Authentication over Noisy Channels
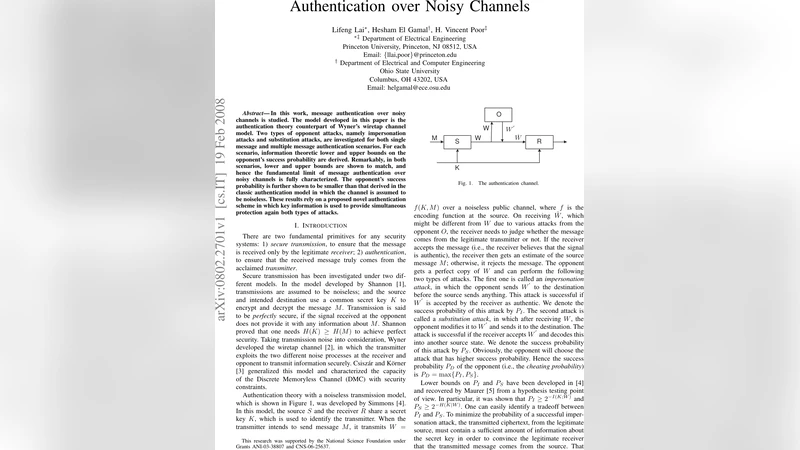
In this work, message authentication over noisy channels is studied. The model developed in this paper is the authentication theory counterpart of Wyner’s wiretap channel model. Two types of opponent attacks, namely impersonation attacks and substitution attacks, are investigated for both single message and multiple message authentication scenarios. For each scenario, information theoretic lower and upper bounds on the opponent’s success probability are derived. Remarkably, in both scenarios, lower and upper bounds are shown to match, and hence the fundamental limit of message authentication over noisy channels is fully characterized. The opponent’s success probability is further shown to be smaller than that derived in the classic authentication model in which the channel is assumed to be noiseless. These results rely on a proposed novel authentication scheme in which key information is used to provide simultaneous protection again both types of attacks.
💡 Research Summary
The paper “Authentication over Noisy Channels” extends the classical authentication problem—originally formulated by Simmons for noiseless public channels—into the realm of noisy communication, by leveraging the wire‑tap channel model introduced by Wyner. The authors consider a scenario where a sender (S) and a legitimate receiver (R) share a secret key K and wish to authenticate a message M transmitted over a discrete memoryless channel (DMC). An adversary (O) observes a noisy version Z of the transmitted codeword X, while the legitimate receiver observes Y. Two classic attack types are studied: impersonation (the adversary injects a codeword before the legitimate transmission) and substitution (the adversary intercepts X, modifies it, and forwards a forged version). The cheating probability is defined as (P_D = \max{P_I, P_S}), where (P_I) and (P_S) are the success probabilities of impersonation and substitution, respectively.
The key contribution is a complete information‑theoretic characterization of (P_D) for both single‑message and multiple‑message authentication when the main channel is “less noisy” than the eavesdropper’s channel, i.e., (I(X;Y) > I(X;Z)). Under this condition the authors construct a novel authentication scheme that simultaneously protects against both attacks using the entire entropy of the secret key. The scheme works as follows: the sender first encodes the message M using a wire‑tap code that achieves a positive secrecy rate, then encodes the key K using the same codebook. The receiver decodes both parts; if the recovered key matches the shared secret, the message is accepted as authentic. Because the wire‑tap code guarantees that the eavesdropper’s mutual information about the key satisfies (I(K;Z) \le n\epsilon) (with (\epsilon) arbitrarily small), the adversary’s optimal strategy reduces to guessing the key, yielding a success probability bounded by (2^{-H(K)}).
To prove optimality, the authors first revisit the known lower bounds (P_I \ge 2^{-I(K;W)}) and (P_S \ge 2^{-H(K|W)}) from Simmons and Maurer, where W is the noiseless authentication tag. They then derive matching upper bounds for the noisy case. The upper‑bound analysis relies on a refined type‑class argument and a partitioning of the wire‑tap codebook into exponentially many subsets with vanishing average (L_1) distance between the induced output distributions. Lemma 1 (borrowed from Hayashi’s work) guarantees the existence of such a partition when the secrecy condition (I(X;Y) > I(X;Z) + 2\delta) holds. By bounding the adversary’s optimal choice of key given its observation Z with the average (L_1) distance, they show that both (P_I) and (P_S) cannot exceed (2^{-H(K)}). Since the lower bounds also achieve this value when the full key entropy is used for authentication, the bounds coincide, establishing the exact fundamental limit: \
Comments & Academic Discussion
Loading comments...
Leave a Comment