Success Exponent of Wiretapper: A Tradeoff between Secrecy and Reliability
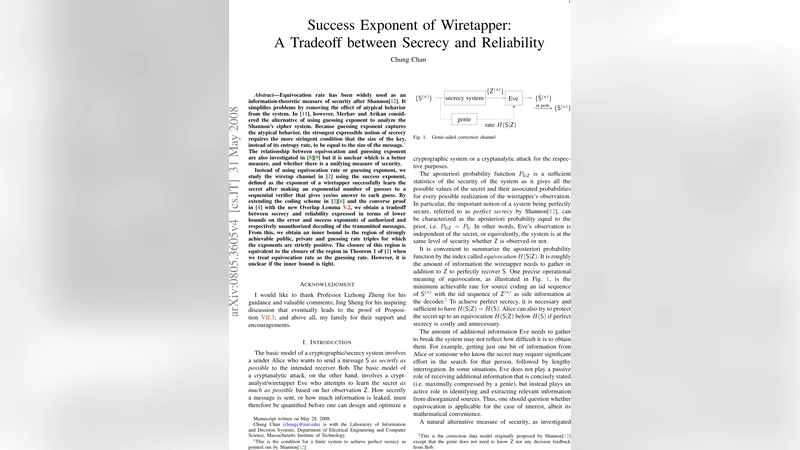
Equivocation rate has been widely used as an information-theoretic measure of security after Shannon[10]. It simplifies problems by removing the effect of atypical behavior from the system. In [9], however, Merhav and Arikan considered the alternative of using guessing exponent to analyze the Shannon’s cipher system. Because guessing exponent captures the atypical behavior, the strongest expressible notion of secrecy requires the more stringent condition that the size of the key, instead of its entropy rate, to be equal to the size of the message. The relationship between equivocation and guessing exponent are also investigated in [6][7] but it is unclear which is a better measure, and whether there is a unifying measure of security. Instead of using equivocation rate or guessing exponent, we study the wiretap channel in [2] using the success exponent, defined as the exponent of a wiretapper successfully learn the secret after making an exponential number of guesses to a sequential verifier that gives yes/no answer to each guess. By extending the coding scheme in [2][5] and the converse proof in [4] with the new Overlap Lemma 5.2, we obtain a tradeoff between secrecy and reliability expressed in terms of lower bounds on the error and success exponents of authorized and respectively unauthorized decoding of the transmitted messages. From this, we obtain an inner bound to the region of strongly achievable public, private and guessing rate triples for which the exponents are strictly positive. The closure of this region is equivalent to the closure of the region in Theorem 1 of [2] when we treat equivocation rate as the guessing rate. However, it is unclear if the inner bound is tight.
💡 Research Summary
The paper introduces a novel security metric for the wiretap channel called the “success exponent,” which measures the exponential rate at which an eavesdropper’s probability of correctly guessing the secret decays when the eavesdropper is allowed to make a sequential yes/no query to a verifier. This metric captures atypical events that are ignored by the traditional equivocation (conditional entropy) measure and complements the guessing exponent studied by Merhav and Arikan.
The authors consider the classic wiretap model of Wyner and Csiszár–Körner: Alice transmits a pair of messages – a public message m and a private (secret) message l – using a stochastic encoder f that produces a length‑n codeword X. The codeword passes through a memoryless broadcast channel (W_b, W_e) observed by the legitimate receiver Bob and the eavesdropper Eve, respectively. Bob employs a deterministic decoder φ_b to recover (m,l); Eve first decodes the public part with a deterministic decoder φ_e and then attempts to recover the secret by submitting up to λ = e^{nR_λ} guesses to a sequential verifier that answers “yes” or “no.” Eve’s list decoder ψ returns a set of λ candidate secrets; success occurs if the true secret belongs to this set.
Three exponential performance measures are defined:
- E_b: the error exponent of Bob’s decoding (probability that φ_b fails).
- E_e: the error exponent of Eve’s decoding of the public message.
- S_e: the success exponent, i.e., the exponent governing the decay of Eve’s probability of including the true secret in her λ‑list.
The main technical contribution is a single‑letter inner bound on the set of achievable triples (R_M, R_L, R_λ) together with corresponding positive exponents (E_b, E_e, S_e). The bound is derived by extending the coding scheme of Csiszár–Körner (random binning with stochastic encoding) and by introducing a new “Overlap Lemma 5.2.” This lemma quantifies how often codewords corresponding to different secret messages overlap in the channel output space, which is crucial for analyzing Eve’s list‑decoding success. The authors also employ the classical Packing Lemma to bound the error probabilities for Bob and for Eve’s public‑message decoding.
The resulting inner bound states that for any choice of auxiliary random variables (U, V) satisfying the usual Markov chain U → V → X → (Y,Z), the following inequalities guarantee positive exponents:
- R_M ≤ I(U;Y) – I(U;Z) (public rate limited by the secrecy advantage).
- R_L ≤ I(V;Y|U) – I(V;Z|U) (private rate limited by the conditional secrecy advantage).
- R_λ ≤ I(V;Z|U) (the allowed guessing rate cannot exceed the information Eve obtains about the secret given the public part).
Under these constraints, the error exponents E_b and E_e are lower‑bounded by the corresponding random‑coding error exponents, while S_e is lower‑bounded by a function of the overlap probability derived in Lemma 5.2.
Importantly, the closure of the achievable region coincides with the region described in Theorem 1 of Csiszár–Körner when equivocation is interpreted as a guessing rate, showing that the success‑exponent framework recovers the classical secrecy capacity result while providing a finer-grained trade‑off between secrecy and reliability.
The paper acknowledges that the inner bound may not be tight; no matching outer bound is presented, leaving open the question of whether larger exponent triples are possible. Future work could explore tighter converse arguments, alternative coding constructions (e.g., multi‑layer superposition coding), or extensions to continuous alphabets and more general eavesdropper capabilities.
From a practical perspective, the success exponent directly quantifies the number of allowed password‑guess attempts or verification queries before the eavesdropper’s success probability becomes negligible. This makes the metric attractive for designing systems where a verifier (e.g., a login server) is exposed to brute‑force attacks, allowing designers to balance the permissible number of attempts against the desired security level.
In summary, the paper provides a rigorous information‑theoretic analysis of a new secrecy metric, derives single‑letter inner bounds on achievable rates and exponents, and demonstrates how this framework unifies and extends previous notions of equivocation and guessing exponent in the wiretap channel setting.
Comments & Academic Discussion
Loading comments...
Leave a Comment