Next Challenges in Bringing Artificial Immune Systems to Production in Network Security
The human immune system protects the human body against various pathogens like e.g. biological viruses and bacteria. Artificial immune systems reuse the architecture, organization, and workflows of the human immune system for various problems in comp…
Authors: Michael Hilker
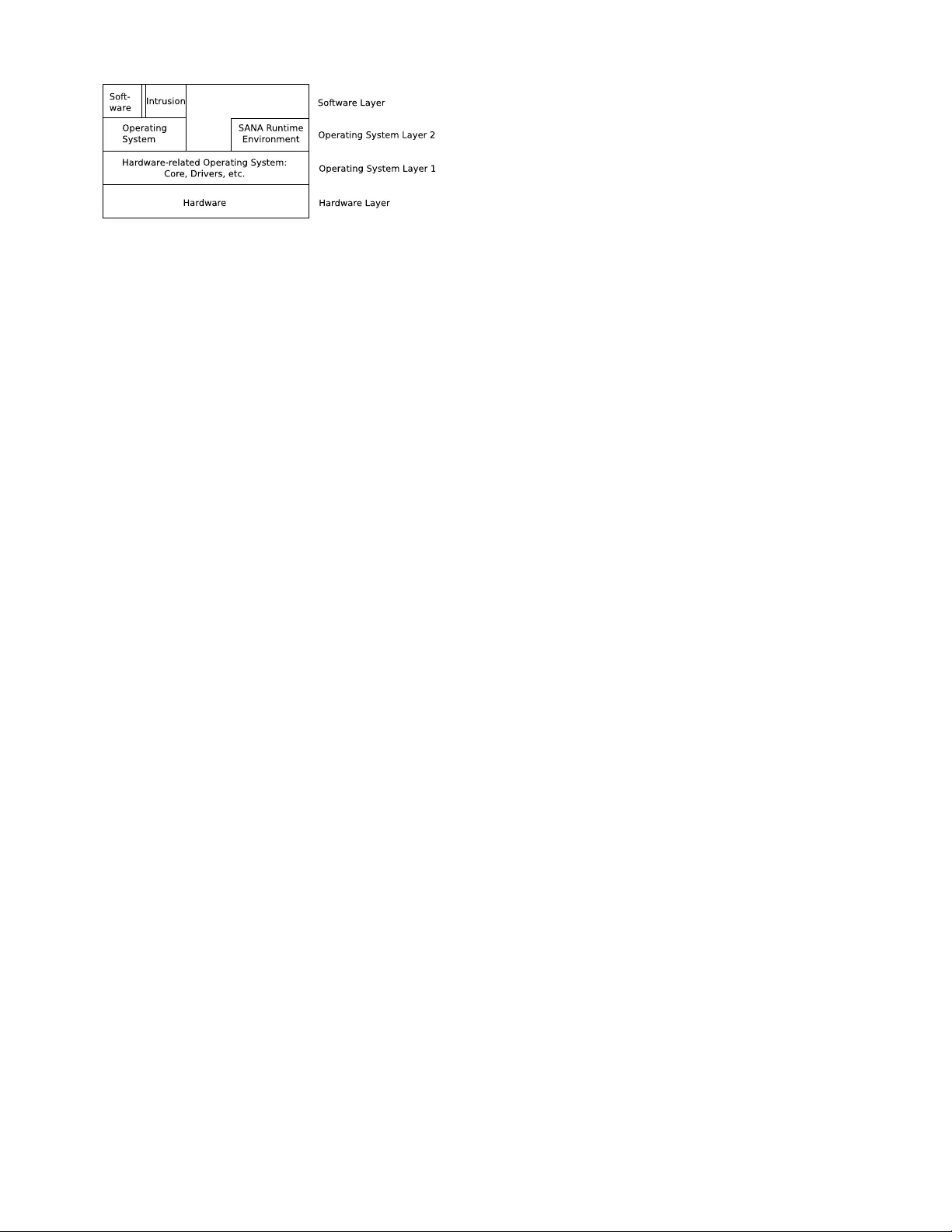
Ne xt Challenges in Bringing Ar tificial Imm une Systems to Pr oduction in Netw ork Security Michael Hilker University of Luxembourg 6, Rue Richard Coudenhove-Kalergi 1359 Luxembourg michael.hilker@uni.lu ABSTRA CT The h uman imm une system protects the h uman bo dy against v arious pathogens lik e e.g. biological viruses and bacteria. Artificial immune systems reuse the architecture, organiza- tion, and w orkflo ws of the h uman immune system for v arious problems in computer science. In the netw ork security , the artificial immune system is used to secure a net w ork and its nodes against in trusions lik e viruses, worms, and tro jans. Ho w ever, these approaches are far aw a y from pro du ction where they are academic pro of-of-concept implementat ions or use only a small part to protect against a certain in- trusion. This article discusses the required steps to bring artificial immune systems into pro duction in the netw ork securit y domain. It furthermore figures out the challenges and pro vides the description and results of the protot ype of an artificial immun e system, which is SANA called. Categories and Subject Descriptors I.2 [ Artificial Intelligence ]: Distributed Artificial Intelli - gence; C.2.4 [ Distributed Systems ]: Distributed Applica- tions— deployment, administr ation, self-management K eywords Net w ork Security , Artificial Imm une Systems, Bio-Inspired Computing, Distributed Systems 1. INTR ODUCTION Net w ork securit y is the domain where a net w ork is pro- tected against in trusions. These in trusions are automatic attac ks lik e viruses, w orms, and tro jans as wel l as man ual attac ks p erformed b y hac k ers or normal users trying to gain access to resource s where they normally hav e no access. Dif- feren t v arious protection systems try to protect the netw ork and its no des where the protection system consists of sev eral protection comp onents. The protection comp onents are a soft w are or hardware solution using a specific type of tasks Permission to make digital or hard copies of all or part of this work for personal or classroom use is granted without fee provided that copies are not made or distributed for profit or commercial advantage and that copies bear this notice and the full citation on the first page. T o cop y otherwise, to republish, to post on servers or to redistribute to lists, requires prior specific permission and/or a fee. BIONETICS 2007 December 10-12, 2001, Budapest, Hungary Copyright 200X A CM TB A ...$5.00. for detecting a set of in trusions. Examples are the host- based antivirus softw ares, firewa lls, and malew are guards or the net w ork-based pac k et filters and in trusion detection sys- tems (IDS) [21]. These components run different tasks like observing the fi le access and system calls on a no de or header and conten t scanning of pac k ets. The protection system is mostly a collection of protection comp onents lac king of col- laborative w ork and sophisticated information managemen t in order to iden tify upcoming more and more intelligen t and adaptiv e intrusions. The systems do not c hec k itself or use the information in order to identify infected nodes - no des with a running intrusion -, not proper w orking comp onents, and abnormal b eha vior. No v el approac hes are the artificial imm une systems. These systems reuse the arc hitecture, organization, and workflo ws of the human immune system for v arious domains in com- puter science where this article fo cusses on the netw ork se- curit y domain. Ho w ever, the curren t approac hes in artifi- cial imm une system are far aw a y from productive w ork and mainly implement a few parts of the human immun e system as an academic proof-of-concept implementation, whic h fo- cus on detecting a certain intrusion. The steps to bring an artificial imm une system in to production so that the secu- rit y systems profit from the adv an tages are discussed in this article. Afterwards, the protot yp e SANA of an artificial im- m une system is in tro duced and its results in different attac k scenarios are discussed. 2. THE NETWORK SECURITY DOMAIN In the netw ork securit y domain is the goal to identify the in trusions using protection systems; a great o verview about net w ork security is in the bo ok [24]. The protection systems consist normally of the following protection component s: An tivirus Softw are The antivirus soft w are observ es a node whether an infected file is accessed or a suspicious sys- tem call o ccurs. The in trusions are mostly described using a signature where pattern matc hing is us ed. When an intrusion is found asks the an tivirus softw are the user how to proceed. Firew all The netw ork traffic consists of pack ets where the firew all analyses the pack et header in order to find in- trusions. When an intrusion is found is the user con- sulted for further steps. P ac k et Filter In t he netw ork equipment is the pac ket filter installed. It analyses the pac ket header for in trusions. F urthermore, it defines a netw ork security p olicy with allo w ed and disallow ed traffic, i.e. allo w ed and disal- lo w ed p orts and netw ork protocols. In trusion Detection System Imp ortant no des - e.g. In- ternet gatew a y and email server - require additional support because they are more likely an aim for attack- ers than normal no des. Therefore, in trusion detection systems are used, which c hec k each pack et completely , observ e the no de for suspicious behavior, and report w arnings and alerts directly to the administ rator [3, 5, 21]. Other Systems Different other protection systems exist, whic h p erform certain tasks for netw ork securit y . Ex- amples are virus throttles slowing down the propaga- tion of viruses [27] or automatic analyzing systems of infected nodes [20]. The protection system defines the used protection comp o- nen ts, the configuration, and the w orkflows. Additionally , it defines in whic h w a y the administrator main tains the net- w ork, keeps the system up-to-date, and the resp onse work- flo ws when an intrusion is iden tified. Curren t protection systems use a fully centralized appro- ac h. Each no de of the netw ork has one or more client soft- w ares, which are administrated using a single managemen t serv er - cl ient -serv er architecture. The administrator installs and configures in eac h no de antivirus soft w are and firewall, in the net w ork equipment the pack et filters, and in imp or- tan t nodes the IDS. The client softw ares are the already described comp onents and observ e the no de for suspicious behavior. The alerts - e.g. identification of an in trusion - are sent to the user of the node, who decides ho w to pro- ceed. The wa rnings are sent to the managemen t server and are manually ev aluated by the administrator. The man- agemen t server co ordinates the client softw are in providing updates and administrative tasks. It also chec ks the no des whether the client softw are runs or not. The differen t clien t soft w ares do not collab orate as well as the messages from differen t no des are not combined ev aluated in order to iden- tify abnormal b ehavior. F urthermo re, the system do es not c hec k itself for the ident ification of not proper working or outdated components and it has serious problems with in- fected no des. F or the ev aluation of protection system exist differen t cri- teria [5, 19]: Completeness The protection system should secure the nodes of the net w ork. F urthermore, it should secure all no des against all known in trusions. Pro duction T oleran t The pro duction i n the netw ork sho- uld not be influenced b y the securit y system - reducing of the false-p ositiv es. Efficiency The resources should b e used efficiently so that the protection system do es not require too man y re- sources. F urthermore is this imp ortant to solv e the pac k et loss problem where IDS stop chec king pack ets when a certain load is reached [22]. Easy Usage The security system should use as many pos- sible automatic w orkflo ws so that the administration is reduced. Self-Chec king The system should chec k itself regularly in order to iden tify infected nodes, not proper workin g or outdated securit y comp onen ts, and abnormal b ehavior in the netw ork. Adaptiv ely In order to iden tify the curren t intrusi ons as w ell as modified and no vel intrusions, the security sys- tem should adapt to the current situation and provide adaptiv e workfl ow s to identify no vel intru sions. Coping with upcoming In trusions Nov el intrusions an- alyze the protection system and use weak p oint s, cam- ouflage itself so that it cannot b e detected an ymore, and so cial engineering is more and more used where the normal users are mislead to provide interna l infor- mation as e.g. passw ords. Implemen tation, Maintenance, Up dates, Extension These p oints should be simplified so that the admin- istrator is able to in troduce no v el tec hniques and up- dates in to the system quickly . The system should chec k and repair itself, and the implementation should b e fast. In addition, the system should pro vide a status snapshot when the administrator demands it. In the net w ork securit y domain, common used protection systems use a cen tralized appro ach using th e client-serv er ar- c hitecture. The clien ts demand information from the serv er and the clients p erform the tasks with a reporting to the serv er. Current protection systems hav e serious problems in eac h of th ese criteria a nd in co ping with upcoming more and more in telligen t and adaptive intrusions. Examples of these in trusions are the theoretical bradley virus [7] and meta- morphic or polymorphic viruses that change its signature in ev ery propagation [25]. The emerges out of the static ar- c hitecture with standard pattern matching algorithm. Thus no v el approac hes should dynamically adapt to the curren t situation and p erform different analysis and com bine the re- sults and information to identify nov el intrusions. Existing artificial immune systems for the netw orks security domain are discussed in the next section. 3. AR TIFICIAL IMMUNE SYSTEMS FOR NETWORK SECURITY The artificial imm une system is a modeling of the h uman imm une system for a specific application domain; in this article the domain is netw ork security . Details about the h uman imm une system are not explained in this article and it is referred e.g. to [16]. In the design and implementation of an artificial imm une system, mostly a few parts of the h uman immune system are mo deled. The article [8] defines and ev aluates four different methods approac hing from the researc h in artificial immune systems [6]: Artificial Negative and Positiv e Selection The artifici- al cells are generated randomly and are afterw ards ev aluated whether they are toleran t to normal netw ork traffic or not - negative selection - and whether they detect abnormal netw ork traffic or not - p ositive selec- tion. Danger Theory The idea is that the artificial cells release signals describing their status, e.g. safe signals and danger signals. The v arious artificial cells use the sig- nals in order to adapt their b ehavior. Artificial Clonal Selection and Hypermutation The artificial cells resp ond when an in trusion is found: it firstly copies itself hea vily so that the num ber of this artificial cell increases and the intrusion is found in sev eral no des. Second, the artificial cell mutate in or- der to iden tify the intrusion more prop erly , e.g. in adapting the int ernal patterns for finding intrusions. Artificial Immune Netw orks These net w orks describ e a mathematical mo del of an tibo dies and an tigens that bind and in terfere each other. The system reacts to the current situation of bindings and its strength. In [8] is stated that these four methods are the most promising as w ell as no v el approaches of the artificial im- m une systems, whic h are significan t different to existing ap- proac hes of computer science in gen eral. How ev er, the nega- tiv e selection is not a ppropriate for anomaly detection - iden - tification of intrusions according to b ehavior analysis [23]. The organization of the imm une system is important and differen t to the curren t protection systems in net w ork secu- rit y: the imm une cells work autonomously as a mobile entit y . The w orkflows are fragmen ted in differen t small tasks, w hic h are performed by different cells. The high n um ber of cells ensures redundancies so that a partly breakdo wn does not influence the performance of the o v erall system. The lymph nodes are a meeting p oin t betw een v arious cells and they respond to even ts in the net w ork through releasing immune cells and antigens. The b one marro w and th ymus releases con tin uously no vel immune cel ls in order to keep the popula- tion up-to-date. The cell comm unication enables the collab- oration betw een imm une cells and the system manages itself so that the whole bo dy is secured. The self-c hec king and -healing iden tifies and remov es not proper w orking immu ne cells. This organization should b e used when an artificial imm une system is deploy ed so that the fault tolerance and redundancies are av ailable. F or the netw ork securit y domain exist different approaches to use an artificial immune system or algorithms motiv ated b y the human imm une system: AR TIS/LISYS This artificial immun e system secures a broadcast netw ork against intrusions. The artificial cells reside in the nodes and c hec k the n etw ork pack ets for certain patterns. A pattern is a string con taining the information ab out the source- and destination IP and p ort as well as the used netw ork proto col. The artificial cells are generated according to the h uman imm une system: the cells are randomly generated and the appropriate cells a re selected using the p ositive and negativ e selection. More details ab out this approach can b e found e.g. in [15]. LIBTISSUE Aic k elin and his team implemented this arti- ficial immune system si mul ator in a client/serv er arc hi- tecture [2, 26]. The data collector are distributed o ver the clien ts and the analyzing part is cen tralized in the serv er. Herein, e.g. the den tritic cells of the innate im- m une system are implemented [9, 10] and approaches of the danger mo del [1]. CIDS Dasgupta introduces approaches to use an artificial imm une system in the netw ork security domain [4]. The used archit ecture is a m ulti-agen t system with roaming agents performing different tasks. How ev er, the architectu re is different to the human imm une sys- tem. Other approaches Other artificial immune systems for net- w ork security fo cus mostly on the multi-agen t architec- ture without the biological-motiv ated architecture. In some approac hes are e.g. a broadca st net w ork used so that the artificial cells m ust not mo v e or only the cap- turing of information is distributed and the analysis is cen tralized. An example is explained in [11] discussing the generation of immune algorithms for ev olutionary detectors but the orga nization of the system i s not dis- cussed. In [17] is a blueprin t of an artificial imm une system described where several parts are similar in t he SANA system in troduced b elow. In [18] are sev eral algorithms analyzed and a framew ork of an artificial imm une system introduced. The next section describ es challenges in the pro cess of bringing an artificial immune system into production in the net w ork securit y domain, which also copes with the up com- ing requiremen ts due to future trends in intrusions. 4. NEXT DESIGNING AND IMPLEMENT A- TION T ASKS The archit ecture b etw een artificial immune systems and common used protection systems is different. In con trast to the client-serv er arc hitecture of commo n used protection sys- tems, the artificial imm une systems implement a distributed arc hitecture where light weigh ted, mobile, and autonomous w orking artificial cells perform the required tasks. In order to run these cells in each node, some kind of middlew are m ust be installed on eac h no de, whic h handles the access to the resources of the node and also includes common used se- curit y comp onen ts. The middleware should also ensure that only allow ed artificial cells can access the resources and solv e other securit y issues. F urthermore, the middlew are should con tain the kno wledge for the normal pro duction so that the artificial cells are light w eigh ted and platform indep en- den t. The middleware should distingui sh the operating and securit y system so that legal evidences can b e sav ed and the system is chec ked from outside. F or the maintenance of the protection system are w ork- flo ws required. The administrator demands regularly a sta- tus snapshot of the system as well as the administrator w an ts to kno w the current status of the system. Therefore, all nodes should collect status information and sp ecialized nodes pro vide quickly a summary status snapsho t. How ever, the system should also analyze the warnings and alerts au- tonomously so that the load of the administrator is reduc ed. The administrator should b e able to access all nodes and all comp onents. The implemen tation of the system should be feasible and fast where extensions and no v el techniques should b e quickly deplo y ed to all components of the system. Updates - e.g. of the database of kno wn in trusions - are fre- quen t and the system should include the up dates as fast as possible e.g. through p ositiv e and negative selection. The installation of up dates and extensions should b e monitored so that unsuccessful installations are detected and rep orted. Infected no des or not proper w orking components are a serious problem in curren t security systems. The artificial imm une system should iden tify these comp onen ts through self-c hec king workflo ws. F urthermore, it should dev elop a strategy how to disinfect the no des or to repair the compo- nen ts - self-repairing and -healing. The information, which are gathered in this process, should b e included in further protection processes - learning of the system. Due to the enormous num ber of artificial cells and to enable nov el w orkflo ws, the information management must be more sophisticated implemen ted. The different artificial cells perform only small tasks and sev eral cells ha v e to coop- erate so that the goals are reached. Therefore, a communi- cation protocol should b e implemente d where a cell informs a set of cells about a certain even t - p oint to m ulti-point comm unication. Then, the artificial cells should use the comm unication proto col for collab orative w ork where e.g. the danger theory can be used and self management orga- nizes the artificial cells. Another p oint is that information from differen t nodes and from different analysis pro cesses are used in order to identify suspicious b ehavio r beside the standard processes of net w ork security . A protection system should secure the netw ork against all attac ks where esp ecially mo dified or nov el attacks are hard to preven t. Curren t protection systems use mostly the sig- nature based approac h extended with some heuristics and, th us, ha ve serious problems with nov el attacks. Artificial im - m une systems should b e adaptive in order to cope with the more and more intelligen t and adaptiv e intrusions. There- fore, b oth the artificial cells as w ell as the ov erall system should adapt to the current situation. The adaptively in ar- tificial cells can e.g. implemen ted using the artificial clonal selection and hypermutatio n as well as in ternal measure- men ts. These points are problems of protection systems and must be solved when an artificial immune system is deplo y ed in the net w ork securit y domain. SANA is a framew ork for an artificial immun e system and is exp lained in the next sect ion. 5. SANA - AR TIFICIAL IMMUNE SYSTEM SANA is a framework for a distributed protection system where the architecture, design, and workflo ws are mostly biological motiv ated [14] and the p erformance is increased due to an enhancemen t of the organization of the protec- tion components. The security system is an artificial im- m une system using artificial cells as well as common used protection components in order to secure a net w ork against in trusions. The protection comp onents, e.g. an tivirus soft- w ares, firew alls, pac k et filters, intrusion detection systems, and artificial cells, use v arious approac hes, which are b oth biological and non-biological inspired. The differen t parts are discussed in detail: In the se curity envir onment run the differen t common used protection comp onents as w ell as the artificial cells. The se- curit y en vironmen t manages the access to the resources of the no de. It pro vides a common interface for this access like a middlew are b etw een the no de and the protection comp o- nen ts, which work platform-indep endent. F urthermore, the securit y en vironmen t provides only the allo w ed comp onents access to resources. F or this is a distributed public key in- frastructure used, where eac h comp onent authorizes during the access to the resources. The security en vironmen t is so installed that an adversa rial cannot use it for attacks. Therefore, the securit y envi ronmen t is encrypted installed and the communicatio n b etw een the security en vironmen ts is also encrypted. In SANA, the approac h is to install the securit y environmen t as a virtual machine using hardware virtualization - e.g. Op enVZ or KVM. A second virtual mac hine con tains the op erating system for the user. The underlying operating system is only used to utilize the vir- tual en vironmen ts and is only c hanged when the h ardw are is c hanged. The security environmen t is allow ed to ch eck the underlying op erating system and all other virtual machines where other virtual mac hines are not allow ed to see other virtual mac hines. Then, an in trusion in the underlying op- erating system can b e detected because this system c hanges only when the hardw are changes. An in trusion in the nor- mal operating system cannot see the security environmen t and this is also secured against attacks through integrit y c hec ks. The different lay ers in the implemen tation are also visualized in figure 1. The protection components consist of t w o t ypes, which are installed in the security en vironmen t. The common used protection components like antivirus softw ares, fire- w alls, pack et filters, and intrusion detection systems are in- stalled and registered in a sec urit y en vironmen t without an y c hanges to the internal workflo ws of the components. An artificial cell connects a common used security component to the security environmen t in order to translate the warn- ings and alerts, to inform the comp onent about even ts, and to chec k and update the securit y component. The second t yp e is the p opulation of artificial c el ls [14]. Eac h cell is a ligh t w eigh ted and mobile agent p erforming certain tasks in the security en vironmen ts and mo ving through the netw ork. The tasks are v arious: e.g. chec king the pack ets, files, or system calls for intrusions [13], iden tifying infected no des [12], p erforming regular chec ks, and collecting status infor- mation. How ev er, the cells can p erform all tasks and nov el tec hniques are deploy ed through nov el artificial cells. E.g., the pac k et c hecking cells bu ild up a distribu ted in trusion de- tection system pr otecting all nodes against in trusions p ack ed in netw ork pack ets. The w arnings and alerts generated b y the protection components are combined in a common log file for eac h security environmen t. The information collected in the system are used to learn the system, e.g. to develop new strategies to defend the netw ork - self-learning. SANA uses lots of differen t artificial cells, which are re- dundan t installed in the netw ork. The workflo ws consist of several small tasks where eac h task is performed by one cell. F or the collab oration is the artificial c el l c ommuni- c ation used, whic h is a robust, fault-toleran t, and efficient comm unication proto col for point to multi-point comm u- nication. Two specialized no des are added: the artificial lymph nodes supply the protection comp onents of a small area with additional information and respond to imp ortant messages. F urthermore, the artificial lymph nodes decide when a message is sen t to all no des of the net work and they collect information ab out the supplied netw ork part. The second sp ecialized no de is the central nativity and training station (CNTS) that implements an artificial b one marrow and th ym us. It generates and releases contin uously nov el artificial cells in order to k eep the p opulation of cells up-to- date. Thereb y , it also includes nov el approac hes of netw ork securit y lik e enhancements and up dates. In addition, it col- lects status information for the administra tor and for further analysis. The v arious artificial cells mov e through the netw ork au- tonomously . Ho w ever, it must b e alw a ys guaran teed that eac h no de is prop erly secured. Therefore is the self-mana- gement used where each securit y comp onent knows the re- Figure 1: Implementation lay ers in a netw ork no de. The op erating system and the SANA run time envi- ronmen t in op erating system la y er 2 run in different hardw are virtualizations. The op erating system in la y er 1 c hanges only when the hardware changes. quired security it pro vides - the securit y v alue. Eac h no de calculates its securit y level basing on the secu rity v alues and when this level falls below a certain threshold, it starts a notification pro cess. This pro cess attracts cells from nearb y nodes to mo v e to th is node and that cells in this node do not lea v e; how ever, the cells still w ork autonomously . An addi- tional workflo w of the self-management organizes the cells, whic h flow through the netw ork and p erform certain tasks, so that each no de is regularly chec ked but not to o often to sa v e resources. Differen t protection comp onen ts w ork in the artificial im- m une system SANA and each comp onent p erforms other tasks as well as gains other information. This information should b e exc hanged in order to iden tify abnormal behavior quic kly . Therefore, the artificial cell communication is used to exc hange messages b etw een a sender and a set of receiv ers in a small area of the netw ork. Important messages are also broadcasted to all receiv ers in the netw ork or immediately to the administrator. F urthermore, the cells exc hange ev- ery time step summary information ab out the current sta- tus in order to inform the nearb y cells. All of these cells calculate a danger level and adapt their in ternal b ehavior accordingly - implementation of the danger the ory . Other adaptiv e w orkflo ws are to iden tify also mo dified intrus ions using a similarity measuremen t and that the cells mo v e to the area where the attacks are more likely to o ccur. SANA also iden tifies infected nodes using a sp ecial type of artificial cells in reusing the information from components c hecking net w ork pac k ets. Then, the system quarantines these no des and starts a disinfection pro cess. The maintenance workflo ws are different to common used securit y systems. The artificial cells shutdo wn ov er time and the CNTS release nov el cells ov er time. These no v el cells include the newest information and techniques about in trusions and the population is alw a ys up-to-date. The other components are updated using up dating cells, whic h flo w through the net w ork and report each up date; th us, un- successful up dates and outdated comp onents are identified. Chec king cells furthermore test the protection components and report not prop er working components. These cells also c hec k if a no de is iden tified with a certain in trusion. Nov el approac hes of net w ork securit y are introduced using a no v el t yp e of artificial cells and are quickly released by the CNTS because they w ork platform-independen t in the security en- vironmen t. The administrator can alwa ys demand a status snapshot using the information collected by the CNTS and they can access each security environmen t using the net- w ork for more detailed information. The administrator can define the granularit y of the demanded information and the system collects the information using artificial cells and the information stored in the artificial lymph nodes and CNTS. Important messages are immediately sen t to the administra- tor using the artificial cell comm unication. The main tenance w orkflo ws are implemen ted through a management softw are, whic h enables access to all security environmen ts and their securit y comp onen ts. The administrator uses this manage- men t soft w are to administrate SANA and its components and to observe the w orking of the nodes. Due to the virtualization of SANA’s security en vironmen t and the op erating system, they are no longer platform de- pendent. Consequen tly , the system is able to duplicate, halt, and transfer them ov er the net w ork. This leads to a com- plete differen t view of the system where a service orien ted arc hitecture is in tro duced. The artificial lymph no des as w ell as the CNTS provide on demand security comp onents as virtual mac hines, whic h are transferred to the demanding securit y environmen t when a certain ev ent o ccurs to p erform additional non-standard pro cesses. Additionally , as infected iden tified op erating systems are duplicated in order to sav e the legal evidences and to mov e these to CNTS for further analysis to enhance the system. In addition, the op erating systems can b e organized as services so that an user works alw a ys with the same system and can also quickly mov e the operating system to other no des. How ev er, the latter issue is not in the scop e of the SANA system. SANA’s pro ject status is that it is implemen ted on a net- w ork simulator as a proof-of-concept implemen tation. The automatic workflo ws work well and the adaptive b ehavior increases the performance. Using the differen t t yp es of arti- ficial cells are redundancies installed so that a partly break- do wn do es not influence the ov erall system. The results of SANA are explained in the next section. 6. RESUL TS The p erformance of SANA is more than acceptable. Us- ing the main tenance workflo ws, the system can b e easily updated and extended. The system pro cesses the warnings and alerts automatically and uses this information in order to configure and adapt itself so that it copes with the cur- ren t situation. Imp ortant information are quickly delivered to the administrator, who can influence the system. The sta- tus information are collected in the CNTS and the admin- istrator can alw a ys access the information e.g. for further analysis. The self-management organizes the v arious artifi- cial cells so that all no des are prop erly secured and regular c hec ks are performed on all nodes. The artificial cell com- m unication works well so that the artificial cells can quic kly and reliably exchan ge messages for collab oration. A GNOSCO - a sp ecial type of artificial cells iden tifying in- fected no des using the information gathered b y components analyzing the netw ork traffic [12] - helps to k eep the sys- tem free of infections and impro ves the performance signifi- can tly because common used systems mostly do not iden tify infected no des. F urthermore, AGNOSCO uses the infor- mation from lots of protection components, whic h are dis- tributed ov er nearly all no des. Other cells p erform regular c hec ks in order to identify infections, not prop er working components, and abnormal b ehavior - self-chec king. These cells rep ort infections quickly and increase the performance because a not prop er working protection comp onents are a risk for the whole netw ork. After iden tifying a problem, the system dev elops a strategy to solv e it - self-repairing and -healing. Examples are to add nov el artificial cells for the iden tification of new intrusions or to disinfect a no de us- ing an artificial cell. Otherwise, the system quaran tines the node quic kly and informs the administrator for disinfectio n. Most attac ks tow ards netw orks are not only p erformed to- w ards a single no de bu t rather tow ards sev eral no des in order to find a w eak p oint in the netw ork - e.g. IP-range scan- ning; to cop e with this is the artificial clonal selection and h yp erm utation used. In order to find suc h attac ks, SANA com bines the information gathered in differen t nodes for the iden tification of abnormal attacks through a more sophisti- cated information managemen t. One example is the already explained AGNOSCO approach. Other approac hes are to com bine summaries of the logs of different nodes and an- alyze these in order to find patterns describing abnormal behavior. F or co op eration and adaptiv ely , the artificial cells exc hange con tin uously summary status information in order to adapt their in ternal thresholds so that the ov erall sys- tem SANA adapts quic kly to the current situation, whic h is a first implementation of the danger theory and will be extended in the near future. The distinguished installation through hardware virtual- ization enab les sev eral new features where especially the ser- vice orien ted arc hitecture (SOA) helps to demand the re- quired comp onents in order to react to the certain ev en ts lik e identification of infections. The duplication of virtual mac hines w orks w ell and the in trusions can be stored in or- der to analyze them in detail and to use the legal evidences for legal analysis. The distinguished installation further- more secures the security system against attacks b ecause the normal operating system is not able to attac k the se- curit y en vironmen t and the securit y environmen t is secured with integ rity chec ks. F or the ev aluation of SANA, differen t attack scenarios are implemen ted and sim ulated. SANA p erforms well and pro- tects the netw ork efficiently: W orm, Virus, and T ro jan A ttacks A w orm attac ks the node ov er the netw ork using some security holes. The w orm mostly installs itself in th e no de - infection called - and p erforms certain tasks; the v irus is installed when the host-programm is executed. Often, they open a bac kdoor so that other in trusions or hack ers can o c- cup y the no de. SANA detects and remov es the net- w ork pac k ets con taining the w orm or virus, when it is kno wn b y SANA. In fected nodes are identified and dis- infected as well as backdoors are identified by regular c hec ks; the information are used in order to dev elop a protection stra tegy . Th us, SANA protects the netw ork against w orms as well as viruses and also disinfects it. Due to the regular chec ks is the performance higher than in common used protection systems. With the com bined analysis of different nodes and the status messages sen t every time step are multi-step or multi- stage attac ks identified b ecause eac h step is detected and rep orted to the nearby cells. Encrypted T raffic Attac ks These attack s install a bac k- door in some no de and connect to this no de o v er the net w ork with encrypted traffic. The netw ork pack ets can be only chec ked at the sou rce and destination n o de of the connection where the so urce node is the hack er’s node and normally not accessible. SANA uses a dis- tributed IDS installed b y the artificial cells and chec ks the net w ork traffic on all no des. Th us, infected pack- ets are identified and remo v ed at the destination no de and the bac kdoor is identified as w ell as remo v ed b y regular che cks performed by artificial cells. Hac k er Attac ks The identification of hack er attac ks is more difficult than identifying a w orm or virus attack . F or prev en ting a hack er attac k, SANA uses at least the same workflo ws as curren t protection systems. Addi- tionally artificial cells chec k regularly the nodes for in- stalled bac kdoors - e.g. VPNserver with IPsec -, whic h are used b y the hac k er for further en tries to the no de. Also, other c hanges and additionally installed soft w are is detected and rep orted to the administrator in order to secure the netw ork more properly . So cial Attac ks This type of attack is p erformed by users with in ternal information, e.g. an unsatisfied emplo y ee trying to gain in ternal information for further usage. The problem is to distinguish betw een the normal and abnormal netw ork usage of such an user. Ho wev er, some characteristics are e.g. that the user tries to ac- cess resources, whic h are normally not used by this user, and the user tries differen t passw ords generating login errors. Analyzing only the information from a single no de is mostly not sufficien t but combining the information from several nodes giv es a hint in order to iden tify such an user. Therefore, SANA uses artificial cells analyzing the log files of all no des and iden tifies these users. Ph ysical Attac ks The adversaria l has physical access to the node. The adv ersarial can connect external stor- ages, additional hardw are, or start another op erat- ing system. SANA identifies ch anges in the security en vironmen t and the hardware virtualizaton system through integrit y chec ks and do es not start the in- fected system. F urthermore, the neigh bor no des of a starting machine isolate the no de until the security en vironmen ts of the no des sync hronize and enable the net w ork access. Without a running security environ- men t is a net work access not p ossible and the neigh b or nodes rep ort the no des without prop er securit y envi- ronmen t. Th us, ph ysical attac ks and c hanges in the securit y systems are detected and preven ted. T o sum up, SANA sho ws that a distributed approach like an artificial imm une system enables additional features not pro vided by common used protection systems. Th ese fea- tures are e.g. analysis combining information from lots of differen t no des, c hec king from outside through the installa- tion of the security environmen t, and the coop eration be- t ween the n umerous small comp onents. F urthermore, the fast deplo ymen t of extensions and updates as well as the au- tomatic workfl ows without in teraction with the user. The virtualization enables fu rther features lik e the duplication of infected virtual machines. With theses features, the p erfor- mance of SANA is significantly better compared to common used protection systems b ecause SANA also adapts to the curren t situation in the netw ork as well as SANA can be quic kly enhanced with nov el approaches.. 7. CONCLUSION Artificial immu ne systems provide sev eral adv antages in protecting a netw ork against intrusions compared to com- mon used protection systems. Especially the architecture using lots of ligh t w eigh ted, mobile, and autonomous artifi- cial cells without a central ized server facilitates a more so- phisticated information managemen t and a self-c hec king for the identification of abnormal behavior. The chec king from outside as well as the quickly deploymen t is imp ortant for coping with upcoming intrusions. In order to bring an arti- ficial immune system in to pro duction, several tasks hav e to be done where especially the implemen tation and the design are c hallenges. SANA is a framew ork of an artificial imm une system and shows that the performance of artificial imm une systems in the net w ork secu rity domain is more than accept- able. The next steps are to sim ulate more realistic attac k scenarios and to discuss how to implemen t the security en- vironmen t in each node. 8. REFERENCES [1] U. Aick elin, P . Bentley , S. Cayzer, J. Kim, and J. McLeo d. Danger theory: The link betw een ais and ids? In Pr o c e e dings of the ICARIS 2003. LNCS 2787 , 2003. [2] U. Aick elin, J. Greensmith, and J. Twycross. Imm une system approac hes to intrus ion detection - a review. In Pr o c e e dings of the ICARIS 2004. LNCS 3239 , 2004. [3] S. Axelsson. Intrusio n detection systems: A surv ey and taxonom y . T echnical Report 99-15, Chalmers Univ ersit y of T ec hnology , 2000. [4] D. Dasgupta, F. Gonzalez, K. Y allapu, J. Gomez, and R. Y arramsettii. Cids: An agen t-based in trusion detection system. Computers & Se curity , 24(5), 2005. [5] H. Debar, M. Dacier, and A. W espi. T o w ards a taxonom y of intrusion -detection systems. Comput. Networks , 31(9):805–822, 1999. [6] L. N. DeCastro and J. Timmis. Artificial Immune Systems: A New Computational Intel ligenc e Appr o ach . Springer, first edition, 2002. [7] E. Filiol. Strong cryptograph y armoured computer viruses forbidding code analysis: the bradley virus. In EICAR2005 , v olume 14, 2005. [8] S. M. Garrett. How do w e ev aluate artificial immune systems? Evol. Comput. , 13(2):145–177, 2005. [9] J. Greensmith, U. Aick elin, and S. Ca yzer. In troducing dendritic cells as a nov el immune-inspired algorithm for anomaly detection. In Pr oc e e dings of the ICARIS 2005. LNCS 3627 , 2005. [10] J. Greensmith, J. Twycross, and U. Aick elin. Dendritic cells for anomaly detection. In Pr o c e e dings of the CEC , 2006. [11] C. R. Haag, G. B. Lamont, P . D. Williams, and G. L. P eterson. An artificial immune system-inspired m ultiob jective ev olutionary algorithm with application to the detection of distributed computer netw ork in trusions. In Pr o c e e dings of the GECCO , 2007. [12] M. Hilker and C. Sc hommer. Agnosco - iden tification of infected no des with artificial ant colonies. In Pr o c e e dings of R ec ent Ad vanc es in Soft Computing (RASC), Kent, UK , 2006. [13] M. Hilker and C. Sc hommer. Description of bad-signatures for net w ork intrusion detection . In Pr o c e e dings of the AISW-NetSe c during ACSW, CRPIT V ol. 54, Hob art, Austr alia , 2006. [14] M. Hilker and C. Sc hommer. Sana - securit y analysis in internet traffic through artificial imm une systems. In Pr o c e e dings of the T rustworthy Softwar e Workshop, Schloss Dagstuhl, IBFI , 2006. [15] S. A. Hofmeyr and S. F orrest. Immunit y by design: An artificial immun e system. In Pr o c e e dings of the Genetic and Evolutionary Computation Confer enc e , v olume 2, pages 1289–1296, Orlando, Florida, USA, 13–17 1999. Morgan Kaufmann. [16] C. A. Janewa y , P . T ra v ers, M. W alport, and M. Shlomc hik. Immunobiolo gy: the Immune System in He alth and Dise ase . Garland Publishing, sixth edition, 2004. [17] J. O. Kephart, G. B. Sorkin, M. Swimmer, and S. R. White. Blueprin t for a computer immune system. In Pr o c e e dings of the Virus Bul letin Confer enc e , 1997. [18] J. Kim. Inte gr ating Ar tificial Immune Algorithms for Intrusion Detecti on . PhD thesis, 2002. Department of Computer Science, Univ ersit y College London. [19] P . Mell, V. Hu, R. Lipmann, J. Haines, and M. Zissman. An ov erview of issues in testing intrusio n detection systems. T echnical Report NIST IR 7007, National Institute of Standard and T ec hnology . [20] S. Neuhaus and A. Zeller. Isolating intrusions b y automatic experiments. In Pr o c e e dings of the 13th Annu al Network and Distribute d System Se curity Symp osium , pages 71–80, F ebruary 2006. [21] M. Ro esch . Snort - light weigh t int rusion detection for net w orks. In LISA ’99 , 1999. [22] L. Schaeli ck e and J. C. F reeland. Characterizing sources and remedies for pack et loss in net work in trusion detection systems. In Pr oc e e dings of the IISWC , 2005. [23] T. Stib or, J. Timmis, and C. Eck ert. On the appropriateness of negativ e selection defined ov er hamming shape-space as a net w ork in trusion detection system. In Pr oc e e dings of CEC 2005 , 2005. [24] P . Szor. The Art of Computer Virus R esear ch and Defense . Addison-W esley Professional, 2005. [25] P . Sz ¨ or and P . F errie. Hunting for metamorphic. In Virus Bul letin Confer enc e and Symante c White Pap er , 2001. [26] J. Twycross and U. Aick elin. T ow ards a conceptual framew ork for innate immunit y . In Pr o c e e dings of the ICARIS 2005. LNCS 3627 , 2005. [27] M. M. Williamson. Throttling viruses: Restricting propagation to defeat malicious mobile co de. In Pr o c e e dings of ACSA C ’02 , 2002.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment