On Distributed Function Computation in Structure-Free Random Networks
We consider in-network computation of MAX in a structure-free random multihop wireless network. Nodes do not know their relative or absolute locations and use the Aloha MAC protocol. For one-shot computation, we describe a protocol in which the MAX v…
Authors: Sudeep Kamath, D. Manjunath
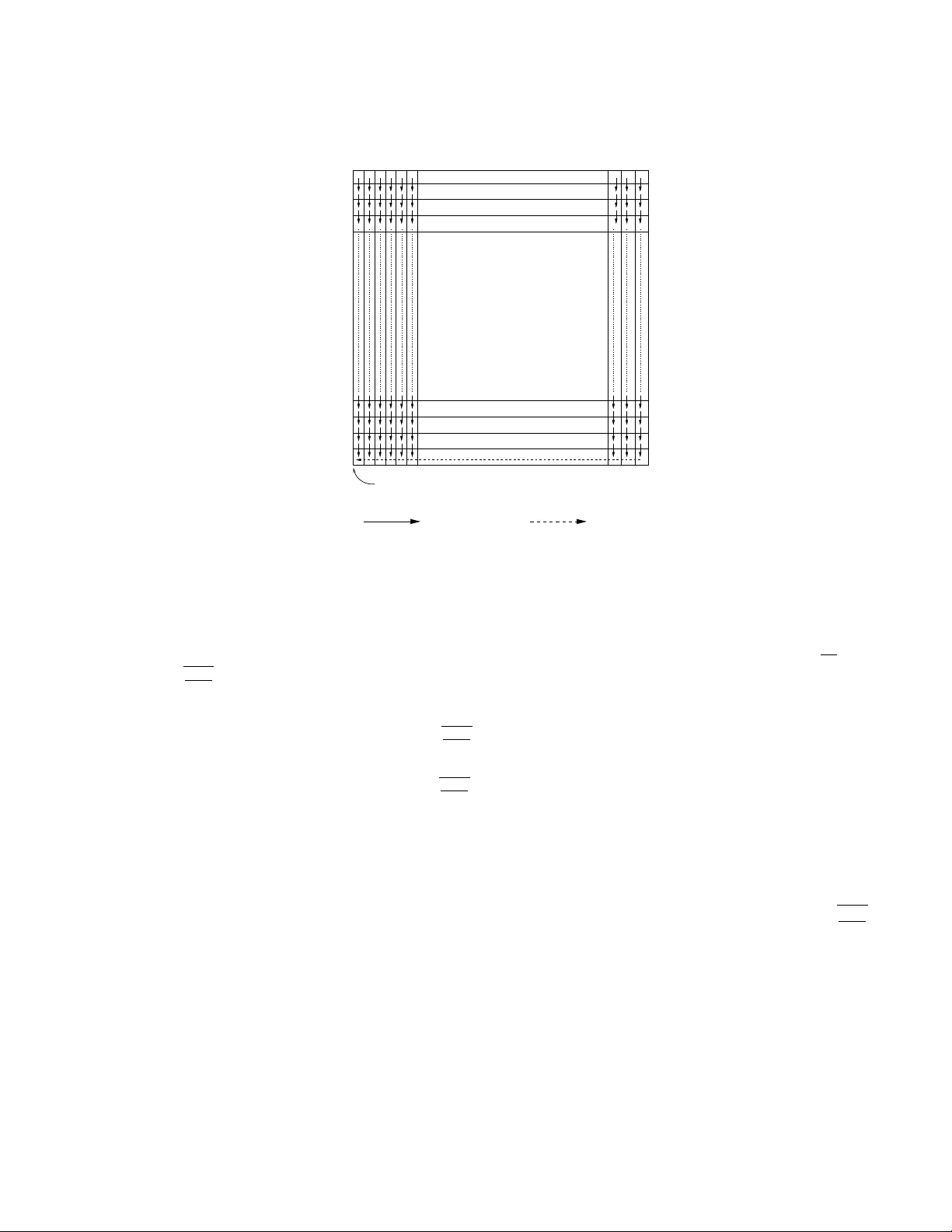
On Distributed F unction Computation in Structure-F ree Random Net w orks Sudeep Kamath and D. Manjunath ∗ Dept of Electrical Engg I IT Bom bay Mum bai INDIA 400 076 sudeep,dmanju@ee.iitb.ac.in Abstract THIS P APER IS ELIGIBLE FOR THE STUDENT BEST P APER A W ARD. W e consider in-net work computation of MAX in a structure-free random m ultihop wireless net work. No des do not kno w their relative or absolute lo cations and use the Aloha MAC proto col. F or one-shot computation, w e describ e a protocol in whic h the MAX v alue b ecomes a v ailable at the origin in O ( p n/ log n ) slots with high probabilit y . This is within a constan t factor of that required b y the b est co ordinated protocol. A minimal structure (knowledge of hop-distance from the sink) is imposed on the netw ork and with this structure, w e describ e a proto col for pipelined computation of MAX that ac hieves a rate of Ω(1 / (log 2 n )) . 1 In tro duction Early w ork on computation of functions of binary data o ver wireless net works focused on computing o ver noisy , time-slotted, broadcast net works, e.g., [1, 6]. With increasing interest in wireless sensor net works, recent research has concen trated on ‘in-netw ork’ computation ov er m ultihop wireless net works, e.g., [2, 5, 4], which also assume that time is slotted. The primary fo cus of the ab ov e researc h has b een to define an oblivious proto col that iden tifies the no des that are to transmit in eac h slot. This implies that the no des hav e organized themselv es in to a netw ork and hav e their clo c ks synchronized. Both of these require significant effort. In this paper w e describ e a proto col for in-net work computation of MAX in a structure-free net work, (i.e., in a net work where nodes do ∗ Researc h carried out at the Bharti Centre for Communication Research and supp orted in part b y gran ts from the Ministry of Information T echnology of Gov ernment of India A ccepted a t ISIT 2008 1 not ha ve an iden tity and hence do not kno w the top ology) that uses the Aloha MAC proto col. W e first describ e the One-Shot MAX proto col for one-shot computation of the MAX and its analysis. W e sho w that, with high probability (w.h.p.), the sink will hav e the result in a time that is within a constan t factor of that required by a structured netw ork. W e then imp ose a minimal structure and describ e the Pipelined MAX proto col and its analysis. W e show that the rate of computing the MAX in this net work is Ω( 1 log 2 n ) . 2 MAX in Multihop Aloha n nodes are uniformly distributed in [0 , 1] 2 and eac h no de is assumed to kno w n. The sink, the no de that is to ha v e the v alue of the MAX , is at the origin. The nodes do not ha ve an identit y and they do not know either their relative or their absolute p ositions. Hence, the netw ork does not kno w its top ology . This of course means that a schedule for transmissions cannot b e defined. Thus a random access proto col is an obvious c hoice at the MA C lay er. W e first assume that the nodes use the s-Aloha MAC proto col. F or p edagogical con v enience, we will assume slotted-Aloha at the MA C la y er. The analysis easily extends to the case of pure Aloha MA C. Spatial reuse is analyzed using the w ell-known