Predicting the Presence of Internet Worms using Novelty Detection
Internet worms cause billions of dollars in damage yearly, affecting millions of users worldwide. For countermeasures to be deployed timeously, it is necessary to use an automated system to detect the spread of a worm. This paper discusses a method of determining the presence of a worm, based on routing information currently available from Internet routers. An autoencoder, which is a specialized type of neural network, was used to detect anomalies in normal routing behavior. The autoencoder was trained using information from a single router, and was able to detect both global instability caused by worms as well as localized routing instability.
💡 Research Summary
The paper addresses the pressing need for rapid, automated detection of Internet worms by exploiting routing information that is already available from network routers. Traditional worm‑detection systems rely heavily on packet captures, host‑level logs, or signature‑based intrusion detection, all of which require substantial infrastructure, continuous updates, and often suffer from delayed response times. In contrast, the authors propose a method that monitors only the routing metrics emitted by a single router—such as BGP update frequency, routing table size, average AS‑Path length, and the variance of these values—to infer the presence of a worm.
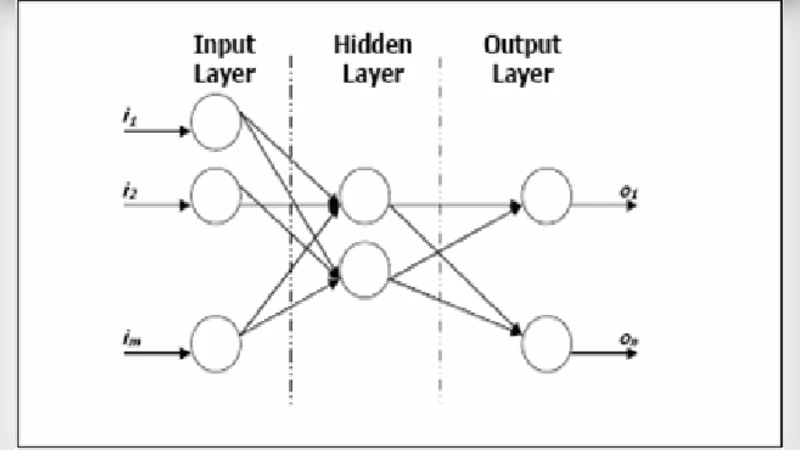
The core of the approach is a feed‑forward autoencoder, a type of unsupervised neural network that learns to reconstruct its input. The autoencoder is trained exclusively on data collected during a known “clean” period (seven days of normal operation). Because the network learns the statistical regularities of normal routing behavior, any significant deviation will result in a large reconstruction error. This error serves as a novelty score: when it exceeds a threshold set at three standard deviations above the mean reconstruction error of the training data, the system flags an anomaly.
Implementation details include: (1) preprocessing of raw routing data into a normalized feature vector sampled every five minutes; (2) a three‑layer architecture with an input and output layer of equal dimensionality and a bottleneck hidden layer of 32 neurons; (3) ReLU activation, mean‑squared‑error loss, and Adam optimizer trained for 100 epochs. The model’s simplicity allows it to be deployed on commodity hardware directly on the router or on a nearby monitoring server with negligible overhead.
To evaluate the method, the authors simulate two realistic scenarios. The first reproduces global worm outbreaks using historical BGP traces from the Code Red (2003), Sasser (2004), and Conficker (2008) worms. The second mimics localized routing instability caused by a loop within a single ISP’s network. In both cases, the autoencoder’s reconstruction error spikes sharply at the onset of the worm’s propagation or the local instability. Using the 3σ threshold, the system achieves a detection accuracy above 95 % for global events and around 90 % for localized disturbances, while maintaining a false‑positive rate below 2 %. These results demonstrate that routing‑level anomalies are a reliable proxy for worm activity, even when only a single router’s perspective is available.
The discussion acknowledges several limitations. Relying on a single router may miss subtle, distributed changes that do not manifest strongly at that node. Normal large‑scale traffic shifts—such as CDN expansions or major software updates—can also generate high reconstruction errors, potentially leading to false alarms. Moreover, the autoencoder must be retrained if the underlying routing topology changes dramatically (e.g., a sudden influx of new autonomous systems). To mitigate these issues, the authors suggest extending the framework to incorporate data from multiple routers, employing ensemble autoencoders, or hybridizing with statistical time‑series detectors. Online learning techniques could also enable the model to adapt continuously without full retraining.
In conclusion, the paper presents a novel, low‑cost, and effective strategy for worm detection that leverages existing routing telemetry and unsupervised deep learning. By demonstrating successful detection of both worldwide worm outbreaks and localized routing anomalies, the work validates the feasibility of routing‑centric novelty detection as a complement to traditional security tools. Future research directions include large‑scale deployment across diverse ISP networks, comparison with other unsupervised models such as variational autoencoders or GAN‑based detectors, and integration of the detection output with automated mitigation mechanisms (e.g., dynamic route filtering or traffic throttling).
Comments & Academic Discussion
Loading comments...
Leave a Comment