < R p + γ + k − 1 K n ˜ E c 1 , ˜ E c 2 ! ≤ P k − 1 ˜ S k < R p + γ + k − 1 K n − k − 1 β k ,n ( R p + 2 γ ) ˜ E c 1 , ˜ E c 2 ! (130) ≤ P k − 1 ˜ S k < − γ + o (1) ˜ E c 1 , ˜ E c 2 ! , (131) where β k ,n = ( k − n 1 / 4 ) · K n − κ n K n , o (1) is notational c on venien ce for lim n →∞ o (1) = 0 , and (130 ) follo ws from (128), (129), an d s ince for all i , A i ≥ 0 almost surely . Since ˜ S k is a z ero-mean b ounded martingale, for k ≥ n 1 / 2 and large enough n , we can ap ply a bounde d martingale c oncentration ine quality [22, p. 57, Corollary 2.4.7] to yield P k − 1 k X i =1 A k < R p + γ + K n ˜ E c 1 , ˜ E c 2 ! ≤ exp − k ( γ + o (1)) 2 / 2 (132) = exp −⌈ √ n ⌉ ( γ + o (1)) 2 / 2 · exp − ( k − ⌈ √ n ⌉ )( γ + o (1)) 2 / 2 (133) From the above res ult an d a u nion bou nd, P ( ˜ E 3 | ˜ E c 1 , ˜ E c 2 ) ≤ exp −⌈ √ n ⌉ ( γ + o (1)) 2 / 2 · n X k = ⌈ √ n ⌉ exp − ( k − ⌈ √ n ⌉ )( γ + o (1)) 2 / 2 (134) ≤ exp −⌈ √ n ⌉ ( γ + o (1)) 2 / 2 · ∞ X m =0 exp − m ( γ + o (1)) 2 / 2 (135) Howe ver , the geome tric series does not a ff ect the error p robability by more than a c onstant asymp totically , so taking the limit a bove completes the resu lt. October 29, 2018 DRAFT 34 4) Overall Rate Lo ss: Lemma 12 : For all ν > 0 , ǫ x,i = ǫ x for x 6 = x of f and given any δ > 0 , cons ider the co debook -adaptiv e protocol with p arameters ( γ , C n , κ n , K n ) satisfying 0 < γ < min { ν / 2 , ˜ δ / 2 } , C n = ⌊ n 1 / 32 ⌋ , κ n = ⌊ n 1 / 16 ⌋ , K n = ⌊ n 1 / 8 ⌋ . The n the re exists a c hoice o f the p arameter ˜ δ ∈ (0 , 1 / 8) s o tha t with proba bility going to 1 as n → ∞ , the cog niti ve radio ach iev es rates R ≥ R IB ( ~ ǫ, R p ) − δ . (136) Pr oo f: Let ˜ E 1 , ˜ E 2 , ˜ E 3 be defined as in Lemmas 8, 10 , and 11 resp ectiv ely . From these resu lts, we know tha t P ( ˜ E 1 ∪ ˜ E 2 ∪ ˜ E 3 ) → 0 (137) as n → ∞ an d thus with high proba bility , 1) Phases I and II a re short, ending by n 1 / 4 (Lemma 8). 2) The ga p betwee n the code book’ s rate an d the RIB fun ction is small (Le mma 10). 3) After time n 1 / 2 , a ll frames a re ac ti ve frames (Lemma 11). Furthermore, we know that b y our repetition co de, there is a loss of κ n positions for our repetition code over a frame K n . Factoring in this source of rate los s along with the f act that we are in Phas e III by time n 1 / 2 (Lemma 8) and a lways in an activ e frame (Lemma 11 ), the rate n − √ n n · K n − κ n K n ( R χ − ˜ δ ) ≥ ( R χ − ˜ δ ) − n − 1 / 2 + κ n K n log |X | (138) is achievable for the cogn iti ve rad io with probability going to 1 a s n → ∞ . Finally , we k now that the gap between the co debook ’ s rate and the RIB function is sma ll (Lemma 1 0), s o R χ ≥ R IB ( ~ ǫ, R p + 2 γ + ˜ δ ) + 6 |X | C