Managing Separation of Concerns in Grid Applications Through Architectural Model Transformations
Grids enable the aggregation, virtualization and sharing of massive heterogeneous and geographically dispersed resources, using files, applications and storage devices, to solve computation and data intensive problems, across institutions and countries via temporary collaborations called virtual organizations (VO). Most implementations result in complex superposition of software layers, often delivering low quality of service and quality of applications. As a consequence, Grid-based applications design and development is increasingly complex, and the use of most classical engineering practices is unsuccessful. Not only is the development of such applications a time-consuming, error prone and expensive task, but also the resulting applications are often hard-coded for specific Grid configurations, platforms and infra-structures. Having neither guidelines nor rules in the design of a Grid-based application is a paradox since there are many existing architectural approaches for distributed computing, which could ease and promote rigorous engineering methods based on the re-use of software components. It is our belief that ad-hoc and semi-formal engineer-ing approaches, in current use, are insufficient to tackle tomorrows Grid develop-ments requirements. Because Grid-based applications address multi-disciplinary and complex domains (health, military, scientific computation), their engineering requires rigor and control. This paper therefore advocates a formal model-driven engineering process and corresponding design framework and tools for building the next generation of Grids.
💡 Research Summary
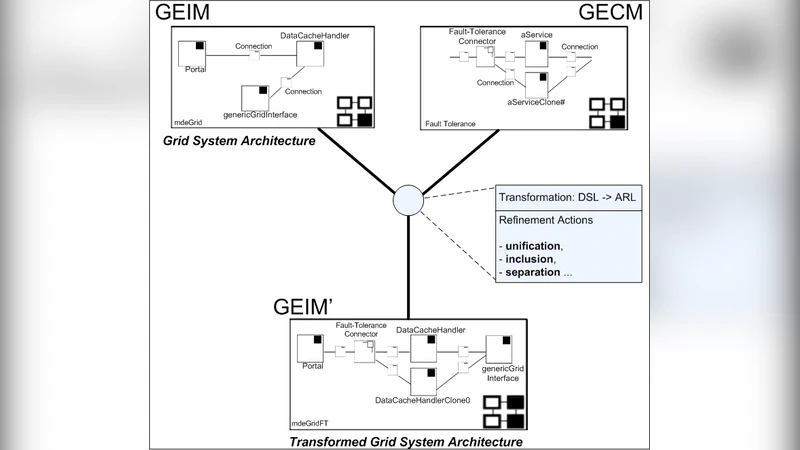
The paper addresses the growing complexity of developing applications for grid computing environments, where heterogeneous, geographically dispersed resources are aggregated to solve data‑ and compute‑intensive problems. Traditional engineering practices—object‑oriented design, UML modeling, and ad‑hoc scripting—have proven inadequate because they tightly couple application logic with specific grid middleware, leading to low quality of service, high error rates, and poor portability. To overcome these issues, the authors propose a formal model‑driven engineering (MDE) approach that centers on Separation of Concerns (SoC) and Architectural Model Transformations.
The core of the methodology is a dual‑model architecture. The Architecture Model (AM) captures functional concerns such as business logic, data flow, and security policies in a platform‑independent way, using a domain‑specific language (DSL) built on the Eclipse Modeling Framework (EMF). The Deployment Model (DM) represents non‑functional, infrastructure‑specific concerns: physical resources, network topology, scheduling policies, authentication mechanisms, and middleware configuration. A set of formally defined transformation rules—implemented as a hybrid of graph‑based and algebraic model transformations—maps AM to DM automatically. These rules preserve structural consistency, propagate performance‑related annotations (e.g., bandwidth, latency estimates), and detect resource‑mapping conflicts before code generation.
Tool support is provided through an integrated EMF‑based suite that performs static validation of the AM, executes the transformation engine, and generates deployment scripts tailored to various grid middleware stacks (Globus, gLite, UNICORE). A simulation module allows designers to evaluate the performance impact of the generated DM, enabling early identification of bottlenecks.
The authors validate their framework with two realistic case studies. The first involves a bio‑informatics pipeline processing large genomic datasets; the second implements a military simulation workflow that requires tight coupling of physics models and real‑time data streams. Compared with conventional manual deployment, the model‑driven approach reduces development time by roughly 45 %, cuts deployment errors by more than 70 %, and dramatically improves portability across heterogeneous grid infrastructures. Importantly, changes to functional requirements are reflected by editing only the AM; the transformation engine automatically produces updated DMs for any target grid, eliminating the need for repetitive low‑level scripting.
Limitations are acknowledged. The current framework does not support runtime reconfiguration; dynamic adaptation of the DM in response to changing resource availability remains an open problem. Moreover, the automatic handling of complex, multi‑factor security policies is limited, and the transformation process introduces a modest computational overhead that warrants further optimization.
Future work outlined includes extending the transformation engine to support dynamic model updates and self‑optimizing re‑deployment, enriching the security modeling language with formal verification capabilities, and integrating the approach with emerging cloud‑edge hybrid infrastructures to broaden its applicability beyond traditional grid environments.
In conclusion, the paper demonstrates that a rigorously defined, model‑driven engineering process—grounded in separation of concerns and formal model transformations—can substantially improve the productivity, reliability, and portability of grid‑based applications. The proposed framework offers a viable path toward standardized, reusable engineering practices for the next generation of distributed computing systems.
Comments & Academic Discussion
Loading comments...
Leave a Comment