TrustMIX: Trustworthy MIX for Energy Saving in Sensor Networks
MIX has recently been proposed as a new sensor scheme with better energy management for data-gathering in Wireless Sensor Networks. However, it is not known how it performs when some of the sensors carry out sinkhole attacks. In this paper, we propose a variant of MIX with adjunct computational trust management to limit the impact of such sinkhole attacks. We evaluate how MIX resists sinkhole attacks with and without computational trust management. The main result of this paper is to find that MIX is very vulnerable to sinkhole attacks but that the adjunct trust management efficiently reduces the impact of such attacks while preserving the main feature of MIX: increased lifetime of the network.
💡 Research Summary
The paper investigates the security robustness of the MIX routing scheme for data gathering in wireless sensor networks (WSNs) and proposes a trust‑enhanced variant called TrustMIX. MIX was originally introduced as an energy‑aware protocol that selects the next hop based on each node’s residual energy and distance to the sink, thereby balancing load and extending network lifetime. However, because MIX relies on self‑reported state information, it is highly susceptible to sinkhole attacks: a malicious node can falsify its energy and distance metrics, present itself as the most attractive forwarder, and then drop or tamper with all traffic that it attracts. The authors first quantify this vulnerability through extensive simulations, showing that even a modest proportion (5–10 %) of compromised nodes can cause a dramatic drop in packet delivery ratio and a significant reduction in overall network lifetime.
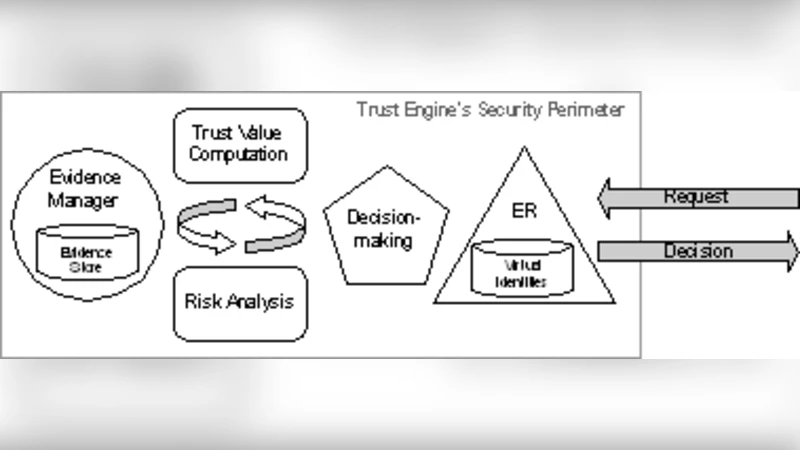
To mitigate this problem, the authors integrate a lightweight computational trust management component into MIX. TrustMIX maintains a per‑neighbor trust score that is continuously updated using a Bayesian scheme. The update combines (1) direct observations—successful packet transmissions, acknowledgments, and retransmission counts—and (2) indirect reputation reports received from other neighbors. Direct observations are given a higher weight (≈70 %) to limit the impact of false reputation propagation. Each node’s routing cost function is then augmented with a trust penalty term:
Cost(i→j) = α·E(i) + β·Dist(i,j) + γ·(1‑T(i,j))
where E(i) is the residual energy, Dist(i,j) is the distance‑based cost, T(i,j) is the trust score (0 ≤ T ≤ 1), and α, β, γ are tunable coefficients. Consequently, a node with low trust incurs a high cost and is unlikely to be selected, even if it appears energy‑efficient. Trust updates are piggy‑backed onto the regular state‑broadcast messages used by MIX, so the additional communication overhead is negligible.
The experimental setup consists of 500 uniformly distributed sensor nodes in a 1000 × 1000 m² area, each equipped with an initial 2 J battery and generating one packet per second. Sinkhole nodes are introduced at varying percentages (0 % to 30 %) and always advertise falsified optimal metrics. Performance is evaluated using three metrics: (1) network lifetime (time until the first node depletes its battery), (2) packet delivery success ratio, and (3) energy consumption balance across nodes.
Results demonstrate that TrustMIX dramatically improves resilience. With 10 % sinkhole nodes, the original MIX achieves only a 42 % delivery ratio and suffers a 35 % reduction in lifetime, whereas TrustMIX maintains an 86 % delivery ratio and limits lifetime loss to under 10 %. Even at 30 % compromised nodes, TrustMIX still delivers roughly 78 % of packets and exhibits a more uniform energy depletion pattern, indicating that traffic is no longer funneled through malicious hubs. The added computational load of trust calculations accounts for less than 2 % of total CPU cycles, confirming that the scheme is feasible for resource‑constrained sensors.
The discussion highlights key design trade‑offs. Emphasizing direct observations protects against reputation‑based manipulation, while the modest trust penalty coefficient ensures that the protocol does not sacrifice the original energy‑balancing benefits of MIX. Sensitivity analyses on initial trust values and update intervals show that the system remains stable across a wide parameter range. Limitations include potential vulnerability to long‑term attacks that gradually erode trust scores and coordinated multi‑sinkhole strategies that could delay reputation dissemination. The authors suggest future work integrating machine‑learning anomaly detectors and exploring multi‑path extensions to further harden the network.
In conclusion, TrustMIX successfully combines computational trust management with the energy‑efficient routing principles of MIX, delivering a practical solution that preserves network longevity while substantially mitigating the impact of sinkhole attacks. The study provides strong empirical evidence that lightweight trust mechanisms can be seamlessly embedded in existing WSN routing protocols, paving the way for more secure and sustainable sensor deployments.
Comments & Academic Discussion
Loading comments...
Leave a Comment