n log 2 C n · |Y | + 3 ˜ δ 2 |X | log ˜ δ 2 |X | 2 · |Y | (139) ≥ R IB ( ~ ǫ, R p + 2 ˜ δ ) + 6 |X | C n log 2 C n · |Y | + 3 ˜ δ 2 |X | log ˜ δ 2 |X | 2 · |Y | , (140) ≥ R IB ( ~ ǫ, R p ) + 6 |X | C n log 2 C n · |Y | + 3 ˜ δ 2 |X | log ˜ δ 2 |X | 2 · |Y | + 12 ˜ δ log 4 ˜ δ |X | · |Y | , (141) where (140) follows by ou r as sumption a bout γ and (141) from Lemma 17 given our as sumption about ˜ δ . Combining (138) w ith (14 1), our assu mptions about ( C n , κ n , K n ) imply that for large enoug h n , the rate R IB ( ~ ǫ, R p ) − δ 2 − ˜ δ + 3 ˜ δ 2 |X | log 2 |X | 2 · |Y | ˜ δ + 12 ˜ δ log |X | · |Y | 4 ˜ δ ! (142) October 29, 2018 DRAFT 35 is achiev able for the cognitiv e radio with probability going to 1 as n → ∞ . One can now o bserve tha t the parenthetical te rm in (142 ) vanishes a s ˜ δ goe s to 0 , so choosing ˜ δ ∈ (0 , 1 / 8) su ch tha t this parenthe tical term is less tha n δ 2 completes the p roof. A P P E N D I X I I I T E C H N I C A L L E M M A S This appe ndix c ontains a series of se lf-contained technical lemmas that are included here for com- pleteness . It is likely that many o f them exist elsewhere in the literature, but we were una ble to find the references. A. A Markov Pr operty Lemma 13 : Let A j be i.i.d. Bernoulli- p ran dom variables such that p ∈ (0 , 1) . Define stopping times ˜ N 2 k − 1 = r · inf { i > r − 1 ˜ N 2 k − 2 : i X j =1 A i − i · q ≥ τ } , ( 143) ˜ N 2 k = r · inf { i > r − 1 ˜ N 2 k − 1 : i X j =1 A i − i · q < τ } , ( 144) where ˜ N 0 = 0 . Then for a ll real τ , q an d integers r , an d on the event { ˜ N 2 k < ∞ } , P ( ˜ N 2 k + 1 − ˜ N 2 k > ℓ · r | ˜ N 2 k < ∞ ) = P ( ˜ N 1 ≥ ℓ · r | τ − ( q + 1) · r ≤ ˜ S 0 < τ ) . (145 ) Pr oo f: De fine ˜ S i = P i j =1 A i − i · q · r and note that it is Markov . P ( ˜ N 2 k + 1 − ˜ N 2 k > ℓ · r | ˜ N 2 k < ∞ ) = P ( ˜ S ˜ N 2 k +1 < τ | τ − ( q + 1) · r ≤ ˜ S ˜ N 2 k < τ , ˜ N 2 k < ∞ ) ℓ · r − 1 Y m =1 P ( ˜ S ˜ N 2 k + m +1 < τ | ˜ S ˜ N 2 k + m < τ , ˜ N 2 k < ∞ ) (146) = P ( ˜ S 1 < τ | τ − ( q + 1) · r ≤ ˜ S 0 < τ , ˜ N 2 k < ∞ ) ℓ · r − 1 Y m =1 P ( ˜ S m +1 < τ | ˜ S m < τ ) (147) = P ( ˜ N 1 ≥ ℓ · r | τ − ( q + 1) · r ≤ ˜ S 0 < τ ) (148) where (146) follo ws from the definition o f the s topping times an d the fact that ˜ S i is Markov , (147) from the strong Markov property [21, p. 285, Theo rem 5.2.4], and (148) by the de finition of the s topping time. October 29, 2018 DRAFT 36 B. Hy pothesis T esting a nd Cod ebook Err ors Lemma 14 : Let C be a rando m cod ebook for the DMC p Y | X ( y | x ) with 2 nR codewords whe re the codewords are g enerated inde penden tly acco rding to the distribution p X ℓ ( x n ) = ℓ Y i =1 p X ( x i ) . (149) Let C = I ( X ; Y ) . If ma ximum likelihood decod ing is use d a t the deco der , then for R < C , the e rror probability P error is bo unded from above b y P ( W 6 = ˆ W ) ≤ e − ℓ ( C − R ) 2 8 /e 2 +4(log |Y | ) 2 . (150) Pr oo f: T he resu lt is based o n an exercise in Gallager’ s bo ok [24, p. 539, Prob lem 5. 23], which in turn deriv e s from a result in that text [24, p . 1 38, Theorem 5.6.2]. While the re is a n error in the deriv ation outlined in that exercise, a corrected p roof is g i ven in [25]. Lemma 15 : Let p 1 ( y ) and p 2 ( y ) be two probability distributions s uch tha t p 1 ( y ) 6 = p 2 ( y ) for a t least one y ∈ Y . Given ℓ samp les of o ne of these distrib utions, then there exists a (random) hypo thesis test T such that P ( T ( Y ℓ ) 6 = i | Y ℓ selected iid from p i ) ≤ e − ℓ · r (151) where r > 0 is some cons tant. Pr oo f: The following is simply a variation on Stein’ s lemma. W e will construct a randomized hypothes is test that g i ves this performance. For e ach sample , inde pende ntly choo se with prob ability λ ∈ (0 , 1) a symb ol un iformly over the alphab et; with proba bility 1 − λ , choos e the s ample. Th is generates a new s equen ce o f indep endent random variables ˜ Y i with distrib ution ˜ p i ( y ) = (1 − λ ) p i ( y ) + λ |Y | . (15 2) Note that our a ssumptions imply that ˜ p 1 ( y ) 6 = ˜ p 2 ( y ) for at lea st one y ∈ Y , and thus D ( ˜ p 1 k ˜ p 2 ) > 0 ,D ( ˜ p 2 k ˜ p 1 ) > 0 . (153) Now obs erve tha t log ˜ p 2 ( y ) ˜ p 1 ( y ) ≤ log |Y | λ , (154) log ˜ p 1 ( y ) ˜ p 2 ( y ) ≤ log |Y | λ . (155) October 29, 2018 DRAFT 37 Using this, we c onstruct the rando m hypothe sis test T as follows. Let Z i = 1 log |Y | λ · log ˜ p 1 ( ˜ Y i ) ˜ p 1 ( ˜ Y i ) . (156) W e now define our hypo thesis tes t to be T ( Y ℓ ) = 1 P ℓ i =1 Z i ≥ 0 2 otherwise . (157) If P ℓ i =1 Z i ≥ 0 , T ma ps to 1 . Othe rwise, it map s to 2 . Whe n distribution 2 is the true one, we express the e rror probab ility as P ( ℓ X i =1 Z i ≥ 0 | se lected from p 2 ) = P ( ℓ − 1 ℓ X i =1 Z i + D ( ˜ p 2 k ˜ p 1 ) ≥ D ( ˜ p 2 k ˜ p 1 ) | selected from p 2 ) . (158) By Ho eff ding’ s inequality [22, p. 57, Corollary 2.4 .7], we c an bo und this p robability by P ( ℓ − 1 ℓ X i =1 Z i + D ( ˜ p 2 k ˜ p 1 ) ≥ D ( ˜ p 2 k ˜ p 1 ) | selected from p 2 ) ≤ e − ℓ „ D ( ˜ p 2 k ˜ p 1 ) log |Y | λ « 2 / 2 . (159) By a similar argument, one c an also s how that P ( ℓ − 1 ℓ X i =1 Z i − D ( ˜ p 1 k ˜ p 2 ) ≤ − D ( ˜ p 1 k ˜ p 2 ) | selected from p 1 ) ≤ e − ℓ „ D ( ˜ p 1 k ˜ p 2 ) log |Y | λ « 2 / 2 . (160) Setting r = 1 2 min D ( ˜ p 1 k ˜ p 2 ) log |Y | λ , D ( ˜ p 2 k ˜ p 1 ) log |Y | λ 2 completes the proof. C. Mon otonicity , Conc avity , and Con tinuity of a Cost-Constrained Capacity Lemma 16 : Let 0 ≤ ǫ x ≤ 1 for all x a nd defi ne ǫ 0 = min x ǫ x , which is a chieved u niquely by so me x . Th en C ( ~ ǫ, λ ) = max p ( x ): P x ǫ x p ( x ) ≤ λ I ( X ; Y ) , (161) is no ndecrea sing conc av e in λ o n the interval [ ǫ 0 , 1] . Pr oo f: Since increasing λ increas es the s et of cha nnel inp ut dis trib u tions over which to maximize, it is clea r tha t C ( ~ ǫ , λ ) is non decreas ing. As a c on venien t s horthand, let I p = I ( X ; Y ) d enote the mutual information with the inpu t distrib ution p . Let p 1 be the maximizing input distrib ution for C ( ~ ǫ, λ 1 ) and p 2 the maximizing inp ut distributi on for C ( ~ ǫ, λ 2 ) , both of wh ich are gua ranteed to exist for λ i ∈ [ ǫ 0 , 1] , i ∈ { 1 , 2 } . Th en (1 − ρ ) C ( ~ ǫ, λ 1 ) + ρC ( ~ ǫ, λ 2 ) = (1 − ρ ) I p 1 + ρI p 2 (162) ≤ I (1 − ρ ) p 1 + ρp 2 , (163) ≤ C ( ~ ǫ, (1 − ρ ) λ 1 − ρλ 2 ) , (164) October 29, 2018 DRAFT 38 where (163) follows from the con cavity of mutual information with respec t to its inp ut distribution a nd (164) by definition. Thus, the function is co ncave. Lemma 17 : Let 0 ≤ ǫ x ≤ 1 for all x a nd defi ne ǫ 0 = min x ǫ x , which is a chieved u niquely by so me x . Co nsider C ( ~ ǫ, λ ) = max p ( x ): P x ǫ x p ( x ) ≤ λ I ( X ; Y ) , (165) where λ ∈ [ ǫ 0 , 1] and C ( ~ ǫ, λ ) = 0 for λ < ǫ 0 . Th en for 0 < ∆ ≤ 1 4 , 0 ≤ C ( ~ ǫ, λ + ∆) − C ( ~ ǫ, λ ) ≤ − 6∆ log 2∆ |X | · |Y | . (166) Pr oo f: The lower bound follows immediate ly from L emma 16. For the uppe r b ound, note that C ( ~ ǫ, ǫ 0 ) = 0 s ince the c onstraint can only be met by ap plying a ll the probability to a s ingle choice of x . Let λ ≥ ǫ 0 . Let p 1 ( x ) be the maximizing input distrib ution for C ( ~ ǫ, λ + ∆) . If p 1 ( x ) is found in the s et of valid inp ut distributions for C ( ~ ǫ, λ ) , then C ( ~ ǫ, λ + ∆) = C ( ~ ǫ, λ ) . Otherwise , we can de fine p 2 ( x ) = P x ǫ x p 2 ( x ) = λ and observe that λ ≤ X x ǫ x p 1 ( x ) ≤ λ + ∆ , (167) which implies that 0 ≤ X x ǫ x ( p 1 ( x ) − p 2 ( x )) ≤ ∆ (168) 0 ≤ X x (1 − ǫ x )( p 2 ( x ) − p 1 ( x )) ≤ ∆ . (169) Thus, X x | p 2 ( x ) − p 1 ( x ) | = X x ǫ x | p 2 ( x ) − p 1 ( x ) | + X x (1 − ǫ x ) | p 2 ( x ) − p 1 ( x ) | (170) ≤ 2∆ (171) Let I p = I ( X ; Y ) when the inp ut distribution for X is p . Then by the continuity of e ntropy [23, L emma 2.7, p. 33], C ( ~ ǫ, λ + ∆) = I p 1 (172) = I p 2 + ( I p 1 − I p 2 ) (173) ≤ C ( ~ ǫ, λ ) − 3 · 2∆ log 2∆ |X | · |Y | (174) This is still valid as an upper b ound for λ < ǫ 0 becaus e of the mon otonicity of C ( ~ ǫ, λ ) from Lemma 16 . October 29, 2018 DRAFT 39 Lemma 18 : Let 0 ≤ ǫ x ≤ 1 for all x a nd defi ne ǫ 0 = min x ǫ x , which is a chieved u niquely by so me x , s o ǫ 0 < ǫ 1 = m ax x ǫ x . Con sider C ( ~ ǫ, λ ) = max