Hierarchical Grid-Based Pairwise Key Pre-distribution in Wireless Sensor Networks
The security of wireless sensor networks is an active topic of research where both symmetric and asymmetric key cryptography issues have been studied. Due to their computational feasibility on typical sensor nodes, symmetric key algorithms that use t…
Authors: Abedelaziz Mohaisen, DaeHun Nyang, KyungHee Lee
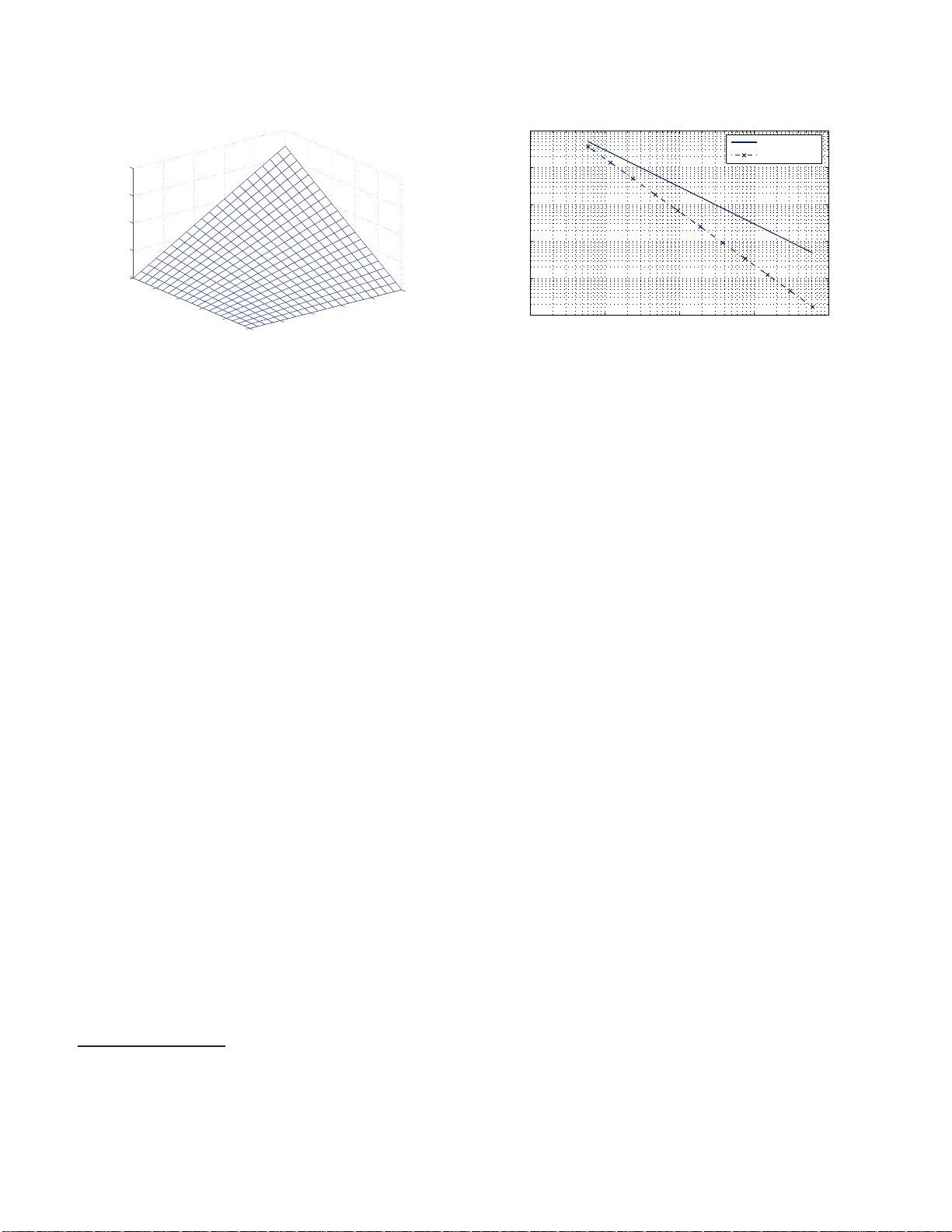
Hierarc hical Grid-Based P airwise K ey Pre-distri bution in Wireless Sensor Net w orks Ab edelaziz Mohaisen ∗ , DaeHun Nyang † and KyungHee Lee ‡ Abstract The se curity of wir eless sensor networks is an active topic o f r ese ar ch wher e b oth symmetric and asymmetric key crypto gr aphy issues have b e en studie d. Due to their c omputational fe asibility on typic al sensor no des, sym- metric key algorithms that use the same key to encrypt and de crypt messages have b e en intensively studie d and p erfe ctly deplo ye d in such envir onment. Be c ause of the wir eless sensor’s limite d infr astructur e, the b ottlene ck chal lenge for deploying these algorithms is the key dis- tribution. F o r the same re aso n of r esour c es r est riction, key distribution me chanisms which ar e use d in tr adi- tional wir eless n etworks ar e not efficient for sensor net- works. T o over c ome the key distribution pr oblem, sever al key pr e-distribution algorithms and te chniques that as- sign keys or keying material for the networks no des in an offline phase have b e en int ro d uc e d re c ently. In this p ap er, we int ro d uc e a supplemental distribution te ch- nique b ase d on the c ommunic ation p att ern and deploy- ment knowle dge mo deli ng. Our te chnique is b ase d on the hier ar chic al grid dep loyment. F or gr anting a pr o- p ortional se curity level with nu mb er of dep endent s en - sors, we use di ffer ent p olynomials in differ ent or ders with differ ent weights. In se ek of our pr op ose d work’s value, we pr ovide a detaile d analysis on the u se d r e- sour c es, r esulting se curity, r esiliency, and c onne ctivity c omp ar e d with other r elate d works. Keyw ords : Sensor network se curity, key pr e- distribution, deployment know le dge, grid network, c om- munic ation efficiency. ∗ Electronics and T elec ommu nications Re searc h I nstitute, Daejeon 305-700, Korea † Graduate School of Inform ation T ec hnology and T elecom- mun ication, Inha Unive rsity , Inc heon 402-751, Korea, n y ang@inha.ac.kr ‡ Departmen t of Electrical Enginee ring, The Univ ers i t y of Su- wo n, Suw on, 445-743, Korea 1 In tr o duction Sensor netw ork consists of a h ug e num b er of sen- sor no des whic h are inexpe ns iv e, low-pow ered and resource s-constrained small dev ic e s [5]. The typical sensor no de contains a p ow er unit, a sensing unit, a pro cess ing unit, a stor age unit, and a wireless transceiver (T/R) [1]. The concept o f micro- sensing and wireless connection in the sensor netw ork promises several a pplications in military , environment, health- care, and many other commercial domains [15]. Due to sensor no des reso urces’ c o nstraints, public key algo- rithms such like Deffie-Hellman key agre e men t [7 ] o r the RSA Signature [28] are undesirable to b e used. In spite of rec e nt results on the computationa l feasibilit y of those algor ithms [1 1, 20, 32, 3 3], it is still early to widely deploy these alg orithms since using them will exp ose a vulnerability to denia l of ser vice attack (DoS) [6, 34]. On the other hand, symmetric key algo rithms that use same key for encrypting and decrypting messages are desir able in the sensor netw o rk. This desirability is due to the computational ligh tness on the t ypical sen- sors. F rom ano ther point, due to the weak infrastr uc- ture of the sensor netw or k , traditional secret k e y distr i- bution mec hanisms such lik e the Ke y Distribution Cen- ter (K DC) can not b e used. The main iss ue therefor e is summarized in ho w to distribute secret keys or key- ing material that are resp onsible on gener ating sec r et keys among differen t sensor no des [10]. Since the man- ual mo dification of the sensors’ conten ts is undesirable after the in-field deployment phase, sev eral key pr e- distribution schemes that assign and distribute keying material o r se cret keys in an off-line phase hav e b een prop osed. In the following section, we review s ome of those sc he mes follow e d by our main con tr ibution. 1.1 Related W orks Two o f the ea rly works in [2, 3] ar e widely known for their nov e lty . Consider ing a netw o rk that cons ists 1 of N no des, in the first w ork by Blom et. a l. [2] a sym- metric matrix of size N × N is required to stor e the different N 2 keys for securing communication within the entire net work. No de s i ∈ N has row and column in the matrix. If tw o no des s i , s j would like to co m- m unicate, they use the ent ries E ij in s i side and E ji in s j side which a re equal (i.e., E ij = E ji since the matrix is symmetric). T o reduce the memor y requir e - men ts, a slight mo dification is in tro duced b y Du et al. [9]. The following are defined, a public matrix G of size ( λ + 1) × N and a priv ate symmetric matrix D o f size ( λ + 1 ) × ( λ + 1) w he r e D e ntries are gener ated randomly . Also, A = ( D · G ) T of size N × ( λ + 1) is defined. F or a node s i , row R i in A and co lumn C i in G ar e selected. When tw o no des s i , s j would like even- tually to c omm unicate secur ely , they firstly exchange their C i , Cj then k ij = R i · C j is co mputation in the side of s i and k j i = R j · C i is computed in the side of s j . Note that k j i = k ij based on the symmetric prop- erty of A , D , G . The se cond work by Blundo et. al. [3] pr opo sed three proto cols for secure dy namic confer - ences [3]. The 2 -conferences proto col uses Symmetric Biv ariate Polynomial (SBP ) to distr ibute keys for N no des. The SBP has the following general form: f ( x, y ) = t X i,j =0 a ij x i y j , where ( a ij = a j i ) (1) This p olynomial is of deg ree t where t ≤ N . F or a no de s i with identifier I D i , the share g ( y ) expressed in E qn 2 is calcula ted and lo aded to s i ’s memor y for gene r ating future secr et keys. Similarly , for tw o no des s i , s j that would lik e to co mm unica te securely , k ij = g i ( j ) , k j i = g j ( i ) ar e ev aluated lo cally in the corres p onding sides and used r esp ectiv ely as secret keys. g i ( y ) = f ( i, y ) (2) In the se ns or netw or ks era , the early scheme of key pre-distribution s pecifica lly for WSN is intro duced by Eschenauer and Gligor (a.k.a., E G scheme) [10]. In EG sc heme, each no de is let to ra ndomly pick a key r ing S k of size k from a big keys p o ol of size P . The picking pr o ces s maintains a probabilistic c o nnec- tivit y betw e en any no de a nd other nodes in the entire net work. This co nnectivit y is noted as p actual and de- fined as p actual = 1 − (( P − k )!) 