Joint Cooperation and Multi-Hopping Increase the Capacity of Wireless Networks
The problem of communication among nodes in an \emph{extended network} is considered, where radio power decay and interference are limiting factors. It has been shown previously that, with simple multi-hopping, the achievable total communication rate…
Authors: Sam Vakil, Ben Liang
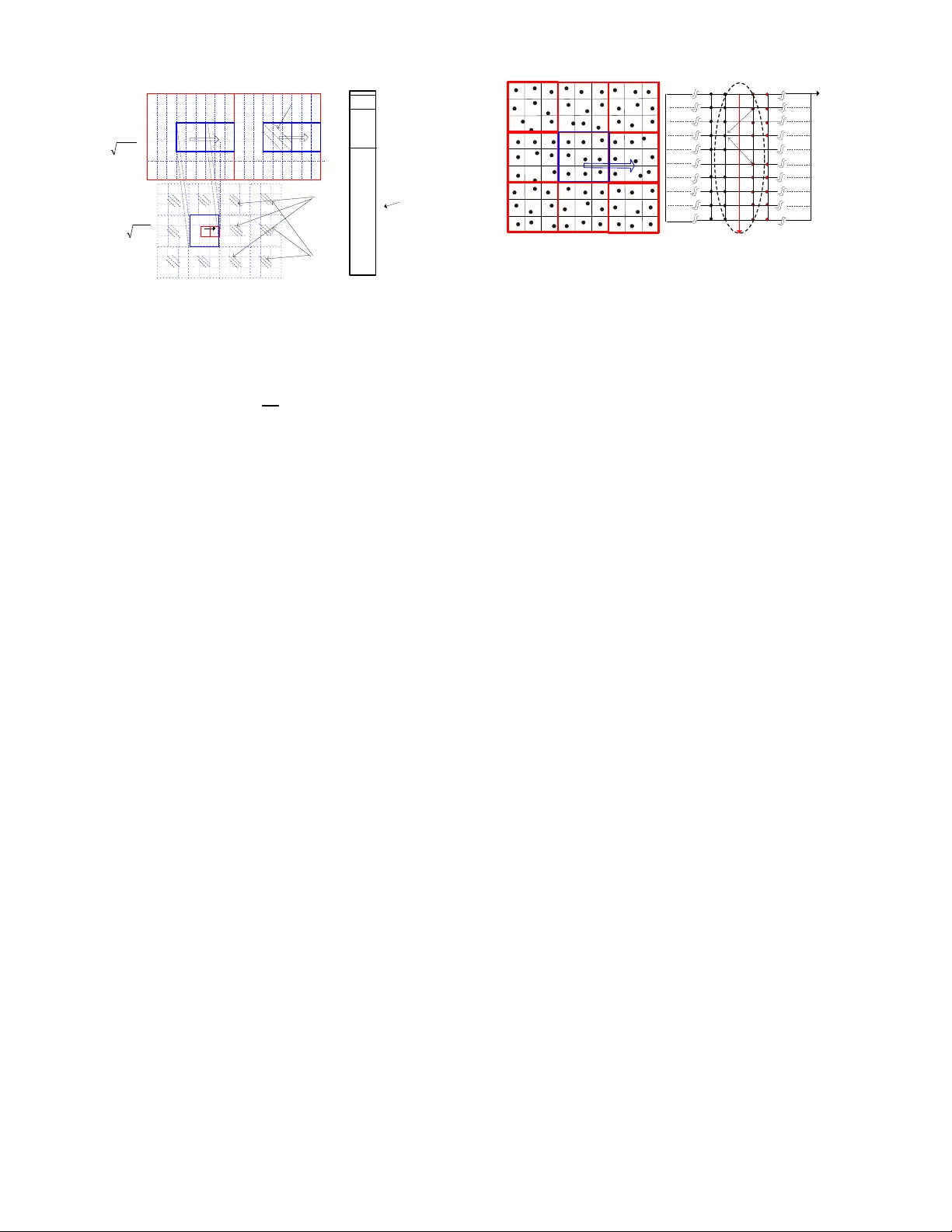
Joint Cooperation and Multi-Hopping Increase the Capacity of W ireless Netw orks Sam V akil, Student M ember , IEEE , and Ben Liang, Senior Member , IEEE Abstract —The problem of communication among nodes in an extended network is considered, where radio power decay and in- terference are limiting factors. It h as b een shown previously that, with simple multi-hoppi ng, the achiev able t otal communication rate in such a network is at most Θ( √ N ) . In th is work, we stu dy the benefit of node c ooperation in conjunction with multi-hoppi ng on the network capacity . W e pro pose a multi-phase communi- cation scheme, combining distributed MIMO transmission with multi-hop f orwarding among clusters of nodes. W e derive the net- work throughput of t his communication scheme and d etermine the optimal cluster size. Th is provides a constructive lowe r bound on the network capacity . W e first show th at in regular networks a rate of ω ( N 2 3 ) can be achieved with transmission power scaling of Θ( N α 6 − 1 3 ) , where α > 2 is the signal path- loss exponent. W e further extend this res ult to random n etworks , where we show a rate of ω ` N 2 3 (log N ) 2 − α 6 ´ can be achieved with transmission power scaling of Θ( N α 6 − 1 3 (log N ) − ( α − 2) 2 6 ) in a random network with unit node density . In particular , as α app roac hes 2, only constant transmission power is r equired. Finally , we stu dy a random network with density λ = Ω(log N ) and show that a rate of ω (( λN ) 2 3 ) i s achieved an d th e required p ower scales as Θ( N α 6 − 1 3 λ α 3 − 2 3 ) . I . I N T RO D U C T I O N Understand ing the feasibility of multi-h op wireless net- works has been the subject of a great deal of research . In this regard, much mathematical and practical consideration has been devoted to studying the capa city of such networks. In the semina l work o f Gup ta and Kumar [1], it h as be en shown that under the assumption of po int-to-po int communicatio n, the per-node asy mptotic capacity decays at least as fast 1 √ N for a dense network with N nodes, wher e the number of nodes app roaches infinity within a unit disk or unit sphere. Subsequen t studies have sh own similar dec ay fo r uppe r-bound on capacity in an e x tended network , wher e the dep loyment are a increases linearly with the number of nodes wh ile the node density remains constant [2][3][4]. In such network s, be sides interferen ce, the r adio p ower decay over large co mmunicatio n distances is another determ ining factor affecting the commu- nication rate. The r esults o f [1] are based on th e assump tion that the commun ication between a specific source -destination pair is The authors are affili ated with the Department of Electric al and Computer Engineeri ng, Univ ersity of T oronto, 1 0 King’ s College Road, T oronto, On tario, M5S 3G4, Canada. E mail: { v akil,li ang } @co mm.utoronto.ca. This work was supported in part by a grant from LG Electronics. A preliminary version of this paper has appeared in the IEEE Communications Society Conference on Sensor , Mesh and Ad Hoc Communicati ons and Networks (SECON) 2008. This version contai ns additiona l detai ls and expan ded analysis on differe nt netw ork en vironment s. always deter iorated by the con current tran smission of the other nod es. In con trast, coop erativ e communication can result in consider able capacity gain s by discard ing this con straint. Under this setting, the n otion o f a link is c onsidered as a set of users, enco ding and transmitting messages in coord ina- tion. Such a com munication setting mimics a Multiple-Inpu t Multiple-Outp ut (MIM O) a ntenna system [ 5] in a distributed fashion, where u sers act as v irtual anten na arrays coope rating to transm it a message towards the d estination. Exploiting the spatial m ultiplexing gain of MIMO is appea l- ing, since MIMO co mmunicatio n can r esult in linear ca pacity increase as a f unction of th e n umber of antennas in the high SNR regime [5]. Furthermo re, Ozgur et a l h as r ecently extended th is result to distributed MIMO c ommun ication [6] to achiev e lin ear capac ity scaling with N in a de nse network with constan t transmission power , b y utilizing a hierarchical commun ication scheme with sing le-hop d istributed MIMO transmission be tween th e sou rce and destination clu sters. Howe ver, multi-hop forwarding is e ssential to the efficiency of large-scale extended networks. It remains an open pro blem to quantify the capacity o f multi-hop cooperativ e comm unication. This work represents a step toward this directio n. W e extend our results in [7] and study the b enefit of coo peration in an extended network , by combining peer-node coopera tion with multi-hop forwardin g to mitigate the path-loss power d ecay and harness spatial multiplexing gain . W e prop ose a multi- phase comm unication scheme based on multi-hop distributed MIMO forwarding among clusters of nod es, where a cluster is a hierarch ically organized set of no des tha t coo perate simultaneou sly to transmit a single message vector . W e then derive the n etwork throug hput of this com munication scheme by con sidering the optimal cluster size. W e first show that, for a r e g ular network , wh ere one node is ran domly p laced within each square of unit area, the network throug hput scales as ω ( N 2 3 ) with transmission power r equiremen t of Θ( N α 6 − 1 3 ) , whe re α > 2 is the sign al p ath loss expo- nent. W e f urther extend this r esult to a random netwo rk , where the no des are u niformly distributed with unit node density , and show that thro ughpu t s caling is lower-bounded by ω N 2 3 (log N ) 2 − α 6 with transmission p ower require ment of Θ( N α 6 − 1 3 (log N ) − ( α − 2) 2 6 ) . W e finally study a random netw ork with incr easing node d ensity and show that if the density λ follows λ = Ω(lo g N ) the thro ughpu t s caling is lower- bound ed by ω (( λN ) 2 3 ) with po wer scaling Θ( N α 6 − 1 3 λ α 3 − 2 3 ) . The existence of th e pro posed co mmunicatio n scheme provides a constructive lower bound on th e capacity of extended network s with nod e coo peration. 2 The rest of the paper is organized as fo llows. In Section II, we sum marize the related work. Sectio n III details th e network mode l. I n Section IV we explain the three p hases of the comm unication scheme. Section V analytically evaluates each communication phase and pr esents the overall ne twork capacity . W e extend ou r re sults to random networks in Section VI. Finally , the concludin g rem arks are giv en in Section VII. I I . R E L AT E D W O R K Existing research on th e scalin g behavior of multi-ho p wireless networks can be categorized mainly into two group s. The first categor y is concen trated o n infor mation-theo retic upper-boun ds on the netw ork capacity by u sing cut-set bounds, and the second categor y d eals with constructive comm unica- tion schemes wh ich achieve a lo we r-bound on the capacity . Different top ologies such as dense a nd extended network s h av e been co nsidered in each categor y . Information Theor etic Upper-bounds : Th e seminal work [1] provides both upper-boun ds a nd constructive commu nication schemes to show th at the poin t-to-poin t capac ity of a d ense wireless n etwork is Θ ( √ N ) . In [2], [3], [ 4], an d [8], the authors d erive infor mation the oretic upper-boun ds o n th e network capacity . These works study the c apacity scaling of extended n etworks and obtain upper-bounds on the capacity by using cut-set bou nds. I n par ticular, Xie et al pr ove that for en vironmen ts with path- loss expo nent α > 4 an d constant per node power , the expected transport c apacity grows at mo st linearly in the n umber of no des, so that for an extended network with uniformly distributed source-destinatio n pairs, the