p ( x ): P x ǫ x p ( x ) ≤ λ I ( X ; Y ) , (175) where λ ∈ [ ǫ 0 , 1] and C ( ~ ǫ, λ ) = 0 for λ < ǫ 0 . Fu rthermore, X x | ǫ x − ˜ ǫ x | ≤ ∆ ≤ 1 4 . (176) Then | C ( ~ ǫ, λ ) − C ( ~ ˜ ǫ, λ ) | ≤ − 6∆ log 2∆ |X | · |Y | . (17 7) Pr oo f: T he co nstraint on p ( x ) in C ( ~ ˜ ǫ, λ ) ca n be rewr itten as X x ǫ x p ( x ) ≤ λ − X x (˜ ǫ x − ǫ x ) p ( x ) . (178) Since P x (˜ ǫ x − ǫ x ) p ( x ) ≤ P x | ˜ ǫ x − ǫ x | , a tighter con straint on p ( x ) is P x ǫ x p ( x ) ≤ λ − ∆ , and sinc e P x (˜ ǫ x − ǫ x ) p ( x ) ≥ − P x | ˜ ǫ x − ǫ x | , a looser co nstraint on p ( x ) is P x ǫ x p ( x ) ≤ λ + ∆ . Thus C ( ~ ǫ, λ − ∆) ≤ C ( ~ ˜ ǫ, λ ) ≤ C ( ~ ǫ, λ + ∆) . (179) Then o ne can write C ( ~ ǫ, λ ) − C ( ~ ˜ ǫ, λ ) = C ( ~ ǫ, λ ) − C ( ~ ǫ, λ − ∆) + C ( ~ ǫ, λ − ∆) − C ( ~ ˜ ǫ, λ ) (180) ≤ C ( ~ ǫ, λ ) − C ( ~ ǫ, λ − ∆) , (181) and similarly , C ( ~ ǫ, λ ) − C ( ~ ˜ ǫ, λ ) = C ( ~ ǫ, λ ) − C ( ~ ǫ, λ + ∆) + C ( ~ ǫ, λ + ∆) − C ( ~ ˜ ǫ, λ ) (182) ≥ C ( ~ ǫ, λ ) − C ( ~ ǫ, λ + ∆) , (183) Lemma 17 then implies that | C ( ~ ǫ, λ ) − C ( ~ ˜ ǫ, λ ) | ≤ − 6∆ log 2∆ |X | · |Y | . (18 4) October 29, 2018 DRAFT 40 R E F E R E N C E S [1] J. Mitola, “Cognitiv e radio: An i ntegrated agent architecture for software defined radio, ” Ph.D. dissertation, Royal Institute of T echnology , Sweden, 2000. [2] R. T andra and A. Sahai, “Fundamental limits on detection in l o w SNR under noise uncertainty , ” in W ire lessCom 05 Symposium on Signal Proc essing , Maui, Hawaii, Jun. 2005. [3] A. Sahai, N. Hov en, and R. T andra, “Some fundamental l imits on cognitiv e radio, ” in Allerton Confer ence on C ommuni- cation, Contr ol, and Computing , Monticello, Illinois, Oct. 2004. [4] R. T andra and A. Sahai, “SNR walls for signal detection, ” IEEE Jo urnal on Selected T opics in Signal Process ing , vol. 2, no. 1, pp. 4–17, February 2008. [5] N. Devro ye, P . Mitr an, and V . T arokh, “ Achie vable rates in cognitive radio channels, ” IEEE T ransactions on Information Theory , vol. 52, no. 5, pp. 1813–1 827, May 2006. [6] A. Jovi ˘ ci ´ c and P . V i swanath, “Cogniti ve radio: An information-theoretic perspectiv e, ” 2006. [Online]. A vailable: http://www .citebase.org/abstract?id=o ai:arXiv .org:cs/0604 107 [7] I. Maric, A. Goldsmith, G. Kramer, and S . S hamai(Shitz), “On the capacity of interference channels wit h a cognitiv e transmitter , ” i n 2007 W orkshop on Information Theory and Applications (ITA) , UCSD, La Jolla, CA, January 2007. [8] ——, “On t he capacity of interference channels with a partiall y-cogniti ve t ransmitter , ” in 2007 IEEE I nternational Symposium on Information Theory , Nice, France, June 2007. [9] I. Maric, R. Y at es, and G. Kramer , “Capacity of interference channels wit h partial transmitter cooperation, ” IEEE T ransactions on Information Theory , vol. 53, no. 10, pp. 3536–354 8, October 2007. [10] A. Goldsmith, S. Jafar , I. Maric, and S . S riniv asa, “Breaking spectrum gridlock with cognitiv e radios: An information theoretic perspecti ve, ” P r oceedings of the IE EE , 2008. [11] N. Devroy e, M. V u, and V . T arokh, “ Achiev able rates and scaling laws in cognitiv e radio channels, ” EUR ASIP Jo urnal on W ire less Communications and Networking, special issue on Cognitive Radio and Dynamic Spectrum Sharing Systems , 2008. [12] R. Ahlswede, “The capacity region of a channel with t wo senders and two recei vers, ” Annals of Pr obability , vol. 2, no. 5, pp. 805–814, 1974. [13] H. Sato, “T wo-user communication channels, ” Univ ersity of Hawaii, Honolulu, HI , T ech. Rep. B75-29, October 1975. [14] A. Carleial, “Interference channels, ” IEEE T ransactions on Information Theory , vol. 24, no. 1, pp. 60–70, January 1978. [15] M. H. M. Costa, “On the Gaussian interference channel, ” IEEE T ransactions on Information Theory , vo l. 31, pp. 607–615 , 1985. [16] M. Gastpar , “On capacity und er recei ve and spatial spectrum-sharing constraints, ” IEEE T ran sactions on Information Theory , vol. 53, no. 2, pp. 471–48 7, February 2007. [17] A. Ghasemi and E. Sousa, “Capacity of fading chann els under spectrum-sharing constraints, ” in IEEE Internationa l Confer ence on Communications , vol. 10, June 2006, pp. 4373–4 378. [18] R. Mudumbai, B. Wild, U. Madhow , and K. Ramchandran, “Distributed beamforming using 1 bit feedback: From concept to realization, ” in Allerton Confer ence on Communication, Contro l, and Computing , Monticello, Illinois, S eptember 2006. [19] R. Mudumbai, J. Hespanha, U. Madho w , and G. Barriac, “Scalable f eedback control for distributed beamforming in sensor networks, ” in International Symposium on Information Theory , Adelaide, Australia, September 2005. [20] T . Cover and J. Thomas, Elements of Information Theory , 2nd ed. W iley-Interscience, 2006. [21] R. Durrett, Pr obability: Theory and Examples, 3r d ed , ser . Information and System Sciences Series. Duxbury , 2004. October 29, 2018 DRAFT 41 [22] A. Dembo and O. Zeitouni, Lar ge Deviations T echniques and Applications, 2nd ed , ser . Stochastic Modelling and Applied Probability . Springer , 1998. [23] I. C sisz ´ ar and J. G. K ¨ orner , Information Theory: Coding T heor ems for Discre te Memoryless Systems . Orlando, FL, USA: Academic Press, Inc., 1982. [24] R. Gallager , I nformation Theory and Reliable Communication . John Wiley and Sons, 1968. [25] C. Chang, unpublished manuscript, 2006. October 29, 2018 DRAFT
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment