Random Linear Network Coding: A free cipher?
We consider the level of information security provided by random linear network coding in network scenarios in which all nodes comply with the communication protocols yet are assumed to be potential eavesdroppers (i.e. “nice but curious”). For this setup, which differs from wiretapping scenarios considered previously, we develop a natural algebraic security criterion, and prove several of its key properties. A preliminary analysis of the impact of network topology on the overall network coding security, in particular for complete directed acyclic graphs, is also included.
💡 Research Summary
The paper investigates the intrinsic security offered by random linear network coding (RLNC) in a setting where every node in the network follows the prescribed communication protocol but may act as an internal eavesdropper—a “nice but curious” adversary. This model diverges from classical wire‑tap scenarios that assume external attackers and instead focuses on the information that can be gleaned by legitimate intermediate nodes that have the ability to form linear combinations of the packets they receive.
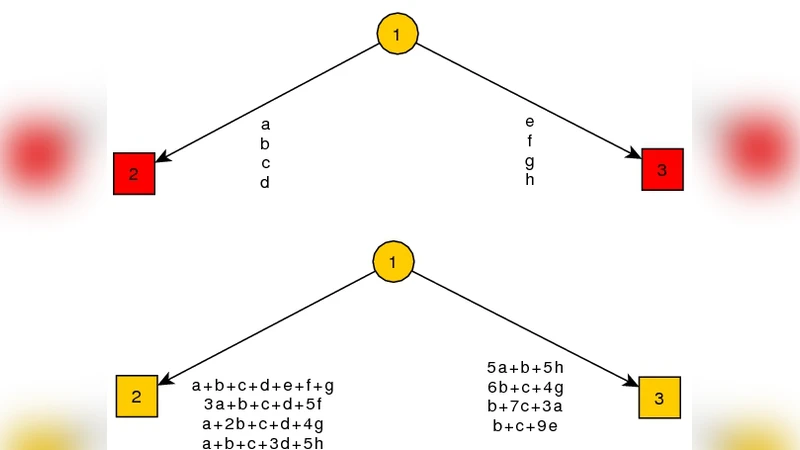
The authors first formalize the “nice but curious” model. Each node receives a set of packets, multiplies them by a randomly chosen coefficient vector over a finite field, and forwards the resulting linear combination. Because the coefficients are selected uniformly at random from a sufficiently large field, the global coding matrix that describes the transformation from source messages to packets observed at any node is, with high probability, full‑rank. The paper argues that traditional information‑theoretic secrecy metrics (e.g., equivocation) are inadequate for this internal‑adversary setting, prompting the introduction of a new algebraic security criterion.
The algebraic security criterion measures the dimension of the subspace spanned by the packets a node can observe relative to the dimension of the original message space. If the observed subspace has a rank significantly lower than the message dimension, the node cannot solve the linear system required to recover the source data without additional information. The authors prove three key properties of this criterion:
- Global Rank Preservation – Random coefficient matrices retain full rank across the entire network, ensuring that all honest receivers can decode the source messages while internal nodes see only a reduced‑rank projection.
- Node‑Level Recoverability Bound – For any given node, the probability of successful message reconstruction depends on the ratio of the node’s observed rank to the source dimension. When this ratio approaches one, security degrades; when it is small, reconstruction becomes computationally infeasible.
- Topological Influence – The network’s graph structure directly impacts the algebraic security level. In a complete directed acyclic graph (complete DAG), every node has the same indegree and outdegree, leading to uniform security guarantees across the network. In contrast, asymmetric or tree‑like topologies create “information hubs” with higher indegree, which can accumulate enough linear combinations to raise their observed rank and thus weaken security.
The paper then delves into a detailed analysis of complete DAGs. By modeling the coding process as a sequence of random linear transformations, the authors derive closed‑form expressions linking field size, network depth, and node count to the expected observed rank at any intermediate node. Simulations confirm that, for sufficiently large fields, the observed rank remains bounded well below the source dimension, even as the network scales. Moreover, the security improves with network size because the random mixing of packets grows more diverse, diluting any single node’s knowledge.
In the discussion, the authors compare RLNC‑based security to conventional cryptographic schemes. RLNC offers the attractive property of “key‑free” confidentiality: no secret keys need to be distributed or stored, and the randomness inherent in the coding coefficients provides a layer of obfuscation. However, they acknowledge that RLNC alone cannot guarantee perfect secrecy in all scenarios. In particular, nodes that happen to receive a large enough set of linearly independent packets (e.g., due to high indegree) may still reconstruct the source, suggesting that RLNC should be complemented with lightweight authentication or encryption when absolute confidentiality is required.
Finally, the paper outlines future research directions: extending the algebraic security framework to dynamic networks with changing topologies, incorporating non‑linear coding operations, and evaluating robustness against packet loss and delay. The authors also propose exploring hybrid schemes that combine RLNC with traditional cryptographic primitives to achieve both high throughput and provable security guarantees.
Overall, the work provides a rigorous foundation for understanding how random linear network coding can serve as a partial cipher in cooperative networks, quantifies the impact of graph topology on security, and offers practical insights for designing secure, high‑performance communication systems in environments where every node is both a participant and a potential eavesdropper.
Comments & Academic Discussion
Loading comments...
Leave a Comment