Physical Layer Network Coding Over Finite And Infinite Fields
Direct application of network coding at the physical layer - physical layer network coding (PNC) - is a promising technique for two-way relay wireless networks. In a two-way relay network, relay nodes are used to relay two-way information flows betwe…
Authors: Zhang Shengli, Soung chang Liew, Lu Lu
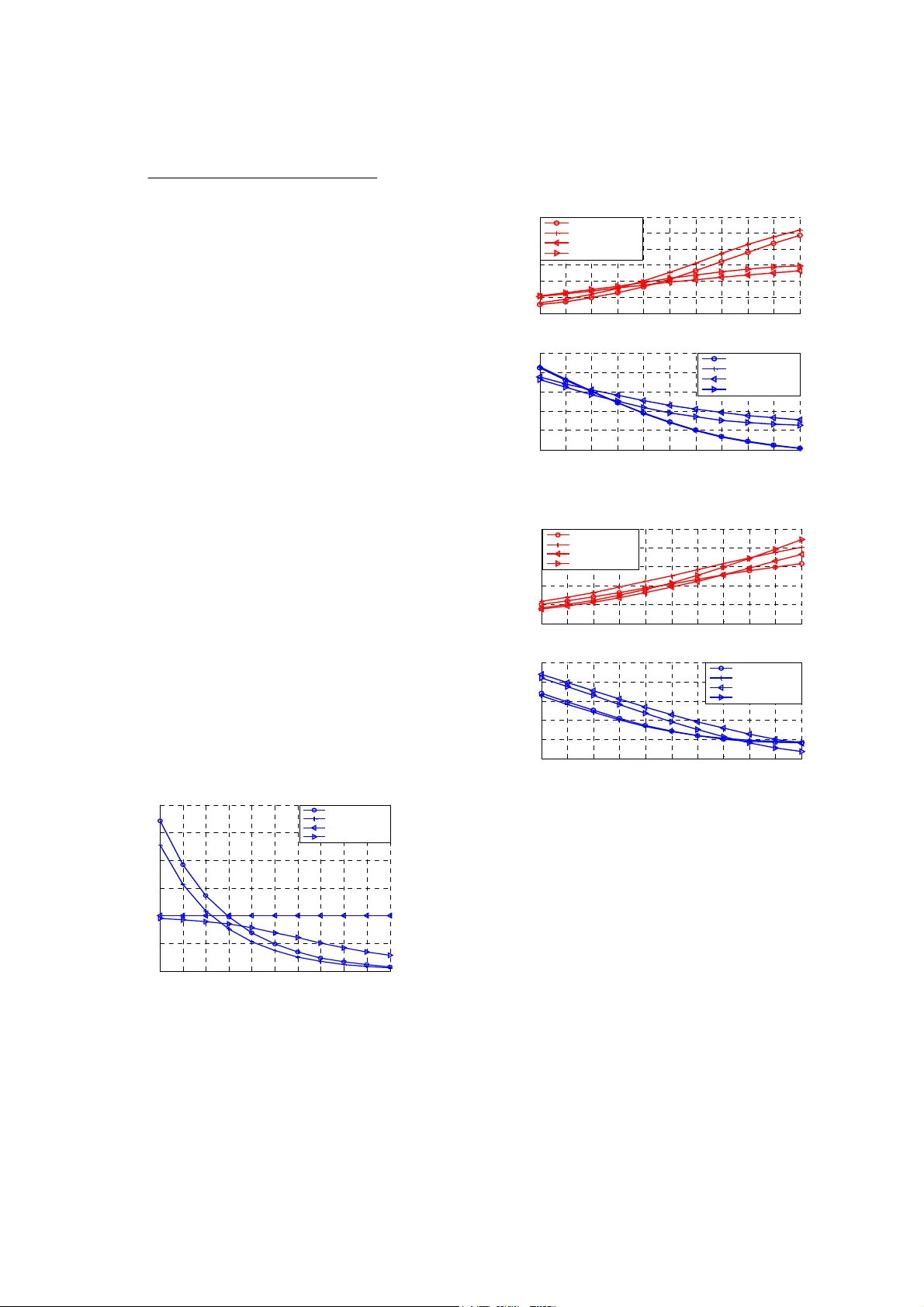
Physical Layer Network Coding Schemes over Finite and Infinite Fields Shengli Zhang, Soung Chang Liew , Lu Lu The Department of Information Engineering The Chinese University of Hong Kong, Hong Kong, China Email: {slzhang5, soung, ll007}@ie.cuhk.edu.hk Abstract: Direct application of network coding at the physical layer - physical layer network coding (PNC) - is a promising technique for two-way r elay wireless networks. In a two-way relay network, r elay nodes are used to r elay two-way information flows between pairs of end nodes. This paper proposes a pr ecise definition for PNC. Specifically , in PNC, a relay node does not decode the sour ce information from the two ends separately , but rather dir ectly maps the combined signals received simultaneously to a signal to be r elayed. Based on this definition, PNC can be further sub-classed into two categories - PNCF (PNC over finite field) and PNCI (PNC over infinite field) - according to whether the network-code field (or groups, rings) adopted is finite or infinite. For each of PNCF and PNCI, we consider two specific estimation techniques for dealing with noise in the mapping process. The performance of the four schemes is investigated by means of analysis and simulation, assuming symbol-level synchronization only . I. INTRODUCTION Network coding, first proposed in [1], is a promising technique for achieving max-flow min-cut capacity in multicast transmission. Linear network coding has been shown to be powerful enough to achieve this capacity [2]. This paper focuses on the use of linear network coding in wireless networks. Although the original investigation of network coding was in the context of wired networks, its potential to boost performance in wireless networks could be even more significant thanks to the broadcast nature of the wireless medium [3]. Ref. [3] shows that direct application of network coding at the physical layer in a wireless relay network could double the capacity of bidirectional point-to-point communication. A similar idea was independently presented in [4]. The analog network coding proposed in [5] is essentially another variation of physical layer network coding (PNC). Several other PNC schemes have also been proposed for the wireless two-way relay channel (TWRC). For example, [6] proposed a PNC scheme based on T omlinson-Harashima precoding. In [7], a number of memoryless relay functions, including the BER optimal function, were identified and analyzed assuming phase synchronization between signals of the transmitters. Under the general definition for PNC given in our paper here, there is a one-to-one correspondence between a relay function and a specific PNC scheme. W e give a precise definition for PNC to distinguish it from the traditional straightforward network coding (SNC). Additionally , we classify PNC schemes into two categories - PNCF (PNC over finite field) and PNCI (PNC over infinite field) - according to whether the network-code field (or groups, rings) adopted is finite or infinite. W ith the definition and classification, the construction of a PNC scheme can be regarded as consisting of two parts: (i) determination of the network code to be used at the relay node; (ii) computation of the information to be relayed at the relay node based on the signals received from the two end nodes. In this paper , we investigate several well-known signal estimation techniques for (ii) under PNCF and PNCI. Among the resulting schemes, one is ANC, one is a novel scheme and the other two are the generalizations of the PNC schemes in [3, 7]. For all the four PNC schemes, only symbol-level synchronization is assumed. II. SYSTEM MODEL AND DEFINITIONS A. System model 1 N 2 N 3 N Figure 1. T wo way relay channel W e consider the two-way relay channel as shown in Fig.1, in which nodes N 1 and N 2 exchange information with the help of relay node N 3 . W e assume that all nodes are half-duplex, i.e., a node can not receive and transmit simultaneously . This is an assumption arising from practical considerations because it is difficult for the wireless nodes to remove the strong interference of its own transmitting signal from the received signal. W e also assume that there is no direct link between N 1 and N 2 . An example in practice is a satellite communication system in which the two end nodes on the earth can only communicate with each other via the relay satellite. In this paper , W i denotes the un-coded packet of N i ; X i denotes the corresponding transmitted packet after channel coding and modulation; and Y i denotes the received base-band packet at N i . A lowercase letter, w , x , or y, denotes one symbol within the corresponding packet. Because of half-duplexity and the lack of a direct link between N 1 and N 2, the transmission must consist two phases: the uplink and downlink phases. Under PNC, for the uplink phase, N 1 and N 2 transmit to N 3 at the same time. Therefore, N 3 receives 31 3 1 2 3 2 3 yh x h x n =+ + (1) where n i is the noise at N i assumed to be complex Gaussian with unit variance; and h ij is the complex path-loss coefficient for the channel from N i to N j . Fading is not considered in this paper . For all the packets ( X 1 , X 2 and X 3 ), QPSK modulation is assumed, and the transmitting power is normalized to 2, which is the QPSK signal’ s variance. In (1), symbol-level synchronization is implied. The carrier phase offset and the transmitting power differences are combined into h ij . W e also assume that the path-loss coefficients h ij can be perfectly estimated by each receiving node N i . Furthermore, the relay node N 3 will forward h i3 estimated by to both end nodes. In the downlink phase, N 3 generates a new signal, x 3 , based on the received signal y 3 , and broadcasts it to both N 1 and N 2 . W e can write the signals received by N 1 and N 2 as 13 1 3 1 2 3 2 3 2 y h xn y h xn =+ = + (2) The target information to be received at the destinations, x 1 at N 2 and x 2 at N 1 , will be decoded from y 1 and y 2 , respectively , with the help of the nodes’ self-information. In general, x 3 must be a function of x 1 and x 2 , denoted by 31 2 (, ) xf x x = . The following sub-section defines and classifies PNC based on different forms of the function f . B. Definition and classification of PNC For comparison purposes, let us review SNC briefly. T raditionally , SNC [8] is regarded as an upper layer technique and is separated from other lower-layer signal processes such as modulation and channel coding. It works as follows. N 3 first decodes W 1 and W 2 separately . Then it encodes W 1 and W 2 into a network coded version W 3 . After that, W 3 is channel encoded and modulated into X 3 before being sent out PNC was inspired by the observation that it is unnecessary for the relay node to know the exact source information [3]. W ith PNC, N 3 transforms Y 3 directly to a network coded version of the combined input symbols without detecting the individual input symbols separately . More formally , PNC is defined as follows: Definition 1: Physical layer network coding is the coding operation which dir ectly transforms the r eceived baseband signal 3 y in (1) to a network-coded symbol 31 2 (, ) xf x x = for r elay , without separate detection of x 1 and x 2 . If the network code is over a finite field (e.g., GF (2)) then the PNC scheme belongs to PNCF . If there were no noise, the transformation from y 3 to 31 2 xxx =⊕ 1 would be deterministic. However , due to noise, PNCF generates an estimation of 12 xx ⊕ from the received signal y 3 . If the network code is over an infinite field (e.g., the real field R or complex field C [10]) then the PNC scheme belongs to PNCI. In this paper , the network code of x 1 and x 2 over 1 For QPSK, 12 ,{ 1 } xx j ∈± ± , 12 1 2 Re( ) Re( ) xx x x ⊕= + i 12 Im( ) Im( ) jx x i . This definition is equivalent to the GF(2) addition of 12 , xx for the real and imaginary parts separately . complex field is fixed to 31 3 1 2 3 2 xh x h x =+ to match the multiple access channels, as in [5, 10]. W ithout noise, the received signal, 31 3 1 2 3 2 yh x h x =+ , is already in the form of real/complex field network coding. T o deal with noise, PNCI generates an estimation of 13 1 23 2 hx h x + from y 3 . III. P ARTICULAR PNC SCHEMES The previous section gives a general definition for PNC, and divides PNC schemes into two broad subclasses - PNCF and PNCI – according to the network code used. Given a network code, we could also use different estimation techniques at the relay node to compute the relayed value. This section considers three specific estimation functions. A. PNCF schemes Under PNCF , we want to estimate 12 xx ⊕ from y 3 . W e introduce two estimation methods here. A.1 MAP-based PNCF The estimator for maximum a posteriori (MAP) estimation is 12 3 3 12 12 {1 } arg max P r( | ) ( ) xx j xy x x P x x α ⊕∈ ± ± =⊕ ⊕ (3) where α is a coefficient to constrain the average power of 3 x , and 12 () Px x ⊕ is the a priori distribution of 12 xx ⊕ , which is a constant of 1/4 under QPSK modulation. We can rewrite (3) as ', ', ', ' { 1} ' ' ' ' ( ') '( ') ' '( ') '( ') ( ') ( ') ( ') ( ') 3 (, ,, ) a r g m a x {} () abcd a b c d a b c d a b c d abcd abcd PP P P xa c j b d ∈± −− − − − − − − = ++ + =⊕ + ⊕ (4) where 1 j =− and ,, , , { 1 } , abcd Pa b c d ∈± is the probability that y 3 is received when x 1 = a + jb and x 2 = c + jd , given by 31 2 31 3 2 3 Pr( | , ) (( ) ( ) , 1 ) abcd P y x a jb x c jd yh a j bh c j d ϕ == + = + =−+ −+ ( 5 ) where 22 2| | / 2 2 1 (, ) 2 e μσ ϕμ σ πσ − = . Only symbol-level synchronization is assumed in the MAP-based PNCF in (4). If we have the stronger condition of power and carrier-phase synchronization such that 13 23 0 hh h == is a real value, then (4) becomes 33 0 3 0 3 30 30 3 ( ( 2 , 1) ( 2 , 1) 2 ( , 1) ) ( ( 2 , 1) ( 2 , 1) 2 ( , 1) ) RR R II I xs i g ny h y h y jsign y h y h y ϕϕ ϕ ϕϕ ϕ =− + + − +− + + − (6) where 3 R y is the real part of the received symbol and 3 I y is the imaginary part. It is easy to verify that (6) is equivalent to the original PNC scheme introduced in [3]. W e could regard (4) as a generalization of the original PNC scheme. A. 2MMSE-based PNCF Another estimation method is the minimum mean square error (MMSE) estimation. Applying MMSE estimation at the relay node, we can obtain 31 2 3 3 {1 } {| } P r ( | ) tj xx x y t t y αε α ∈± ± =⊕ = ∑ (7) where α has the same meaning as in (3) and 12 3 {| } xx y ε ⊕ is the MMSE estimation of 12 xx ⊕ given y 3 . W e have 3 12 3 3 {1 } {1 } 3 {1 } ,,, {1 } ''' ' ', ', ', ' { 1} Pr( | ) Pr( ) {| } P r ( | ) Pr( | ) () 1 4 tj tj sj abcd abcd abcd abcd ty t t xx y t t y ys acj bd P P ε ∈± ± ∈± ± ∈± ± ∈± ∈± ⊕= = ⊕+ ⊕ = ∑∑ ∑ ∑ ∑ (8) The MMSE estimation of the whole packet, 12 3 {| } XX Y ε ⊕ , can be obtained by estimating every symbol in the packet as in (8). W riting the power constraint 2 12 3 2/ | { | }| EX X Y αε =⊕ explicitly (recall that α constrains the average power of the overall packet, and 2 12 3 (| { | } | ) EX X Y ε ⊕ is the average power of the estimated packet), we can substitute (8) into (7) to obtain 3 2 ,,, {1 } ''' ' 12 3 ', ', ', ' { 1 } () 2 4 |{ | } | abcd abcd abcd abcd acj bd P x P EX X Y ε ∈± ∈± ⊕+ ⊕ = ⊕ ∑ ∑ (9) Note that the x 3 estimated in (9) is a continuous value, while the x 3 estimated in (4) is discrete. W ith the stronger power and carrier-phase synchronization assumption, i.e. 13 23 0 hh h == is a real value, (8) can be rewritten as 22 03 0 03 0 22 03 0 03 0 cosh 2 exp( 2 ) cosh 2 exp(2 ) 11 22 cosh 2 exp( 2 ) cosh 2 exp(2 ) RI RI hy h hy h j hy h hy h −− + ++ (10) Eqn. (10) is equivalent to the eqn. (22) in [7], which describes an estimate-and-forward scheme. The threshold in (22) in [7], however , is not explicitly specified. Eqn. (10), on the other hand, makes use of the optimal threshold value. Furthermore, unlike (22) om [7], we have not assumed carrier-phase synchronization in (9). The MMSE-based PNCF is more general than the scheme in [7] in that it encompasses both cases with and without carrier-phase synchronization. The case without carrier-phase synchronization is of practical interest because of its easier implementation. B. PNCI schemes W e now consider the PNCI schemes, whose objective is to estimate 13 1 23 2 hx h x + from y 3 . B.1 Linear -MMSE-based PNCI Linear MMSE estimation is widely used due to its simplicity and good performance. If we use linear MMSE to estimate 13 1 23 2 hx h x + , we get 22 3 3 13 23 3 2/ ( 2 ( | | | | ) 1 ) xy h h y α == + + ( 1 1 ) where α is the power constraint coefficient. The definition of Linear-MMSE-based PNCI scheme in (1 1) is simply the ANC scheme of [5]. We can also see from (1 1) that the linear MMSE-based PNCI scheme only depends on the absolute value of the channel coefficients. As a result, unlike in the PNCF schemes, the carrier phase offset between the signals of the end nodes will not affect the performance here. B.2 MMSE-based PNCI According to estimation theory , the linear MMSE estimation is optimal in terms of minimizing the estimation error when the distribution of 13 1 23 2 hx h x + is Gaussian. For non-Gaussian distribution as in our system (due to the assumption of QPSK modulation at N 1 and N 2 ), the unconstrained MMSE estimation should perform better . The general MMSE-based PNCI scheme leads to 12 31 3 1 2 3 2 1 1 2 2 3 {1 } {1 } () P r ( , | ) tj t j xh t h t x t x t y α ∈± ± ∈± ± =+ = = ∑∑ (12) W ith similar derivation and transformation as before, we can rewrite (12) as 13 23 3 ,,, {1 } ''' ' ', ', ', ' { 1 } [( ) ( ) ] ' abcd abcd abcd abcd h a jb h c jd P x P α ∈± ∈± ++ + = ∑ ∑ (13) where 2 33 11 '2 / ( | { | } | ) 16 16 EX Y αα ε == are coefficients to satisfy the power constraint. W ith the stronger power and carrier -phase synchronization assumption, i.e. 13 23 0 hh h == is a real value, (12) can be rewritten as 30 3 0 3 ,{ 1 , 0 , 1 } 30 3 0 ', ' {1, 0 , 1 } () ( 2 , 1 ) ( 2 , 1 ) 2' (2 ' , 1 ) ( 2 ' , 1 ) RI RI ab ab ab j y a h y b h x ya h y b h ϕϕ α ϕϕ ∈− ∈− +− − = −− ∑ ∑ (14) IV. PERFORMANCE ANAL YSIS AND SIMULA TION In this section, we first review the concept of the generalized SNR (GSNR), originally proposed in [9] as a measure for the quality of memoryless relay channels. Then we analyze the GSNR performance of the four PNC schemes in the previous section. W e prove that MMSE estimation maximizes the GSNR at the destination nodes. In addition, we compare the GSNR and BER performance of the four schemes based on numerical simulation. A. Review of GSNR GSNR was originally proposed [9] as a measure of the quality of one-way relay channels. Consider a three-node one-way relay system, where x is the signal from the source, 1 () rg x n =+ is the regenerated signal at the relay , and 2 yr n =+ is the received signal at the destination. If 11 () () gx n x n α += + is a linear function, then 12 (/ ) yx n n αα =+ + . The SNR at the destination is 22 22 2 11 [| | ] [| | ] [| | ] x n P Ex SNR P En En α α == + ( 1 5 ) where P x is the power of the data x and P n is the power of the noise. If g is a non-linear function, however , the signal y can not be written as the addition of x and an independent noise directly . And the definition of SNR is not so clear as (15). T o deal with regenerate function g that could be nonlinear in general, we could express y in the following form [9]: 2 [] () [| | ] u Ex y yx e Ex ∗ =+ ( 1 6 ) where superscript ∗ denotes the conjugate transpose. It is easy to verify that the error 2 [| | ] [] u Ex ey x Ex y ∗ =− is uncorrelated to x . The GSNR is defined as [9] 2 2 [| | ] [| | ] x u P Ex GSNR MSUE Ee == ( 1 7 ) where MSUE denotes the mean square uncorrelated error (uncorrelated to data x ). Simulations in [9] showed that there is a correspondence between GSNR and BER when BPSK modulation is assumed (larger GSNR implies smaller BER, and vice versa). GSNR, however , is easier to analyze than BER for general relay (regeneration) functions, and is a more convenient metric for analysis. For PNC schemes studied here, the numerical simulation in the second sub-section also shows that there is a correspondence between GSNR and BER in our systems. B. GSNR Analysis This sub-section gives the GSNR expressions of the four PNC schemes. MAP-based PNCF First, we consider MAP-based PNCF . According to the expression in (16), we rewrite the relay function as 12 3 31 2 1 2 (( ) ) () 2 u Ex x x xxx d xx e ∗ ⊕ =⊕ + = ⊕ + (18) According to (4), the Euclidean distance between 3 x and the original symbol 12 xx ⊕ is 012 12 12 0 12 12 1 12 2 01 () () 2( ) xx xx d xx xx xx εε ε ε ε ε ∗ ∗ −− − ⎧ ⎪ ⊕− ⊕ ⎪ = ⎨ −⊕ − ⊕ ⎪ ⎪ −⊕ ⎩ (19) where 0 ε ( 1 ε ) is the probability that only the imaginary (real) part of the estimation is wrong, and 2 ε is the probability that both the real and imaginary parts of 3 x do not equal to those of 12 xx ⊕ . The probability of 0 ε , 1 ε , and 2 ε can be calculated from (4). Then we can calculate the power constraint coefficient 12 3 12 01 2 () (( ) ) () 1 1 ( 2 ) 22 xx x Ex x d E εε ε ∗ ∗ ⊕ ⊕ =+ =− + + (20) Based on (20), we can calculate u ε in (18) and obtain the MSUE at the relay 22 _0 1 2 (| | ) 2 /( 1 ) 2 PNCF MAP u MSUE E e εε ε == − − − − (21) The GSNR at the destination node N i , denoted by GSNR i , can be obtained based on (21). Appendix 1 shows that 22 3 22 3 2| | 1, 2 || 1 i i i h GSNR i hM S U E β β == + ( 2 2 ) where 2/ 2 MSUE β =+ . MMSE-based PNCF For MMSE-based PNCF , the MSUE at the relay node is 3 _ *2 2 12 3 2( 2 Re( ) 1 ) | 1 | [| ( | ) | ] PNCF MMSE y MSUE Ex x y λλ ε =+ − + ⊕ (23) where * 12 12 3 2/ [ ( ) ( | ) ] 1 Ex x x x y λε ∗ =⊕ ⊕ − . The derivation of (23), omitted here, is similar to the proof of Theor em 1 in [9]. The GSNR at the end nodes can be obtained by substituting (23) into (22). Linear MMSE-based PNCI For linear MMSE-based PNCI, the MSUE analysis is simple because the uncorrelated error is just the Gaussian noise which is assumed to be normalized. Therefore, the MSUE at the relay node is _ 2 PNCI linearMMSE MSUE = ( 2 4 ) The GSNR at the end node N i can be expressed in terms of MSUE at the relay (see Appendix 2 for details): 22 2 3' 3 22 3 || | | 1, 2 ' 3 || 1 ii i i hh GSNR i and i i hM S U E β β ′ == = − ′ + (25) where 22 13 23 2/ 2 ( | | | | ) hh M S U E β ′ =+ + . MMSE-based PNCI For general MMSE-based PNCI in (13), the MSUE at the relay node is 3 22 _1 3 2 3 *2 2 13 1 23 2 3 2(| | | | )(2 Re( ) 1 ) |1 | [ | ( | ) | ] PNCI MMSE y MSUE h h Eh x h x y λ λε =+ + −+ + (26) where 22 * 13 23 * 13 1 23 2 13 1 23 2 3 2(| | | | ) 1 [( ) ( | )] hh Eh x h x E h x h x y λ + =− ++ . The derivation of (26), omitted here, is similar to the proof of Theor em 1 in [9]. The GSNR at the end nodes in terms of MSUE in (26) is of the same form as (25). W e now compare the GSNR performance of PNCF and PNCI. Theorem 1 in [9] shows that a scaled version of the MMSE estimation is optimal in term of minimizing the MSUE at both relay and the destination. For the PNCF and PNCI schemes, we have the following similar conclusions. Theorem 1: In our system, the MMSE based PNCF scheme minimizes the MSUE (Maximizes the GSNR) at the r elay node and the two destination nodes among all possible PNCF schemes. Theorem 2: In our system, the MMSE based PNCI scheme minimizes the MSUE (Maximizes the GSNR) at the r elay node and the two destination nodes among all possible PNCI schemes. The basic idea of the proof of Theor em 1 is the same as that of Theor em 2 . It consists of the following two steps. The first step is to prove that MMSE schemes minimize the MSUE at the relay node, which is similar to the proof in [9, Theor em 1 ] and is omitted here. The second step is to prove the equivalence between minimizing MSUE at the relay and maximizing GSNR at the destinations, which can be found in Appendices 1 and 2 . C. Simulation Result This subsection presents simulation results of the four PNC schemes within the system defined in Section II. Limited by space, we only present results related to the case in which the channels for nodes N 1 and N 2 are symmetric, i.e. 13 23 31 32 || | | , | | | | hh h h == . 0 1 2 3 4 5 6 7 8 9 10 0 1 2 3 4 5 6 SNR for uplink c hannels (dB ) MSUE at r el ay MAP PNCF MMSE PN C F Linear MM SE P NCI MMSE PN C I Figure.2 MSUE at the relay when downlink channels are 5dB W e first compare the performance of MMSE and non-MMSE estimations. From Fig.2 and Fig.3, we can see that MMSE estimation is better in terms of maximizing the GSNR and minimizing the MSUE, for each PNC class (PNCI and PNCF). The BER performance is shown in Fig. 3(b). Generally speaking, as in [9] for one-way relay , there is a correspondence between the BER performance and the GSNR performance: a larger GSNR usually leads to a smaller BER with the QPSK modulation in our system. 0 1 2 3 4 5 6 7 8 9 10 0 0.5 1 1.5 2 2.5 3 (a) SNR for uplink c hannels (dB ) GSNR at t he end nodes MAP PN C F MMSE PN C F Linear MM S E PNCI MMSE PN C I 0 1 2 3 4 5 6 7 8 9 10 0.05 0.1 0.15 0.2 0.25 0.3 (b) SNR for uplink c hannels (dB ) BER at t h e end nodes MAP PN C F MMSE PN C F Linear MM S E PNCI MMSE PN C I Figure.3 GSNR and BER at end nodes when downlink channels are 5dB 0 1 2 3 4 5 6 7 8 9 10 0 0.5 1 1.5 2 2.5 (a) SNR for downlink c hannels (dB ) GSNR at t he end nodes MAP PNC F MMSE PN C F Linear MM SE P NCI MMSE PN C I 0 1 2 3 4 5 6 7 8 9 10 0.05 0.1 0.15 0.2 0.25 0.3 (b) SNR for downlink c hannels (dB ) BER at t he end nodes MAP PN C F MMSE PN C F Linear MM S E P NCI MMSE PN C I Figure.4 GSNR and BER at the end nodes where uplink channels are 5dB Let us now compare the performance between the two PNC classes. From the simulation results, we can see that the relative performance of the two classes depends on the quality of the uplink and downlink channels. In particular , Fig. 2 and Fig. 3 show that the PNCF (PNCI) schemes are better when the uplink channel is good (bad). This could be understood intuitively by considering an extreme situation. When the uplink channel is very good, the estimation errors for both PNCI and PNCF schemes are negligible. However , the power needed to send the PNCF signals, 12 xx ⊕ , is 2, while the power needed to send the PNCI signals, 13 1 23 2 hx h x + , is much bigger . Fig. 4 shows that PNCF (PNCI) schemes perform better when the downlink channel is bad (good). This could also be understood by considering another extreme situation. When the downlink channel is so good that all the information available at the relay node can be sent to the end nodes without any loss, PNCF is worse since it loses some information through transforming 13 1 23 2 hx h x + to 12 xx ⊕ . V . CONCLUSION This paper has proposed a definition for physical-layer network coding (PNC) for two-way relay channels. Specifically , in PNC, a relay node does not decode the information it receives from the two ends separately , but rather will map the combined signals received simultaneously from two ends into a network-coded symbol. Different mapping functions give rise to different possible schemes within the general PNC class. If a particular PNC scheme uses a network code over a finite field, then it belongs to the subclass of PNCF; whereas if it uses a network code over an infinite field, then it belongs to the subclass of PNCI. W ith noise, there is an additional issue of estimating the network-coded symbols at the relay . For a given network code, different estimation techniques will give rise to dif ferent schemes. W e have studied two particular estimation schemes for each of PNCF and PNCI. Our results show that the MMSE schemes outperform the non-MMSE schemes. In addition, when the uplink channel is good and the downlink channel is bad, the PNCF schemes perform better than the PNCI schemes, and vice versa. This paper has focused on memoryless relay protocols in which channel coding is not applied at the relay node. For PNCF , the end nodes could apply channel codes, such as LDPC code, T urbo code, that are linear for addition over finite field GF(2), i.e. ⊕ . The relay node would then decode the symbol 12 xx ⊕ from the combined signals received [12]. For PNCI, however , there is no channel code such that decoding can be performed over the symbol 13 1 23 2 hx h x + . Reference: [1]. R Ahlswede, N Cai, SYR Li, R W Y eung, “network information flow”, IEEE Trans. on Inform. Theory , V ol.46(4), pp.:1204 – 1216, 2000. [2]. S.-Y .R. Li, R.W . Y eung, and N. Cai, “Linear network coding”, IEEE Trans. on Inform. Theory , vol. 49(2), pp. 371–381, 2003. [3]. S. Zhang, S. Liew , and P . Lam, “Physical layer network coding,” ACM Mobicom2006 , 2006 [4]. P . Popovski, and H. Y omo, “the anti-packets can increase the achievable throughput of a wireless multi-hop network”, IEEE Pr oc. ICC2006 , 2006 [5]. S. Katti, S. S. Gollakota, and D. Katabi, “Embracing wireless interference: Analog network coding,” MIT T ech. Report , Cambridge, MA, February , 2007. [6]. Y . Hao, D. Goecket, Z. Ding, D. T owsley , and K. K. Leung, “Achievable rates of physical layer network coding schemes on the exchange channel,” submitted to ICC2008. [7]. T . Cui, T . Ho, and J. Kliewer , “Relay strategies for memoryless two way relay channels: performance analysis and optimization”, submitted to ICC’08. [8]. Y W u, P A Chou, SY Kung, “Information exchange in wireless networks with network coding and physical-layer broadcast ”, Pr oc. 39th Annual Conf. Inform. Sci. and Systems (CISS) , 2005. [9]. K. S. Gomadam, S. A. Jafar, “Optimal relay functionality for SNR maximization in memoryless relay networks”, JSAC, vol.27(2) , pp. 390-401, Feb. 2007. [10]. S. Shintre, S. Katti, S. Jaggi, B. K. Dey , D. Katabi and M. Medard, “real and complex network codes: promises and challengess”. Pr oc. Netcod2008 , Hong Kong, 2008. [11]. T . Cover , and J. Thomas, “Elements of information theory ,” 2 nd ed. New Y ork: W iley , 2006 [12]. S. Zhang, S. Liew , and P . Lam, “Physical layer network coding,” http://arxiv .or g/ftp/arxiv/papers/0704/0704.2475.pdf [13]. B. Nazer, M. Gastpar , “Computation over multiple access channels,” IEEE T rans. Inform, Theory , vol. 53, pp. 3498-3516, 2007 Appendix 1 For PNCF , the GSNR at destination N i is 22 3 22 3 2| | 1, 2 || 1 i i i h GSNR i hM S U E β β == + where 1/ 2 MSUE β =+ . Proof: Consider N 1 . For an estimator at the relay , 12 ˆ () u Xr x x e =⊕ + with 2 [| | ] u MSUE E e = , the received signal at N 1 is 13 1 1 2 1 () u yh x x e n β =⊕ + + By adding its own “self” symbol x 1 on the received signal, N 1 can obtain 11 1 3 1 2 3 1 1 1 '( ) u yy x h x h e n x ββ =⊕ = + + ⊕ Obviously the information x 2 is uncorrelated to 31 1 1 () u he n x β +⊕ . Then the GSNR of 1 ' y can be written as 22 2 31 31 1 22 2 31 31 2| | 2 | | || 1 ( || 1 ) 2 hh GSNR hM S U E h M S U E β β == ++ + The last equation shows that maximizing GSNR at the destination is equivalent to minimizing the MSUE at the relay for PNCF schemes. The calculation of GSNR 2 is similar . Appendix 2: For PNCI schemes , the GSNR at destination N i is 22 2 3' 3 22 3 || | | 1, 2 ' 3 || 1 ii i i hh GSNR i and i i hM S U E β β ′ == = − ′ + where 22 13 23 1/ 2 ( | | | | ) hh M S U E β ′ =+ + . Proof: Consider N 1 . For an estimator at the relay , 13 1 23 2 ˆ () u Xr h x h x e =+ + with 2 [| | ] u MSUE E e = , the received signal at N 1 is 13 1 1 3 1 2 3 2 1 =( ) u yh h x h x e n β ′ ++ + Making use of the self information x 1 , N 1 can obtain 1 1 31 13 1 31 23 2 31 1 ' u yy h h x h h x h e n ββ β ′′ ′ =− = + + Since x 2 is uncorrelated to 31 1 u he n β ′ + , GSNR of 1 ' y is 22 2 2 2 31 23 31 23 1 22 2 2 2 31 31 13 23 2| | | | 2 | | | | || 1 ( || 1 ) 2 ( || | | ) hh hh GSNR hM S U E h M S U E h h β β ′ == ′ ++ + + As in PNCF , the last equation shows that maximizing GSNR at the destination is equivalent to minimizing the MSUE at the relay for PNCI. The calculation of GSNR 2 is similar .
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment