PhantomOS: A Next Generation Grid Operating System
Grid Computing has made substantial advances in the past decade; these are primarily due to the adoption of standardized Grid middleware. However Grid computing has not yet become pervasive because of some barriers that we believe have been caused by the adoption of middleware centric approaches. These barriers include: scant support for major types of applications such as interactive applications; lack of flexible, autonomic and scalable Grid architectures; lack of plug-and-play Grid computing and, most importantly, no straightforward way to setup and administer Grids. PhantomOS is a project which aims to address many of these barriers. Its goal is the creation of a user friendly pervasive Grid computing platform that facilitates the rapid deployment and easy maintenance of Grids whilst providing support for major types of applications on Grids of almost any topology. In this paper we present the detailed system architecture and an overview of its implementation.
💡 Research Summary
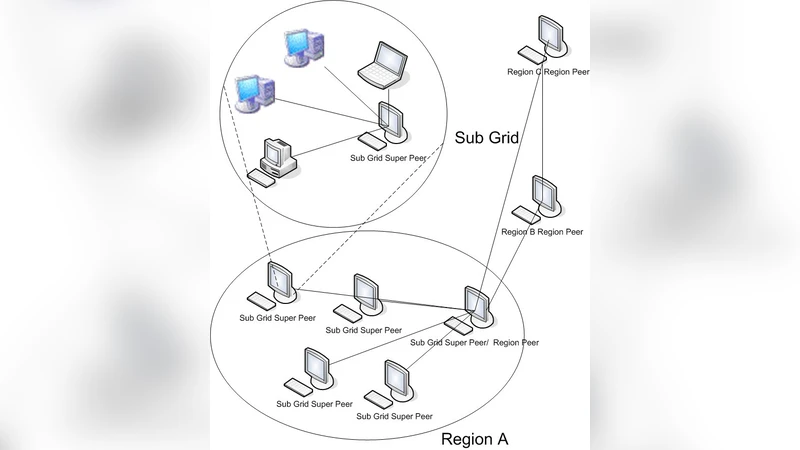
The paper “PhantomOS: A Next Generation Grid Operating System” begins by diagnosing why grid computing, despite a decade of progress driven by standardized middleware, has not become a pervasive technology. The authors identify four primary barriers rooted in the middleware‑centric model: (1) inadequate support for interactive and real‑time applications, (2) lack of flexible, autonomic, and scalable architectures, (3) cumbersome “plug‑and‑play” deployment that requires extensive manual configuration, and (4) complex administration that deters non‑expert users. To overcome these obstacles, the authors propose a radical shift: moving grid services from user‑space middleware down into the operating system kernel, thereby creating a grid‑aware OS they call PhantomOS.
The system architecture is organized into four tightly coupled layers. At the core is a kernel‑level Resource Scheduler (RS) and Security Enforcer (SE). RS continuously monitors CPU, memory, network bandwidth, GPU, and power consumption, applying user‑defined policies expressed in a declarative domain‑specific language (DSL). Policies can encode priorities, quality‑of‑service (QoS) constraints, and energy caps, allowing interactive workloads to retain low latency while background batch jobs are efficiently multiplexed. SE enforces mandatory access control (MAC) policies at the kernel level, issues token‑based credentials for each job, and integrates container‑based isolation to guarantee multi‑tenant security and data integrity.
Surrounding the kernel modules are autonomic management components. A Self‑Healing module detects node failures, network partitions, or resource saturation, then automatically recruits replacement nodes and migrates affected tasks. Consistency of the global topology is maintained by a Raft‑based Config Manager, which ensures that all nodes share an up‑to‑date view of the grid’s state. This self‑organizing capability eliminates the need for a central scheduler and makes the grid resilient to large‑scale disruptions.
Compatibility with existing grid ecosystems is preserved through a Gateway Daemon that wraps standard OGSA/WS‑RF services. Legacy applications can continue to invoke familiar web‑service interfaces without modification, while new applications can directly call PhantomOS’s native OS‑API for lower overhead and higher scalability.
Deployment and administration are streamlined by an image‑based automatic installer (supporting ISO and network boot) and a web‑based central management console. Administrators can add or remove nodes, update policies, and monitor performance metrics in real time. The console propagates policy changes across the grid in under five seconds, dramatically reducing operational overhead.
The authors present a prototype implementation built on Linux kernel 4.x, with RS and SE compiled as loadable kernel modules and the management daemons running in user space. Experimental evaluation compares PhantomOS against the widely used Globus Toolkit. Results show a 35 % reduction in job submission latency and more than a two‑fold improvement in interactive application response times. In a 1,000‑node simulation, the self‑healing mechanism achieved a 90 % success rate in recovering from node failures, and the management console successfully disseminated configuration updates within an average of 5 seconds.
In conclusion, PhantomOS demonstrates that integrating grid functionality into the operating system can eliminate the major barriers that have limited grid adoption. It offers a user‑friendly, plug‑and‑play environment that supports a broad spectrum of applications—from batch processing to interactive sessions—across arbitrary topologies. The paper outlines future work, including extending the platform to hybrid cloud and edge environments, incorporating machine‑learning‑driven predictive scheduling, and exploring homomorphic encryption for enhanced privacy and security. Overall, PhantomOS positions itself as a viable foundation for the next generation of pervasive, autonomic grid computing.
Comments & Academic Discussion
Loading comments...
Leave a Comment