A Knowledge-Based Analysis of Global Function Computation
Consider a distributed system N in which each agent has an input value and each communication link has a weight. Given a global function, that is, a function f whose value depends on the whole network, the goal is for every agent to eventually compute the value f(N). We call this problem global function computation. Various solutions for instances of this problem, such as Boolean function computation, leader election, (minimum) spanning tree construction, and network determination, have been proposed, each under particular assumptions about what processors know about the system and how this knowledge can be acquired. We give a necessary and sufficient condition for the problem to be solvable that generalizes a number of well-known results. We then provide a knowledge-based (kb) program (like those of Fagin, Halpern, Moses, and Vardi) that solves global function computation whenever possible. Finally, we improve the message overhead inherent in our initial kb program by giving a counterfactual belief-based program that also solves the global function computation whenever possible, but where agents send messages only when they believe it is necessary to do so. The latter program is shown to be implemented by a number of well-known algorithms for solving leader election.
💡 Research Summary
The paper tackles the fundamental problem of global function computation in distributed systems: each agent holds a local input and the weight of its outgoing links, while the goal is for every agent to eventually learn the value of a function f that depends on the entire network N. The authors adopt a knowledge‑based perspective, building on the framework of Fagin, Halpern, Moses, and Vardi, to characterize precisely when such a computation is possible and to design protocols that achieve it with minimal communication overhead.
1. Characterizing Solvability via Bisimulation
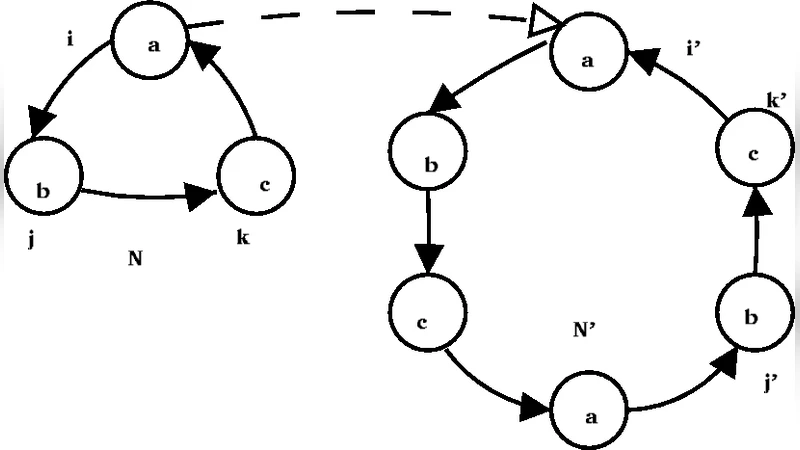
The authors model a network as a finite, directed, weighted graph whose nodes are agents. Agents share a common prior knowledge set 𝒩, the set of all networks they consider possible. To capture what an agent can deduce after k rounds of communication, they introduce a family of equivalence relations ∼ₖ (k‑bisimilarity) on pairs (N,i). Two pairs are 0‑bisimilar if the agents have the same input and identical outgoing edge weights under a bijection of their out‑neighbors. For k>0, (N,i)∼ₖ(N′,i′) holds if they are 0‑bisimilar and there exists a bijection between their incoming neighbors that preserves edge weights, bidirectionality, and the (k‑1)‑bisimilarity of the corresponding predecessor pairs. The key theorem states that global function computation is solvable exactly when, for every possible network N′ in 𝒩, the actual pair (N,i) remains bisimilar to (N′,i′) for all k, i.e., the agents can never distinguish the true network from any alternative in 𝒩. This condition subsumes earlier results on anonymous rings, unique identifiers, and bounded‑diameter graphs.
2. The Full‑Information Protocol
A straightforward solution is the full‑information protocol: in each round every agent broadcasts all the network information it currently possesses to all its out‑neighbors. Because messages are reliably delivered and stamped with round numbers, after enough rounds each agent learns the entire network topology, inputs, and edge weights, provided the bisimulation condition holds. While correct, this protocol can generate a prohibitive number of messages (essentially O(|E|·diameter)).
3. A Knowledge‑Based (KB) Program
To reduce redundancy, the authors propose a knowledge‑based program where actions depend on the agent’s knowledge operator Kᵢ. The core rule is: send a piece of information msg to neighbor j only if you do not know that j already knows msg. Formally, if ¬Kᵢ(Kⱼ(msg)) then send(msg). This program still guarantees convergence to the correct global value whenever the bisimulation condition is satisfied, because any information that could affect the computation is eventually propagated, but unnecessary duplicate transmissions are avoided.
4. Counterfactual Belief Optimization
A subtle inefficiency remains: an agent may still send msg to a neighbor who will learn it later through a different path. To eliminate this, the authors incorporate counterfactual belief constructs of the form ϕ > ψ (read “if ϕ were true, then ψ would hold”), following Halpern and Moses (2004). The refined rule becomes: send msg to neighbor j only if, were you not to send it now, you would still not believe that j will eventually learn msg. This captures the intuition “don’t send if the neighbor will learn it anyway”. The resulting counterfactual‑based KB program dramatically cuts message overhead while preserving correctness.
5. Connection to Classical Leader Election Algorithms
The paper demonstrates that, in the special case of leader election on rings with distinct identifiers, the counterfactual‑based KB program is essentially implemented by several well‑known algorithms:
- Le Lann’s algorithm (1977), Chang‑Roberts (1979), and Peterson’s algorithm (1982) all follow the pattern “only the agent with the currently highest identifier forwards its identifier to the right; lower identifiers stop forwarding”. This matches the counterfactual condition that a lower‑ID node believes the higher‑ID node will eventually disseminate the maximal identifier, so it refrains from sending.
- The optimal flooding protocol for bounded‑diameter networks also satisfies the counterfactual rule, because each node forwards a message only if it believes that some neighbor has not yet received it.
Thus, the authors unify a broad class of classic distributed protocols under a single epistemic framework.
6. Significance and Outlook
The contributions are threefold:
- A complete epistemic characterization of when global functions are computable in arbitrary finite networks, expressed via bisimulation.
- A generic KB protocol that solves the problem whenever it is solvable, together with a counterfactual refinement that achieves near‑optimal communication.
- A unifying perspective that shows many existing leader election, spanning‑tree, and network‑discovery algorithms are concrete implementations of the same epistemic principle.
By bridging modal epistemic logic with concrete distributed algorithm design, the paper provides a powerful tool for reasoning about the interplay between initial knowledge, communication patterns, and computational feasibility in distributed systems. It opens avenues for designing new protocols that are provably optimal with respect to both correctness and message complexity, guided by the underlying knowledge and belief structures of the participating agents.
Comments & Academic Discussion
Loading comments...
Leave a Comment