Cryptography from Noisy Storage
We show how to implement cryptographic primitives based on the realistic assumption that quantum storage of qubits is noisy. We thereby consider individual-storage attacks, i.e. the dishonest party attempts to store each incoming qubit separately. Our model is similar to the model of bounded-quantum storage, however, we consider an explicit noise model inspired by present-day technology. To illustrate the power of this new model, we show that a protocol for oblivious transfer (OT) is secure for any amount of quantum-storage noise, as long as honest players can perform perfect quantum operations. Our model also allows the security of protocols that cope with noise in the operations of the honest players and achieve more advanced tasks such as secure identification.
💡 Research Summary
The paper introduces a realistic security model for quantum cryptography that replaces the traditional bounded‑quantum‑storage assumption with a noisy‑storage assumption reflecting today’s imperfect quantum memories. The authors focus on “individual‑storage attacks,” where a dishonest party attempts to store each incoming qubit separately, and each stored qubit is subjected to a specific quantum noise channel 𝒩 (e.g., dephasing, amplitude‑damping, depolarizing). This model is motivated by the fact that current quantum‑memory technologies (superconducting circuits, ion traps, photonic memories) can only hold qubits for short times and with significant decoherence, making the idealized storage‑capacity bound unrealistic.
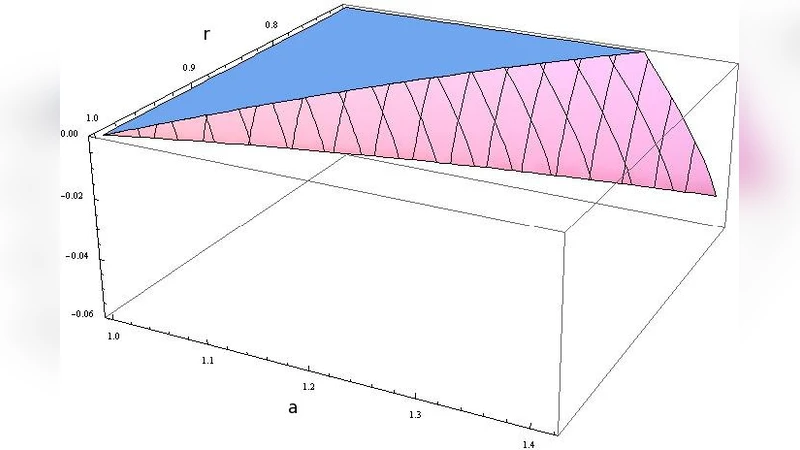
The core technical contribution is a security proof for an oblivious transfer (OT) protocol under this noisy‑storage model. The protocol proceeds in two phases: (1) the sender prepares random BB84‑type qubits in randomly chosen bases and sends them to the receiver; (2) after a waiting period during which the receiver must store the qubits, both parties publicly reveal their basis choices, allowing the receiver to recover the bits corresponding to the basis of his choice while remaining ignorant of the other bits. The authors model the adversary’s stored quantum system as ρ_E = 𝒩^{⊗n}(ρ_in), where n is the number of qubits and 𝒩 is the noise channel. Using smooth min‑entropy H_min^ε(X|E) and the uncertainty relation for noisy quantum memories, they bound the amount of information the adversary can retain about the sender’s string X. Crucially, they show that for any non‑trivial noise level (i.e., any p > 0 for the depolarizing channel), the “information gap” between the honest receiver’s knowledge and the adversary’s knowledge remains positive, guaranteeing that the OT remains secure regardless of how many qubits are transmitted.
The analysis also extends to the case where honest parties are not ideal. By incorporating error‑correcting codes and privacy‑amplification techniques, the authors demonstrate that the OT protocol can tolerate realistic levels of measurement error and channel loss, yielding a “noisy‑tolerant OT” that still satisfies the security definition. This mirrors the development of noisy‑tolerant QKD but is applied to a two‑party primitive rather than key distribution.
Beyond OT, the paper sketches how the noisy‑storage model can be leveraged for secure identification. In this scenario, a client and a server share a short secret key; the client authenticates by engaging in a quantum exchange that, under the noisy‑storage assumption, prevents a malicious server from learning the client’s secret even if it possesses a quantum memory. The authors provide a sketch of the protocol and argue that the same entropy‑based security analysis applies.
In the discussion, the authors acknowledge limitations: the model assumes independent storage of each qubit and does not cover collective‑storage attacks where an adversary might store entangled blocks of qubits. They also note that the noise model is static; real devices may exhibit time‑varying decoherence rates, which would require a dynamic analysis. Future work is suggested on extending the proof techniques to collective attacks, on refining the noise model to include leakage and non‑Markovian effects, and on experimental validation using current quantum‑memory platforms.
Overall, the paper makes a significant conceptual shift by treating quantum storage noise as a security resource rather than a mere implementation flaw. It provides rigorous entropy‑based arguments that any amount of realistic noise suffices to protect oblivious transfer, and it opens the door to a broader class of two‑party cryptographic tasks that can be secured under physically motivated assumptions about quantum memory. This work bridges the gap between theoretical quantum cryptography and the practical constraints of near‑term quantum hardware.
Comments & Academic Discussion
Loading comments...
Leave a Comment