Decentralized Two-Hop Opportunistic Relaying With Limited Channel State Information
A network consisting of $n$ source-destination pairs and $m$ relays is considered. Focusing on the large system limit (large $n$), the throughput scaling laws of two-hop relaying protocols are studied for Rayleigh fading channels. It is shown that, u…
Authors: Shengshan Cui, Alex, er M. Haimovich
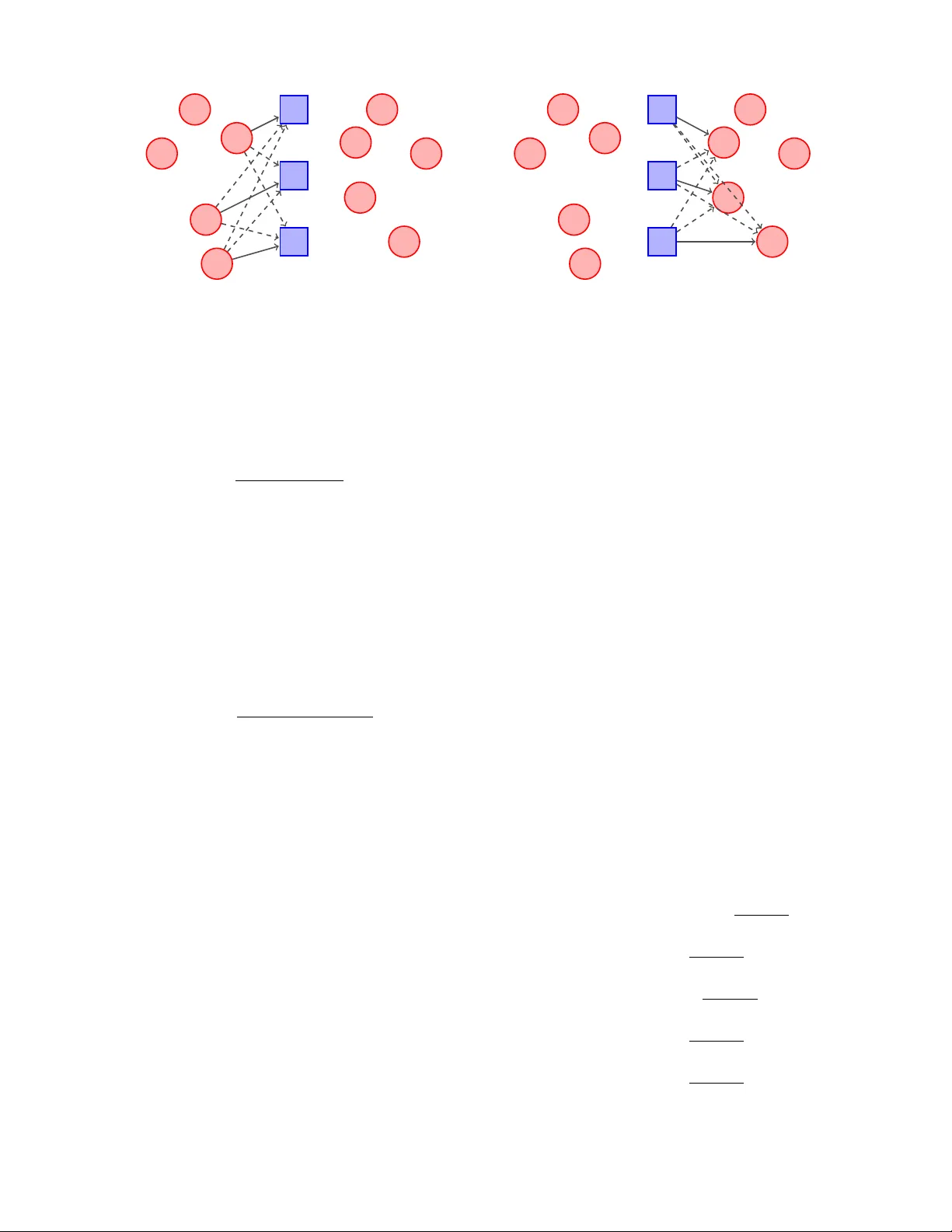
Decentralized T wo-Hop Opportunistic Relaying W ith Limited Channel State Information Shengshan Cui and Alexander M. Haimo vich Department of Electrical and Computer Engineering New Jerse y Institute of T echnology , Ne wark, NJ 07102, USA Email: { shengshan.cui, alexander .m.haimovich } @njit.edu Oren Somekh and H. V incent Poor Department of Electrical Engineering Princeton Univ ersity , Princeton, NJ 08544, USA Email: { orens, poor } @princeton.edu Abstract —A network consisting of n source-destination pairs and m relays with no dir ect link between source and destination nodes, is considered. Focusing on the large system limit (large n ), the throughput scaling laws of two-hop relaying protocols are studied for Rayleigh fading channels. It is shown that, under the practical constraints of single-user encoding-decoding scheme, and partial channel state information (CSI) at the transmitters (via integer -value feedback fr om the receiv ers), the maximal throughput scales as log n even if joint scheduling among relays is allowed. Furthermore, a novel opportunistic r elaying scheme with recei ver CSI, partial transmitter CSI, and decentralized relay scheduling, is shown to achieve the optimal throughput scaling law of log n . I . I N T R O D U C T I O N The ev er growing demand for ubiquitous access to high data rate services necessitates new network architectures, such as ad hoc and relay networks. Over the last decade, a large body of work analyzing the fundamental system throughput limits of such networks has been reported. In particular , numerous communication schemes approaching these limits under various settings have been proposed, e.g. [1]–[5]. Notably , Gowaikar et al. [2] proposed a ne w wireless ad hoc network model, whereby the strengths of the connections between nodes are drawn independently from a common dis- tribution, and analyzed the maximum system throughput under different fading distributions. Such a model is appropriate for en vironments with rich scattering but small physical size, so that the connections are governed by random fading instead of deterministic path loss attenuations (i.e., dense network). When the random channel strengths follow a Rayleigh fading model, the system throughput scales as Θ(log n ) . 1 This result is achie v able through a multihop scheme that requires central coordination of the routing between nodes. In this work, we focus on dense netw orks and two-hop relaying schemes, in which n source nodes communicate with n destination nodes via m relay nodes (no direct connection is allowed between sources and destinations). Dana and Hassibi hav e proposed an amplify-and-forward protocol in [4] and shown that a throughput of Θ( n ) bits/s/Hz is achiev able 1 Throughout the paper log( · ) indicates the natural logarithm. For two func- tions f ( n ) and g ( n ) , f ( n ) = O ( g ( n )) means that lim n →∞ | f ( n ) /g ( n ) | < ∞ , and the notation f ( n ) = o ( g ( n )) means that lim n →∞ | f ( n ) /g ( n ) | = 0 . W e write f ( n ) = Θ( g ( n )) to denote f ( n ) = O ( g ( n )) and g ( n ) = O ( f ( n )) . with m ≥ n 2 relay nodes. It is assumed that each relay node has full local channel state information (CSI) (backward channels from all source nodes, and forward channels to all destination nodes), so that the relays can perform distributed beamforming . In [5], Morgenshtern and B ¨ olcskei showed a similar distrib uted beamforming scheme which demonstrates tradeoffs between the le vel of a v ailable CSI and the sys- tem throughput. In particular , using a scheme with relays partitioned into groups, where relays assigned in the same group require knowledge of backward and forward channels of only one source-destination (S–D) pair , the number of relays required to support a Θ ( n ) throughput is m ≥ n 3 . Hence, restricting the CSI in such a way increases the number of required relays from n 2 to n 3 to support throughput of Θ( n ) . While the two-hop schemes reported in [4] and [5] do not require central coordination among relays (central coordina- tion is required for the multihop schemes of [1]–[3]), some lev el of transmitter CSI (channel amplitude and/or phase) is still required. In a lar ge system, obtaining this lev el of CSI, especially at the transmit side, may not be feasible. This consideration leads to the following questions: How does the throughput scaling change under a practical, partial CSI assumption? Can the throughput scaling bounds be approached with any specific schemes? In the sequel, we giv e partial answers to the questions above by restricting ourselves to decode-and-forward protocols. In Section II, an upper bound on the throughput is calculated in the large system regime. It is sho wn that with only partial CSI at the transmitters, the throughput scaling of any two- hop scheme is upper -bounded by Θ(log n ) . In Section III, an opportunistic relaying scheme that can achie ve the optimal scaling is proposed. This scheme operates in a completely de- centralized fashion and requires only recei ver CSI kno wledge and a low-rate feedback to the transmitters. Finally , Section IV concludes the paper . I I . T H R O U G H P U T S C A L I N G U P P E R B O U N D F O R T W O - H O P P RO TO C O L S In this section, we establish an upper bound on the through- put scaling of two-hop protocols. W e adopt the random connection model of [2] and specifically assume a Rayleigh fading model, i.e., the connections between any source-to- relay (S–R) pair and between any relay-to-destination (R–D) pair follow independent and identically distributed (i.i.d.) flat Rayleigh fading. W e assume that in each hop the receiv ers hav e perfect CSI knowledge of the channel realizations, but the transmitters do not hav e full CSI knowledge. W e assume a single-user encoding-decoding scheme, i.e, mutual interfering signals are treated as additiv e noise. Furthermore, we assume the transmission rate is fix ed, i.e., the transmission rate of each scheduled link is not adaptiv e to instantaneous signal- to-interference-plus-noise ratio (SINR). Accordingly , a trans- mission is deemed successful only if the SINR is not belo w a prescribed threshold. W e have the following throughput upper bound. Theor em 1: Under the aforementioned assumptions, the throughput of each hop scales at most as log n . Pr oof: (Outline) W e begin with the first hop. Since the transmission rate of each link is a fixed number , finding the throughput upper bound is equiv alent to finding the maximum number of concurrent successful transmissions. T o this end, we consider follo wing genie scheme. For any channel realization of the network, the genie scheme is assumed to hav e the full CSI of the netw ork, and thus is able to schedule in ev ery time-slot the largest set of concurrent successful S–R pairs. Specifically , in testing whether m concurrent successful transmissions are supported or not, the genie scheme will deploy m relays and test whether there exists an m -element subset of source nodes whose transmissions to relays are all successful. In doing so, the genie scheme will test all n m ways of choosing m sources for transmission. Moreover , for each combination of m sources, the genie scheme tests m ! possible ways of associating S–R pairs. If the genie scheme can find a combination, among all n m m ! possible combinations, such that all transmissions are successful, we claim that m simultaneous transmissions are achiev able. By a probabilistic argument, it is shown in [6, Th. 2] that with probability approaching 1 , one cannot find a set of log n log 2 + 2 nodes whose simultaneous transmissions to the relays are all successful. Conv ersely , with probability approaching 1 , and for an y > 0 , there e xists a set of (1 − ) log n 2 log 2 + 2 nodes whose simultaneous transmissions to relays are all successful. Since the genie scheme executes an exhausti ve search for maximum number of concurrent successful transmissions, it sets the upper bound for any decentralized scheme. Upper bound for the second hop can be deri ved similarly to the first hop. There, we seek to find the existence of an m -element destination set such that all m concurrent R–D transmissions are successful. The reader is referred to [6, Th. 2] for the complete proof. Theorem 1 implies that the throughput scaling of the two- hop scheme is upper-bounded by the order of log n . Thus, we are able to answer the first question raised at the outset of the paper: the lack of full transmitter CSI reduces the throughput scaling from a power law ( Θ( n 1 / 2 ) [4] and Θ( n 1 / 3 ) [5]) to a logarithmic law Θ(log n ) if n is interpreted as the total number of nodes in the network. When implementation is concerned, ho we ver , we note that the genie scheme in the proof requires joint scheduling among relays and thus is not readily implementable in practice. W e are left with the question as to whether the same throughput scaling is achie v able with practical constraints such as decentralized relay operation and low rate feedback. I I I . O P P O RT U N I S T I C R E L A Y I N G S C H E M E Assuming decentralized relay operation, the relays cannot cancel mutual interference and hav e to contend with single- user encoding-decoding in the two hops. Nevertheless, mul- tiuser div ersity gain, an innate feature of fading channels, is still av ailable and lends itself to distributed operation. It is shown in the sequel that, somewhat surprisingly , by exploiting the multiuser diversity , the throughput scaling of log n can be achiev ed with decentralized relay operations. T o enable the scheduling, the scheme requires an index-valued (integer) CSI from the receiv ers via lo w-rate feedback. A. Scheduling As illustrated in Fig. 1, the proposed opportunistic relaying scheme is a two-hop, decode-and-forward-based communica- tion protocol. In the first hop, a subset of sources is scheduled for transmission to the relays. Then, the relays decode and buf fer the packets receiv ed in the first hop. During the second hop, the relays forward packets to a subset of destinations (not necessarily the same set of destinations associated with the sources set in the first hop). The two phases (hops) are time-interleav ed: Phase 1 and Phase 2 take place in e ven and odd-index ed time-slots, respectiv ely . W e assume that the channel gains are dominated by the effects of small-scale fading. In particular , it is assumed that the wireless network consists of i.i.d. flat Rayleigh channels. Accordingly , the channel gain γ i,r between the i th source node ( 1 ≤ i ≤ n ) and the r th relay node ( 1 ≤ r ≤ m ), and the channel gain ξ k,j between the k th relay ( 1 ≤ k ≤ m ) and the j th destination node ( 1 ≤ j ≤ n ), are exponentially distributed random v ariables, i.e., γ i,r , ξ k,j ∼ Exp(1) . Quasi- static fading is assumed, in which channels are fixed during the transmission of each hop, and take on independent values at different time-slots. W e also assume that, in both hops, the receiv ers are a ware of their backward channel information, and allo w for an integer -v alue CSI feedback from recei vers to transmitters (relays to sources in Phase 1 , and destinations to relays in Phase 2 ). 1) F irst Hop Scheduling: The first hop scheduling can be thought of as a natural generalization of the classic multiuser- div ersity-scheme with single receiver antenna [7] to multiple, decentralized antennas. Specifically , all relays operate inde- pendently , and each relay schedules its best source by feeding back the index of the source. For example, relay r compares the channels γ i 0 ,r , 1 ≤ i 0 ≤ n , and schedules the transmission of the strongest source node, say i = arg max i 0 γ i 0 ,r , by feeding back the index i . The o verhead of this phase of the protocol is a single integer per relay node. Suppose the scheduled nodes constitute a set K ⊂ { 1 , . . . , n } , then since there are m relays, up to m source nodes can be scheduled, 1 2 3 4 5 6 7 8 9 10 1 2 3 (a) 1 2 3 4 5 6 7 8 9 10 1 2 3 (b) Fig. 1. A two-hop network with n = 5 S–D pairs and m = 3 relay nodes (denoted by the blue squares). (a) In the first hop, source nodes { 3 , 4 , 5 } transmit to the relays. (b) In the second hop, the relays transmit to the destination nodes. Solid lines indicate scheduled links, while dashed lines indicate interferences. i.e., |K| ≤ m (a source can be scheduled by multiple relays). The scheduled source nodes transmit simultaneously at the same rate of 1 bit/s/Hz. The communication from source i to relay r is successful if the corresponding SINR P1 ≥ 1 , i.e, SINR P1 i,r = γ i,r 1 /ρ + P t ∈K t 6 = i γ t,r ≥ 1 , (1) where ρ is the av erage signal-to-noise ratio (SNR) of the S–R link. 2) Second Hop Scheduling: In the second hop, the trans- mitters are the m relay nodes, and the multiuser div ersity is achiev ed by scheduling the destination nodes via a SINR ≥ 1 criterion. In particular , each destination node j , 1 ≤ j ≤ n , with the assumption of kno wing the forward channel strengths, ξ k,j , 1 ≤ k ≤ m , computes m SINRs by assuming that relay k is the desired sender and the other relays are interference: SINR P2 k,j = ξ k,j 1 /ρ R + P 1 ≤ ` ≤ m ` 6 = k ξ `,j , (2) where ρ R denotes the a verage SNR of the R–D link. If the destination node j captures one good SINR, say , SINR P2 k,j ≥ 1 for some k , it instructs relay k to send data by feeding back the relay index k . Otherwise, the node j does not provide feedback. It follows that the o verhead of the second hop is also at most an index value per destination node. When scheduled by a feedback message, relay k transmits the data to the destination node at rate 1 bit/s/Hz. In case a relay receiv es multiple feedback messages, it randomly chooses one destination for transmission. It is noted that in the steady state operation of the system, the relays are assumed to buf fer the data received from all source nodes, such that it is a vailable when the opportunity arises to transmit it to the intended destination nodes over the second hop of the protocol. This ensures that relays always hav e packets destined to the nodes that are scheduled. It should also be noted that, due to the opportunistic nature of scheduling, the receiv ed packets at the destinations are possibly out of order and therefore each destination is assumed to hav e capability of buf fering data. B. Thr oughput Analysis In this subsection, we first deri ve analytical expressions of the throughput for each hop assuming the system has a finite number of nodes. Then, we extract the scaling laws when the system size increases, i.e., n → ∞ , and compare those to the upper bounds established in the previous section. For the sake of brevity , we provide here only an outline of the deriv ation, and the reader is referred to [6] for more details. 1) F inite n and m : In the first hop, m relays independently schedule sources. The number of scheduled sources could be any integer between 1 and m . Accounting only for the case in which e xactly m sources are scheduled, the a verage throughput of the first hop can be lower -bounded as follows, R 1 ≥ m · Pr[ N m ] · Pr[ S m ] , (3) where Pr[ N m ] is the probability of having exactly m sources scheduled, implying a total transmission rate of m bits/s/Hz. Pr[ S m ] is the probability for a successful S–R transmission. By symmetry , each source node has a probability of 1 /n to be the best node with respect to a relay . Thus, Pr[ N m ] = n ( n − 1) · · · ( n − m + 1) /n m . For finite values of n and m , exact characterization of Pr[ S m ] is mathematically in volved. This is because the numerator (the maximum of n i.i.d. random variables) and the denominator (summation of some non- maximum random v ariables) are not independent. Fortunately , it is possible to further lower -bound Pr[ S m ] as follows, Pr[ S m ] = Pr[ SINR P1 ≥ 1] = Pr X 1 /ρ + Y ≥ 1 = Pr[ X ≥ s ] · Pr X 1 /ρ + Y ≥ 1 X ≥ s + Pr[ X ≤ s ] · Pr X 1 /ρ + Y ≥ 1 X ≤ s ≥ Pr[ X ≥ s ] · Pr X 1 /ρ + Y ≥ 1 X ≥ s ≥ Pr[ X ≥ s ] · Pr s 1 /ρ + Y ≥ 1 = 1 − F X ( s ) F Y ( s − 1 /ρ ) , (4) where X represents the maximum of n i.i.d. exponential ran- dom v ariables, whose cumulativ e distribution function (CDF) can be written explicitly as F X ( x ) = (1 − e − x ) n . The term F Y ( · ) denotes the CDF of the aggregate interference, which is sho wn in [6] to be well approximated to a chi-square random v ariable with 2( m − 1) degrees-of-freedom with CDF F Y ( y ) = 1 − e − y P m − 2 k =0 1 k ! y k , when n is suf ficiently large, e.g., n > 40 . Note that the lo wer bound (4) suggests a suboptimal scheduling scheme according to which, each relay schedules the transmission of the “strongest” source only if the source’ s po wer gain exceeds a prescribed threshold s . The probability of such event is giv en by 1 − F X ( s ) , and F Y ( s − 1 /ρ ) is a lo wer bound on the probability of a successful communication with the relay at a rate of 1 bit/s/Hz. Substituting the lower bound of Pr[ S m ] into (3), we get a lower bound on R 1 , as expressed in the following lemma. Lemma 1: For any ρ , n > m and s > 0 , the achiev able throughput of the opportunistic relay scheme of the first hop is lower -bounded by R 1 ≥ m n ( n − 1) ··· ( n − m +1) n m 1 − (1 − e − s ) n F Y s − 1 ρ . (5) T urning to the second hop and recalling that its scheduling is based on SINR instead of SNR, all transmissions are suc- cessful by definition. Thus, the throughput of the second hop depends on how many relays receive feedback and therefore transmit data packets to the destinations. Furthermore, a relay is scheduled when at least one destination measures its channel with SINR greater than or equal to one. Therefore, the average throughput can be characterized in a closed form expression, as formulated in the lemma. Lemma 2: For any ρ R , n and m , the achiev able throughput of the opportunistic relay scheme in the second hop is gi ven by R 2 = m 1 − 1 − e − 1 /ρ R 2 m − 1 n ! . (6) 2) Larg e n and F inite m : With the closed-form expressions of (5) and (6) at hand, we proceed to the regime of large n , but fixed m . The discussion of this regime is of practical impor- tance in that as communication de vices become perv asiv e, the number of infrastructure nodes (here the relays) is not likely to keep pace. As mentioned above, the parameter s in (5) can be in- terpreted as a scheduling threshold. Note that in a system with n sources and Rayleigh fading channels, the maximum channel gain seen by each relay is of the order of log n [8], we empirically set s = log n − log log n in (5). Then, it is easy to show that R 1 → m with n → ∞ . Similarly , letting n → ∞ in (6), results in R 2 → m . Now , since the av erage throughput of the two-hop scheme is R = 1 2 min { R 1 , R 2 } , we conclude that R → m 2 for n → ∞ . The results for large n and finite m are summarized in the following theorem. Theor em 2: For fix ed m , the tw o-hop opportunistic relaying scheme achie ves a system throughput of m/ 2 bits/s/Hz as n → ∞ . In the opportunistic scheme, we make practical assumptions of decentralized relays and partial CSI. Thus, it is instructiv e to compare the throughput of the opportunistic scheme with that of an unconstrained scheme. In fact, it is straightforward to show that, the information-theoretical sum-rate for any two- hop scheme is upper-bounded by m 2 log log n [6, Lemma 3], ev en if relay cooperation and full CSI at the relays are assumed. This upper bound (with cooperation and full CSI) can be interpreted as a multiple antenna system, which is well- known to be able to support m parallel channels. Moreov er , each of the parallel channels enjoys multiuser div ersity gain of log n that translates into a throughput of log log n . In contrast, the opportunistic scheme, with simplified network operation (decentralized operation and partial CSI assump- tion), has no such freedom to support m parallel channels with rate log log n . Ho we ver , it succeeds in preserving the pre-log f actor of the upper bound. Intuiti vely , the inherent multiuser div ersity gain, which is of the order of log n , is applied to compensate for the mutual interference stemming from concurrent transmissions and to make the scheduled links reliable. 3) Larg e n and m : Theorem 2 shows that when the number of S-D pairs n is large and the number of relay nodes m is fixed, the av erage system throughput scales linearly with m . This implies that one can increase the number of relays to increase system throughput. Howe ver , both (5) and (6) present a tradeoff of throughput in m : by making m large, one increases the number of transmissions, but as a consequence the reliability of each link degrades. Therefore, there exists an optimal value of m such that the throughput scaling is maximized. Finding the optimal order of m is equi v alent to finding the throughput scaling of the proposed opportunistic relaying scheme. Specifically , we are interested in finding whether the proposed scheme can achiev e the throughput scaling upper bound of Θ(log n ) established in Section II. T o prov e that the av erage throughput of the first hop indeed scales as Θ(log n ) , it is sufficient to show that the lower bound (5) achiev es scaling of order log n . T o this end, consider the case of m = log n and s = log n − log log n . W ith n → ∞ , it follows that n ( n − 1) ··· ( n − m +1) n m → 1 and 1 − (1 − e − s ) n → 1 . Furthermore, for m = log n , the interference term Y can be approximated by a Gaussian random variable with mean and variance both equal to log n . Due to the symmetry of the Gaussian distribution, we have F Y (log n − log log n − 1 /ρ ) ≈ F Y (log n ) = 1 2 . This result implies that if we deploy m = log n relays, with high probability , log n sources will be scheduled for transmission, and half of them will be, on average, successful. This yields an av erage throughput of 1 2 log n for the first hop. Examining the asymptotic behavior of (6) with respect to m and n , it is straightforw ard to sho w that the maximum throughput scaling of the second hop also scales as Θ(log n ) [6, Th. 3]: Theor em 3: For the second hop of the two-hop oppor - tunistic relaying scheme, if the number of relays m = log n − log log n − 1 /ρ R log 2 + 1 , then R 2 = Θ ( m ) = Θ (log n ) . Con versely , if m = log n +log log n − 1 /ρ R log 2 + 1 , then R 2 = o ( m ) . By considering two hops as a whole, we get the follo wing: Theor em 4: Under the setup of Section III, the proposed two-hop opportunistic relaying scheme yields a maximum achiev able throughput of Θ (log n ) . Interestingly , we see that the proposed opportunistic re- laying scheme, which assumes decentralized relay operations and practical CSI assumption, incurs no loss in achieving the optimal throughput scaling upper bound. This gi ves an affirmati ve answer to the second question posed at the outset of the paper . The achie vability of Θ(log n ) is also substantiated by Monte Carlo simulations. In the simulations, the av erage SNR of each hop is assumed to be 10 dB and the simulation curve was obtained by av eraging throughput over 2000 channel realiza- tions. In Fig. 2, the av erage system throughput of the two-hop opportunistic relaying scheme is sho wn as a function of the number of S–D pairs n . (Note that the throughput depends on both n and m . For each v alue of n , optimal throughput (by maximizing ov er m ) is plotted.) W e observe that the throughput exhibits the log n trend, as predicted by Theorem 4. It is also found in simulation that the system throughput is always limited by Phase 1 , i.e., R = 1 2 min { R 1 , R 2 } = 1 2 R 1 . Thus, we also plot 1 / 2 of the upper bound and lower bound of R 1 for reference. Recall that the a verage throughput of R 1 is upper-bounded by the genie bound log n 2 log 2 + 2 (cf. Theorem 1) and lower -bounded by 1 2 log n . Number of S–D Pairs, n A verage Throughput [bits/s/Hz] log n 4l o g2 +1 av erage R 1 4 log n 200 400 600 800 1000 1200 0 . 5 1 . 0 1 . 5 2 . 0 2 . 5 3 . 0 3 . 5 4 . 0 Fig. 2. Simulated average system throughput R and analytical upper and lower bounds. C. F eedback Overhead According to the opportunistic relaying scheme, a feedback mechanism is needed to schedule the good nodes enjoying multiuser diversity . By direct computation, it can be shown that, in the limiting operation regime of m = Θ(log n ) , the feedback overhead per fading block is Θ((log n ) 2 ) for the first hop and Θ(log n log log n ) for the second hop. The overhead of feedback is negligible when the block length is large. I V . C O N C L U S I O N In this paper , we have considered a network having n S–D pairs and m relay nodes, operating in the presence of Rayleigh fading. The emphasis is on characterizing the throughput scaling under the assumption of practical CSI requirement. It has been shown that the lack of full CSI at the relays reduces the throughput scaling drastically from a power law (e.g., Θ( n 1 / 2 ) [4]) to a logarithmic law Θ(log n ) in the total number of nodes n in the network. Furthermore, an opportunistic relaying scheme that operates in a completely decentralized fashion and assumes only CSI at receiv ers and partial CSI at the transmitters, has been proposed and sho wn to achie ve a throughput scaling of Θ(log n ) . Thus, the lack of joint scheduling among relays causes no loss of optimality as far as throughput scaling is concerned. An interesting subject for further research is the perfor - mance analysis of opportunistic relaying schemes employed in more general system models. In particular, models that include both small-scale fading and geographical attenuation (e.g. the model presented in [9]) are of interest. A C K N O W L E D G M E N T This research was supported in part by the U.S. National Science Foundation under Grants CNS-06-26611, CNS-06- 25637 and ANI-03-38807, and by a Marie Curie Outgoing International Fellowship within the 6th European Community Framew ork Programme. R E F E R E N C E S [1] P . Gupta and P . R. Kumar , “The capacity of wireless networks, ” IEEE T rans. Inf . Theory , vol. 46, no. 2, pp. 388–404, Mar . 2000. [2] R. Gowaikar , B. M. Hochwald, and B. Hassibi, “Communication over a wireless network with random connections, ” IEEE T rans. Inf. Theory , vol. 52, no. 7, pp. 2857–2871, Jul. 2006. [3] A. ¨ Ozg ¨ ur , O. L ´ ev ˆ eque, and D. N. C. Tse, “Hierarchical cooperation achiev es optimal capacity scaling in ad hoc networks, ” IEEE T rans. Inf. Theory , vol. 53, no. 10, pp. 3549–3572, Oct. 2007. [4] A. F . Dana and B. Hassibi, “On the power efficiency of sensory and ad hoc wireless networks, ” IEEE T rans. Inf. Theory , vol. 52, no. 7, pp. 2890–2914, Jul. 2006. [5] V . I. Morgenshtern and H. B ¨ olcskei, “Crystallization in large wireless networks, ” IEEE T rans. Inf. Theory , v ol. 53, no. 10, pp. 3319–3349, Oct. 2007. [6] S. Cui, A. M. Haimovich, O. Somekh, and H. V . Poor , “Opportunistic relaying in wireless networks, ” IEEE T rans. Inf. Theory , Dec. 2007, submitted for publication. [Online]. A vailable: http://arxi v .org/pdf/0712. 1169 [7] R. Knopp and P . Humblet, “Information capacity and power control in single cell multiuser communications, ” in Pr oc. IEEE Int. Conf. Communications , vol. 1, Seattle, W A, Jun. 1995, pp. 331–335. [8] P . V iswanath, D. N. C. Tse, and R. Laroia, “Opportunistic beamforming using dumb antennas, ” IEEE T rans. Inf. Theory , vol. 48, no. 6, pp. 1277– 1294, Jun. 2002. [9] R. Go waikar and B. Hassibi, “On the achie vable throughput in two-scale wireless networks, ” in Pr oc. IEEE Int. Symp. Information Theory , Seattle, W A, Jul. 2006.
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment