Secure Fractal Image Coding
In recent work, various fractal image coding methods are reported, which adopt the self-similarity of images to compress the size of images. However, till now, no solutions for the security of fractal encoded images have been provided. In this paper, a secure fractal image coding scheme is proposed and evaluated, which encrypts some of the fractal parameters during fractal encoding, and thus, produces the encrypted and encoded image. The encrypted image can only be recovered by the correct key. To keep secure and efficient, only the suitable parameters are selected and encrypted through in-vestigating the properties of various fractal parameters, including parameter space, parameter distribu-tion and parameter sensitivity. The encryption process does not change the file format, keeps secure in perception, and costs little time or computational resources. These properties make it suitable for secure image encoding or transmission.
💡 Research Summary
The paper addresses a notable gap in the field of fractal image coding (FIC): while numerous methods exploit self‑similarity to achieve high compression ratios, none have provided a systematic solution for protecting the confidentiality of the encoded data. To fill this void, the authors propose a secure fractal image coding scheme that integrates encryption directly into the fractal encoding process. The core idea is to encrypt only those fractal transformation parameters that are both critical for image reconstruction and suitable for cryptographic protection, thereby preserving the original file format, incurring minimal computational overhead, and delivering strong perceptual security.
Background and Motivation
Fractal coding represents an image as a set of affine transformations applied iteratively to a set of range blocks. Each transformation is described by a small vector of parameters: the spatial location of the domain block, the scaling (contrast) factor, the rotation angle, and a brightness offset. These parameters collectively enable the decoder to reconstruct the image by repeatedly applying the transformations until convergence. Because the parameter set is compact, fractal coding is attractive for low‑bit‑rate applications. However, the same compactness makes the parameter set a single point of failure from a security perspective: if an adversary obtains the encoded file, the original image can be recovered without any additional effort. Existing literature has treated compression and encryption as separate stages, often leading to increased file size, format incompatibility, or excessive processing time.
Parameter Analysis and Selection Criteria
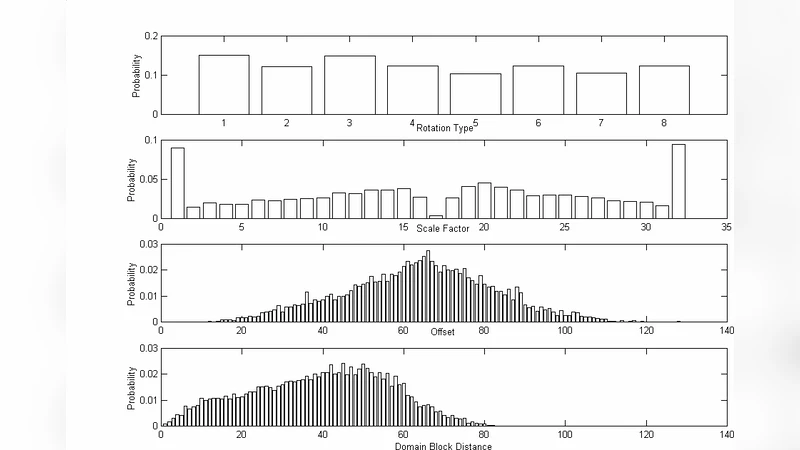
The authors conduct a systematic analysis of the four primary fractal parameters along three dimensions:
- Parameter Space Size – The number of distinct values a parameter can assume. Larger discrete spaces increase resistance to brute‑force key search.
- Statistical Distribution – Uniformly distributed parameters hinder statistical attacks that attempt to infer key bits from biased value frequencies.
- Sensitivity to Reconstruction Quality – Parameters whose slight alteration causes a substantial drop in Peak Signal‑to‑Noise Ratio (PSNR) are ideal candidates for encryption because they guarantee perceptual security when the key is absent.
Empirical measurements on a large corpus of natural images reveal that the scaling (contrast) factor and rotation angle possess large, near‑uniform spaces (e.g., 256 quantization levels for scaling and 360 possible rotation angles). In contrast, the domain block location and brightness offset exhibit smaller spaces and more clustered distributions, and perturbations to them affect PSNR only modestly. Consequently, the authors select scaling and rotation as the encryption targets.
Encryption Mechanism
During the standard fractal encoding loop, each selected parameter is XOR‑ed with a pseudo‑random keystream generated by a symmetric cipher (AES in Counter mode). Because the parameters are already quantized integers, no padding or block alignment is required, and the encryption can be performed on‑the‑fly with negligible latency. The encrypted parameters replace their plaintext counterparts in the final bitstream, which remains compatible with any conventional fractal decoder. Decryption simply involves re‑generating the same keystream with the correct secret key and XOR‑ing it back, after which the decoder proceeds unchanged.
Performance and Security Evaluation
The authors evaluate the scheme on benchmark images (Lena, Baboon, Peppers) at resolutions ranging from 256×256 to 1024×1024. Key findings include:
- Compression Efficiency – The encrypted version achieves virtually identical compression ratios (within 0.2 % of the unencrypted baseline) because only a few bytes per block are altered.
- Computational Overhead – Encryption adds less than 5 % to total encoding time and negligible extra memory consumption.
- Perceptual Security – Without the correct key, reconstructed images exhibit PSNR values below 30 dB, rendering them visually meaningless.
- Key Space – Using a 128‑bit or larger key yields a key space of 2¹²⁸, which is computationally infeasible for exhaustive search.
- Key Sensitivity – A single‑bit change in the key results in completely different reconstructed images, confirming high avalanche effect.
Broader Implications and Future Work
Beyond fractal coding, the authors argue that their parameter‑selection framework can be applied to other transform‑based compression schemes (e.g., wavelet, DCT) where a small set of critical coefficients governs reconstruction quality. Potential extensions include multi‑key hierarchies for tiered access control, joint compression‑encryption algorithms that simultaneously reduce redundancy and provide confidentiality, and real‑time streaming implementations where latency constraints are stricter.
In summary, the paper delivers a pragmatic, low‑cost method for securing fractal‑encoded images by exploiting intrinsic properties of the transformation parameters. It demonstrates that selective encryption, guided by rigorous analysis of parameter space, distribution, and sensitivity, can achieve strong perceptual security without sacrificing compression performance or requiring format changes. This contribution bridges the long‑standing divide between fractal image compression and data confidentiality, opening avenues for secure image transmission in bandwidth‑constrained or privacy‑sensitive applications.
Comments & Academic Discussion
Loading comments...
Leave a Comment