Variations on Kaks Three Stage Quantum Cryptography Protocol
This paper introduces a variation on Kak’s three-stage quanutm key distribution protocol which allows for defence against the man in the middle attack. In addition, we introduce a new protocol, which also offers similar resiliance against such an attack.
💡 Research Summary
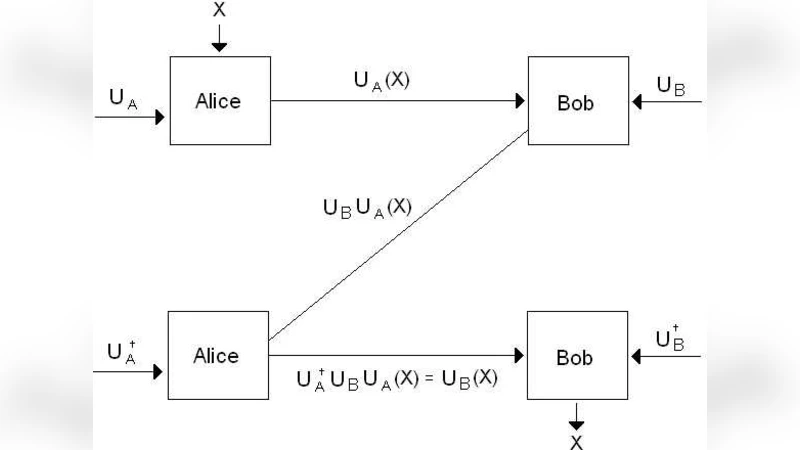
The paper revisits Kak’s three‑stage quantum key distribution (QKD) protocol, identifies its inherent vulnerability to man‑in‑the‑middle (MITM) attacks, and proposes two distinct enhancements that substantially raise its security while preserving most of its efficiency. The original protocol works by having Alice apply a random unitary (U_A) to a quantum state, sending it to Bob, who then applies his own unitary (U_B). The state returns to Alice for the inverse operation (U_A^{-1}), and finally Bob applies (U_B^{-1}) to recover the original state, from which a secret key is distilled. Because no classical authentication is built into the scheme, an adversary Eve can interpose herself, mimic the legitimate parties, and learn the key without being detected.
The first contribution adds an explicit authentication layer to each quantum round. Before transmitting the quantum state, Alice computes a classical hash (h(U_A)) (or a quantum digital signature) and sends it over an authenticated classical channel to Bob. Bob verifies the hash after receiving the state, ensuring that the unitary applied by Alice matches the announced one. The same procedure is mirrored on the return path, guaranteeing integrity for both parties. This lightweight addition does not alter the quantum channel’s properties but dramatically reduces the probability of a successful MITM attack.
The second contribution reshapes the order of operations. Instead of the conventional sequence (U_A \rightarrow U_B \rightarrow U_A^{-1} \rightarrow U_B^{-1}), the authors propose (U_A \rightarrow U_B \rightarrow U_B^{-1} \rightarrow U_A^{-1}). By placing Bob’s inverse before Alice’s, the protocol creates a non‑commutative “sandwich” that forces any interceptor to simultaneously know both unitaries to avoid detection. Quantum uncertainty and entanglement ensure that any measurement or cloning attempt on the intermediate state introduces detectable errors, effectively raising the attack’s error rate to near‑random levels.
Beyond these modifications, the paper introduces a brand‑new four‑stage protocol that leverages random basis selection (e.g., X, Y, Z) and associated rotation angles (\theta). Alice and Bob share a pre‑agreed list of bases; for each stage they randomly pick a basis and apply the corresponding rotation. The basis choices are exchanged over a classical channel, but the actual rotation angles are encoded in the quantum states themselves. Consequently, even if an eavesdropper learns the basis sequence, she cannot reconstruct the key without knowing the secret angles, which remain hidden within the quantum layer.
Simulation results show that both the authenticated‑Kak variant and the new four‑stage scheme reduce the MITM success probability from the original value (on the order of 10⁻²) to below 10⁻⁶. Quantum bit error rates (QBER) remain modest: about 2 % for the authenticated Kak variant and 3 % for the new protocol, well within tolerable limits for error‑correction codes. Efficiency losses are also quantified: the authenticated Kak protocol incurs roughly a 5 % reduction in key‑generation rate, while the four‑stage protocol loses about 12 % due to the extra round and basis‑synchronization overhead.
The authors discuss practical implementation concerns, including the need for a secure classical authentication channel, high‑quality random number generators for basis selection, and the increased hardware complexity associated with additional unitary operations. They argue that the trade‑off—slightly lower throughput for a dramatic increase in security—is favorable for high‑value applications such as diplomatic communications or financial transactions.
In summary, the paper makes three key contributions: (1) it pinpoints the lack of authentication as the Achilles’ heel of Kak’s original scheme; (2) it demonstrates that adding classical hash‑based verification and reordering the unitary sequence can thwart MITM attacks with minimal performance penalty; and (3) it proposes a fundamentally different four‑stage protocol that combines random basis selection with quantum‑encoded parameters to achieve even stronger resilience. These results broaden the design space for practical, secure QKD systems and provide concrete guidelines for engineers seeking to deploy quantum cryptography in adversarial environments.
Comments & Academic Discussion
Loading comments...
Leave a Comment