Information Hiding Techniques: A Tutorial Review
The purpose of this tutorial is to present an overview of various information hiding techniques. A brief history of steganography is provided along with techniques that were used to hide information. Text, image and audio based information hiding techniques are discussed. This paper also provides a basic introduction to digital watermarking.
💡 Research Summary
The paper “Information Hiding Techniques: A Tutorial Review” offers a broad, introductory survey of steganography and digital watermarking, tracing their historical roots from antiquity to modern digital environments and describing a variety of practical embedding methods across multiple media.
Historical Overview
The authors begin with anecdotal accounts from ancient Greece (e.g., Histiaeus tattooing a slave’s scalp) and Roman invisible inks, moving through medieval treatises such as Trithemius’s Steganographia and early modern works by Gaspari Schott. They highlight wartime applications—null ciphers in World War I, microdot photography in World II, and covert markings on maps during the Boer War—illustrating that the desire to conceal the existence of a message predates electronic communication.
Steganography vs. Cryptography
A clear distinction is drawn: cryptography encrypts the content but leaves the ciphertext visible, whereas steganography hides the very fact that a message exists by embedding it in innocuous cover data. The paper argues that the two techniques are complementary; a robust security solution often combines encryption (to protect the payload) with steganography (to hide the payload’s existence).
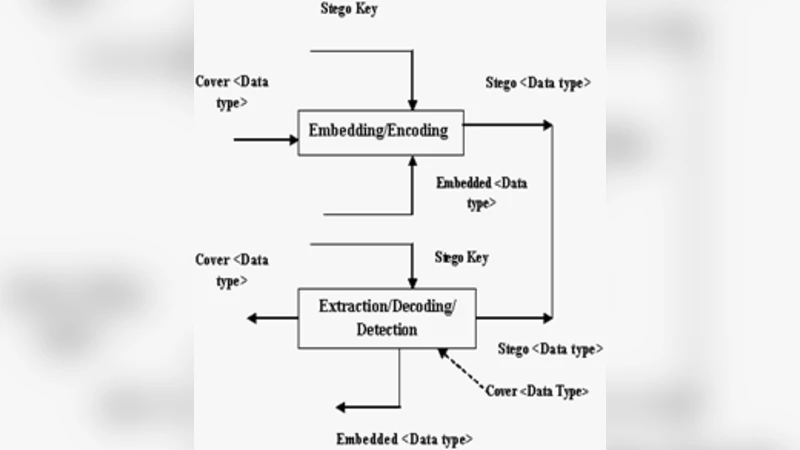
Steganographic Protocols
Three protocol families are defined:
- Pure Steganography – no secret key exchange; security relies solely on obscurity.
- Secret‑Key Steganography – a shared stego‑key is used to embed and extract the hidden data; the key must be exchanged securely.
- Public‑Key Steganography – leverages asymmetric cryptography; the sender encrypts with the receiver’s public key, and only the private key can recover the hidden payload. This model inherits the key‑management advantages of public‑key cryptography.
Media‑Specific Embedding Techniques
The paper surveys concrete methods for several media types:
- Text – whitespace manipulation, line‑break patterns, null ciphers (e.g., taking the second letter of each word), and linguistic steganography (sema‑grams, open codes).
- Images – Least Significant Bit (LSB) substitution, Discrete Cosine Transform (DCT) coefficient alteration, palette reordering, and more sophisticated spread‑spectrum approaches (though not detailed).
- Audio – LSB embedding, frequency‑domain modulation, echo hiding, and exploiting compression quantization noise.
- File Systems – hidden partitions, unused cluster space (e.g., FAT16’s 32 KB per file slack), and kernel patches such as Linux’s sfspatch that combine encryption with steganography to conceal files on disk.
- Network Protocols – covert channels in IP header fields (Identification, Sequence Number) and TCP fields (Acknowledgment numbers). The authors provide a numeric example where specific Identification values encode the ASCII string “HIDE”. They also mention OSI session‑layer manipulation to embed data in control information.
Security Principles
Kerckhoffs’s Principle is invoked: the system should remain secure even if an adversary knows every design detail except for a short, random secret (the key). This underlines the importance of robust key management in any steganographic scheme.
Digital Watermarking
A brief section distinguishes watermarking from steganography, noting that watermarking’s primary goal is copyright protection and integrity verification rather than covert communication.
Critical Assessment
While the tutorial succeeds in compiling a wide array of historical anecdotes and practical techniques, it suffers from several shortcomings:
- Lack of quantitative analysis – No capacity, payload‑to‑cover‑size ratios, or detection probability metrics are presented.
- Outdated references – The survey stops short of recent advances such as deep‑learning‑based steganalysis, generative adversarial network (GAN) steganography, or adaptive embedding algorithms.
- Implementation details – The paper provides high‑level descriptions but no pseudo‑code, experimental results, or performance evaluations.
- Presentation issues – Numerous typographical errors and inconsistent formatting hinder readability.
Consequently, the paper is best suited as an introductory classroom resource that familiarizes students with the breadth of information‑hiding concepts. Researchers and practitioners seeking to design or evaluate modern steganographic systems will need to consult more recent, technically detailed literature that includes security proofs, empirical steganalysis results, and discussions of legal/ethical implications.
In summary, the article delivers a comprehensive historical and conceptual overview of information hiding, categorizes steganographic protocols, enumerates media‑specific embedding strategies, and emphasizes the complementary role of encryption. However, its pedagogical value is limited by the absence of rigorous analysis, up‑to‑date references, and practical implementation guidance.
Comments & Academic Discussion
Loading comments...
Leave a Comment