network capacity is O ( √ N ) [4]. While in simple mu lti-hoppin g, increasing the tran smission power does not improve the capacity scaling, Jovicic et al in [2] show th at the upper-bound on the network transpor t capacity scales lin early with n ode p ower . Similar r esults are shown in [4]. Their results motiv ates u sing th e extra degree of freed om provided by the ch oice of transmission power . W e exploit this in the proposed collab orative scheme to in crease the network capacity . Constructive Communica tion S chemes: T o umpis et al in [9] have pro posed a gridd ing of a unit area ne twork an d the use of 9 -TDMA s chedulin g to deri ve the same lower -b ound on capacity as [1] in a m ore straigh tforward manner . They furth er extend their model to conside r the effect of node m obility and fading on the cap acity . Francesche tti et al in [10] h av e closed the previous gap between the capacity in arbitrary and random networks. They u se percolation theor y to show that the sum capacity of their proposed communicatio n scheme scales as Θ( √ N ) . Non e of th e above utilizes coo perative tr ansmission. There has been mu ch r esearch in to n ode c ooperatio n in the con text of single-sourc e, single- destination, and N relays. For example, Gastpar e t al in [ 11] show an achiev able rate scaling of Θ(log N ) . Howe ver, Ozgur et al in [6] are th e first to exploit the linear-scaling result of MIMO commu nica- tion in a mu ltiple-source n etwork u sing a d istributed MI MO paradigm . For a dense network, t hey propose a hierarchical co- operative commun ication scheme with sing le-hop distributed MIMO transmission to achieve a network through put scaling of Ω( N 1 − ǫ ) , ∀ ǫ > 0 , and single-h op distributed MIMO transmission. They further show that wh en th e same sch eme is applied to the more realistic extende d network model, it results in a thro ughpu t Θ( N 2 − α 2 + ǫ ) , implyin g that for α < 3 , the schem e outpe rforms simple multi-hop ping. Our work is mo ti vated by [ 6]. Howe ver, we prop ose a multi-hop distributed M IMO scheme specifically designe d for extended networks. Furthe rmore, we show th at with a small increase in the transmission power , our scheme p erforms unifor mly b etter than sim ple m ulti-hopp ing for all values of α > 2 . As f ar as we are a ware, ther e is no existing work on analyz ing th e achiev a ble rate of combin ing coo perative commun ication and multi-hop forwarding. Finally , Ae ron an d Saligrama in [ 12] have studied th e effect of node cooper ation o n the capacity of wireless networks with a fixed receiver SNR at all nodes and obtain ed Θ( N 2 3 ) network thro ughpu t, throu gh sp atially separ ated MIM O relays which collaborate in their transmissions. Ho wever , th e assump- tion o f constant receiver SNR at all nodes implies that the transmission power ne eds to scale as Θ( N α 2 ) . In contr ast, in this work we show that with m uch lower power scaling, the same commu nication rate can be ach iev ed by using multi-h op distributed MI MO tr ansmissions. I I I . N E T W O R K M O D E L W e c onsider an extend ed network with N nodes distributed within the area B N = [0 , √ N ] × [0 , √ N ] . W e fir st evaluate the capacity re sults for nod es following a sp ecial top ology that we call a r egular network . I n a regular network, we divide B N to N squares of u nit are a a nd a ssume there is exactly one node in each such sq uare. W e then gen eralize our r esults to a rand om network , wh ere nodes are d istributed indepen dently and u niformly over the are a B N . A matching of the source -destination p airs is picked at random , so that each node is the destination of exactly on e source. It is assum ed that the so urces are all send ing their messages with a co mmon source-to-d estination rate R ( N ) bits/sec, and the total n etwork thr oughp ut is T ( N ) = N R ( N ) bits/sec. Each node di vides its messages into sub -blocks o f length L bits and sends packets with length equal to a multip le of L d uring the comm unication with its intended rec eiv er . It will be clear later tha t the pro per sub-blo ck size L d epends only on the MIMO transmission details and does not affect the thr oughp ut scaling ana lysis. In con trast, the multiplier to L is an optim ization p arameter dep endent on the o ptimal size of a cluster w hich will be explained in d etail in Section V. Similar to the model of [1][6][1 0][12], we co nsider a line-of-sig ht en v ironmen t without fading or shadowing. The channel g ain between two nod es i and j in the network is assumed to fo llow a stand ard baseband model and can b e written as h ij = e i θ ij d α 2 ij , (1) where d ij is the Euclidea n distance between the two nodes, i is the un it imagin ary n umber, θ ij is the phase chang e distributed unifor mly and independ ently in [0 , 2 π ] [5], and α > 2 is the 3 S R1 { 2 nd Level S R1 R2 R2 R2 R R R1 R1 R1 R1 R1 R1 R1 1 st Level ) 2 ( g ) 1 ( g { Iteration 2 1 st level transmit-cluster 1 st level receive-cluster { Iteration 1 Interferers 2 nd tier Interferers 1 st tier Interferer { { (a) g(1) g(2) L=g(K) Number of bits sent a fter kth-level cast g(K-1) Packet of size L . . . (b) Fig. 1. (a) k th-le ve l clusters and patte rn of interferer s to a specific cluster in the intra-cluste r phase . (b) Iter ati ve progre ssion of int ra-clust er pa cke t transmission. path lo ss exponent, such that the power of the received signal at node j fro m n ode i equ als P i d α ij , where P i is the transmission power of no de i . Th en, th e received message at n ode j at time m can be expressed as Y j [ m ] = X i ∈ T [ m ] h ij [ m ] X i [ m ] + Z j [ m ] + I j [ m ] , (2) where T [ m ] represents th e set o f acti ve senders at time m transmitting signals X i [ m ] to n ode j , which can be added constructively [5], Y j [ m ] is the received message at nod e j at time m , Z j [ m ] is the ad ditiv e wh ite Gaussian noise at node j with variance N 0 , and I j [ m ] is the interf erence from the node s which are destructive to the reception of node j . W e do n ot con sider sophisticated mu lti-user detection technique s at the receiver no des a nd simply treat interfer ence as noise to o btain a lower-bound on the network capacity . Furthermo re, since we are p roposing a con structiv e lower- bound o n th e cap acity , during each commu nication phase, a network top ology wh ich results in th e lowest commun ication rate is co nsidered. T herefor e, th e dependen cy of the chann el gains on time can be removed in our analysis. I V . C O M M U N I C A T I O N S C H E M E W e consider a commun ication scheme whose r ate provides a constructive lo wer-bound on the network capacity . W e arra nge the nodes in to a hierarch ical K level clustering structu re, ea ch lev el consisting o f 9 no n-overlapping lower - le vel clusters in a 3-by- 3 formatio n, such that the k th-level cluster refer s to the set of nod es that lie in a square of area g ( k ) = 3 2 k , as depicted in Fig. 1(a). Unless o therwise stated, we u se th e term cluster synonymou sly with the term K th -level clu ster . The prop osed scheme is c omprised of three pha ses , intra- cluster message dissemination from the source to all nodes in its cluster, in ter-cluster message for warding toward the destination node’ s cluster, and message decod ing at the de sti- nation. In th e fo llowing we explain the transmission sch eme in each ph ase for the regular network. The generalizatio n to the case o f a r andom n etwork f ollows the same structu re and th e difference is explain ed in Section VI. Th rough out the paper, we use the notatio n P ( i ) , fo r the tr ansmission power during the i th ph ase. TX RX5 RX6 RX7 RX8 RX9 RX2 RX3 RX4 (a) Transmit Receive 1 2 3 4 5 6 7 8 9 10 r x t x y i 1 j 2 j 2 2 1 = = ij ij D D (b) Fig. 2. (a) Patte rn of transmissions between the neighbor clusters. (b) Node topology for constructing capacity lo wer- bound. Center red line represents border between two 2nd-le vel clusters Phase 1: Intra-Cluster Communication . Th e g oal of th is phase is to distribute eac h source node’ s message to the set of g ( K ) no des in th e sou rce’ s clu ster ( which will serve as r elays for the sourc e in the next ph ase). W e utilize a hierarchical cooper ation strategy carr ied out in K iteratio ns as shown in Fig. 1(a). Each sou rce node divides its message to packets of length g ( K ) L bits, ( i.e., g(K) sub-blo cks and L bits pe r sub-block ). The packet’ s tra nsmission is carried out in a K - lev el pro gression as sho wn in Fig. 1(b), such tha t af ter the k th itera tion, the source S will have for warded g ( k ) L bits o f its packet. W e assume th at the nodes tran smit with a common constant power P (1) = P du ring this p hase. The d etails of th is iterativ e comm unication sche me are given in the f ollowing. T wo k th-level clusters are said to be n eighbors if their bound aries touch. The refore, each k th-level cluster has 8 neighbo rs. T o av oid interferen ce from neighbor ing clu sters, TDMA is used to sch edule transmission am ong the 9 par- titioning ( k − 1) th-level clusters within a k th-level cluster . This is c alled a 9-TDMA schem e. As shown in Fig . 2(a ), 9- TDMA imp lies that, dur ing the k th iteration , on ly one a mong the nine ( k − 1) th level clusters ac ts as the transmit-cluster , and its eigh t neig hbor clusters are potential r eceive-clusters . The ( k − 1) th level transmit- and receive-clusters communicate using distributed MIMO tran smission. W e call e ach such commun ication a k th -level cast . At the receiv e-cluster side, during th e k th-lev el cast, each of the ( k − 1) th-level r eceive- clusters is set to acti ve receive mod e in a round -robb in manner, based o n a specific order as depicted in Fig. 2(a). During the fir st iter ation, an activ e source per forms 8 consecutive 1 st-level casts to transmit a different s ub-blo ck of L bits to each of its 8 neigh bor no des and keeps L b its in its own buf fer . Hence, a t th e end of the first iteration, the 1st-level cluster contain s 9 L bits. During the second iteration, as de picted in th e 2 nd-level in Fig. 1 (a), th e g (1) = 9 nodes in side th e first lev el tran smit-clusters act as distributed antennas, sending their messages a t the sam e time. Th us, during each 2 nd- lev el cast, 9 L bits are sent s imultaneou sly using distributed MIMO to on e of the 8 neig hbor receive- clusters of size g (1 ) . Note that concurr ently with this, the source can distribute anoth er set of 9 L bits to its 1st-le vel 4 cluster in preparatio n for the n ext 2n d-level cast. 1 Hence, throug h 8 consecutive 2nd- lev el casts, 81 L bits o f th e source are transmitted in this iteration to the 2nd- le vel cluster . This pattern rep eats, so that in th e K th iteration , g ( K ) L bits of the source are transmitted to the K th- le vel cluster . The n umber of iterations, K , and the refore the re quired time, T 1 , to finish this step are design pa rameters to be fo und in Section V. Later , to d etermine th e e ffect of interfer ence on the n etwork throug hput, we no te that the set of interfer er cluster s imposed by 9 -TDMA fo llows the pattern depicted in Fig. 1(a ), where R represents the k th-level receive-cluster . The shaded transmit- clusters, with cor respond ing r eceiv e-clusters labe led ‘R1’, ac t as interferers (1 st tier interfere rs), since they are transmitting synchro nously during R’ s recep tion. It is clear that in the i th tier there are 8 i in terferers. (So me of the 2nd tier interfe rers are de picted in the figu re). As the clusters incr ease in size, we still have the sam e pattern for th e interferer s’ locations. T his can be b etter seen in Fig. 1 (a) by con sidering the 2nd -lev el cast, whe re the spatial separation of interferer s is multiplied by 3 fro m that of the 1st-lev el cast. Phase 2: Inter -Cluster Communication . The goal of this phase is to deliver the messag e vecto r of leng th g ( K ) L bits from the sou rce-clusters tow ards the destination -clusters in a multi-hop fashion. By a destination -cluster, we m ean a clu ster of size g ( K ) that include s the corre sponding final destinatio n for a specific source node. W e co nsider a cluster-based rou ting scheme in which ho p-by- hop commu nication between ne igh- boring cluster s is perfo rmed either h orizontally or vertically as shown in Fig . 3. Each interm ediate cluster along the p ath is called a r elay-clu ster , which acts as a distrib u ted multi-antenna system to forward its received me ssage vector . In th e first h op, the n odes of the tra nsmitting relay-clu ster indepen dently en code the message vecto r to C symbols using a Gaussian c ode-bo ok of power P (2) = 2 α P g ( K ) α 2 − 1 . In Section V -B, we will show that within each hop g ( K ) C symbols are tran smitted in one sho t and we b enefit from g ( K ) spatial degrees of freed om in MIMO com munication . These symb ols are sent syn chrono usly to the receiving relay- cluster . The nod es in th e receiving relay- cluster then amplify their receive observation to meet th e power req uirement P (2) , and forward it to the next clu ster alon g th e h orizontal path . Such m essage pro pagation contin ues until th e m essage vector reaches the cluster with the same vertical b ound aries as the destination cluster, as illustrated in Fig . 3. Then, the ho p- by-ho p distributed MIMO com munication among th e clusters is perform ed vertically until the message vector r eaches the destination cluster . W e denote the require d time to complete the routing of a node’ s message by T 2 . Phase 3: Mess age Decoding a t the Destination . In this phase, e ach no de in the d estination cluster ha s an observation of th e message tr ansmitted by the source S . The nodes each quantize their observation into Q bits and synchron ously tra ns- 1 This operati on assumes the full-dup lex communica tion, w hich is common in multi-hop capacit y an alysis [1]. If only half-duple x communication is av ailable, the 1st-le vel s ource-c luster will simply wait for the source to send suf ficient data before each 2nd-le vel cast. The same procedure can be applied in all lev els, and it is easy to show that the resultant increase in transmission time does not change the scaling of the optimal cluster size or the network throughput . S D Kth-level Cluster Fig. 3. Routing in the inter-c luster phase. mit the quan tized observations towards the destination u sing a common constant power P (3) = P . Th is co mmunicatio n set- ting can be considere d as a simple distributed Multiple -Input Single-Outp ut (MISO) system in the de stination cluster . W e again use a 9-T DMA scheduling in this ph ase to deter mine the activ e clusters for transmission, which results in inter ference mitigation. W e den ote the requ ired time to complete message transmission fro m th e destinatio n cluster to the destination node by T 3 . V . S C A L I N G L A W S F O R R E G U L A R N E T W O R K S In this section, we d eriv e the asymp totic achiev ab le network throug hput T ( N ) using th e propo sed com munication schem e. It is clear that the ef ficiency of this scheme hinges on the optimization of th e cluster ( K th -level cluster) size. While larger clu sters result in higher MIMO gain , better inter ferer separation, and lower cluster-hop co unt, the no des inside large clu sters need to distribute their m essages to a large number of nodes and c ompete with m any nodes fo r medium access. By consider ing such tr adeoffs, we derive the optimal cluster size to minimize the total tra nsmission time of the three co mmunica tion phases. Note th at the communicatio n overheads, such as n ode sch eduling and hiera rchy f ormation , are negligib le in the long run and a re igno red in ou r analysis [6][9][10]. A. In tra-Cluster Com munication During the ( k + 1 ) th iter ation of intra-c luster message dissemination, a k th -level cluster transmits a message vector to each of its 8 neigh boring k th -lev el clusters in 8 consecutive ( k + 1 ) th-level casts. W e no w deriv e a lower - bound on th e achiev able rate, den oted R k Intra , during each such tr ansmission. Consider two adjacent squares of side leng th 3 k which share an edge. The achiev able commun ication r ate between the correspo nding two k th- lev el clusters can b e expressed using MIMO capacity results [13]. Using a no tation similar to the one we ad opted in (2), th e vector of the received message s at the k th -lev el r eceiv e-cluster can b e expressed as Y g ( k ) × 1 = H X g ( k ) × 1 + Z g ( k ) × 1 + I g ( k ) × 1 , (3) where H represents the g ( k ) × g ( k ) channel matr ix. T reating the inter ference simp ly as anoth er source of n oise, th e in ter- ference plus n oise power at a nod e j in th e re ceiv e-cluster is giv en as N 0 + I k j , where I k j represents the interfer ence power at j dur ing th e ( k + 1) th-level cast. In order to d erive a capacity lower - bound , we can rep lace the in terference power at all of 5 the no des in side a sp ecific k th-level cluster by I k = max j I k j . Assuming th at th e transmitted signals, X i , a re iid and chosen from an Gau ssian d istribution N (0 , P ) and pe rfect ch annel state informa tion is available at the recei ve cluster , the mu- tual info rmation b etween the transmit- and receiv e-clusters is lower - bound ed by the special case of Gaussian noise plu s interferen ce. Henc e, we have R k Intra = I ( X ; Y , H ) ≥ log det( I + P N 0 + I k H H ∗ ) . (4) W e now d erive a more useful expression to rep lace the above gener al f orm. An example of in tra-cluster MIMO com- munication is depicted in Fig. 2(a) fo r 1st-le vel clusters of size g (1) = 9 . T he worst case top ology hap pens when the transmitters are located at the furthest p ossible d istance from the receivers. Fig ure 2 (b) demonstra tes such a topo logy in th e 3rd-level cast for two horizo ntally ad jacent 2n d-level clusters of size g (2) = 81 . W itho ut loss of generality , we labe l the b order (e.g., center red lin e in Figure 2(b)) between the two adjacent k th- lev el clusters as the ref erence x -coord inate. Then, g i ven th e constra int that th ere is on e nod e in side each square, setting the transmit nod es’ x -co ordina tes to x t = − 1 , − 2 , . . . , − p g ( k ) , and the r eceive nodes’ x -coord inates to x r = 1 , 2 , . . . , p g ( k ) results in maximu m sepa ration between them. W e n ext find the y -co ordinates for the worst case topo logy . W e focus on th e transmit an d recei ve nodes which lie in squares ad jacent to th e bor der . The y -coo rdinate fo r othe r nodes f ollows the same stru cture b y symm etry . W e index th e y -coo rdinates o f the horizontal ed ges from 1 to p g ( k ) + 1 as sh own in Fig. 2(b). In general it is not easy to find the indices along the transmit and rece i ve ed ges that m inimize R k Intra . Howev er , f or ou r analysis, since there is a h orizontal distance of at least two b etween any two nodes ch osen from the transmit a nd the recei ve clusters (i.e., x r − x t ≥ 2 ), we h av e h ij ≤ 1 2 α 2 . For α > 2 , the small value of h ij facilitates tight lo wer-bounds for the MIMO com munication rate between the two adjacent clusters. Lemma 1 b elow states that the con struction of this lower-bound is eq uiv alen t to finding the y -coo rdinate fo r transmit and receiv e no des such that T r ( H H ∗ ) = P i ∈ T k P j ∈ R k | h ij | 2 is minimized, where T k represents the set of nod es in the k th-lev el tr ansmit-cluster and R k is the set of k th-lev el r eceiv e-cluster nod es. Lemma 2 then p rovides the explicit y -co ordinates. The proo fs are given in the appen dix. Lemma 1: The cap acity exp ression lo g det( I + P N 0 + I H H ∗ ) is tig htly lower-bounded by log (1 + P N 0 + I T r ( H H ∗ )) , where Tr is the matrix trace op eration. Lemma 2: The lowest rate in a ( k + 1) th-level cast is achieved when the no des on the transmit side are located at y i ∈ { 1 , · · · , p g ( k ) + 1 }\ { √ g ( k )+1 2 } and th e no des on th e re- ceiv e side ar e located at y j ∈ { 1 , · · · , p g ( k ) + 1 }\ { √ g ( k )+3 2 } or vice versa d ue to symmetry . W e n ext use Lem mas 1 and 2 to d erive the ach iev ab le commun ication rate. W e d efine the vertica l distance between two no des i and j as D ij = | y i − y j | . Clearly , D ij ∈ { 0 , 1 , · · · , p g ( k ) } . I n order to ev alu ate P i ∈ T k P j ∈ R k | h ij | 2 we have to q uantify the numbe r of transmit-receiv e p airs ( i, j ) , along x t = − 1 and x r = 1 , which are located at a specific vertical distance D ij = d from each other . W e den ote this quantity by Φ d = |{ ( i , j ) | D ij = d, x i = − 1 , x j = 1 }| . For a giv en vertical separatio n, D ij = d , between a pa ir of nodes, we have X X ( i,j s.t. D ij = d ) | h ij | 2 = − 1 X x t = − √ g ( k ) √ g ( k ) X x r =1 Φ d p ( x r − x t ) 2 + d 2 α . The ab ove sum can b e written as u ( d )Φ d , wh ere u ( d ) = √ g ( k ) X x t =1 √ g ( k ) X x r =1 1 p ( x r + x t ) 2 + d 2 α > √ g ( k ) X x =2 x − 1 ( x 2 + d 2 ) α 2 > Z √ g ( k ) 2 x − 1 ( x 2 + d 2 ) α 2 dx > Z √ g ( k ) 2 x/ 2 ( x 2 + d 2 ) α 2 dx = 1 4( α 2 − 1) ( 1 (4 + d 2 ) α 2 − 1 − 1 ( g ( k ) + d 2 ) α 2 − 1 ) , α > 2 . (5) In orde r to evaluate Φ d , we first q uantify the n umber of nodes φ d ( q ) , with distance 0 ≤ d ≤ p g ( k ) fr om a node i located at ( x i = − 1 , y i = q ) , q ∈ { 1 , · · · , p g ( k ) + 1 }\{ √ g ( k )+1 2 } , in the k th- lev el transmit-cluster . It is clear th at Φ d = P √ g ( k )+1 q =1 ,q 6 = √ g ( k ) +1 2 φ d ( q ) . The fo llowing facts are used to co mpute φ d ( q ) : • Each nod e in the transm it-cluster (except y i = √ g ( k )+3 2 ) has 1 node o f vertical distan ce 0 from it at the r eceiv e- cluster . • If q − d ≥ 1 but q + d > p g ( k ) + 1 , or q − d < 1 but q + d ≤ p g ( k ) + 1 , there is o ne nod e located at d istance d fr om node i . • If q − d ≥ 1 and q + d ≤ p g ( k ) + 1 , there are two n odes at d istance d from no de i . • For all q a nd d , if y j = √ g ( k )+3 2 , th en it c annot be used in computing φ d ( q ) , since by Lemm a 2 y j is removed from the set of receiver ind ices. Hence, we can quantify φ d ( q ) as f ollows: φ d ( q ) = I q − d ≥ 1 \ q + d > p g ( k ) + 1 + I q − d < 1 \ q + d ≤ p g ( k ) + 1 + 2 I q − d ≥ 1 \ q + d ≤ p g ( k ) + 1 − I q + d = p g ( k ) + 3 2 [ | q − d | = p g ( k ) + 3 2 − I d = 0 , where I represents the indic ator fu nction, such that it equa ls to 1 if its con dition hold s and 0 otherw ise. 6 Summarizin g the above, we have Φ d = p g ( k ) − 1 , if d = 0 2 p g ( k ) − 3 , if d = 1 2 p g ( k ) − 2 d − 2 , if 2 ≤ d ≤ √ g ( k ) − 1 2 2 p g ( k ) − 2 d, i f d = √ g ( k )+1 2 2 p g ( k ) − 2 d + 2 , if √ g ( k )+3 2 ≤ d ≤ p g ( k ) . (6) Giv en Φ d , Lem ma 3 below states the scaling law of Tr ( H H ∗ ) . The pr oof is giv en in the ap pendix . Lemma 3: As g ( k ) → ∞ , T r ( H H ∗ ) = X i ∈ T k X j ∈ R k | h ij | 2 = ω ( p g ( k )) . Using the a bove lemmas, we characterize the intra-clu ster commun ication time. During the k th iteration, we den ote by l a [ k ] the m inimum spatial separ ation b etween the inter ferers which are located at tier a and a node inside the r eceiving cluster . Beca use of th e 9- TDMA transmission schem e, there are at most ⌈ 1 3 q N g ( k ) ⌉ tiers during the k th iter ation. In order to obta in an up per-bound on the inter ference, we assume that all of the g ( k ) nod es in an interfere r cluster are located at th e closest b ound ary to the receiv e-cluster R. Therefo re, l a [ k ] ≥ (3 a − 2) p g ( k ) . Hence, the interf erence is upper-bound ed as I k ≤ ⌈ 1 3 q N g ( k ) ⌉ X a =1 8 a P g ( k ) l a [ k ] α ≤ 8 P g ( k ) α 2 − 1 ⌈ 1 3 q N g ( k ) ⌉ X a =1 a (3 a − 2) α < 8 P g ( k ) α 2 − 1 1 + 1 3 ⌈ 1 3 q N g ( k ) ⌉− 1 X a =1 1 (3 a + 1) α − 1 ≤ 8 P g ( k ) α 2 − 1 1 + 1 3 Z ⌈ 1 3 q N g ( k ) ⌉− 1 a =0 1 (3 a + 1) α − 1 da − − − − → N →∞ 8 c 2 P g ( k ) α 2 − 1 , (7) where c 2 is a constant. Eqn. (7) sugg ests the following. By in creasing the size of th e clusters, due to the schedulin g algorith m, the spatial separation o f th e interf erer nod es from the receive-cluster increases. Alth ough th e numb er of nodes inside each c luster is increasing, the overall effect of interferen ce dimin ishes. Hence , in the limit, for large clusters, the co mmunicatio n becomes noise limited . There fore, we h av e the following conclusion . Pr opo sition 1: As g ( k ) → ∞ , du ring a ( k + 1) th-lev el cast, R k Intra = ω (log g ( k )) . Pr oof: The proof imm ediately follows from Lem mas 1 and 3 and the fact th at the interference power tends to 0 as g ( k ) → ∞ . Since the p roposed intra-c luster commu nication uses K iterativ e steps to distribute a ll g ( K ) bits of th e source S to the nodes inside the K th-level c luster , the time required to finish this p hase is T 1 = K X k =1 T k 1 , (8) T T R R R R 1 st Tier Interferer Cluster Potential Receive Rela y- Clusters Active transmit relay- cluster among 25 cluster s { ) ( K g ) ( 2 K g d TR = Fig. 4. Alternate inter -cluste r communication scheme and inte rferer locat ions. where T k 1 represents the time taken to finish the k th iteration . In the k th iter ation, 9 consecutive k th-level casts ar e per- formed , each with a rate of R ( k − 1 ) Intra = ω (log g ( k − 1)) . At th e same time that MIMO tr ansmission is in effect between two neighbo r ( k − 1) th-level clusters of size g ( k − 1) , the ( k − 1) th- lev el transmit-cluster receives new packets to transmit th em to another ad jacent cluster of size g ( k − 1) durin g th e next MIMO transmission. The req uired time to finish the k th iteration is, therefor e, equal to the m aximum o f these two times. Since g ( k − 1 ) L bits are sen t in one sho t during each such tran smission using MIMO co mmunicatio n, we have T k 1 ≤ max(9 g ( k − 1 ) L log g ( k − 1) , 9 T k − 1 1 ) < 9 c 3 Lg ( k − 1) , (9) for a constant c 3 and k > 1 . This can be easily shown by induction since T 1 1 is a constant. This lead s to th e fo llowing conclusion . Pr opo sition 2: T he total required tim e to finish the intra- cluster com munication ph ase is o ( g 2 ( K )) . Pr oof: Sin ce g ( k ) = 3 2 k , the time required to finish th e broadc asting of each n ode’ s pa cket is upper bo unded as T 1 < 9 c 3 L K X k =1 3 2( k − 1) = 9 c 3 L 1 8 ( g ( K ) − 1) . (10) Hence, T 1 = o ( g ( K )) . Since th is step h as to b e repeated g ( K ) times for all of the n odes inside e ach K th-level cluster , the total requ ired time is o ( g 2 ( K )) . B. In ter-C luster Commu nication W e deriv e a lower bound fo r the achiev able rate, denoted R Inter , f or the second phase of the prop osed schem e, by considerin g an alternate in ter-cluster commun ication scheme as shown in Fig . 4, where we assume a o ne-cluster separation between ea ch pair of transmit-rece i ve relay clusters. The capacity result obtained by this alternate scheme can serve as a lower b ound for the original scheme because the d istance between any two n odes within the alter nate scheme is larger than th at in the old scheme . Furthermo re, we observe the following about th e alternate scheme: • The a th-tier interferer nodes are lo cated at a d istance of at least (4 a − 2) p g ( K ) from the destination cluster, for 1 ≤ a ≤ ⌈ √ N 5 √ g ( K ) ⌉ . • A 25-T DMA scheme is used , so there is o ne active transmit relay-cluster among 25 clusters of size g ( K ) (the optimal cluster size). 7 In the following we quantify the interfer ence in e ach cluster , and demo nstrate th at g ( K ) d egrees of fr eedom are achievable in the prop osed MIMO communica tion. The de riv ation of the max imum a mount of in terference for the nodes of each receive cluster f ollows the same lines as (7), and we on ly replace the spa tial separation of 3 a − 2 with 4 a − 2 . It can be e asily verified that as bef ore, by replacin g this new value, th e term inside the summation in (7) approa ches a constant, and we can upper-bound the inter-cluster interference as I Inter ≤ 8 c 4 P (2) g ( K ) α 2 − 1 = 8 c 4 2 α P for a co nstant c 4 . This leads to the f ollowing two lemm as, which were developed in [6] for a dense network but here we show to hold in the e x tended network und er considera tion. The proo fs are given in th e append ix. Lemma 4: The achie ved mu tual infor mation between any pair o f tr ansmit-receive relay-clu sters d uring th e m ulti-hop phase, an d hen ce R Inter , g rows at least linearly with g ( K ) . Lemma 5: Ther e exists a strategy to enco de the observation at each node in the final re ceiv e-cluster at a fix ed rate, Q , and still m aintain th e ab ove linear g rowth of the mu tual informa tion fo r the g ( K ) × g ( K ) quantized MIMO chan nel. W e now summ arize the overall requ ired tim e to complete this p hase in the f ollowing pr oposition: Pr opo sition 3: T he to tal req uired time to co mplete the inter-cluster commu nication ph ase is o ( p N g ( K )) . Pr oof: Dur ing each step of the pro posed 25- TDMA commun ication, 1 25 of the clusters ac t as active sources. Due to Lem mas 4 an d 5, the full spatial mu ltiplexing is achieved in this phase, and at any p oint alon g the ro ute the rate between immed iate adjacen t clu sters is lower -bound ed b y the rate be tween the clu sters located two cluster-hops away . Sinc e C symbo ls are sent over e ach cluster-hop, th e comm unication time between ea ch pair of transmit-r eceiv e relay-clusters scales as T 2 = C g ( K ) g ( K ) = C . There are O ( q N g ( K ) ) cluster-hops between the so urce and the destina tion since th ere are at most a total of q N g ( K ) squares of size g ( K ) along a horizo ntal path as well as a vertical path. Therefor e, the end-to- end communica tion time is upper-bound ed by 25 C q N g ( K ) . W e also shou ld note that there ar e g ( K ) n odes inside each cluster . Therefor e, the total time required to co mplete the inter-cluster c ommun ication is upper-boun ded b y 25 g ( K ) C q N g ( K ) = 25 C p N g ( K ) . C. Message Decoding at the D estination Let I D represent the interferenc e power at any destination node durin g this phase. Follo wing our analy sis of in terference in (7), and due to the 9-TDMA u sed to select th e active K th - lev el clu sters, it is c lear that lim g ( K ) →∞ I D = 0 . Hen ce, the achiev able co mmunic ation rate can b e written as R D = I ( X ; y , H ) = log (1 + P N 0 g ( K ) X l =1 | h lD | 2 ) , where | h lD | 2 is the square amp litude of the channel between any n ode l in th e clu ster and the destination D , and y is the vector of th e re ceiv ed message at the destination. In order to derive a lo w er-bound on R D , we assum e tha t the destination is located o n on e o f the corner s of the cluster . In a regular network , th is cho ice results in the smallest value for P g ( K ) l =1 | h lD | 2 . T o evaluate th is term , we use Fig. 2(a) as an examp le. W e consider the no de located at the up per-right corner . There are 3 no des in 3 squares which are adjacent to the squar e conta ining this node, each located at a distan ce of at most 2 √ 2 f rom the destination. W e call these nodes 1st- tier nodes. Likewise, the 2nd- tier con sists of 5 nodes with a distance of at mo st 3 √ 2 fr om the destination. Generalizin g the idea, it can be verified that in the z th tier, th ere are 2 z + 1 nodes o f distance at least √ 2( z + 1 ) from the destination D . Therefo re, we have lim g ( K ) →∞ g ( K ) X l =1 | h lD | 2 > ∞ X z =1 2 z + 1 ( √ 2( z + 1)) α = ∞ X z =2 1 √ 2 α ( 2 z α − 1 − 1 z α ) = 1 √ 2 α (2 ξ ( α − 1) − ξ ( α ) − 1 ) = c 6 , where ξ is the Riemann-Zeta function. Hen ce, R D is a constant c 6 and do es not scale with th e cluster size. This leads to th e following co nclusion. Pr opo sition 4: T he req uired time to complete the m essage decodin g ph ase is o ( g 2 ( K )) . Pr oof: Based on the r esult o f Lem ma 5 each no de quantizes its observation of the message using a co nstant, Q , bits an d th e communicatio n rate is lower-bounded by a constant, therefo re, the req uired time to finish e ach MI SO transmission to deli ver g ( K ) b its is T 3 < C Qg ( K ) c 6 . Because of the 9-TDMA scheme and the fact th at there are g ( K ) destination node s in side each cluster, the overall r equired time to com plete this step is o ( g 2 ( K )) . D. Constructive Lower -Boun d on the Capa city The lower b ound o n the cap acity can now be derived, since we kn ow th e scaling behavior o f th e req uired time for each phase and th e to tal num ber of bits transmitted in the network. As g ( K ) → ∞ , th e total required time to finish transmitting a p acket using the pro posed c ommun ication sche me is t total = o ( g ( K ) 2 ) + o ( p N g ( K )) + o ( g ( K ) 2 ) = o ( p N g ( K )) + o ( g ( K ) 2 ) . Therefo re, since each nod e sen ds a packet of length g ( K ) and ther e are N nodes in the n etwork, the o verall network capacity can be written as T ( N ) = N g ( K ) t total = N g ( K ) o ( p N g ( K )) + o ( g ( K ) 2 ) . Note th at sin ce we are in terested in the scalin g be havior of th e capacity , our goal is to find K ∗ = V ( N ) = arg max K T ( N ) for some function V . By letting o ( p N g ( K )) = o ( g ( K ) 2 ) , we find the optimal g ( K ∗ ) = c 7 N 1 3 , for some constant c 7 . Substituting this in to T ( N ) , we ha ve the follo wing m ain result. Theor em 1: Assuming α > 2 , the achiev able network throug hput for all sou rce-destinatio n pair s usin g the propo sed 8 algorithm is T ( N ) = ω ( N 2 3 ) with a p ower scaling of P (2) = 2 α P g ( K ) α 2 − 1 = c 8 N α 6 − 1 3 for some constant c 8 . V I . S C A L I N G L AW S F O R R A N D O M N E T W O R K S A. Ra ndom Network with Un it Node Density In th is section, we a ssume that N no des are distributed unifor mly random ly in the area B N with un it den sity and study the achiev able network th rough put. The co mmunica tion algorithm is in natu re the same as tha t o f the case for a r egular network. W e explain the min or differences where app ropriate and der iv e the asymptotic thr oughp ut for th is rand om network. 1) Com munication insid e Squar es: I n a random n etwork, we cannot guar antee tha t each unit area contains exactly on e node. Hence, instead of squares with unit ar ea, we study squares of area A log N , for A > 1 , an d find a tight bound on the n umber of n odes inside eac h such squ are as stated in Lemma 6. W e then apply th e r esults of Section V to this setting. Lemma 6: For all squar es o f area A log N , A > 1 , in dexed as 1 ≤ j ≤ ⌊ N A log N ⌋ , the numb er of nodes, M j , inside ea ch square is in the interval [(1 − δ ) A log N , (1 + δ ) A log N ] , ∀ δ > 0 , with pro bability p → 1 . The pr oof is giv en in the ap pendix . W e a ssume that in stead of p ackets o f len gth g ( K ) L , the nodes transmit their messages in packets of len gth g ′ ( K ) LA log N bits for the case of random networks. Here g ′ ( K ) repr esents the optimal numb er of squ ares with ar ea A log N in side th e cluster . For this topo logy , we add an extra phase bef ore each 1st-level cast of th e intra-c luster commun ication in ord er to distribute each node’ s m essage inside the squar es of ar ea A lo g N . In this phase, each so urce no de transmits a dif ferent sub- block of L bits to each of the A log N − 1 other nod es inside the squ are. As befo re, a 9- TDMA scheme is u sed to determ ine the set of acti ve squares. Within each acti ve squ are of area A log N , only on e no de sends its message at a gi ven time. Therefo re, using a similar an alysis to (7), it is straightf orward to deduce th at th e interf erence tend s to 0 inside each squ are and th e comm unication is lim ited b y no ise as N → ∞ . The distance between any pair of A lo g N n odes lo cated inside each squ are is at most √ 2 A log N . Theref ore, the commun ication rate between ea ch pair is lo wer-boun ded by log (1 + P (2 A log N ) − α 2 ) → P (2 A log N ) − α 2 as N → ∞ . Hence, each n ode can d istribute its packet of length AL log N bits amon g its ne ighbor n odes in the square in c 9 (log N ) 1+ α 2 seconds f or some constant c 9 . 2) Mo dified Thr ee-phase Scheme a nd Capac ity E valuation : The same scheme f or intra-c luster co mmunicatio n can now be used with a slight modification, such that instead of h aving one node in each 0 th-level cluster , we now have A log N no des. I n order to find the topology leading to the lowest communication rate, we follow the lines of analysis in Section V-A with the slight difference that during the k th iteration, we assume all A log N node s inside each square o f area A log N are co- located at the worst-case point, whose location can be f ound similarly to h ow Lem ma 2 is derived. In o rder to der iv e the lower -boun d on the co mmunica tion rate in this case, we also need to consider the fact that the distance between any two n odes is multip lied b y √ A log N c ompared to the case in a regular network. It is clear th at since the squ are area grows with N , th e resulting interference, I k random , during th e k th itera tion ob eys I k random → 0 . Applying the a bove changes to th e numbe r of nodes in each square and their relativ e distance, the result of Pr oposition 1 is mo dified to the following. Pr opo sition 5: I n the random network with unit node d en- sity , as g ′ ( k ) → ∞ , R k Intra = ω (log (1 + g ′ ( k )( A log N ) ( A log N ) α 2 )) . Hence, if g ′ ( k ) = o ((log N ) α 2 − 1 ) , th en R k Intra = ω ( g ′ ( k )(log N ) 1 − α 2 ) ; otherwise, R k Intra = ω (log ( g ′ ( k )(log N ) 1 − α 2 )) . Defining T ′ k 1 similarly to T k 1 in Section V -A, we have the required time to finish the k th iteration T k tot ≤ c 9 (log N ) 1+ α 2 + T ′ k 1 = c 9 (log N ) 1+ α 2 + max(9 AL log N g ′ ( k − 1) R ( k − 1 ) Intra , 9 T ′ k − 1 1 ) ≤ c 10 (log N ) α 2 g ′ ( k ) . The first term in the above sum mation accoun ts for th e required time to propag ate the message in side the squ ares of area √ A log N . The second term has th e same stru cture as (9). T he last in equality follows fro m induction and the fact that T ′ 1 1 ≤ c 10 (log N ) α 2 . From this, we obtain the fo llowing conclusion . Pr opo sition 6: T he to tal time req uired to co mplete the intra-cluster commun ication phase in a ran dom n etwork with unit no de density is o ((log N ) α 2 +1 g ′ 2 ( K )) . Pr oof: Along the sam e line as (10), an d by rep lacing T k tot < c 10 (log N ) α 2 g ′ ( k ) , it is clear th at T ′ 1 = K X k =1 T k tot = o ((log N ) α 2 g ′ ( K )) . Since th ere are g ′ ( K ) A lo g N nodes inside each clus- ter , the overall required time to finish this phase is o ((log N ) α 2 +1 g ′ 2 ( K )) . The in ter-cluster com munication and message-decoding phases ar e almost identica l to the regular network case. At the beginn ing o f the inter-cluster com munication , within eac h cluster of size g ′ ( K ) A lo g N th ere are Ag ′ ( K ) log N nodes. By u sing Lemmas 4 and 5, it is clear th at th e ach iev ed capacity in this phase, R Inte r , gro ws at least linearly with g ′ ( K ) log N an d the power constrain t in th is ph ase is P (2) = 2 α P ( g ′ ( K ) log N ) α 2 − 1 . Hence, we h av e Pr opo sition 7: I n the random network with unit node d en- sity the total required time to complete inter-cluster com mu- nication is o ( p N g ′ ( K ) log N ) . The r equired time for decodin g at the destina tion clu ster follows fro m th e a nalysis in Section V -C. I t can b e sh own that we can maintain a co nstant ra te R D of co mmunica tion, and 9 therefor e the re quired time to complete MI SO co mmunicatio n is T ′ 3 = C Qg ′ ( K ) log N R D = o ( g ′ ( K ) log N ) . Hen ce, we have Pr opo sition 8: I n the random network with unit no de den- sity th e total requ ired time to complete the message decod ing phase is o ((log N ) 2 g ′ 2 ( K )) . W e can now write the total co mmunicatio n time fo r a random n etwork as t ′ total = o ( p N log N g ′ ( K )) + o ((log N ) α 2 +1 g ′ 2 ( K )) , and th e network through put is given by T ( N ) = N ( g ′ ( K ) log N ) o ( p N log N g ′ ( K )) + o ((log N ) α 2 +1 g ′ ( K ) 2 ) . T o maximize T ( N ) , we set o ( p N log N g ′ ( K )) = o ((log N ) α 2 +1 g ′ 2 ( K )) . The refore, the optimal cluster size g ′ ( K ) log N is c 11 N 1 3 (log N ) 2 − α 3 , for a constant c 11 . Hence, we o btain the following main r esult for a ra ndom ne twork. Theor em 2: In th e r andom network with unit node d ensity assuming α > 2 , the achievable network thro ughpu t for all source-destination pairs using the pro posed algorithm is T ( N ) = ω N 2 3 (log N ) 2 − α 6 with a req uired power scaling of P (2) = 2 α P ( g ′ ( K ) log N ) α 2 − 1 = c 12 N α 6 − 1 3 (log N ) − ( α − 2) 2 6 for som e con stant c 12 . B. Ra ndom Network with Den sity λ = Ω(log N ) W e can use a similar algorithm as Section VI-A to find constructive lower - bound s on the capacity scaling behavior of an extende d network with a n ode density λ = Ω (lo g N ) . Lemma 7: For all squa res of unit area indexed as 1 ≤ j ≤ N , if λ = Ω(log N ) , the number of n odes, M j , inside the square is in the interv al [(1 − δ ) λ, (1+ δ ) λ ] , ∀ δ , with probab ility p → 1 . Pr oof: T he p roof is similar to the pr oof of Lemma 6. The probab ility of ly ing in a square o f u nit ar ea equals P ( S i = 1) = 1 N . He re, S = P λN i =1 S i represents the n umber of no des inside a unit squ are and we hav e p [ S < (1 − δ ) λN P ( S i = 1)] = p [ S < (1 − δ ) λ ] < e − λ δ 2 2 . Using the u pper-bound version o f the b ound we have, p [ S > (1 + δ ) λN P ( S i = 1)] = p [ S > (1 + δ ) λ ] = e − λf ( δ ) . If we c hoose λ ≥ A log N for A > max( 2 δ 2 , 1 f ( δ ) ) , with proba bility 1 the nu mber of no des M j inside all un it square s follows (1 − δ ) λ < M j < (1 + δ ) λ , 1 ≤ j ≤ N and ∀ δ > 0 . As op posed to squares of area A log N in the p revious section, th e base squar es of unit a rea are consider ed and the nodes transmit their messages in packets of length λLg ( K ) . By employing the 9-TDMA communication, interferen ce tend s to a constant inside each unit s quare. The distance between an y pair of λ nodes located inside each u nit square, is at most √ 2 . Therefo re, a con stant communica tion rate between each p air is achieved inside the square, and e ach node can transmit λL bits to its neighb or n odes in c 13 λ seco nds for some co nstant c 13 W e replicate the analysis d one in (7 ) a nd co nsider the fact that instead of g ( k ) nodes, the k th-level cluster c onsists o f λg ( k ) no des. Th erefore, by mo difying (7) we can show that the interf erence I k random during th e k th iteration o beys I k random ≤ 8 P c 2 λ g ( k ) α 2 − 1 . (11) If g ( k ) = o ( λ 2 α − 2 ) ( high interferen ce regime) th e rate of the k th-level cast scale s as ω (log ( g ( k ))) , and if g ( k ) = ω ( λ 2 α − 2 ) , since lim g ( k ) →∞ I k random → 0 the rate scales a s ω (lo g ( λg ( k ))) . In th e k th iteration, a ( k − 1) -le vel cluster transmits 3 2( k − 1) λL bits to one of its neighbors, and usin g the same line of re asoning that we used to der i ve T k tot in Section VI -A, we h av e T k tot ≤ c 13 λ + T ′ k ≤ c 13 λ + max(9 λLg ( k − 1) log g ( k − 1) , 9 T ′ k − 1 1 ) ≤ 9 c 14 λLg ( k − 1) . Pr opo sition 9: T he total time r equired to finish the intra- cluster comm unication ph ase in a rand om ne twork with den - sity λ = Ω(log N ) is o ( λ 2 g 2 ( K )) . Pr oof: Alon g the same line as (9), and by replacing T k tot < 9 c 14 λLg ( k − 1) , it c an be deduce d that T 1 = o ( λg ( K )) . There are λg ( K ) no des inside eac h c luster of size g ( K ) , therefor e, the overall r equired time to finish this p hase is o ( λ 2 g 2 ( K )) . The achieved capacity in the inter -cluster phase, R Inte r , grows at least linearly with λg ( K ) and the power constraint in this phase is P (2) = 2 α P g ( K ) α 2 − 1 . Pr opo sition 10: Th e to tal required time to finish the inter- cluster comm unication (routing) in a r andom network with node den sity λ = Ω(log N ) is o ( p N g ( K ) λ ) . Pr oof: T he pr oof follows from the pro of o f Prop osition 3 and the fact that th ere are λg ( K ) n odes in each c luster instead of g ( K ) nodes. T o e valuate the required time for message decodin g at the destination cluster, it can b e easily shown that in the MISO analysis, th e lower-bound on the sum P λg ( K ) l =1 | h ld | 2 equals c 15 λ , since in the worst case scenario, in tier z all the (2 z + 1) λ nodes are located at the distanc e ( z + 1) √ 2 from the destination. For the interfer ence analysis, con sidering (11) an d replacin g k = K , we again have two p aradigms. I f λ = o ( g ( K ) α 2 − 1 ) , I D → 0 , o therwise I D = o ( λ g ( K ) α 2 − 1 ) . The rate of commun i- cation in the first case obeys R D ≤ log(1 + P c 15 λ N 0 ) , and in the second ca se it obeys R D ≤ log(1 + c 15 λ λ g ( K ) α 2 − 1 ) = o (log g ( K )) . In bo th cases, T 3 = λg ( K ) C 2 R D = o ( λg ( K )) . Hence, Pr opo sition 11: Th e total r equired tim e to fin ish th e mes- sage decod ing ph ase in a r andom network with node density λ = Ω (lo g N ) is o ( λ 2 g ( K ) 2 ) . 10 W e can now write the total comm unication time for this setting as t ′ total = o ( p N g ( K ) λ ) + o ( λ 2 g ( K ) 2 ) . The n etwork throug hput in this case fo llows T ( N ) = ( λN )( g ( K ) λ ) o ( p N g ( K ) λ ) + o ( λ 2 g ( K ) 2 ) . T o ma ximize the throu ghput we set o ( p N g ( K ) λ ) = o ( λ 2 g ( K ) 2 ) . Therefore, the clu ster size in this case can be expressed as c 16 N 1 3 λ 2 3 . The optimal clu ster si ze decreases by increasing the n ode d ensity , whic h is expected sin ce a clu ster of area g ( K ) h as more n odes co mpared to th e case of regu lar networks due to hig her n ode density an d as a result the same degrees of freedom can be achiev ed in a smaller area. Theor em 3: The ach ie vable ne twork throughp ut assuming α > 2 fo r all po ssible source-destination pa irings and u sing the propo sed algorithm for rando m networks with λ = Ω(log N ) follows T ( N ) = ω (( λN ) 2 3 ) with a required power scaling of P (2) = 2 α P g ( K ) α 2 − 1 = c 17 N α 6 − 1 3 λ α 3 − 2 3 . V I I . C O N C L U S I O N In this paper we stud y the commun ication amon g no des in an extended network, where both sign al in terferenc e and power decay are limiting factors of the network capacity . Through the asymptotic an alysis o f a pro posed thr ee-phase com munication scheme, we q uantify h ow the ap propr iate combination of nod e cooper ation, in the fo rm of distributed v irtual an tenna array s, and multi-h op message relay ing, am ong op timally sized clus- ters of nodes, can incr ease the ne twork through put. The use of spatially separated clusters o f distributed an tennas brings benefits from both the spa tial multiplexing gain of M IMO and the mitigation of inter ference. At the same time, multi-hop commun ication among the clusters allo ws significant p ower scaling ad vantage over d irect MIMO commun ication b etween the source and destination c lusters. The deriv ed asy mptotic throug hput of the propo sed co mmunicatio n schem e provides a con structive lower boun d to the capacity of an extended network with node coo peration. A P P E N D I X A P R O O F O F L E M M A 1 From linear a lgebra it is well known that the deriv ati ve of the determina nt of a squ are matrix, A , can be written as d det( A ) = Tr ( adj ( A ) dA ) = det( A ) tr ( A − 1 dA ) fo r an in vertible matrix A . Using T aylor series expan sion, we have det( A + δ X ) = de t ( A ) + Tr ( adj ( A ) X ) δ + O ( δ 2 ) , f or sma ll δ an d matrix X . Th e last ter m is obtain ed by comp uting the second or der derivati ve of the deter minant. Therefo re, we can simplify the argumen t of the lo g fu nction in the g iv en capacity expression as fo llows, de t( I + P N 0 + I H H ∗ ) = det ( I ) + det( I ) Tr ( I − 1 P N 0 + I H H ∗ ) + O ( δ 2 ) = 1 + Tr ( P N 0 + I H H ∗ ) + O ( δ 2 ) . Sinc e h ij < 1 2 α 2 , we can choose δ = 1 2 α . A P P E N D I X B P R O O F O F L E M M A 2 There are p g ( k ) transmitter nodes (at x t = − 1 ) and p g ( k ) receiver nodes (at x r = 1 ), an d p g ( k ) + 1 horizo ntal locations for th e n odes to be placed. Ther efore, we need to cho ose on e of the indices on each side and rem ove it fro m the s et of node locatio ns. T o minimize P i ∈ T k P j ∈ R k | h ij | 2 , we shou ld choose the index i on the transmit side and j on the receive side fo r wh ich the sums P g ∈ R k | h ig | 2 and P g ∈ T k | h gj | 2 are maximized, a nd remove them f rom th e index set. The ind ex i ch osen to be removed f rom the transmitter set is th e one wh ich results in the largest n umber of r eceiv er indices with small vertical distan ce from node i . It is po ssible for at most two distinct nodes with indices in the receiv e- cluster to have a com mon d istance from a node with ind ex i in the transmit-clu ster . Choosing i such th at y i = √ g ( k )+1 2 or y i = √ g ( k )+3 2 , results in having a n ode which has the largest number o f receiver nodes with small distanc es fro m it. (For example, th is is equi valent to choo sing y i = 5 or y i = 6 in Fig. 1 (b )). Let’ s set i = √ g ( k )+1 2 . By symmetry , the rem oved index in the receive-cluster equa ls to one o f the above g iv en indices. Choosing j = √ g ( k )+3 2 instead o f j = √ g ( k )+1 2 results in r emoving cha nnels with larger amplitud es fr om P g ∈ T k | h gj | 2 . Swapping the values of i an d j results in the same achievable rate. A P P E N D I X C P R O O F O F L E M M A 3 W e ev alu ate lim g ( k ) →∞ P √ g ( k ) d =0 u ( d )Φ d . For g ( k ) → ∞ , the second term in (5) approa ches 0 an d we h av e lim g ( k ) →∞ u ( d ) → c 1 (4+ d 2 ) α 2 . Using (6), for d > 0 , Φ d ≥ 2 p g ( k ) − 2 d − 2 . There fore, we have lim g ( k ) →∞ P √ g ( k ) d =0 u ( d )Φ d ≥ lim g ( k ) →∞ P √ g ( k ) d =0 c 1 (4+ d 2 ) α 2 Φ d > c 1 2 α (2 p g ( k ) − 2) + 2 p g ( k ) P √ g ( k ) d =1 c 1 (2+ d ) α − J → C p g ( k ) , where the last equality follows from the fact th at P √ g ( k ) d =1 − 2 d − 2 ( d +2) α in limit tends to a c onstant, J , and P √ g ( k ) d =1 c 1 (2+ d ) α can be written in terms of the Riemann- Zeta fu nction with a con stant a rgument. Therefo re, the final result h olds for so me constant C . A P P E N D I X D P R O O F O F L E M M A 4 This result is in essence similar to Lemma 4.3 of [6 ]. W e only n eed to establish a f ew facts here. The minimu m distance between a pair of nod es, i ∈ T an d j ∈ R , is p g ( K ) , an d the maximum o f such a distance equ als p 10 g ( K ) . Furth ermore, the distance b etween th e center o f tr ansmit- and rec ei ve- clusters eq uals d T R = 2 p g ( K ) . The refore, d ij follows 1 2 d T R ≤ d ij ≤ √ 10 2 d T R , and hen ce, d − α 2 ij = d − α 2 T R ρ ij , for ρ ij ∈ [( 2 √ 10 ) α 2 , 2 α 2 ] . By treating the interference as a sour ce of noise, and based on our assumption that P (2) = 2 α P g ( K ) α 2 − 1 , th e 11 mutual info rmation b etween the two clu sters ca n be wr itten as R Inter = I ( X ; Y , H ) = log det( I + P (2) N 0 + I Inter H H ∗ ) ≥ log det( I + 2 α P g ( K ) α 2 − 1 N 0 + 8 c 4 2 α P H H ∗ ) = log det( I + P c 5 g ( K ) F F ∗ ) , where X , Y , and H are respectively the c orrespon ding inp ut, output, and chann el m atrices, F is a g ( K ) × g ( K ) matrix with elements F ij = ρ ij e θ ij , a nd c 5 is a con stant. The rest of the prob lem has the same struc ture as Lemma 4.3 in [6] and the linearity of the rate g rowth with the numb er of distributed antennas follows fro m there. A P P E N D I X E P R O O F O F L E M M A 5 The p roof fo llows fro m Lemm a 4.4 of [6] and the fact th at the recei ved power P r at an y node j in the receive-cluster follows P r = P g ( K ) i =1 P (2) | h ij | 2 ≤ P g ( K ) i =1 P (2) 1 g ( K ) α 2 = 2 α P g ( K ) α 2 − 1 P g ( K ) i =1 1 g ( K ) α 2 = 2 α P , w hich is a constant. A P P E N D I X F P R O O F O F L E M M A 6 Assuming that there are N n odes distributed unif ormly over B N , for each node we define the random v ariable S i to be equal to 1 if it lies in a given sq uare with area A log N and 0 otherwise. Clearly , P ( S i = 1) = A log N N . Using Cherno ff ’ s bound s for bin omial rand om variable S = P N i =1 S i , which represents the n umber of no des inside a squ are, we have p [ S < (1 − δ ) N A log N N ] = p [ S < (1 − δ ) A log N ] < e − A log N δ 2 2 = N − A δ 2 2 , and, f urthermo re, p [ S > (1 + δ ) N A log N N ] = p [ S > (1 + δ ) A log N ] < e − A log N f ( δ ) = N − Af ( δ ) , where f ( δ ) = (1 + δ ) log (1 + δ ) . T o gu arantee that the number o f nodes inside all the squar es o beys these inequalities, we use the unio n bound of the probab ilities. It directly f ollows that if A > max( 2 δ 2 , 1 f ( δ ) ) , with pro bability 1 the nu mber of n odes M j inside all squar es of a rea A log N follows (1 − δ ) A log N < M j < (1 + δ ) A log N , 1 ≤ j ≤ N and ∀ δ > 0 . R E F E R E N C E S [1] P . Gupta and P . Kumar , “The ca pacit y of wireless netw orks, ” IEE E T ransaction s on Information Theory , vol. 46, pp. 388–404, March 2000. [2] A. Jovicic , P . Vi swana th, and S. R. Kulkarni, “Upper bounds to transport capac ity of wireless networ ks, ” IEE E T ransac tions on Informatio n Theory , vol. 50, pp. 2555–2565, November 2004. [3] O. Lev eque and I. E. T alatar , “Information-the oreti c upper bounds on the capac ity of lar ge exte nded ad hoc wireless netw orks, ” IEE E T ransact ions on Information Theory , vol. 51, March 2005. [4] L . L. Xie an d P . R. Kumar , “On the path-loss att enuat ion regi me for positi ve cost and linear scaling of transport capacity in wireless netw orks, ” J oint Special Issue of IEE E T ransactio ns on Information Theory and IEEE/ACM T ransactions on Networking on Networking and Informatio n Theory , vol. 52, pp. 2313–2328, June 2006. [5] D. Tse and P . V iswanat h, Fundamentals of W ir eless Communicati on . Cambridge Univ ersity Press, May 2005. [6] A. Ozgur , O. Lev eque, and D. Tse, “Hierarch ical cooperation achie ves linea r capacity scaling in ad-hoc networks. ” in Pr oc. IEEE Infocom 2007 also in the IEEE T ransaction s on Information Theory , December 2007. [7] S. V akil and B. Liang, “Eff ect of joint cooperati on and multi-hoppin g on the capac ity of wireless networks, ” in Proc . IEEE Communicat ions Societ y Confer ence on Sensor , Mesh and Ad Hoc Communicati ons and Network s (SECON) , June 2008. [8] L . L. Xie and P . R. Kumar , “ A netwo rk information theory for wireless communicat ions: Scali ng la ws and optimal operation, ” IEEE T ransac - tions on Information Theory , vol. 50, pp. 748–767, May 2004. [9] S. T oumpis and A. J. Goldsmith, “Large wireless networks under fading, mobility , and delay constraints, ” in P r oc. IEE E Infocom , March 2004. [10] M. Franceschetti , O. Dousse, D. N. C. Tse, and P . Thiran, “Closing the gap in the capacit y of wireless networks via percolati on theory , ” IEEE T ransaction s on Information T heory , vol. 53, pp. 1009–1018, March 2007. [11] M. Gastpar and M. V etterli , “On the capaci ty of wireless netw orks: the relay case, ” in Proc. IEEE Infocom , June 2002. [12] S. Aeron a nd V . Saligrama, “W ireless ad hoc networks: S trate gies and scaling la ws for the fixed SNR regime, ” IEEE T ransacti ons on Informatio n Theory , vol. 53, pp. 2044–2059, June 2007. [13] I. E. T elatar , “Capac ity of multi-anten na Gaussian channels, ” Eur opean T ransaction s on T elecommunica tion , vol. 10, pp. 585–595, Nov ember - December 1999. PLA CE PHO TO HERE Sam V akil recei ved the B.Sc. degree in Electrical Engineeri ng from Sharif Uni ve rsity of T echnol ogy in T ehran, Iran, in 2002 and the M.E ng degre e in Electric al E nginee ring from McGill Univ ersity in Montreal , Canada, in 2004. He is now pursuing the Ph.D. degree in Electric al & Computer Engineering at the Unive rsity of T oronto. His current research intere st includes the design and analysis of cooper- ati ve communicati on protocol s for wirele ss ad-hoc and wireless networ ks. PLA CE PHO TO HERE Ben Liang recei ved honors simultaneous B.Sc. (valed ictori an) and M. Sc. degrees in elect rical enginee ring from Polytechn ic Uni ver sity in Brooklyn, New Y ork, in 1997 and the Ph.D. degre e in electric al engineering with computer s cienc e minor from Cornell Univ ersity in Ithaca, Ne w Y ork, in 2001. In the 2001 - 2002 academic year , he was a visiti ng lect urer and post-doc toral research associat e at Cornell Uni ve rsity . He joined the Departmen t of E lectri cal and Computer Engineering at the Univ ersity of T oronto in 2002, where he is no w an Associat e Professor . His current research interests are in m obile netw orking and multimedia systems. He won an Intel Foundation Graduate Fello wship in 2000 to ward the completion of his Ph.D. disserta tion and an Early Researcher A ward (ERA) give n by the Ontario Ministr y of Research and Innov ation in 2007. He was a co-author of the Best Paper A ward at the IFIP Networki ng confer ence in 2005 and the Runner -up Best Pap er A ward at t he Inter nation al Conferen ce on Qualit y of Servic e in Hete rogeneo us W ired/ W ireless Networ ks in 2006. He is an editor for the IEE E Transa ctions on Wire less Communications and an associate editor for the Wile y Security and Communication Networks journal . He serves on the organiz ationa l and techni cal committees of a number of confere nces each year . He is a senior member of IE EE and a member of AC M and T au Beta Pi.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment