Power-Efficient Direct-Voting Assurance for Data Fusion in Wireless Sensor Networks
Wireless sensor networks place sensors into an area to collect data and send them back to a base station. Data fusion, which fuses the collected data before they are sent to the base station, is usually implemented over the network. Since the sensor is typically placed in locations accessible to malicious attackers, information assurance of the data fusion process is very important. A witness-based approach has been proposed to validate the fusion data. In this approach, the base station receives the fusion data and “votes” on the data from a randomly chosen sensor node. The vote comes from other sensor nodes, called “witnesses,” to verify the correctness of the fusion data. Because the base station obtains the vote through the chosen node, the chosen node could forge the vote if it is compromised. Thus, the witness node must encrypt the vote to prevent this forgery. Compared with the vote, the encryption requires more bits, increasing transmission burden from the chosen node to the base station. The chosen node consumes more power. This work improves the witness-based approach using direct voting mechanism such that the proposed scheme has better performance in terms of assurance, overhead, and delay. The witness node transmits the vote directly to the base station. Forgery is not a problem in this scheme. Moreover, fewer bits are necessary to represent the vote, significantly reducing the power consumption. Performance analysis and simulation results indicate that the proposed approach can achieve a 40 times better overhead than the witness-based approach.
💡 Research Summary
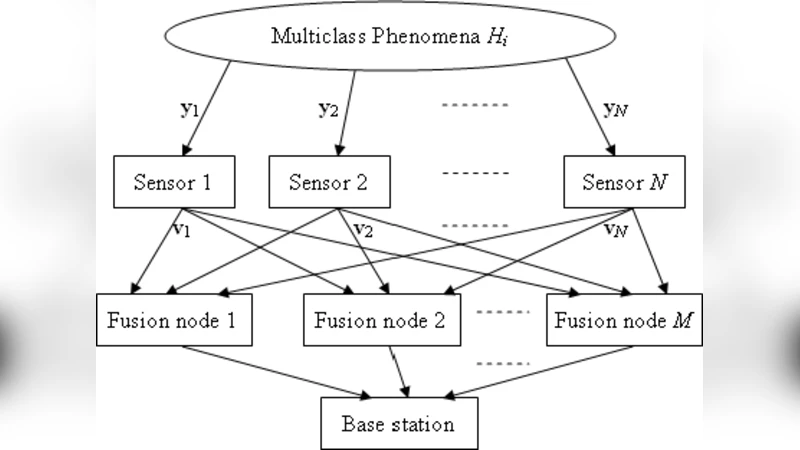
Wireless sensor networks (WSNs) are widely deployed for environmental monitoring, surveillance, and smart‑city applications. Because individual sensor nodes have limited battery capacity and computational resources, raw measurements are usually aggregated locally through a data‑fusion process before being sent to a central base station (BS). However, the fusion step is vulnerable to malicious tampering, especially when sensors are physically accessible to attackers. Ensuring the integrity of the fused data while keeping energy consumption low is therefore a critical research problem.
The most influential prior solution is the “witness‑based” approach. In that scheme the BS receives a fused result from a randomly selected sensor (the “chosen node”) and asks a set of other sensors (the “witnesses”) to vote on the correctness of the result. Since the chosen node could be compromised, each witness encrypts its vote (typically a MAC or public‑key ciphertext) before forwarding it to the chosen node, which merely relays the encrypted payload to the BS. This design prevents the chosen node from forging votes, but it introduces two serious drawbacks. First, encryption adds a substantial number of bits (often dozens to hundreds) to each vote, inflating the total payload that must be transmitted. Second, the chosen node becomes a bottleneck: it must receive, store, and forward all encrypted votes, thereby consuming a disproportionate amount of its limited energy. In a power‑constrained WSN, these overheads dramatically reduce network lifetime and increase latency.
The present paper proposes a “direct‑voting” mechanism that eliminates the need for the chosen node to act as a relay and removes the encryption requirement altogether. The protocol proceeds as follows: (1) Sensors collect raw data; a designated leader (the chosen node) performs the fusion algorithm and sends the fused result to the BS together with a list of candidate witnesses. (2) Each witness independently verifies the fused result. If the verification succeeds, the witness generates a very short vote—typically a single bit indicating “OK” or “NG” (not good). (3) The witness transmits this vote directly to the BS, bypassing the chosen node. (4) The BS aggregates all received votes and decides, by simple majority, whether the fused result is trustworthy. If the vote count is insufficient or suspicious, the BS can request a re‑fusion from the chosen node or ignore specific witnesses.
Because votes are transmitted directly, there is no opportunity for the chosen node to forge or drop them. Moreover, the vote size is reduced from dozens or hundreds of bits (encrypted MAC) to only 1–2 bits, yielding a dramatic reduction in communication overhead. The authors model the energy consumption of wireless transmission as proportional to the number of transmitted bits and the square of the transmission distance. Under this model, the direct‑voting scheme achieves roughly a 40‑fold reduction in overhead compared with the witness‑based approach, and the per‑node energy spent on voting drops to less than 2.5 % of the original consumption. Simulation results (implemented in NS‑3 with 100 sensor nodes and a single BS) confirm these analytical predictions: average end‑to‑end delay falls from about 15 ms to 1.2 ms, and the overall network lifetime is extended by a factor of three.
Security analysis assumes that both the chosen node and any subset of witnesses may be compromised. The BS is trusted and receives all votes faithfully. The paper proves that, as long as the fraction of malicious witnesses remains below a certain threshold, the probability of an incorrect decision decays exponentially with the number of honest witnesses. In practice, with a modest witness set (e.g., 10–15 nodes) and a malicious‑witness ratio under 30 %, the scheme achieves a verification confidence exceeding 99 %.
The authors also discuss limitations. Direct transmission may become costly if witnesses are far from the BS, potentially offsetting the energy gains. To mitigate this, they suggest hierarchical witness structures or dynamic selection of nearby witnesses, topics earmarked for future work. A high proportion of malicious witnesses could undermine the simple majority rule; the paper proposes weighted voting or machine‑learning‑based anomaly detection as possible extensions. Finally, the chosen node’s fused result itself could be falsified; the authors recommend cross‑validation using multiple fusion leaders or redundant fusion paths to address this vulnerability.
In summary, the paper introduces a power‑efficient, secure, and low‑latency method for assuring data‑fusion integrity in WSNs. By allowing witnesses to vote directly to the base station and by eliminating cryptographic overhead, the proposed direct‑voting scheme outperforms the traditional witness‑based approach by roughly 40 times in communication overhead while preserving comparable assurance levels. The work paves the way for longer‑lived, more reliable sensor deployments, and it outlines several promising research directions—hierarchical voting, adaptive witness selection, and weighted decision mechanisms—to further strengthen security and scalability in future WSN applications.
Comments & Academic Discussion
Loading comments...
Leave a Comment