2 ( P − 2 k )! P ! . If tw o no des s i , s j share a key k : k ∈ S k i ∩ S k j they b oth ca n use k a s a secr et k ey . Otherwise, a pa th k ey e s tablish- men t phase via single or several intermediate no de(s) is p erformed. In [10] the usage of memory is reduced, how ever, a fra il resiliency is resulted (i.e., if a small nu m ber of no des ar e compr omised, big comm unication fraction of non-compr o mised no des is disclo sed). T o improv e the resiliency , Chan et. al. pro pos ed the q-composite scheme [4]. Using the sa me pro cedure of EG, a key b etw een tw o no des s i , s j is av ailable if and only if S k i ∩ S k j is a set of q n um ber of keys. If { k 1 , . . . , k q } ∈ { S k i ∩ S k j } , hash ( k 1 || k 2 , . . . , || k q ) is used as k ij , k j i . Otherwise, intermediate no de(s) are used. More a nalytical a nalysis on the pro babilistic schemes is shown by Kw ang and Kim in [13] In addition to improving Blom’s scheme in [2], Du et. al. prop osed tw o schemes for key pre-distributio n in [8, 9]. In the ea rly one they introduced a deploy- men t knowledge ba s ed s c heme that improves B lom ’s [2] by av oiding the unnecessar y memory , communica- tion, a nd computation with r e asonable connectivity [8]. In [9], a multi-space matrix scheme based on [2, 10] is introduced. A τ num b er of priv ate matrices D is selected ra ndomly out of ω pre-construc ted ma tri- ces providing c o nnectivit y p actual that is e x pressed as p actual = 1 − (( ω − τ )!) 2 ( ω − 2 τ )!) ω ! . Different A s’ are created us- ing the different D s’. τ rows of the different A s’ are selected and assig ned for ea c h node. F or s i , s j , if they hav e a common space τ i,j : τ i,j ∈ τ i ∩ τ j , the rest of Blom ’s scheme is p erformed. Otherwise, an interme- diate no de that has a n intermediate space is used to construct a path key in a pa th key establishment phase. Even though muc h memory and communication are re- quired and sma lle r connectivity is generated, this work provides a higher re s iliency than in both of RG [4] and Chan et. al. [10]. F or more accur a cy , different deploy- men t structures with practical err or measurements and the probability distribution functions p df based on [8] are in tro duced by Ito et. al. in [14] Sim ultaneously , Liu et. al. proposed several schemes in [18, 19] for key distribution which are mainly based on Blundo et. al. [3 ]. In [18], the po lynomial-based mechanism is us ed to assig n several po lynomials for ea ch no de in a similar wa y of EG scheme [1 0]. Tw o no des ca n establish a secret key if and only if they shar e a common p olynomial. Other- wise, the tw o no des use an intermediate no de for es- tablishing a se cure path. The most significant work b y Liu et. al. is in [18, 19]. In b oth works, for a netw or k of siz e N , a tw o dimen- sional deployment structure that cons tr ucts a gr id of N 1 / 2 × N 1 / 2 is sug gested. Different no des are deploy ed on differ en t int ersecting p oints and different p olyno - mials a re assig ned fo r the different rows and columns of the gr id. F or t w o no des s i and s j , if R i = R j or C i = C j , (i.e., b oth no des hav e the same p olynomial’s share), a direct key establishment is p erformed. Else (i.e., R i 6 = R j and C i 6 = C j ), an intermediate node is used in an a pa th key establishment pha se. In this work, even if a big fraction of no des p c of the ov er all 2 net work siz e N is compromised, the netw ork r e mains connected via a lternative intermediate no des. The big fraction p c herein is measur ed to b e p c ≤ 6 0 % o f N . Also, an n-dimens ional scheme is intro duced in [19]. Finally , the deployment knowledge for sp ecial purp oses and applications using proba bilis tic ma nner has b een studied in [26, 27] while a general securit y architecture has been prop osed in [25]. 1.2 Our C o n tributions In this pap er we intro duce a new scheme using the Hier ar chic al Grid as a deploymen t framework and Blundo ’s scheme as key generato r (a.k.a ., keying ma- terial). Thr ough this pap er, our main contributions are the following: • Provide a scala ble, r obust, and novel framework for the key pr e-distribution that gives a p erfect connectivity v alue (i.e., the connectivity is alwa y s equal to ‘1’ using the s ingle hop communication manner) to establis h a pair wise key . • Optimize the usage of the different net work re- sources, mainly , communication overhead, mem- ory usage, a nd r e quired computation. • Analyze and pro vide a mathematical mo del of o ur scheme’s p erformance. • Provide and discuss the alternative aga inst an y po ssible securit y a ttac k ag a inst o ur s cheme. W e take adv an tage of different fla t deploymen t zones in a hiera rchical grid re presentation for deploying the different sens o r no des. Based on each s e ns or no de’s lo - cation, s e veral symmetric polynomia ls lik e these intro- duced in [3 ] are a ssigned to genera te secret keys. Each po lynomial in the assigned gro up for every sensor node is used for securing communication within a targ eted zone. As a result, eac h no de can communicate with any other no de in the netw or k using the shared keying material. W e show how the connectivity a pproaches a prefect desirable lev el in bo th of the random and non- random cases. As well, we show the v alue of our scheme against s o me given attacks and study the its security under the a moun t of consumed resour ces. 1.3 P ap er Structure The rest of the pa p er is or ganized as follows. Sec- tion 2 introduces the notations and definitions which are used througho ut the paper and Section 3 in tro- duces our scheme. W e co ns ider an extensive analysis of our scheme’s connectivity as a main interesting is- sue in Section 4. In Section 5, we consider the analysis of re sources consumption and the security ana lysis in Section 6 co nsidering several a ttac ks. Finally , w e intro- duce a c omparison betw een our w o rk and set of previ- ous works in Section 7 follow ed by concluding r emarks in Section 8 . 2 Notations and Definitions The following definitions a nd no tations are used throughout the rest o f this pap er. 2.1 Definitions Definition 1 (Net work order n ) . a network desig n p a- r ameter that indic ates the size of the n et work and the numb er of p olynomials use d in e ach sensor no de. Definition 2 (Basic grid or ba s ic zone) . set of sensor no des in a ge o gr aphic al ar e a that initial ly use the same p olynomial of de gr e e t 0 Definition 3 (Polynomial Order O ) . an inte ger that de cides t he sc op e wher e t he p olynomial is use d to es- tablish a se cu r e p air-wise key, wher e O ∈ { 1 , 2 , . . . , n } . Each no de has some m inimum or der of 1 and maxi- mum or der of n Definition 4 (Polynomial Degr ee t 0 ) . a se cu rity p a- r ameter t hat indic ates the s t r ength of the p olynomial against the c ompr omise and expr esses how many dif- fer ent n o des that c arry shar es of this p olynomial must b e c ompr omise d for r eve aling t he p olynomial itself for an attacker. The subscription 0 to n expr esses t he or- der of the p olynomial. 2.2 Notations The nota tion in table 1 is used thr ough the r est of the paper . 3 HGBS for P airwise KPD Our scheme uses Blundo [3] as a k e y ing material gen- erating blo ck to ge nerate different secret keys for dif- ferent no des. The distribution o f the k eying mater ial is per formed on sensor no des deploy ed in a Hier ar chic al Grid as shown in Figur e 1. Our grid ma inly consid- ers the ro uting gr id used in [17] with s ligh t mo difica- tion. This mo dification relies on using the duplication growth factor to mov e from an or der to ano ther. In our work, we aim to pr ovide each s ensor node with a set o f 3 T able 1. Notation T erm Indication n the net work o rder N nu m ber o f senso r no des in the en tir e netw o rk m nu m ber o f senso r no des in the basic grid B z k mo des distribution unit thr ough the netw ork B z basic zone (a lso, Basic Gr id) O x order of the x th net work grid t 0 degree of the basic p olynomial in the B z t n degree of the p olynomial for grid of order n s i , s j sensor no des I D i ident ifier of the senso r node i G n nu m ber o f the Basic Zones in the netw or k different p olynomials for establishing secr et keys. The main r ule of the different p olynomials is to make sev- eral zones with v ar y ing num b er o f no des approachable by a given no de. In the following subs e ctions, w e pro- vide a description of our scheme including the following po in ts : the deploymen t grid ov erview, no de iden tifica - tion mechanism, keying material gene r ation, secure key establishment and the scheme parameter s adjustment . 3.1 Ov erview o f the Deploymen t Grid Consider a net w ork that co nsists of N sensor no des. The different no des are deploy e d in a net work of gr id structure as of Figure 1. In this deploymen t struc- ture, the netw o rk is divided into n hierar c hical order s of grids. Each order i consists of 2 i − 1 basic zone. The ba- sic zone B z is a g eographica l reg io n bounded by [2 k , 2 k ] dimensions (i.e., length and width). Also, k is identified as the a uniform distribution unit of the senso r no des in the WSN and the leng th unit as well. The num ber of the no des m in B z is (2 k ) 2 . The or der defined earlier is used to repr esent the growth o f the net work. The high- est order O n contains G n =2 n − 1 nu m ber of basic grids. The total num b er of no des in the netw ork is N wher e N = m × G n = (2 k ) 2 × 2 n − 1 . As shown in Figure 1, B z is any grid with the dimensions [G1X,G1Y] which has O 1 . Simila rly , the dimensions [G2X,G2Y] are con- sidered fo r grids of or de r 2 ( O 2 ), [G3X,G3Y] will be considered for O 3 , and so on until O n . An obvious note to mention here is that a n y zone which b elongs to o r der O a includes twice as m uch as the num b er o f no des in zone O a − 1 . G 3X G 2X G 1X k k G 1Y G 2Y G3 Y G1 Y G2 Y G 3Y k O r der 1 O r der 2 Order 3 Figure 1. Sensor nodes deplo yment in a hier - ar chical grids network 3.2 No de Iden tifier Our scheme uses a smart identifi cation mater ial (ID) which is unique for each no de thro ugh the netw or k . The function of the ID in our scheme is to iden tify the no de within the netw o rk, to re pr esent the keying mate- rial (i.e. po lynomials) of the no de, and to provide “an extra sense” of the no de lo cation assuming a limited mobility . The use of the hiera r ch ical grid with a duplicat- ing g rowth facto r makes it poss ible to represent the different basic zones of Figure 1 in a binary tree as shown in Figur e 2. In this tree, the height r epresents the maximum or der and the num ber of leav es r epre- sents the num b er of basic zo nes in the netw ork. F or each leaf no de, the attached n umbers are sequences that represent the identifiers of different no des within the same bas ic zones (i.e. lo cal ID in a B z where 1 ≤ I D local ≤ m ). The different p olyno mials are a s - signed to the internal no des of the tree. I n the tr ee, left br a nc hes are assigned to “0” bit v alue and right branches to “1 ” bit v alue. The final senso r no de’s ID is the binary string of tracing the path fro m the ro ot to the end leaf that the sensor belo ng s to concatena ted with the lo cal ID. This structure of ID is shown in Figure 3 . T he length o f this ID can b e expressed as follows | I D | = n + ⌈ lg( m ) ⌉ (3) Where m is is the n umber of no des in the ba s ic zone. 4 P 3 1 P 2 1 P 1 2 P 1 1 P2( y -1 ) P1( x -2 ) P1( x -3 ) P 2 2 P 1 4 P 1 3 P 2 y P 1 x P1( x -1 ) P 3 z Pn 1 0 1 0 1 0 0 1 0 1 1 0 L R N1 N2 N 3 Nm- 1 Nm N1 N2 N3 Nm- 1 Nm N1 N 2 N 3 Nm-1 Nm N1 N 2 N3 Nm-1 N m N1 N2 N3 Nm- 1 Nm N1 N2 N3 N m- 1 Nm N1 N2 N3 Nm- 1 Nm N1 N2 N3 N m- 1 Nm O n O 3 O 2 O 1 Nodes x = 2 n -1 y = 2 n -2 z = 2 n -3 Figure 2. Node ID generation determining node’ s location in WSN Local I D Basic Gr id ID - L ocation I D - n-Bits Log 2 (m) Bits 0 1 2 3 4 5 0 Las t Bi t First B it n First B it Las t Bi t D-Bits [Uniqu e Node ID i n WSN ] Figure 3. Node ID structu re in the hierarc h ical grid F or a net work with a lar g e size, n can b e c o nsidered a constant for a flexible desig n that a ccepts dynamic net work growth. 3.3 Key Material Assignmen t Several keying materia l (or s imply p olynomia ls) is assigned for the differen t sensor no des. Using the gr id deploymen t struc tur e as of Fig ure 1, different po lyno- mials with the appr opriate security para meter are as- signed for the no de ba sed on which grids of which order it belo ngs to. Initially , SBP of degr ee t 0 which is as- signed to the cor resp onding basic g rid B z is assigned for establis hing secret keys for the pa irs of no des within the same B z . The usag e of this p olynomial will pro - vide a v alue of 1 2 n − 1 of dir e ct connectivity . The other po lynomials are used for the co nnectivit y to reach the desirable one based on the no de’s lo ca tion and gr an ting the corresp onding connec tivity . W e ass ume that the no des which are deployed w ithin the same bas ic grid hav e the higher pr o babilit y for communicating with each other and tho s e outside the concerned ba sic grid have a less communication prob- ability . This a ssumption is imp ortant sinc e the usage of the poly no mials with small degree that require a less co mputation p ow e r is so frequent a nd the us age of the hig her degree p olynomia ls is le s s frequent. The pro cedure of gene r ating the keying material and the assignment for the different senso r no des is s ho wn in Algorithm 1. Algorithm 1 : Keying material assignment Input : Net work order n , set of all no des’ IDs, set of path IDs d , Net work size N Output : n polyno mials shares for each no de x as k x . for i = 1 to n do 1 for j = 0 to 2 i − 1 do 2 p [ n − i + 1 ][ j ] ⇐ SBP of degr ee t 3 end 4 for x = 1 to N do 5 k x [ n − i + 1 ] = 6 p [ n − i + 1 ][ d/ (2 ( i − 1) ]( I D x , y ) end 7 end 8 3.4 Key Establishmen t T o secur e the communication b etw een no des s i , s j , secret key generation is required. Considering the ID of bo th no des and the p olynomial set g enerated by the a l- gorithm in Algo rithm 1 , firstly , a p olynomial f ∗ ( x, y ) is selected out of the s ha red p olynomials in the tw o no des. The selected p o lynomial must b e common in bo th nodes ’ polynomia ls with the minimum t-de gr e e (i.e., referring to Figure 2, the the most close parent to the lea ves of both nodes s i , s j ). T o establish the secure key , Algorithm 2 is applied. Note that, this a lgorithm is applied in b oth of s i , s j to generate the pairw is e key . Also, only the p olynomial shar e is used after its ev alua - tion in a lgorithm in Algo rithm 1 as ex pressed in Eq n 2 . Algorithm 2 : Key establishment pro cedure Input : P a th identifiers d i , d j , node’s s j ID ( j ), set of no de’s i polyno mials shares; k i [] Output : Symmetric k ey K ij . Begin; 1 for c = 0 to d i . length − 1 do 2 if d i [ c ] = d j [ c ] then 3 g ( y ) = k i [ c ]; 4 Break ; 5 end 6 end 7 k ij = g ( j ) 8 5 3.5 P arameters Adjustmen t The critical pa rameter in our scheme that control the res ources usage and resulting secur it y is the p oly- nomial degr ee t 0 and the r elationship b et ween t 0 and other p olyno mials’ degr ees in the different order s . A less imp ortant factor in our sc he me’s analysis is the communication traffic function (CTF). The degree t 0 is totally dependent on the num b er o f no des in the basic grid [3]. In [2 9], the authors assig ned t 0 to b e 20. How ever, this assumption does no t pr ovide correla ted dynamic sec urit y strength with the change of netw or k size. Generally , if we c o nsider 0 < α ≤ 1 as a secur it y parameter, t 0 can be expressed as t = α ∗ m for more reliable security assumption. Using the same memory as in [12], t 0 can be as signed to 0 . 6 × m whic h will make the bas ic zone secure till the compromis e of 0 . 6 m + 1 num b er of no des that b elong to the sa me grid. F or a differen t num b ers of no des in the netw o rk, Fig ure 8 s hows the required memory in K B to sto re the dif- ferent p olynomial co efficients. On the other hand, the remaining ( n − 1)-p olynomials’ degr ees t 1 , t 2 , · · · , t n − 1 are to follow one o f the following a ppr oaches: (i) T o hav e the v alue of t 0 and the growth o f the netw or k order will lead to the same v alue o f the po lynomial g rowth. (ii) T o consider the different t degre es indep endent ly . F or the communication traffic function (CTF), our deploymen t scenario consider s that the no des which are mostly to co mm unica te are the neighbor s in the same basic gr id while other no des in o ther grids hav e a less traffic fraction. In the analysis, we consider tw o differ- ent functions: The geometric s eries distribution func- tion and the exp onential dis tribution functions. Note that, the summation of pro babilities for the commu- nication from a given zone that represents a set of given no des to all other zo nes is equal to one (i.e. P n i =1 p pd f = 1). F or a geo metric CTF, c is deter mined satisfying Eqn 4. CTF = n X i =1 c 2 i − 1 = 1 (4) 4 Connectivit y Dividing the ne tw ork hierar c hically provides a con- nectivity using mor e than one keying material (i.e., symmetric p olynomials). This connectivity enables dif- ferent no des b elonging to different basic g rids to com- m unicate securely in 1-hop fashion. Let us cons ider C as the provided connectivity . Bas ed on the structure of the gr id, the p olynomial assigned to B z provides con- nectivity of C 1 which is expre ssed as m m × 2 n − 1 = 1 2 n − 1 . In g eneral ter ms, the p olynomial for the i th order grid provides connectivity of m × 2 i − 1 m × 2 n − 1 = 1 2 n − i for the no des that b elong to it. Thus, for the highest order, the pro- vided connectivity is m × 2 n − 1 m × 2 n − 1 = 1 which exclusively includes all of the b elow o rders’ connectivity (i.e., C i for i = 0 to n − 1). F or a more genera l conce ptio n, we consider tw o t ype s of connectivit y . The first t ype conceptualize the connectivity tha t conside r s sensor no des s i , s j in the net work r egardless to their lo cation while the second t ype consider senso r no des according to their pr ecise minim um-w eighted po lynomial that they shar e . F or the first case, no des are randomly deploy ed in the field and the tra ffic do es no t have a regular pattern. The connectivity is expres sed as the pr o babilit y p z for the t wo no des s i , s j to be in the same grid. Simila r ly , this can b e formulated a nd expressed as the probability for t wo no des within so me order order to exa ctly be lo ng to the s ame minim um or der z which enables establish- ing keys with minimal weigh ted p olynomial. Also, it can b e express ed as the pro babilit y of randomly pick- ing tw o no des with the condition that they b elong to the s a me order . This probability is s hown in Figure 6 p z = 2 ( z − 1) m 2 N 2 − 1 = 2 ( z − 1) m 2 2 ( n − 1) m 2 − 1 = (2 z − 1 m )(2 z − 1 m − 1 ) (2 n − 1 m )(2 n − 1 m − 1) = 2 z − n 2 z − 1 m − 1 2 n − 1 m − 1 (5) Consider a, b as tw o in teger s such that a ≥ b > 1, a b is alwa ys gr e ater than or e qual to a − 1 b − 1 . Applying this to Eqn 5 we get that (2 z − 1 m − 1) (2 n − 1 m − 1) ≤ 2 z − n . F r om all, we get: p z ≤ 2 ( z − n ) 2 (6) On the other hand, the second type of connectivity con- siders tw o no des s i , s j , whe r e their used polynomia l to generate secret key is previously determined based on the fixe d deployment structure and tr affic mo del. A connectivity C i is deter mined a s the provided certain connectivity provided by the minimal net work o rder that the tw o no des b elong to . This is t ypically equiv - alent to the connectivity provided by any p olynomial assigned for an y the given p olynomial or der as in Eqn 7. C i = 2 i − 1 2 n − 1 = 2 i − n (7) F or b oth p z and C i , the ov erall connectivity is de- fined as the provided ability to each no de to commu- nicate s ecurely w ith other no des in secure manner r e - gardless to the order they b elong to and the shared 6 1 2 3 4 5 6 7 0 0.1 0.2 0.3 0.4 0.5 0.6 0.7 0.8 0.9 1 Separating orders Connectivity Random Communication ( β =2) Deterministic connectivity β =1) Communication pattern of β =1.3 Communication pattern of β =1.5 Communication pattern of β =1.7 Figure 4. Connectivity with different traffic parameters po lynomial they use. In other words, the overall con- nectivity is determined as the v alue o f p z or C i when z or i g o to n as follo ws : C n = 2 ( z − n ) 2 z = n = 2 ( i − n ) i = n = 1 (8) F or a g eneral connectivity form that co nsiders de- gree o f ra ndomness which determines each no de’s knowledge o f the deployment str ucture given and the accuracy of communication mo del descr iption [22], w e define β as c omm unication pattern’s parameter wher e C = (2 i − n ) β and 1 ≤ β ≤ 2. Fig ur e 4 sho w s the connectivity provided by the order’s p olynomials ac- cording to different β v alues. 5 Ov erhead Analysis In this part we consider o ur scheme’s overhead. This ov erhea d is mainly repr esen ted by the memory required for the k eying materia l repres en ta tion, the computa- tion required for a single biv ar iate p olyno mial’s e v alu- ation o n GF ( q ) in a single v ar iable, and the commu- nication req uir ed for exchanging the concer ned sensor no de’s identifiers. 5.1 Net work Capacit y Our scheme uses the different reso urces of the net- work in a rea s onable manner. The r e duction in using any resource can affect other co rrelated re sources and downgrade the ov er all p erfor ma nce. In this section, we measure the cos t o f our scheme by analytical and ma th- ematical fo r m ulas in terms of the netw ork resource s . F rom the details ab ov e, the tota l netw ork capacity N can be express e d as N = 2 ( n − 1) × (2 k ) 2 (9) Where n is the la rgest p olynomial or der in the net w ork and k is the distribution unit of no des. The rela tio n- ship betw een k and n fo r different netw ork size N a nd ranging n is shown in Figur e 5 and Fig ure 6. 0 2000 4000 6000 8000 10000 0 0.5 1 1.5 2 0 5000 10000 15000 N n k Figure 5. T he relationship between n, k , N for 0 < n ≤ 2 . 0 2000 4000 6000 8000 10000 0 2 4 6 8 10 0 5000 10000 15000 N n k Figure 6. T he relationship between n, k , N for 0 < n ≤ 10 . 5.2 Memory Ov erhead The a moun t o f memory which is requir ed per no de is to r epresent the no de ID shown in Eqn 3 and the differ- ent n-p olynomials’ shares . F or a p olynomial f ( x, y ) of degree t 0 whose co efficients in GF ( q ), ( t 0 + 1) × lg ( q ) 7 bits a r e r equired as a represe ntation space. F or the memory us e, w e introduce t wo differen t appro aches: 1. T o as sign different degr ees for the different p olyno - mials regar dless to the num b er of the distributed shares of the p olynomial. 2. T o make the growth of the different poly nomials’ degrees sa me as that of the gr owt h of the num b er of the no des that hold those p olynomials ’ shar es. Thu s, a ll po lynomials in the first or der hav e degree t 0 and the i th order p olynomials have degree of 2 i − 1 × t 0 . The firs t case c ost in bits is represented in Eq n 1 0 as follows: M 1 = n + lg N 2 n − 1 + n αN 2 n − 1 + 1 lg( q ) (10) The first tw o terms are for the ID representation and the third term for n -p olynomials repres en tation. The second case is shown in E q n 11 where the third ter m is the summation of the r equired memory to r epresent n po lynomials of different de g rees and α is the secur ity parameters , P weig ht is f ( x, I D )’s ( t 0 + 1)-co efficient s representation memory . M 2 = n + lg N 2 n − 1 + P weig ht n X i =1 (2 i − 1 ) = n + lg N 2 n − 1 + (2 n − 1 ) αN 2 n − 1 + 1 lg( q ) (11) Also, the memory requirement in Eqn 11 can b e considered as a geometric series with bas e r in terms of the highest order’s p olynomial (i.e. r = 1 2 ). F or this r epresentation, the summation is held for n terms giving the following: M 3 = 1 + 1 2 + · · · + 1 2 n − 1 ( αN × lg ( q )) = ( αN × lg ( q )) × " n − 1 X i =0 1 2 i # (12) Recall that r : − 1 < r < 1, the summation of the first n terms is S n = 1 − r n +1 1 − r . T his g iv es the following: M 3 = ( αN lg( q )) 1 − 1 2 n +1 1 − 1 2 ! (13) 0 0.2 0.4 0.6 0.8 1 0 2000 4000 6000 8000 10000 0 8 16 24 32 α N Memory Figure 7. The required memo ry for different security parameters and network size in our scheme. Figure 7 shows the requir ed memory for differen t net work siz e N and secur it y par ameter α . Also , Fig- ure 8 s hows the re quired memory for the Blundo’s sin- gle p olynomia l represe ntation. Note that, the memory requirements is linearly depe nden t on bo th N and α . 5.3 Computation Ov erhead Each time a key is required, the ev a luation of p oly- nomial f ( x, I D ) of degree t is p erformed in single v ari- able. Due to the differe nce o f t deg ree s ho wn ear lier, different scenar ios ar e co nsidered. In case of using the first memor y scenar io, the required computation can be summarized in a s ingle p olynomial f ( x, I D ) of de- gree t 0 ev aluation regardless to the degree. In the se c - ond scenar io wher e we a ssign different deg ree according to the gr owth factor for the different netw ork orders , the communication pa tter n and co mm unica tio n pr ob- ability function based o n the lo ca tion determines the required p olyno mial to b e co mputed and the r equired computational power. F rom other p oint, ev a luating a po lynomial of degree t require s 2 t num b er of multiplications 1 . Based o n [16]; using the long integer multiplication, it requir es 64 num b er o f 8-bit w o rd multiplication to m ultiply t wo int egers in finite field of q = 2 64 . In c o n trast, it takes only 27 word multiplication o n the sa me pla tform us- ing Karatsuba- Ofman a lgorithm [16]. Th us , the re- quired word multiplication for multiplying tw o integers 1 Recall that the computational weigh t of n - bit n -integers ad- dition i s equiv alent to tw o integers multiplication with the n length. Initiall y , the required num b er of multiplications is 2 t − 1 and the additional one due to the addition operation [16] 8 0 0.2 0.4 0.6 0.8 1 0 2000 4000 6000 8000 10000 0 5 10 15 20 α N Memory Figure 8. Memor y requirements for stor- ing the polynomial’ s coefficients in Blundo’ s scheme with v ar ying α . of leng th 16 and 64 bits consumes 16 8-bit word mul- tiplications. This type of different length oper ations is required for a ccum ulating a long eno ugh key that fits with the requir ed standar d k ey length (e.g. DES of 56 bit, AES of 128 and R C5 of 64) 2 . C P avg = n X i =1 ( p i C P t i ) ! + c (14) Eqn. 14 expresses the re q uired computatio n in terms of the num b er of mult iplications in GF ( q ), where c is computational p ow er required for tw o bi- nary string s compar ison. These strings repr esent the po lynomial path identifier part. Also, p i is the proba- bilit y that tw o no des r eside in different ( i − 1) th grids and C P t i is the requir ed computational p ow er for the i th order po lynomial ev aluatio n. F or tw o different com- m unication traffic functions, Figure 9 shows the c o m- putational consumption growth cur ve in terms of the nu m ber of multiplications in GF ( q ) acco rding to the growth of the netw ork size. 5.4 Communication O verhead Our scheme does no t require any ex tr a means of communication except of the no des’ identifiers ex- change which costs lg ( N ) bits tr ansmission as dis c ussed early in the ID representation requirement. The ID it- self is ex pressed in a general form as o f Eq n 3. 2 The RC5 [31] is the most likely to be used on the typical sensor node platform b ecause of its small co de size without a need for extra tables [25]. Thu s, the largest exp ected finite field is of 64 bi ts length. 10 1 10 2 10 3 10 4 10 5 10 −5 10 −4 10 −3 10 −2 10 −1 10 0 Required 8−bit word mutliplications Communication probability CTF=e −c(n+1) CTF=c*0.5 −(n+1) Figure 9. Co mputation overhead for two dif- ferent Communication T raffic Functions. The used parameters are t 0 = 6 0 , β = 0 . 6 , n = 1 1 which suppor ts up to N = 20 4800 . 5.5 Reducible Memory Sch emes Since the memory limitation is the bottleneck for any successfully desig n in wir e less senso r net work, an y set of p o lynomials with an o r der greater than a des ir- able d s uch that 1 < d ≤ n can b e discarded b y giving up the direct connectivit y . T o e ns ure an alterna tive connectivity through in ter mediate no de, a virtual g rid as of [18] ca n b e applied. Once this kind of grid is ap- plied, the higher order po lynomials are removed and replaced by smaller poly nomials that represent the vir- tual g rid. Therefore, the final required memory is de- pendent upo n how many order s are discar ded but a l- wa ys less than the required memory ov er he a d expressed in 12 or 13. 6 Securit y Analysis The security of our scheme follows the sa me a nal- ysis introduced in [3, 18]. The s ecurity of all of these schemes is based on that a net work that uses a biv ariate po lynomial of degre e t is secur e against the compro mis e as lo ng as the num ber of r ev ealed share s is less than or t + 1. In this section, we consider several attacking scenarios a g ainst our scheme. This includes the no de replication attack [2 4], the Sybil attack [23], Denial of Messages (DoM) Attacks [21], a nd Denial o f Service (DoS) A ttacks [34]. 9 6.1 Compromising Effects and Resiliency 6.1.1 An Atta c k Against N c Num b er of No des In cas e of co mpromising a set of nodes whose size is N c that is le ss than t 0 , the fra c tio n of the affected no des other than those whic h are compr omised is 0. This applies for an y kind of attack stra tegy including the random and s elective one [12]. 6.1.2 An attac k against B z An attac k ag ainst the s ingle ba s ic zone can b e suc- cessfully p erformed throug h the compromise of n um- ber of no des N c where N c > t + 1. By c ompromising t + 1 num b er of sensor no des and revealing their secret shares, the main polyno mial of the concerned no de can be r e c o vered[30 ]. Even though, this attack lo o ks mo re difficult due to that 2 n − 1 nu m ber of poly nomials of de- gree t within the net work where the probabilit y p r for t 0 no des to b e b elonging to the s ame p olynomial sha res is in E qn 15. p r = 1 − t 0 − 1 X i =0 N c i m N i N − m N N c − i (15) The probability p r indicates that the num b er of sensor no des to b e co mpromised by revealing its own secr et shares should b e big enough to g uarantee that the a t least t 0 nu m ber of shar es b elong to a sp ecific p olyno- mial. This pr imarily based on the po lynomial degre e t 0 and α , how ever, ov er 60 % of the netw or k size is a reasona ble threshold for α = 0 . 6 6.1.3 An attac k against the w hole netw ork The attack ag a inst the whole netw ork can not b e in synchronized way . How ever; in the worst case, it is po ssible to compromise the entire netw ork b y compro- mising all o f the p o lynomials f ( x, y ) o f t 0 one by one. T o compr omise B z requires t 0 no des to b e compr o- mised. Since the net work consist of G n different B z , it requires to c ompromise G n × t 0 which is a big fraction (i.e. more than 60 % of the netw ork size). Without this amount, the fraction of affected nodes will be les s than 50% o f the netw o rk size. 6.1.4 Sele ctiv e v ersus random no de attac k Even if the no des are deployed randomly , the knowl- edge o f the no des deployment and the a ssigned po ly- nomials for e a c h gro up and the ability to distinguish the different no des based on their B z enables a se- lective attac k that ease the attackers ta s k. On the other hand, the random attack where the attac ker’s knowledge ab out the deploymen t str ategy of the sev- eral no des makes it ha r der to r ev eal a g iven poly nomial that g enerates secure keys fo r a given p olynomial as shown previous ly in Eqn 15. 6.1.5 Sybil and no de repli cation attac ks There are tw o pro blems b elonging to the dynamic growth of sensor netw o rk. Sybil a ttac k [2 3] is done fallaciously by us ing more than one ID for the same no de j and no de replication attack [24] which is p e r- formed us ing the same ID more than one time in the net work. Our work resis ts against these threats b e- cause it requires a structured ID which is unique with a uniform structure ov er the en tire netw o r k. When an attack er fabricates a structured ID, it should follow the limited s tructure sho wn previously and de ploy the no de in sp ecific a rea to c o mm unica te within the sa me B z . 6.1.6 DoM and DoS attac ks Denial o f Messag es [21] is the abilit y of s ome no des (i.e., attacker’s no des) to deprive others of rece iving some broa dcast messa ges. Our fra mew ork does no t re- quire any broadca st capa bilit y . If a n y , it will b e mainly used within the same grid. Thus, the DoM attack will only affect a small fractio n of the whole netw o rk. An example of the Denial of Ser vice[34] is “ attempts to preven t a particular individual from acces s ing a se r - vice” and this mainly happ ens due to a hea vy comm u- nication o r computation b ecause of the k ey generation or a n y outsider reason like attack er message s floo ding. In our sc heme, a ll o f the co mputation a nd comm unica- tion op erations ar e small, and take short time. In the second case, to pe rform a DoS, no de replication attack is required. 6.1.7 Man In the Middl e A ttac k (MITM) Under the assumption that the ra dio coverage is enough to enable the usage of the differen t polynomials for differen t targets, the ma n in the middle attack is im- po ssible. In the ca se of the reduced memory s c he mes , the man in the middle attac k is p ossible with small probability due to that the intermediate no des a r e used for a limited commu nication fractio n o f fo r w arding. As well, each attack er who would like to deploy his own sensor no des to p erform the MITM sho uld k now the ge- ographica l loca tion where to deploy the different sensor no des. 10 T able 2. Co mparison b etween our scheme and a set of oth er schemes in terms of the resources usage and t he resulting connectivity . The con nectivity for t he probabilistic key pre-distribution schemes is probabilistic while it is certain for ot her schemes including ours. Also, the polynomial degree t differ s as shown earlier based on α . Sc heme Communication Computation Memory Connectivit y GBS [18] c SBP Ev aluation ID+2 SBP 2 N 1 / 2 − 1 3D-GBS [18] c SBP Ev alua tion ID+3 SBP 3 N 2 / 3 + N 1 / 3 +1 Plat-Bas ed [22] c SBP Ev aluation ID+3 SBP 3 N 1 / 3 EG [10] c log 2 ( S k ) (2 c + p − p k ) 2 log 2 ( c ) S k keys 1 − (( P − k )!) 2 ( P − 2 k )! P ! CPS [4] c c S k keys m N DDHV [9] c log 2 ( n × τ ) 2 vectors mult. τ + 1 vectors 1 − (( ω − τ )!) 2 ( ω − 2 τ )! ω ! HGBS c SBP Ev aluation ID+ n SBP 1 6.2 Blo ck ed T raffic and It s Recov ery This pap er mainly introduces a new fr amework for the key pre-distr ibution, deployment and smart lo ca - tion base d identification. Howev er, when we applied Blundo ’s scheme [3], w e obtained that even though the i th order p olyno mial where 1 < i ≤ n is compr o - mised, this will not affect the other netw o rk except of that amount of traffic (links) within the i th order grid. Assume the i th order SBP is co mpromised, the frac tion of the blo ck ed traffic will b e m × 2 i − 1 m × 2 n − 1 × p i = 1 2 n − i × p i where p i is the fra ction of tra ffic be tw een nodes resides in different the ( i − 1) th order grids. Using the cur rent p i = 1 2 i − 1 distribution w ill gua rantee that the blo ck ed communication is alwa ys constant v alue regar dless to i v alue. On the recov er y; when t + 1 no des are compro mised, an alterna tiv e s ecure SBP can be use d. In the cas e that an SBP of the c th order grid is co mpromised, the SBP for the ( c + 1) th order g rid is used till the sys- tem recov ery a nd assigning another po lynomial to the affected grid. In cas e of the highest order ’s p olyno - mial compromise, the a mo un t of tr affic compromised will be only 1 2 p ( i = n ) . If w e assume that the fra ction is decreased by half whenever the order of grid increases by 1, the amount will b e will b e 1 2 n − 1 for p n . How- ever, the internal netw or k connectivity will not b e af- fected. Moreover, the ma jor it y of the secure tra ffic in the network will no t b e broken since the deploymen t framework gua rantees that most of the traffic is in B z . 7 Comparison With Others W e s e lected GBS [18], Multi-space [9], EG [10], Q- Comp osite and RPS [4] for the compar ison with our scheme. The compared features are comm unica tion, computation and memory . T able 2 shows this compar- ison in terms of those resources. In our scheme, mem- ory , computation and comm unication requir emen ts are shown in Eqn 10 to Eqn 14 Remark: the co nstan t v alue of communication in GBS dep ends o n whether it’s p o ssible to construct a di- rect key or not. In c a se of using an intermediate no de, the communication cost of the in termediate should b e considered. The a moun t of communication traffic in our sc heme is alwa ys cons tan t b ecause of its na ture. 8 Conclusion W e prop osed a nov el fr amework for the secure key pre-distribution in the WSN. Our prop osed scheme uses a hierarchical grid for the senso r no des deploy- men t that b ounds the heavily comm unicated no des in one basic g rid tha t has stro ng secur e keying mater ial. W e also desig ned a n ID structur e which is unique for the no de and expresses the lo catio n as well as the keying materia l to be used. T o mea sure the perfo r - mance of our framework, we used Blu ndo ’s [3] a s a keying material genera tor blo ck. Mathematical anal- ysis of the computation, co mm unica tion and mem- ory was provided. The different p ossible attacks were lightly touched. The p erformance shown co mparison expressed the v a lue of our framework. References [1] I. Akyildiz, W. Su, Y. Sank a r asubramania m, and E. Ca yirci. A survey on sensor net works, 2002. [2] R Blom. An optimal class of symmetric key gen- eration systems. In Pr o c. of the EUROCR YPT 11 84 worksh op on A dvanc es in cryptolo gy: t he ory and app lic ation of crypto gr aphic te chniques , pages 335–3 38, New Y o rk, NY, USA, 19 85. Springer - V erlag New Y ork, Inc. [3] Carlo Blundo, Alfredo De Santis, Amir Herzb erg , Shay Kutten, Ugo V a ccaro, and Moti Y ung. Perfectly-secure key distribution for dynamic con- ferences. In CR YPTO , pages 4 71–48 6 , 1992. [4] Haow e n Cha n, Adrian P errig, and Dawn Xi- ao dong Song. Random k ey pr edistribution schemes for sensor netw o rks. In IEEE Symp osium on Se cu rity and Privacy , pages 197– , 2003 . [5] David Culler, Deb orah Estr in, and Mani B. Sr i- v astav a . Ov erview o f sens or netw o rks. In IEEE Computer So ciety , pag es 41– 49, 2 004. [6] Jing Deng, Richard Han, and Shiv ak ant Mishra . Defending against path-based dos attacks in wire- less sensor netw or ks. In S ASN , pages 89–96, 2 005. [7] Whitfield Diffie a nd Martin E. Hellman. New di- rections in cryptogr aphy . IEEE T r ansactions on Information The ory , IT-2 2 (6):644–6 54, 1 976. [8] W enliang Du, Jing Deng, Y unghsiang S. Han, Shi- gang Chen, and P ramo d K. V arshney . A key man- agement scheme for wireless sensor netw ork s using deploymen t knowledge. In INFOCOM , 2 004. [9] W enliang Du, Jing Deng, Y ung hsiang S. Han, Pramo d K. V ar shney , Jonathan K atz, and Aram Khalili. A pairwis e key predistribution sc heme for wireless sensor netw o rks. ACM T r ans. Inf. Syst. Se cur. , 8(2):228 – 258, 2005 . [10] Laurent Esc henauer and Virgil D. Gligo r. A k ey- management scheme for distributed sensor net- works. In ACM CCS , pages 41–47, 2 0 02. [11] Nils Gur a, Arun Patel, Arvinderpal W ander, Ha ns Eb erle, and Sheueling Chang Shantz. Co mparing elliptic curve cryptogr aphy a nd rs a on 8-bit cpus. In CHES , pages 11 9–132, 2 004. [12] Dijiang Huang, Ma nish Mehta, Deep Me dhi, and Lein Harn. Lo cation-aware key management scheme for w ir eless sensor netw or ks. In SA SN , pages 29–42 , 2004. [13] Jo engmin Hwang and Y ongdae Kim. Revisiting random key pre-distribution schemes for wireles s sensor net works. In SA SN , pages 43– 52, 2 004. [14] T a k ashi Ito, Hidenori Ohta, Nori Matsuda, and T akeshi Y oneda . A key pre-dis tribution sc heme for secure sensor netw orks using proba bilit y density function of no de de ployment. In S A SN , pa g es 69– 75, 2 005. [15] Holger Karl and Andreas Willig. Pr oto c ols and Ar chite ctu r es fo r Wir eless Sensor Networks . J ohn Wiley & Sons Ltd., ISBN-1 3 988 -0-470 -09510-2 , 2005. [16] Donald Knuth. The Art of Computer Pr o gr am- ming: Semi-nu meric al Alg orithms, volume V ol.2, thir d e ditio n . Addison-W esley , ISBN: 0-201 -89684 - 2, 1997. [17] Jiny ang Li, John Ja nnotti, Do ug las S. J. De Couto, David R. Ka rger, and Rob ert Morr is . A scalable lo cation servic e for geographic ad ho c routing. In MOBICOM , pag es 1 20–13 0, 2000. [18] Dongg ang Liu and Peng Ning. Esta blishing pair- wise keys in distributed sensor ne tw orks. In A CM CCS , pages 52 –61, 200 3. [19] Dongg ang Liu, Peng Ning, and Rong fa ng Li. Es- tablishing pa irwise keys in distributed sensor net- works. ACM T r ans. Inf. Syst . S e cur. , 8(1):41–77 , 2005. [20] David J. Malan, Matt W elsh, and Michael D. Smith. A public- k ey infrastructure for key distri- bution in tin yos based on elliptic curve cr yptogra- ph y . In First I EEE Int . Conf. on S ensor and A d Ho c Comm. and Networks , pages 71–8 0, 2004 . [21] Jo na than M. McCune, E laine Shi, Adrian Perrig , and Michael K. Reiter. Detectio n of denial-of- message attacks on senso r netw ork br oadcasts. In IEEE Symp osium on Se curity and Privacy , page s 64–78 , 2005. [22] Ab edelaziz Mohaisen, Y o ungJae Maeng , a nd Dae- Hun Ny ang. On the g rid bas ed key pre- distribution: T ow ard a b e tter co nnectivit y in w ir e- less se nsor netw or k s. In SS DU 2007, to app e ar , pages 00–00, 20 07. [23] Ja mes News ome, Elaine Shi, Dawn Xiao dong Song, a nd Adrian Perrig . The sybil attack in sen- sor netw orks: analysis & defense s. In IPSN , pa ges 259–2 68, 2004. [24] Bryan Parno, Adria n Perrig, a nd Virgil D. Gligo r. Distributed detection of no de replicatio n attacks in sensor netw o rks. In IEEE Symp osium on Se cu- rity and Privacy , pages 49–63, 20 0 5. 12 [25] Adrian Perrig, Rob ert Szewczyk, J. D. Tygar, Vic- tor W en, a nd David E . Culler. Spins: Security proto cols for sensor netw orks . Wir eless Networks , 8(5):521– 534, 2002 . [26] Rob erto Di Pietro, Luigi V. Mancini, and Ales san- dro Mei. Random key-assignment for secure wir e- less sensor netw or ks. In S ASN , pages 62–71, 2 003. [27] Rob erto Di Pietro, Luigi V. Mancini, and Ales san- dro Mei. Efficient and resilient key discov ery based on pseudo-rando m key pre-deploymen t. In IPDPS , 2004. [28] Ronald L. Rivest, Adi Shamir, and Leona rd M. Adleman. A metho d for obtaining digital sig- natures a nd public-key cr ypto-systems. CA CM , 26(1):96– 99, 198 3 . [29] Stefan Schmidt, Holger Kra hn, Stefan Fischer, and Dietmar W¨ atjen. A security architecture for mobile wireless sensor netw ork s . In ESAS , pag es 166–1 77, 200 4 . [30] Adi Shamir . How to share a secret. Commun. ACM , 22(11):612 – 613, 1979. [31] William Stallings. Crypto gr aphy and Network Se- curity: Principles and Pr actic e, 3r d e dition . Pren- tice Hall, ISBN: 01386901 70, 20 0 3. [32] Arvinderpal W ander, Nils Gura , Hans Eb erle, Vipul Gupta, and Sheueling Chang Shantz. En- ergy ana lysis of public-k e y cryptogra ph y for wir e- less sensor netw o r ks. In PerCom , pages 324– 328, 2005. [33] Ronald J. W atro, Derrick K o ng, Sue fen Cuti, Charles Gardiner , Charles Lynn, a nd Peter Kruus. Tinypk: sec ur ing senso r net works with public k ey techn ology . In SASN , pa ges 59 –64, 2004. [34] An thony D. W o o d a nd J ohn A. Stanko vic. Denial of service in sensor net works. IEEE Computer , 35(10):54 –62, 2002 . 13
Original Paper
Loading high-quality paper...
Comments & Academic Discussion
Loading comments...
Leave a Comment