proto col mo del of interference [3]. F or s-Aloha, this mo del translates to the follo wing. Consider a transmitter at lo cation x 1 transmitting in a slot t. A receiver at location x 2 , can successfully deco de this transmission if and only if the following t wo conditions are satisfied. (1) k x 2 − x 1 k < r n , and (2) k x 2 − x 3 k > (1 + ∆ 0 ) r n for some constant ∆ 0 ≥ 0; x 3 is the lo cation of an y other no de transmitting in slot t. r n is called the transmission radius. A transmission in slot t is deemed successful if all nodes within r n of the transmitter receiv e it without collision. The following is a sufficient condition for successful transmission b y a no de lo cated at x in a slot: k x − x 0 k > (1 + ∆) r n , ∆ = 1 + ∆ 0 , for every other no de transmitting in that slot and located at x 0 . 2.1 One-shot computation of MAX using Aloha Let Z i b e the v alue of the one-bit data at No de i and Z := max 1 ≤ i ≤ n Z i . The proto col One-Shot MAX is as follo ws. No de i can either receive or transmit in a slot but not both. In slot t, No de i will either transmit, with probabilit y p or listen, with probability (1 − p ) , indep enden tly of all the other transmissions in the netw ork. Let X i ( t ) be the v alue of the bit received (i.e., correctly deco ded in the absence of a collision) by No de i in slot t, t = 1 , 2 , . . . . If Node i transmits in slot t or if it senses a collision or idle in the slot, then it sets X i ( t ) = 0 . Define Y i (0) = Z i and A ccepted a t ISIT 2008 2 Y i ( t ) := max { Y i ( t − 1) , X i ( t ) } for t = 1 , 2 , . . . . Y i ( t ) is the ‘running MAX’ at No de i in slot t. If No de i transmits in slot t, it will transmit T i ( t ) = Y i ( t − 1) . It is easy to see that the correct v alue of Z will ‘diffuse’ in the net work in ev ery slot. The p erformance of the protocol, that is, the diffusion time, dep ends on p. The c hoice of p is discussed in Section 3. T o study the progress of the diffusion, we will consider a tessellation of the unit square in to square cells of side s n = d q n 2 . 75 log n e − 1 . This will result in l n := 1 s n = d q n 2 . 75 log n e rows (and columns) of cells in [0 , 1] 2 . There will be a total of M n := 1 s 2 n = d q n 2 . 75 log n e 2 cells. Let C denote the set of cells under this tessellation. Let S c b e the set of no des in Cell c and N c b e the num b er of nodes in Cell c. Under this tessellation, tw o cells are said to b e adjac ent if they hav e a common edge. Let the transmission radius be r n = q 13 . 75 log n n ≈ √ 5 s n . F or this v alue of r n the net work is connected w.h.p. [3]. The exp ected n um b er of no des in a cell is ns 2 n ≈ 2 . 75 log n. F urther, from Lemma 3.1 of [7], for our choice of r n and s n , Pr ( c 1 log n ≤ N c ≤ c 2 log n for 1 ≤ c ≤ M n ) → 1 (1) where c 1 = 0 . 091 and c 2 = 5 . 41 . Our results will hold for netw orks that are connected and which satisfy (1). F rom the choice of r n (i.e., r n ≥ √ 5 s n ) a successful transmission b y an y node from Cell c is correctly decoded b y all no des in Cell c as well as by all nodes in cells adjacen t to Cell c. The v alue of Z can reach the sink along any of the many p ossible trees ro oted at the sink. F or our analysis, we will divide the progress of the diffusion into the following three ‘phases’ and analyze eac h of the three phases separately . W e reiterate that the ab ov e sequence of phases is for the purp ose of analysis of the time to diffusion. The nodes do not p erform an y suc h organization. • Phase I for data aggr e gation within e ach c el l. This phase is completed when every no de of the netw ork has transmitted successfully at least once. • Phase II for pr o gr ess to the b ottom of the squar e. In this phase, the lo cally computed v alues of the MAX get diffused into the cells on one side of the unit square as shown in Fig. 1. • Phase III for pr o gr ess into the sink. In this phase, the v alue of MAX reaches the sink at the origin in the manner sho wn in Fig. 1. W e show in Section 3 that Phase I will be completed in O (log 2 n ) slots w.h.p., Phase II and Phase I I I will eac h b e completed in O q n log n slots w.h.p. These results are combined in to the following theorem. A ccepted a t ISIT 2008 3 Phase II Phase III Sink located at the origin Figure 1: Direction of diffusion during Phase II and Phase II I of proto col One-Shot MAX Theorem 1 If al l the no des exe cute the pr oto c ol One-Shot MAX , then for any α, k > 0 , the maxi- mum of the binary data at the n no des is available at the sink with pr ob ability at le ast 1 − k n α in O q n log n slots. W e will also argue that in another O q n log n n umber of slots, the v alue of Z would ha ve diffused to each no de of the net work. Note that the b est one-shot protocol in an organized net work, under this choice of r n will also require Θ q n log n time slots for a one-shot computation of MAX . The b ound on the time in Theorem 1 is therefore tigh t. 2.2 Pip elined computation of MAX using Aloha If Z were to be computed contin uously using the One-Shot MAX proto col, a throughput of Θ q log n n can b e ac hieved. W e b elieve some structure in the net work is necessary to do b etter. W e will as- sume that all no des ha ve a transmission range that is exactly r n . This strict requirement can b e easily relaxed but we will k eep this assumption for p edagogical con v enience. W e imp ose the follo wing structure in the netw ork. Prior to the computation, eac h no de obtains its minim um hop distance to the sink. Henceforth, w e will refer to this as simply the hop distanc e of A ccepted a t ISIT 2008 4 the no de. F rom (1), each cell in the tessellation is occupied. Since nodes in adjacent cells differ in their hop distance b y atmost 1 , the largest hop distance of a no de in the net work is no more than d := 2 l n = 2 d q n 2 . 75 log n e . Let h i b e the hop distance of No de i. Observe that a transmission by No de i can b e deco ded successfully by No de j only if | h i − h j | ≤ 1 . Hence, if there is a reception by Node i in slot t, then that transmission must hav e b een made b y a no de with hop distance either ( h i − 1) , h i , or ( h i + 1) . Th us, if a node transmits its hop distance mo dulo 3 along with its transmitted bit, then ev ery receiv er that can deco de this transmission successfully , can also, b y the receiv er’s knowledge of its o wn hop distance, correctly iden tify the hop distance of the transmitter. Time is divided in to r ounds , where each round consists of τ slots. Minimizing τ w ould maximize the throughput. W e will discuss this in Section 3. Data arrives at each no de at the b eginning of eac h round, that is, at the rate of 1 data bit per round. Let the v alue of the bit at No de i in the round r b e Z i ( r ) . Z ( r ) := max 1 ≤ i ≤ n Z i ( r ) , for r = 1 , 2 , . . . , is to b e made av ailable at the sink no de, No de s. Pip elined MAX proto col is as follo ws. The sink only receives data and do es not transmit. The other no des in the netw ork perform the follo wing. (W e remind here that the naming of the no des is for our conv enience. The nodes themselv es do not know their iden tity .) In eac h slot, No de i either transmits with probability p or listens with probabilit y (1 − p ) indep en- den tly of all other transmissions in the netw ork. The v alue of p is c hosen as in the One-Shot MAX proto col. Each no de executes the follo wing proto col for round r. T r ansmission: If Node i transmits in slot t of round r , then it transmits three bits ( A i , B i , T i ( r , t )) in the slot. Bits A i and B i are the identific ation bits and are obtained as ( h i mo d 3) . The bit T i ( r , t ) is the transmitted data bit and is obtained as T i ( r , t ) = max { Z i ( r − d + h i ) , Y i ( r − 1) } . Here, b y con ven tion, Z i ( v ) = Y i ( v ) = 0 for v ≤ 0 . Y i ( r − 1) is computed from succesful receptions in round ( r − 1) , as described b elo w. R e c eption: In round r , No de i main tains Y i ( r , t ) for t = 0 , 1 , 2 , . . . , τ . Y i ( r , 0) is initialized to 0 at the b eginning of round r . Y i ( r , t ) stores the MAX of the data bits that No de i has deco ded from all the slots in round r, upto and including slot t, and which w ere transmitted by the nodes with hop distance ( h i + 1) . In slot t of round r , if No de i successfully receiv es a transmission from a no de with hop distance ( h i + 1) (a v ailable from the iden tification bits), then it sets the received data bit to be X i ( r , t ) . If Node i senses an idle or a collision in slot t, or if it receiv es a successful A ccepted a t ISIT 2008 5 transmission from a no de with hop distance differen t from ( h i + 1) , then it sets X i ( r , t ) = 0 . Th us, Y i ( r , t ) = max { Y i ( r , t − 1) , X i ( r , t ) } . Define Y i ( r ) := Y i ( r , τ ) . The sink no de, No de s, obtains the MAX as Z ( r − d ) = max { Z s ( r − d ) , Y s ( r ) } , for all r > d. The dela y of the protocol is d rounds or dτ time slots. Theorem 2 If al l the no des exe cute the pr oto c ol Pip elined MAX , then for any α, k > 0 , ther e exists τ = τ ( α, k ) = Θ(log 2 n ) so that the c orr e ct MAX is available at the sink in a r ound with pr ob ability atle ast 1 − k n α . This achieves a thr oughput of Ω 1 log 2 n with a delay of O ( p n log 3 n ) slots. The optimal pip elined protocol for MAX in an organized netw ork requires Θ(log n ) slots for each round in the absence of block co ding. Thus, the p enalty for minimal organization and no co ordina- tion is the log n o v erhead for the length of eac h round. Also, for our proto col, No de i, with a hop distance of h i , requires a memory of ( d − h i + 1) bits to store Z i ( r ) , Z i ( r − 1) , . . . , Z i ( r − d + h i ) . Th us, the proto col requires eac h no de to ha ve ( d + 1) bits of memory for storage of past data v alues. 3 Pro ofs 3.1 Preliminaries 3.1.1 Bounding the Number of In terfering Neigh b ors Define the in terfering neighborho o d of No de i b y N ( I ) i := { j : 0 < k X i − X j k ≤ (1 + ∆) r n } . As discussed earlier, a transmission from No de i in slot t is deemed successful if all no des within r n of No de i can deco de this transmission without a collision. A sufficien t condition for Node i to b e successful in transmitting in slot t is that no no de b elonging to N ( I ) i m ust transmit in slot t. F rom the proto col mo del, the choice of s n and (1), the set of no des that in terfere with a transmission from a no de in Cell c , (i.e., S i ∈ S c N ( I ) i ) is con tained within an interference square cen tered at Cell c. This square con tains k 1 = 2 d (1+∆) r n s n e + 1 2 cells. F rom (1), |N ( I ) i | ≤ k 1 c 2 log n − 1 (2) Observ e that k 1 is a constan t for large enough n. A ccepted a t ISIT 2008 6 3.1.2 Probabilit y of a successful transmission from a cell Let P i b e the probability that No de i transmits successfully in a slot and P ( c ) , the probability that some no de in Cell c transmits successfully in a slot. P i ≥ p (1 − p ) |N ( I ) i | , and from (2), we hav e P i ≥ p (1 − p ) k 1 c 2 log n − 1 . Successful transmissions b y nodes from Cell c are m utually disjoin t ev ents, and hence, P ( c ) = P i ∈ S c P i ≥ N c p (1 − p ) k 1 c 2 log n − 1 . F rom (1), w e ha ve N c ≥ c 1 log n ∀ c ∈ C and hence, P ( c ) ≥ c 1 log n p (1 − p ) k 1 c 2 log n − 1 . Cho osing p = 1 k 1 c 2 log n maximises the lo w er bound in this inequalit y and yields P ( c ) ≥ c 1 k 1 c 2 „ 1 + 1 k 1 c 2 log n − 1 « − ( k 1 c 2 log n − 1) ≥ c 1 k 1 c 2 e =: p S Th us, the probabilit y of successful transmission from a cell is low er b ounded by a constant p S , indep enden t of the n umber of no des in the net w ork. This will b e crucial to our analysis. 3.2 Pro of of Theorem 1 W e will pro ve Theorem 1 by proving b ounds on the total time required by eac h of phases I, I I and I I I. 3.2.1 Phase I: Data aggregation within eac h cell Consider Cell c. Let T c b e the total n umber of slots required for every no de in Cell c to hav e transmitted successfully atleast once. Recall that p = ( k 1 c 2 log n ) − 1 . W e will b ound T c b y stochastic domination. Consider a sample space S containing mutually disjoint even ts E 1 , E 2 , . . . , E N c . Let Pr ( E q ) = p (1 − p ) k 1 c 2 log n − 1 for 1 ≤ q ≤ N c . Observe that P i ≥ Pr ( E q ) ∀ i ∈ S c and 1 ≤ q ≤ N c . Let E = S N c q =1 E q . W e hav e P E := Pr ( E ) = N c p (1 − p ) k 1 c 2 log n − 1 . Let a sequence of samples b e dra wn indep enden tly from S . Let the n umber of samples required to be drawn from S so that eac h of the even ts E q , q = 1 , 2 , . . . N c o ccurs atleast once, b e the random v ariable T 0 c . The probability of o ccurence of E in a given sample is P E and hence, the waiting time in terms of num b er of samples dra wn, for the even t E to o ccur, as well as the waiting time b etw een consecutiv e o ccurences of E , is given by the geometrically distributed random v ariable Geom( P E ) . Now, consider the ev ents of successful occurences of even t E . If ( l − 1) distinct even ts among E q , 1 ≤ q ≤ N c ha ve already o ccured, then the probability that the next o ccurence of E is due to an as y et unoccured even t E q 0 is (1 − l − 1 N c ) , as each E q , 1 ≤ q ≤ N c is equally probable. The n umber of o ccurences of ev ent E to w ait for the o ccurence of an as y et uno ccured even t among E q , 1 ≤ q ≤ N c is distributed A ccepted a t ISIT 2008 7 as Geom(1 − l − 1 N c ) . The random v ariable T 0 c can thus, b e expressed as: T 0 c = P R 0 c j =1 t 0 c,j where t 0 c,j ∼ Geom( P E ) and R 0 c ∼ P N c l =1 Geom(1 − l − 1 N c ) . No w compare the following tw o even ts: (1) Even t A defined as the successful transmission from Cell c resulting from a successful transmission by No de i in Cell c and (2) Even t B defined as the o ccurrence of E in a sample dra wn from S due to the o ccurence of E q . Observe that Pr ( A ) ≥ Pr ( B ) . F rom this comparison, we see that T c will b e sto chastically dominated by T 0 c i.e. Pr ( T c ≥ z ) ≤ Pr ( T 0 c ≥ z ) ∀ z ∈ N . F urther, T 0 c will b e sto c hastically dominated by the random v ariable T c = P R c j =1 t c,j , where t c,j ∼ Geom( p S ) and R c ∼ P m l =1 Geom(1 − l − 1 m ) with m = d c 2 log n e whic h is an upp er b ound on N c from (1). W e therefore, ha ve Pr ( T c ≥ z ) ≤ Pr ( T c ≥ z ) ∀ z ∈ N It is con venien t to w ork with the random v ariable T c b ecause it is indep enden t of the parameters of Cell c. W e will obtain the moment generating functions (mgf ) of the distributions of the integer- v alued random v ariables inv olv ed. Let the mgf of each random v ariable b e denoted by the same c haracter in sans serif font. F or a random v ariable F, F ( z ) = P j ∈ Z Pr ( F = j ) z − j . The region of con vergence of the mgf is sp ecified in paren theses. t c , j ( z ) = p S z − 1 1 − (1 − p S ) z − 1 := S ( z ) ( | z | > 1 − p S ) R c ( z ) = Π m l =1 (1 − l − 1 m ) z − 1 1 − l − 1 m z − 1 | z | > 1 − 1 m T c ( z ) = X r ∈ N Pr ( R c = r ) [ S ( z )] r = R c 1 S ( z ) = m ! p m S Π m l =1 ( m [ z − (1 − p S )] − ( l − 1) p S ) | z | > 1 − p S m Th us, E [ e sT c ] = m ! p m S Π m l =1 ( m [ e − s − (1 − p S )] − ( l − 1) p S ) for s < log 1 1 − p S m . Cho ose s 1 = log 1 1 − p S 2 m . After some algebra, w e can sho w the following. E [ e s 1 T c ] = m ! p m S m m Π m l =1 e − s 1 − 1 + m − l + 1 m p S − 1 = c m √ π m. A ccepted a t ISIT 2008 8 Here c m = 2 2 m 0 B @ 2 m m 1 C A √ π m → 1 as m → ∞ b y the Stirling appro ximation. F rom the Chernoff bound w e get Pr ( T c ≥ V 1 ) ≤ Pr ( T c ≥ V 1 ) ≤ c m √ π m 1 − p S 2 m V 1 . By the union bound, w e ha v e Pr max c ∈C T c ≥ V 1 ≤ M n c m √ π m 1 − p S 2 m V 1 T o ac hiev e Pr (max c ∈C T c ≥ V 1 ) ≤ k n α , it is sufficient to ha ve (1 − p S 2 m ) V 1 ≤ k n α M n c m √ π m or V 1 ≥ 1 2 log m + log M n + α log n − log k + 1 2 log π + log c m − log(1 − p S 2 m ) Here, m = d c 2 log n e , M n = d q n 2 . 75 log n e 2 . W riting − log 1 − p S 2 m = p S 2 m + p 2 S 2(2 m ) 2 + . . . , we can see that there exists a c hoice of V 1 = O (log 2 n ) , which would b e sufficien t for the completion of Phase I, i.e., ev ery node in every cell of the net w ork w ould ha ve successfully transmitted at least once in V 1 slots, with probabilit y at least 1 − k n α . 3.2.2 Phase I I: Progress to the b ottom of the square Let the columns of cells shown in Fig. 1 be n umbered C 1 , C 2 , . . . , C l n . Let the l n cells in each column b e num b ered from 1 to l n from top to bottom. In this phase, w e are concerned with transmissions in the top w := l n − 1 cells of eac h column. In Phase I, eac h no de has successfully receiv ed the transmissions b y every other no de in its cell. Hence, Phase I I will b e completed if the follo wing sequence of ev ents o ccurs for each column C : A successful transmission b y some node in the first cell of the column, follow ed by a successful transmission b y some no de in the second cell of the column and so on un til a successful transmission b y some no de in the w -th cell of the column. Let the num b er of slots required for this sequence of even ts b e T ( C ) for column C . W e can see that T ( C ) will b e sto c hastically dominated b y T ( C ) := P w j =1 t ( C ) j , where t ( C ) j ∼ Geom( p S ) . W e can th us A ccepted a t ISIT 2008 9 deriv e the following. T ( C ) ( z ) = p w S z − w (1 − (1 − p S ) z − 1 ) w ( | z | > 1 − p S ) E [ e sT ( C ) ] = p w S ( e − s − (1 − p S )) w for s < log 1 1 − p S Pr T ( C ) ≥ V 2 ≤ E [ e s 2 T ( C ) ] e s 2 V 2 = 2 w (1 − p S 2 ) V 2 Pr max 1 ≤ j ≤ l n T ( C j ) ≥ V 2 ≤ l n 2 w (1 − p S 2 ) V 2 where w e hav e used s 2 = log( 1 1 − p S 2 ) in the Chernoff b ound. Thus, to achiev e Pr max 1 ≤ j ≤ l n T ( C j ) ≥ V 2 ≤ k n α , it suffices to ha v e (1 − p S 2 ) V 2 ≤ k n α l n 2 w or V 2 ≥ α log n + log l n + w log 2 − log k − log (1 − p S 2 ) No w, l n = d q n 2 . 75 log n e = w + 1 , and hence, V 2 = O q n log n slots are sufficien t for the completion of Phase II with probability at least 1 − k n α . 3.2.3 Phase I I I: Progress into the sink Phase I I I comprises diffusion of the MAX in to the cell con taining the sink. Let the time required for this to happ en b e the random v ariable T s . It is easily seen from the analysis of the sequence of transmission for Phase I I that Pr ( T s ≥ V 3 ) ≤ 2 w (1 − p S 2 ) V 3 where w is as defined b efore. Calculations similar to those in the analysis for Phase I I sho w that V 3 = O q n log n slots are sufficient for completion of this phase with probability at least 1 − k n α . 3.2.4 Bound on the ov erall time Since eac h of phases I, II and I I I get completed in O q n log n time slots with probabilit y at least 1 − k 0 n α , for appropriate constan ts k 0 , the proto col One-Shot MAX achiev es computation of the MAX at the sink in O q n log n n umber of time slots with probability at least 1 − k n α . If the proto col is follow ed for another V 3 + V 2 slots, the true MAX will diffuse to the complete bottom row, A ccepted a t ISIT 2008 10 and then to the complete netw ork, the direction of diffusion b eing opp osite to that in Phase I I I and Phase II resp ectiv ely . 3.3 Obtaining the Hop Distance The following algorithm Hop Distance Compute obtains the hop distance for eac h no de in the net work. d log d e slots are group ed in to a fr ame and τ = Θ(log 2 n ) ( τ = V 1 as obtained in Phase I analysis of proto col One-Shot MAX ) frames form a sup erfr ame. The algorithm ends after ( d + 1) sup erframes. Let the superframes b e denoted by g 0 , g 1 , . . . , g d . A node either transmits in ev ery slot of a frame or it does not transmit in an y slot of the frame. Each transmission is a n umber expressed in d log d e bits. A t the b eginning of the algorithm, the sink transmits the num b er 0 expressed in d log d e bits in eac h frame of sup erframe g 0 . Each no de of the net work other than the sink executes the follo wing algorithm. No de i mak es no transmission till it has decoded a transmission successfully . Let the first successful reception by Node i happ en in a frame belonging to sup erframe g i and let the deco ded transmission corresp ond to the num b er n i expressed in d log d e bits. Node i sets its hop distance to ( n i + 1) and ignores other successfully received bits in frames from sup erframe g i . During the τ frames from sup erframe g i +1 , No de i transmits, in eac h frame, the n umber ( n i + 1) expressed in d log d e bits, with probability p, indep endently of all the other transmissions in the net work and mak es no transmission with probability (1 − p ) . After the end of round g i +1 , No de i mak es no more transmissions. The total n umber of slots required is ( d + 1) τ d log d e . Lemma 1 The no des of the network c orr e ctly c ompute their minimum hop distanc e fr om the sink, using Hop Distance Compute in O ( p n log 5 n ) time slots with pr ob ability at le ast 1 − k n α for any p ositive α and some c onstant k . W e omit the proof of this lemma. 3.4 Pro of of Theorem 2 Let the set of no des at hop distance h b e G h . Let t i,r b e the first slot in round r that No de i transmits succesfully in. The num b er of slots in a round is τ = Θ(log 2 n ) ( τ = V 1 from Phase I). Ev ery no de in the netw ork would hav e transmitted successfully at least once in eac h round of τ slots w.h.p. Let h max ≤ d be the largest hop distance of a no de in the netw ork. In the pro of, w e will assume that eac h no de of the net work transmits successfully in eac h round at least once. W e A ccepted a t ISIT 2008 11 claim that max i ∈ G h T i ( r , t i,r ) = max j ∈ S h ≤ f ≤ d G f Z j ( r − d + h ) for 0 ≤ h ≤ h max and r > d − h. The sink b eing at hop distance 0 , proving the claim will complete the pro of. Assume that the claim is true for h 0 < h ≤ h max for r > d − h. W e shall show that the claim will then b e true for h = h 0 and for r > d − h 0 . Consider transmissions by the nodes at hop distance h 0 in round ( r + 1) . max i ∈ G h 0 T i ( r + 1 , t i,r +1 ) = max i ∈ G h 0 { max { Z i ( r + 1 − d + h 0 ) , Y i ( r ) }} Since each no de at hop distance ( h 0 + 1) transmits successfully at least once in round r , the transmission of eac h suc h no de is deco ded successfully b y some no de at hop distance h 0 . Hence, max i ∈ G h 0 Y i ( r ) = max j ∈ G h 0 +1 T j ( r , t j,r ) = max j ∈ S h 0 +1 ≤ f ≤ d G f Z j ( r − d + h 0 + 1) where the second equality follows from the induction hypothesis. Hence, max i ∈ G h 0 T i ( r + 1 , t i,r +1 ) = max { max i ∈ G h 0 Z i ( r + 1 − d + h 0 ) , max j ∈ S h 0 +1 ≤ f ≤ d G f Z j ( r − d + h 0 + 1) } = max j ∈ S h 0 ≤ f ≤ d G f Z j ( r − d + h 0 + 1) } whic h prov es the claim for hop distance h 0 for round ( r +1) . By induction, the claim is true for eac h h and each round r > d − h. Therefore, the sink Node s correctly sets Z ( r − d ) = max { Z s ( r − d ) , Y s ( r ) } . The delay of the proto col is dτ = Θ( p n log 3 n ) slots. As transmissions by different no des are indep endent, the analysis in the diffusion of phase I of One-Shot MAX carries o ver. The probability that the computed v alue of Z ( r ) is incorrect for an y giv en round is upper bounded b y k n α for any constants α, k > 0 . A ccepted a t ISIT 2008 12 4 Discussion The total num b er of transmissions (successful as well as unsuccessful) in one execution of One-Shot MAX is Θ( n 3 / 2 log 3 / 2 n ) . In Pip elined MAX , a total of Θ( n log n ) transmissions are made p er round. Note that the corresponding n umber is Θ( n ) with a co ordinated proto col for both cases. Our analysis can be extended to the case where the no des use pure Aloha as the MA C. W e need to use a transmission rate rather than a transmission probability . The success probabilities are calculated similarly except that we now ha ve a collision window that is twice the pac ket length. All calculations are analogous. It is fairly straigh tforward to sho w that in a noiseless, structure-free broadcast net work, the his- togram can b e computed in Θ( n ) slots w.h.p. In the noisy broadcast net work, b y a simple mo di- fication of the proto col of [1], we can show that the histogram can b e computed in Θ( n log log n ) slots w.h.p. References [1] R. G. Gallager. Finding parity in simple broadcast net works. IEEE T r ans. on Info. The ory , 34:176–180, 1988. [2] A. Giridhar and P . R. Kumar. Computing and comm unicating functions o v er sensor net w orks. IEEE Journal on Sele cte d Ar e as in Communic ations , 23(4):755–764, April 2005. [3] P . Gupta and P . R. Kumar. Critical pow er for asymptotic connectivity in wireless netw orks. In W. M. McEneaney , G. Yin, and Q. Zhang, editors, Sto chastic A nalysis, Contr ol, Optimization and Applic ations: A V olume in Honor of W. H. Fleming . Birkhauser, Boston, 1998. [4] Y. Kanoria and D. Manjunath. On distributed computation in noisy random planar net works. In Pr o c. of IEEE ISIT , Nice, F rance, June 2007. [5] N. Kh ude, A. Kumar, and A. Karnik. Time and energy complexit y of distributed computation in wireless sensor netw orks. In Pr o c e e dings of IEEE INFOCOM , pages 2625–2637, 2005. [6] E. Kushilevitz and Y. Mansour. Computation in noisy radio net w orks. In Pr o c. of SODA , pages 236–243, 1998. [7] F. Xue and P . Kumar. The n um b er of neigh b ors needed for connectivit y of wireless net works. Wir eless Networks , 10(2):169–181, March 2004. A ccepted a t ISIT 2008 13
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment