A new queueing strategy for the Adversarial Queueing Theory
In the today's Internet and TCP/IP-networks, the queueing of packets is commonly implemented using the protocol FIFO (First In First Out). Unfortunately, FIFO performs poorly in the Adversarial Queueing Theory. Other queueing strategies are researche…
Authors: Michael Hilker, Christoph Schommer
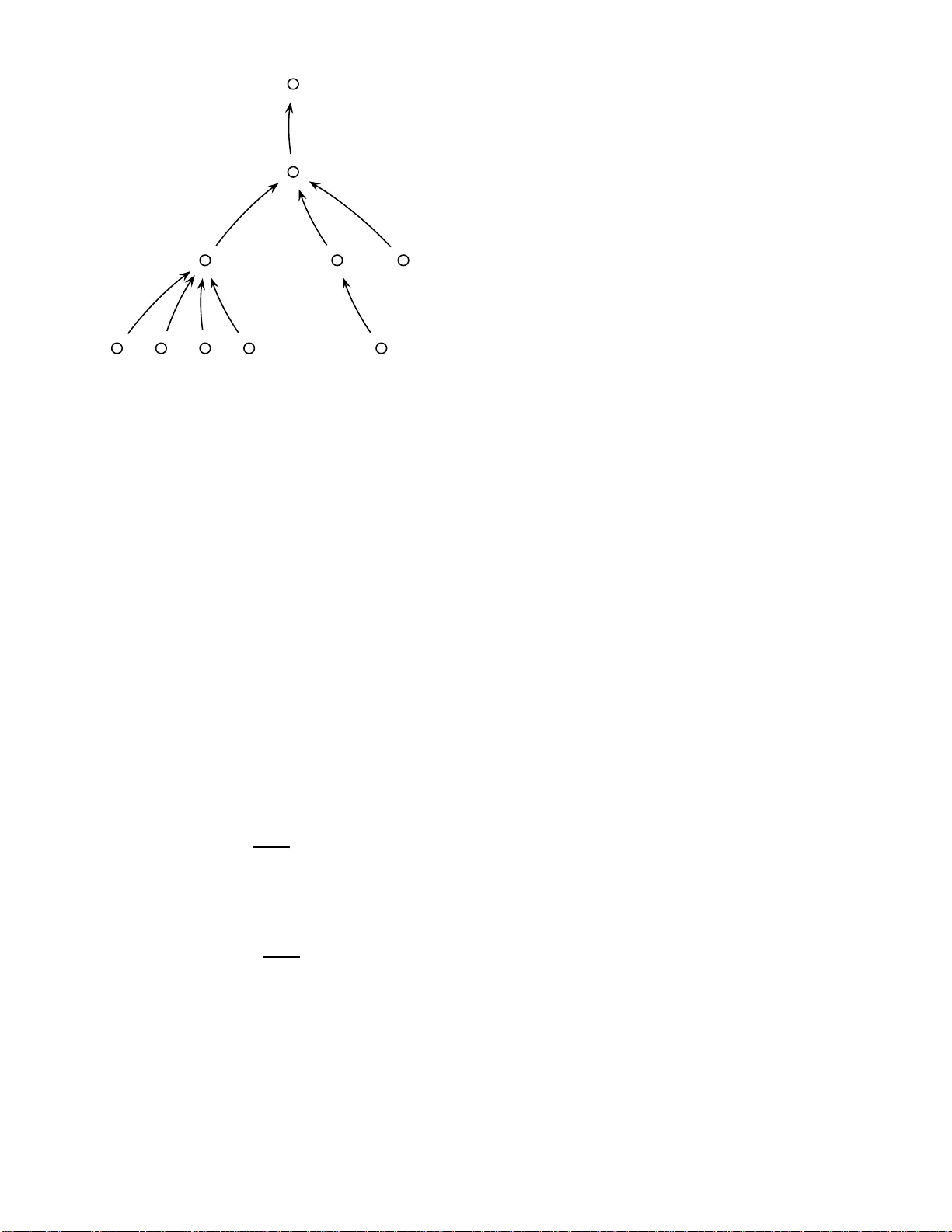
A ne w queueing strate gy for the Adv ersarial Queueing Theory Michael Hilker , Christoph Schommer University of Luxembou rg, Campus Kir chberg Dept. of Computer Science and Comm unication 6, Rue Richard Couden hove-Kalergi, L-135 9 L uxembourg Email: { mich ael.hilker , ch ristoph.scho mmer } @ un i.lu Phone: +352 -4201 01- { 234,228 } Abstract — In the today’s Internet and TCP/IP- networks, the queueing of pa ckets is commonly imple- mented using the protocol FIFO (First In First Out). Unfortunately , FIFO performs poo rly in the Adversar - ial Queueing Theory . Other queueing strategies are re- searched in this model a nd bette r results are performed by alternative queueing strategies, e.g. LIS (Longest In System). This art icle introduces a new queueing protocol called interval- strategy tha t is concerned with the reduction from dynamic to static routing. W e discuss the maximum system t ime for a packet and estimate with up-t o-date results how this can be achieved. W e figure o ut the maximum amount of time where a packet can spend in the network (i.e. worst case system t ime), and a rgue t hat the uni versal instability of the presen ted inter val-strategy can be reached through t hese results. When a large group of queueing strategies is used for queueing, we prove that the interval-strate gy w ill be universally unstable. Finally , we calculat e the maximum time of the stat ic routing to reach an universal stable a nd poly nomial - in detail linear - bounded interval-strategy . Afterwards we close - in order to check this upper bound - with up-t o-date results about the deli very times in sta tic routing. Ke ywords: (Ad versarial) Queu eing T heory , Internet Traf fic Manageme nt, Data Stream s. I . I N T R O D U C T I O N In the today’ s Internet and TCP/IP-networks, the queueing of packets is commonly implement ed us- ing the protocol FIFO (First In First Out). Ho we ver , when traffic resides heavily in th e network, a queue overfl o w can occur and consequently a n umerous- ness number of packets may become lost. Thereby , these packets must be resend by the transmitter; the outcome of this will be higher network traffic and higher d eliv ery time for the resented packets as well as for all packets. The Quality of Life depends on fast, reliabl e and a v ailable com munication connec- tions. W ithout communicatio n, e.g. internet, phone or email , i s t he today’ s life inconceiv abl e. Queueing is one component which highly af fects the speed and realibility of networks. In this article 1 , we concern with novel inspections on Queueing Theory in t he Adversarial Queueing Model. The Adversarial Queueing Model was fir stly in vestigated by Andrews et. al in 1996 [2] and continued in 2001 [3]. The Adversarial Queueing Model tries to simulate a real network i n order to analyse queueing strategies theoretically . T he Queueing is in the Adversarial Queueing Model simulated us ing a game between an adversarial - injects packets in order to overload connections - and the queueing strategy - tries to manage the packets injected b y the adversarial. Queueing The- ory in combination wi th determi nistic adversaries is a n e w and challengi ng research field. So far , the implementati on of networks mos tly uses t he FIFO protocol and seldom other alternative s. In 2002, Bhattacharjee and Goel [4] publ ished an article that described FIFO as an uni versal unst able protocol, eve n at arbitrary low rates. Univ ersal Un- stable means that th ere exist an adversarial and a network where the number of packets in th e system is not bound ed. Generally , a lot of other basic protocols l ike e.g. LIFO (Last In First Ou t), FFS (Farthest From Source), and NTG (Nearest T o Go) 1 This work is supported by the Ministre Luxembour ge ois de l’education et de la r echer ch e through the project INT RA (= INternet TRAffic manag ement and analysis) , which is currently performed at the University of Luxembour g . Parts of the work result from a cooper- ation with the Johann W olfgang Goethe-University , F rankfurt/Main . are commonl y kn own as to be un iv ersal unst able [3]. Universal unstable prot ocols are incon venient for t he implementation of t he q ueueing in networks because these protocols need in finite q ueue size as well as the deliv ery ti me of a packe t is unbound ed. On the other side, t he protocols SIS (Shortest In System), FTG (Farthest T o Go) and NTS (Nearest T o Source) are universal stable, w hereas t he upp er bound for queue size is exponential for t he longest path of the network [3]. Even if a queueing strategy is universal stable it is also i mportant that the number of packets in the system is poly nomial bounded and no t exponential; thus these queueing protocols are not con venient for queueing. The queueing protocol LIS (Longest In System) is uni - versal stable, but a nontrivial upper bou nd - a bound must be in o ( maximum pat hl eng t h in net work ) - is not currently kn own [3], [1]. Furthermore, there exist a lot of alternativ e approaches for queueing in the Adversarial Queueing Mod el wh ich are rarely analysed. In this paper , we insp ect the novel and auspicious queueing protocol interval-strate gy . The interval-strate gy di vides the packets injected by the adversarial in phases, transfers the packets of a phase and delays all packets which are injected during t his ph ase unt il the next phase starts. The main goal in the Adversarial Queueing Model is firstly to find out whether a polynomial upper bound ed protocol exists or not and secondly , if such a strategy can b e used to describe how this polynomial u pper b ounded prot ocol behaves. The m ain motiv ation in the Adversarial Queueing Model is that the performance of existing con- nections i s increased if other queueing strategies than the comm only implemented FIFO is applied. Ne w applicatio ns based on internet are feasible with faster com munication conn ections, e.g. HDTV o ver IP , increased network con nection speed especially for home-connection s, and/or high-bandwidth appli- cations. W e focus on the interv al-strategy approach which reduces the dynamic rou ting to static routing b y reusing known facts about static routing in the context of Adversarial Queueing Theory . The agenda of this article i s: Section II describes the Adversarial Queueing Model and some parameters to ev aluate queue- ing protocols and section III d efines the interval- strategy . In s ection IV, we look on the behavior of the interval-strategy on basi c networks, section V calculates the worst case tim e for static rout ing and section VI analyses the system time of static routing if non forward looking prot ocols - e.g. NTS, FFS - are used for queueing. In section VII, we calculate the upper bound that static routing can use for a phase in order to g et a universal stable and polynomial - in detail linear - bounded interval-strate gy . Section VIII im proves th e interval- strategy and section IX giv es a conclusion and future prospect in this research area. I I . C U R R E N T S I T UA T I O N In the Adversarial Queueing Model - introd uced in [2] and [3] - , the queueing is si mulated by a game between the queueing protocol and an adversarial. The adversarial injects packets with the aim to increase the num ber of packets in the system. The queueing strategy manages which packet is all owed to trav erse whi ch connection s in which tim e-step in order to limit the number of packets in the syst em. The Adversarial Queueing Model is used to model a realistic network situation such as i t occurs in realized n etworks. The main benefit of this model is that a researc her can enforce a mathemati c analysis wi thout using probabi listic traf fic. Hence, t his model is nearer to practical network load; better resu lts are expected. Now take a look at the definiti on of the ad- versarial. The adversarial has the right to inject packets wi th a fixed path th rough the network in e very tim e-step. The num ber of packets injected by a ( r , b ) -adversarial in time i nterval I for an edge e is bounded b y r · | I | + b ; 0 < r < 1 is called injection- rate and b ≥ 1 is called bur st . The Adversarial Queueing Theory uses t he parameter inj ection-rate in order to simu late t he normal network-load as well as the parameter burst in order to sim ulate a short-term overload of a connection. Consequently , the adversarial is allowed to inj ect packets in the network over time and the queueing strategy has to guarantee that t he packets arriv e at the certain destination. T he queueing strategy i s ev aluated how fast p ackets arrive at their destinati ons as well as how many packets are i n a queue and in the syst em. The adversarial kno ws the topology of the network as well as the behaviour of the queueing strategy . The aim o f the queueing s trategy is t o guarantee a prop er transmi ssion of th e packets as well as the aim of the adversarial is to increase the number of packets in the network. T o estimate, if a queueing protocol is con venient, we examine the parameter stabi lity . A protocol is stable on a network against an adversarial if th e number of packets in the network is upper bounded in e very ti me step. A queueing prot ocol is universal stable if the protocol is stable against all adversaries on all networks. Universal stability o f a queueing strategy m eans that in all time steps is t he number of packe ts in each queue upper bounded on all net- works against all adversaries. If a queueing s trategy is univ ersal stable, it is also important to examine the number of packets in the system ; only if this value is polynom ial bo unded - the glo bal aim is to have a linear v alue - is the s trategy approp riate for queuein g. Universal instabi lity of a queueing strategy means that t here exist a network and an adversarial s o that the number of packets i n the system is in the i -t h time step greater than in the i − 1-th time step ( i ∈ I N). These unive rsal unstabl e queueing strategies are incon venient because the queueing s trategies need qu eues with an in finite queue size. There are two main ways of proving. If the motiv ation is • to demons trate that a queueing protocol is universal unstable , we have t o define a network and an adversarial such that the num ber of packets in the network is not upp er boun ded. • to demons trate that a queueing protocol is universal stabl e , we need to upper bou nd the number of packets for all networks and adver - saries. Usually it is also int eresting to estimate the value of the bound. Unfortunately , the av erage case analy sis is less discussed in the research community . The main reason for this is a missing definition and the continuing focus on an existing idea, namel y to find a queueing strategy that probably satisfies all occur- ring problems through one network and adversar - ial. Therefore, the main approaches in Adversarial Queueing M odel base on worst case analyses. I I I . D E S C R I P T I O N O F I N T E RV A L - S T R A T E G Y As described in th e definit ion of the Adversarial Queueing Model, the adversarial injects packets over ti me. In order to receive a good deliv ery time of t he packets, the packets are divided by the interval-strate gy in data phases. Packets pertaining to a phase are routed and all packets of later phases are delayed. The routi ng of one phase is call ed static r outing because all packets reside in the network at st artup. Th erefore, the static rout ing represents a special situation of dy namic routi ng. For dynamic r ou ting , a queueing strategy operates on a network and again st an adversarial which injects pack ets ov er time. Hence, the informatio n for the queueing strategy can change e very time step. The packets t ra verse their paths through the net- work that is fixed by th e adversarial. In each queue and at ev ery time step, the queueing st rategy d ecides whi ch packet tra verses the edge of t he queue. Accordingly , this is t he normal si tuation in queueing and rou ting t heory . For stati c r outi ng , howe ver , al l packets resid e in the n etwork at st artup and no packets will be injected after startup; all information is existing and applicable for the q ueueing strategy from beginning. Of course, static routing is easier t o handle as dyn amic routi ng as well as t here exist approaches wi th bett er results for static rou ting. The id ea of the int erv al-strategy is to reduce the dynam ic routing to st atic routing because static routing is easier to handle. T o map the dynamic routing to static routing, all network edges own two queues, respectively: 1) The first queue is the queue that cares for the static rout ing. 2) The second q ueue contains the packets injected during a static routing phase until the static routi ng phase ends. Concerning the description of the interval-strate gy , it wi ll be assumed that there are no packets in the network at startup. Afterwar ds, the adversarial injects some packets i n th e network in on e time- step. These pack ets are the packets which are rou ted by the first static routing phase. The interval-strate gy transmits the pack ets of the first static routing phase to their dest inations and all packets which are injected during the s tatic routing phase are delayed i n the second q ueue. If all packets of the fir st static routing phase r each the destinations and t he first static routing phase ends, th e packets delayed in t he second queues are copied to the first queues and the second static routing s tarts wit h these packets. Thus, if the i -th stati c rout ing phase is runn ing, these packets will be rou ted and new injected packets will be delayed in the second queues. If all packets of the i -th path receive their destinati ons the packets of the second queues wi ll be copied to the first queue and, afterwards, the i + 1-th static routing phase is started with t hese p ackets. At startu p tim e of the network, we notice a st atic routing phase without any packets. In this case, it terminates immediately and the first ph ase starts routing the packets injected duri ng the first tim e step. So, the int erv al-strategy uses a static routing phase for delivering the packets. W ith s ome modifications, we kn ow that the interval-strate gy performs well [3], [6]. These mod- ifications are: • the int erv al-strategy delays a ll injected packets for a probabil istic time period and • if mo re than one packets want t o trav erse a edge the d ecision which packet is allowed to tra verse the edge is performed by a probabilis- tic event. This probabili stic version of the interval-strate gy is with h igh prob ability universal stable as well as the number of pack ets in system is wi th high probability polynomial bounded. The idea of the interval-strate gy is to use similar requirements and to receive similar results tow ards a d eterministic s trategy . Howe ver , the interval-strate gy is a deterministic v ersion of the probabilist ic. Fortunately , there exist s ome indicators that the interval-strate gy is almost reliable si nce the similar random-based st rategy off ers a well performance. W e b eliev e that there exist a schedule for static routing so that the interval-strate gy is un iv ersal stabl e and polynomial Fig. 1. one way connection line - in detail linear - bounded. Furthermore, a queueing strategy that determi nistically performs the mapping from dynam ic to static routing was rarely analysed in the Adversarial Queueing Theory . Furthermore, we implem ented the in terva l- strategy on a network simu lator and the resul ts are promising because the number of packets in the system is always bounded in a lo t of scenarios. T o si mulate a scenario, a network and adversarial hav e been design ed; they hav e produced lots o f packets in any queues. W e notice that the re sults of the simulati ons substantiate the th eoretical results of this arti cle. I V . I N T E R V A L - S T R A T E G Y O N BA S I C N E T W O R K S In this s ection we describe the beha vior o f the interval-strate gy on basi c networks. A. One way connection line One way connection lines are basic networks where some nodes can send packets from A t o C via B, but C and B cannot send packets to A. If A i s t he start of the line, B is the end of th e li ne and we insert an edge e = ( B , A ) we will recei ve a ring ; an example network is visualized in figure 1. In this part we look on the performance of the interval-strate gy on one way connection l ines. Let A = ( b , r ) t he adve rsarial and let G a one way connection l ine with length d . 1) In the first static routin g phase is the num ber of packets u pper bounded by r · 1 + b whi ch is equal to b because r · 1 < 1 and a packet cannot be fragmented. Hence we see that the static routing phase needs up to b + d time s teps because b pack ets can interfere and ever y packet needs up to d tim e steps to trav erse the own path. 2) In the second phase th e pack ets - injected during the first phase - w ill be routed. The Fig. 2. example for a t ree number of these packets is upper bound ed by r · b + r · d and the second phase needs up to r · b + r · d + d tim e steps. i) W e see iterative ly that the numb er of packets in the i -th phase is upper bou nded by r i − 1 · b + i − 1 ∑ j = 1 r j · d Hence th e number of ti me steps needed b y the i -th phase is upper bounded by r i − 1 · b + i − 1 ∑ j = 0 r j · d If we look on i → ∞ we recei ve a tim e for st atic routing of d 1 − r Therefore, the maxim um delivery time of a pack et is bou nded by 2 · d 1 − r because in t he worst case, the packet waits maxi- mum tim e in the second queue and afterwards the packets needs the maximum ti me for routing. Hence, t he interva l-strategy is uni versal stable and polyno mial bo unded - in detail linear - if the network is a one way connection li ne. B. T r ees Here we focus our view on the performance of the interval-strate gy on trees if static routing needs the worst case t ime. An example for a t ree is visualized in figure 2. Let A = ( b , r ) an adversar ial wit h parameters b ≥ 1 and 0 < r < 1. Let G a n etwork with d as the length of the l ongest path in the network. And let n · d the system time of stat ic routing with n t he maximum number of packets which need an edge e (worst-case system time for static rout ing, s imilar to sectio n V). 1) In the first p hase the num ber of packets i s upper bounded by b - definition of adversarial A - and h ence the syst em tim e of the stati c routing is upper bounded by b · d . 2) The second stat ic rout ing phase contains packets whi ch are i nserted in t he first phase. Therefore, the n umber of packets in the sec- ond p hase is upper b ounded by r · b · d . Conse- quently , the syst em time of the second phase is upp er boun ded by r · b · d 2 . i) W e can see it erativ ely that the number of packets in the i -th phase is up per bounded by r i − 1 · b · d i − 1 and hence the static routing phase is upp er boun ded by r i − 1 · b · d i . Now we look on i → ∞ : lim i → ∞ r i − 1 · d i · b = 0 = d · b → ∞ , if r · d < 1 , if r · d = 1 , if r · d > 1 W e see that t he interval-strategy is univer sal unstable on trees if the practical case r · d > 1 appear . In th e oth er cases, r · d ≤ 1, is the longest network leng th short and the adve rsarial perfor - mance is l ow; hence, these cases are n ot near to practice. Afterwards, w e calculate the worst case of static routing, thereafter , we analys e a common used group of p rotocols for q ueueing and, accordingly , we calculate the maximu m time static routin g may use to recei ve a univ ersal stable and polyno mial bounded i nterval-strate gy . V . W O R S T C A S E S Y S T E M T I M E I N S TA T I C R O U T I N G In t his part, the worst-case syst em time of a packet in static routing is exhibited. In stati c routing, all packets reside initially in th e network. A static routing phase ends when all packets reach their final destinati ons. Lemma 1: Let n be t he maximum numb er of packets for an edge in the network and let d be the length of the longest path i n the network. Then the system tim e is bounded by n · d . Pr oof: If a packet needs n · d + 1 time steps to reach the destinati on, it wi ll either be blocked in the queue of any edge b y n + 1 packets o r it will be blocked in every queue by n packets and trav erses d + 1 edges. The former case is a contradicti on to the definition of the p arameter n , the latter case a contradiction to the definition o f th e parameter d . Hence, th e lem ma 1 is proved. W ith this lemma 1, we n otice that a static rout ing phase ends not later t han n · d t ime steps. This is the worst case t ime for static routing. Lemma 2: The interval-strategy will be u niv ersal unstable if the worst case is applied for st atic routing. Pr oof: The first static routing phase contains up to b packets. S o, the static routing ph ase needs b · d time steps. In these time steps, the packets for the second phase are injected. The packe ts in the second phase are up per bounded by r · b · d ; the static routing phase consequent ly needs r · b · d 2 time steps. If this will be iterated, t he number of packets in the i -th phase is upper bo unded by r i − 1 · b · d i − 1 and the system time for the i -th phase is up per bounded by r i − 1 · b · d i . If i → ∞ and r · d > 1 is valid, the num ber of packe ts in the interva l-strategy will be unbounded and the i nterval-strate gy will b e universal unstable. The s pecial case of r · d ≤ 1 remains unint eresting because the injection rate is rather small and the longest path in the network is short. Remark: It is easy to design a network and an adversarial where the worst case time for static routing occurs in ev ery phase. W ith both l emma 1 and 2, th e worst case tim e for static routing is too slow for the in terva l-strategy in order to become con venient. There fore, we need t o find better sol utions fo r static routing in order to e va luate these solutions for th e in terva l-strategy . V I . I N T E R V A L - S T R A T E G Y W I T H N O N F O RW A R D L O O K I N G P R OT O C O L S Non forwar d looking protocols are queueing strategies which only e v aluate t he b ygone pat hs t hat were visited by the packets. They do not e valuate the giv en paths which the p ackets will trav erse in the future. Exam ples for such p rotocols are NTS and FFS; wi th a few modifications, t he proof i s also valid for alternatives like LIS and SIS. In t he year of 1994, Leigh ton, Maggs and Richa showed that there exist a network and an adversarial where non forward looking protocols hav e a system time of at least n · ( d − 1 ) l og ( n ) for static routing [5]. This result will be us ed as a validation that these proto- cols do not satisfy the int erv al-strategy . Here, a tree is us ed w ith no preconditi ons. Each static routi ng phase is dis joint and a sy stem tim e greater or equal n · ( d − 1 ) l og ( n ) appears in every phase of the int erv al-strategy . W e will show iterative ly that the in terv al-strategy is universal u nstable and t hat these prot ocols are incon venient for the protocol. Therefore, we assume that all static ro uting ph ases will hav e the sys tem time o f n · ( d − 1 ) l og ( n ) . In t he first phase, there are only packets in t he network which are injected during th e first time s tep; thus, the number of these packets is bounded by b and, consequentl y , th e sy stem ti me is b · ( d − 1 ) l og ( b ) . All packets which are routed in the second phase are inj ected during th e first phase; hence, the num - ber of packe ts is bounded by r · b · ( d − 1 ) l og ( b ) and the system tim e for the static rout ing ph ase is r · b · ( d − 1 ) l og ( b ) · ( d − 1 ) l og ( r · b · ( d − 1 ) l og ( b ) ) Let k 1 = b · ( d − 1 ) log ( b ) and k i = r i − 1 · ( d − 1 ) i · b log ( b ) · i − 1 ∏ j = 1 log ( k j ) then we see that k i is th e system time for st atic routing in the i -th phase. If i → ∞ and r · ( d − 1 ) > 1, both the number of p ackets and the system t ime of the static rout- ing phase wil l be unboun ded. T he special case of r · ( d − 1 ) ≤ 1 is far aw ay from practice b ecause the injection rate r i s rather sm all and the longest network path is short. From there, these non forward looking p rotocols are not suitable for i mplementing the queueing in static rout ing under pra ctical conditions. In order to recei ve bett er results, the maximum system t ime for static routing w ill be calculated. Up-to -date result of static rout ing qual ifies the interval-strategy . V I I . U P P E R B O U N D F O R S TA T I C RO U T I N G F O R A P O L Y N O M I A L B O U N D E D I N T E R V A L - S T R A T E G Y In this section, a sharp upper bound for the static routing phase system tim e is calculated in order to receive an univer sal stable and polynomi al bounded in terva l-strategy . W e show as well that i f the interval-strategy is polynomi al bounded it is also linear bounded. It follows: • If this upper bound is reached by a protocol in static rout ing, the interval-strategy is unive rsal stable and poly nomial bound ed. • If t his upp er bound i s not accomplishable, the interval-strate gy is not polynom ial bo unded and perhaps unive rsal unstable. For this, the interval-strate gy is no longer con venient. Theorem 1: If the static routi ng can b e upper bounded by c 1 · n + c 2 · d + c 3 , the i nterval-strate gy will be universal stable and pol ynomial bounded. The parameters are defined as fol lows: • c 1 , c 2 and c 3 are p arameters with a constant value, c 1 ≤ 1, • n is the maximal num ber of packets which contain an edge e in th e path and • d is the length of the l ongest path in the network. Pr oof: By induction with th ree differ ent static routing ph ases to verify the base cases, th e pred- ication wi ll be proved. 1) Startup and first phase: No packets are located in the system at startup. Duri ng one tim e step, an adversarial can i nject at most r · 1 + b packets for one edge; therefore, n is at m ost b because r · 1 < 1. The durati on of the first static rout ing phase is upp er boun ded by c 1 · b + c 2 · d + c 3 . 2) Second phase: All packets which will be rout ed in t he s ec- ond phase are injected during the first phase. Thereby , the number of packets for on e edge is upper bounded by r · ( c 1 · b + c 2 · d + c 3 ) and hence, the static routing p hase is upper bounded b y c 1 · r · ( c 1 · b + c 2 · d + c 3 ) + c 2 · d + c 3 = r · c 2 1 · b + r · c 1 · c 2 · d + r · c 1 · c 3 + c 2 · d + c 3 3) Third phase: W e obs erve the fol lowing: all routed packets of th e thi rd phase were i nserted i n t he sec- ond phase. The numb er of th ese p ackets is bounded b y r · ( r · c 2 1 · b + r · c 1 · c 2 · d + r · c 1 · c 3 + c 2 · d + c 3 ) and the sys tem time for t he third static rout ing phase is bound ed by r 2 · c 3 1 · b + r 2 · c 2 1 · c 2 · d + r 2 · c 2 1 · c 3 + r · c 1 · c 2 · d + r · c 1 · c 3 + c 2 · d + c 3 i) i-th phase: By induction we see that t he number of packets in the i -th phase is bo unded by r i − 1 · c i − 1 1 · b + i − 1 ∑ j = 1 h r j · c j − 1 1 · ( c 2 · d + c 3 ) i and the syst em t ime of the i -th static routi ng phase is bound ed by r i − 1 · c i 1 · b + ( c 2 · d + c 3 ) · ( r · c 1 ) i − 1 r · c 1 − 1 If i → ∞ , the interv al-strategy will be polynomi al because ou t of r · c 1 ≤ 1 f ollows ( r · c 1 ) i ≤ 1 a s well as c 2 and c 3 are constant . If r · c 1 > 1 or either c 2 or c 3 is not constant, the queue size of the interva l- strategy will b e at least exponential. The Theorem is shown. The question is now is the interval-strate gy also linear bounded - in the length of the lon gest path d ? Thus, we hav e lim i → ∞ r i − 1 · c i 1 · b + ( c 2 · d + c 3 ) · ( r · c 1 ) i − 1 r · c 1 − 1 = Θ ( d ) and it follows that 0 ≤ r · c 1 ≤ 1 and c 2 · d + c 3 = Θ ( d ) must b e valid. Are these equati ons valid? The former equation is valid because the values of the parameters c 1 and r are in [ 0 , 1 ] . The latter equation i s valid because c 2 and c 3 are con- stant. Hence, if the interval-strategy is polynomial bounded t he s trategy is als o linear bounded. W e hav e to check now i f this system ti me for the stati c routing can be achieved. Therefore, we present up-to-date facts of s tatic routi ng. It i s highly important that in [5] is proved that a schedul e for stati c routing wit h time O ( n + d ) exists for eve ry packe t set. Furthermore, there are no networks and adversaries known wit h a time greater than n + d . Unfortunately , this upper bound is not proved. Since the proof of [5] is not const ructiv e, it is open in which time the schedule with time O ( n + d ) can be comp uted. There exist some prom ising algorithms that calculate a schedule of acceptable system tim e, but these algorit hms are prob abilistic that can not be used in this determin istic model. Indeed, there are no determini stic protocols for static rout ing wit h acceptable system time known. The a nalysis of the interval-strategy has fi nished, but we still hav e t o search for acceptable and deterministic algo rithms to sol ve static routing. V I I I . I M P RO V E M E N T O F I N T E RV A L - S T R A T E G Y The following case can occur: A static routing phase is running. There are no packets in the static routing phase which need an edge e and the adversarial i njects some packets for this edge e . Now these packets will be delayed until the stati c routing phase finishes and, unfort unatly , th e edge has no traf fic load. Hence, these packets can t ra verse the edge e wit hout interfering with the p ackets of the st atic routing phase if the packets will inserted into t he second queue at the destination o f edge e . Th erefore, the interval-strate gy will be i mproved because in some cases the deli very time for a packet decreases. I X . C O N C L U S I O N The problem of nove l queueing strategies be- comes crucial and of parti cular importance because the com mon used protocol FIFO poorly performs in the Adversarial Queuein g Model. In this con- text, there might be som e hope to increase the network performance by alternative q ueueing pro- tocols. The benefits of higher network performance without increasing the conn ection speed are a bet- ter QoS (Quality of Service), cheaper high speed connections and a better re liability for network and communication connections. The Quality of Life may increase if faster com munication connectio ns are ava ilable. The price of faster communi cations connections decreases and the connections are ob- tainable for anybody . In this article, a new approach for queueing has been introdu ced, des cribed and, in respect to the protocol, analysed. As p robably the most im portant result, the maxim um sy stem time for stati c rout ing is calculated and compared with up-to-date results about static routing. In order to prove the approp ri- ateness and t he g oodness o f t he present ed i nterva l- strategy , additional studies concerning static rou ting need t o be done. There exist further i nteresting questions t hat con- cern e.g. the lo wer bou nds for static routing (which system t ime d oes a stati c routi ng phase need for a giv en net work and adversarial) and/or the important question of this model: does there exist a queueing strategy which offers a polynom ial or ev en linear bounded d eliv ery time for a packet and - in the case it exists - what is it’ s behavior? Additionally , it would become w orthful t o examine a network simulatio n u nder realisti c conditions using an un- con ventional strategy for queueing. These questions will b e ou r challenge for future researches. R E F E R E N C E S [1] Micah Adler and Adi Ros ´ en. Tight Bounds for t he Performance of Longest-in-System on D A Gs. ST ACS - International Sympo- sium on Theor etical Aspects of Computer Science , 19, 2002. [2] Matthew And re ws, Baruch A werb uch, Antonio Fernndez, T om Leighton, Z hiyoung Li u and Jon Kleinber g. Univ ersal Stability Results for Greedy Contention-Resolution Pr otocols. FOC S: IEEE Symposium on F oundation s of Computer Science (FOCS) , 1996. [3] Matthew And re ws, Baruch A werb uch, Antonio Fernndez, T om Leighton, Z hiyoung Li u and Jon Kleinberg. Univ ersal-S tability Results and Performance Bounds for Greedy Contention- Resolution Protocols. Journal of the A CM , 48:39–69, 2000. [4] R ajat Bhattacharjee and Ashish G oel. Instabilty of FIF O at Arbitrarily L o w R ates i n t he Adversarial Queueing Model. IEEE Symposium on F oundations of Computer Science , 44, 2003. [5] F rank T . Leighton, Bruce M. Maggs and Satish B . Rao. P acket Routing and Job-Shop S cheduling in O(C ongestion + Di lation) Steps. Combinatorica , 14:167–186, 1994 . [6] Georg Schnitger . Internet Algorithm. Script of the lecture at the Joha nn W olfgang Goethe-University F ran kfurt/M., Germany , 2004.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment