Cs-Cr

A Bespoke Forensics GIS Tool

Considerations for Cloud Security Operations

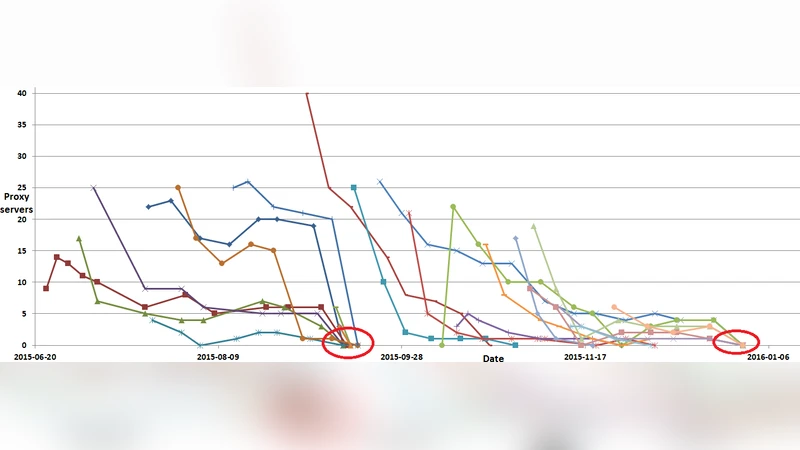
Autonomous collision attack on OCSP services
A Rational Approach to Cryptographic Protocols

First Experimental Demonstration of Secure NFV Orchestration over an SDN-Controlled Optical Network with Time-Shared Quantum Key Distribution Resources
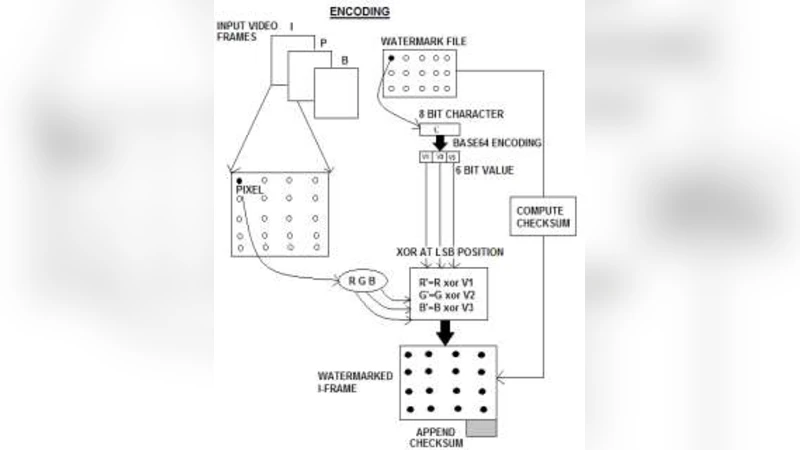
Algorithmic Analysis of Invisible Video Watermarking using LSB Encoding Over a Client-Server Framework

User Data Sharing Frameworks: A Blockchain-Based Incentive Solution

State of the art of Trust and Reputation Systems in E-Commerce Context
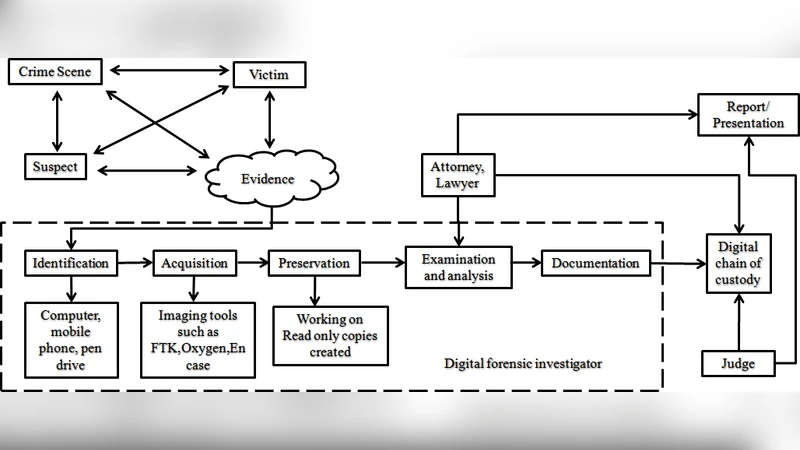
Taxonomy of Digital Forensics: Investigation Tools and Challenges
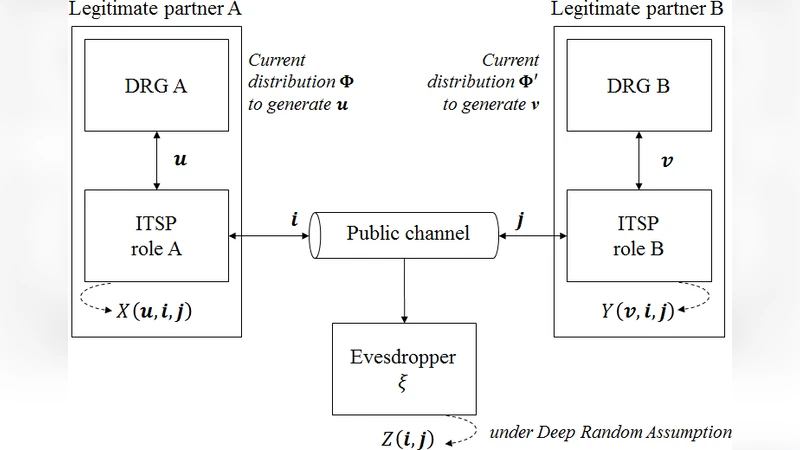
Simulations for Deep Random Secrecy Protocol

Promises and Challenges in Continuous Tracking Utilizing Amino Acids in Skin Secretions for Active Multi-Factor Biometric Authentication for Cybersecurity
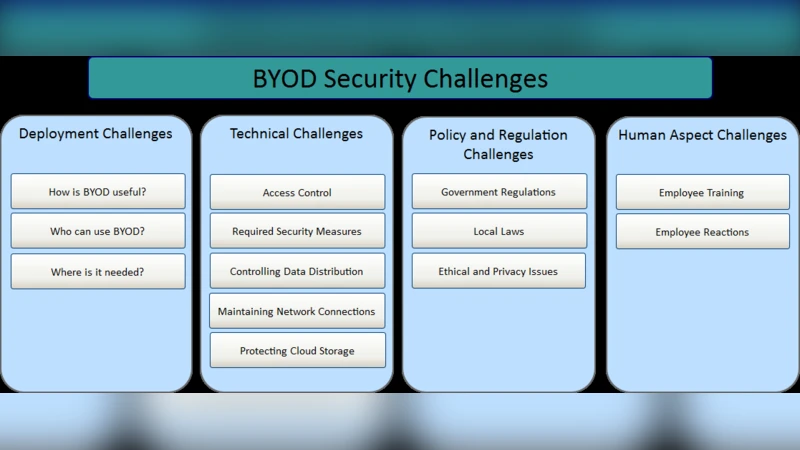
BYOD Security: A New Business Challenge
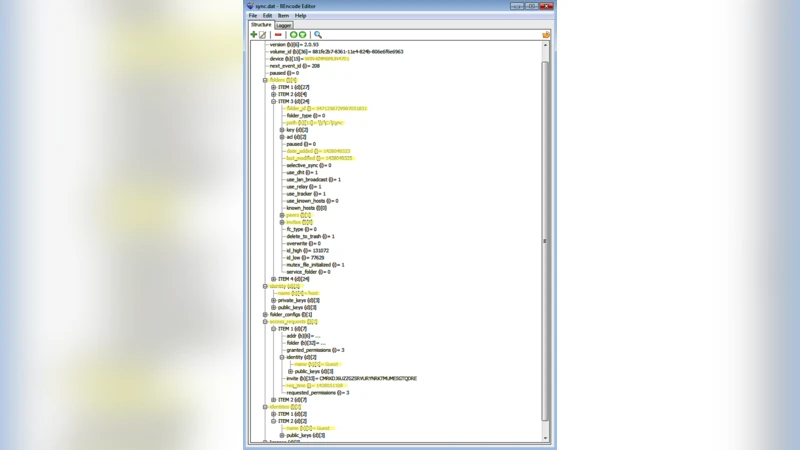
Forensic Investigation of P2P Cloud Storage: BitTorrent Sync as a Case Study
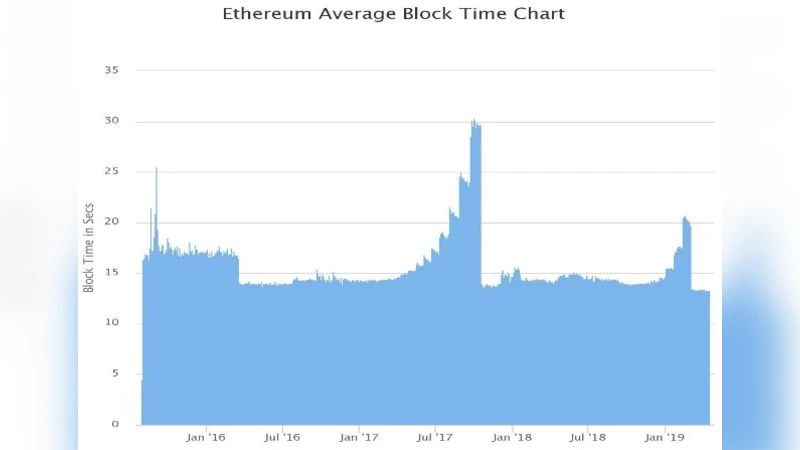
Transaction Confirmation Time Prediction in Ethereum Blockchain Using Machine Learning
Coverless Information Hiding Based on Generative adversarial networks

Privacy Knowledge Modelling for Internet of Things: A Look Back
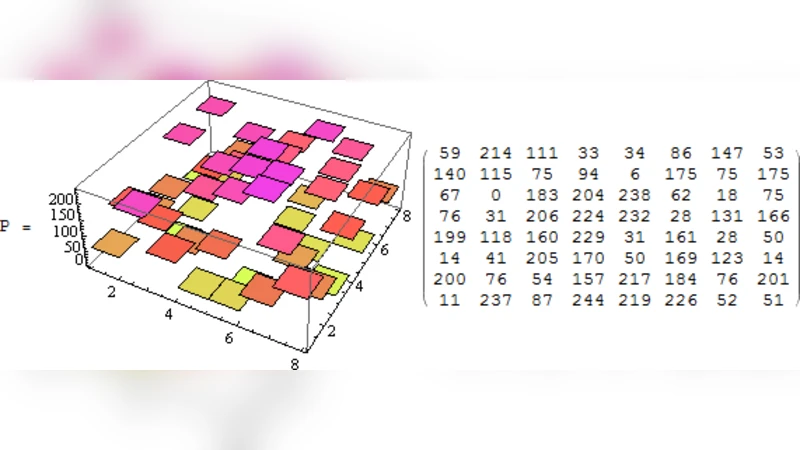
Post-Quantum Cryptography(PQC): Generalized ElGamal Cipher over GL(8,F251)
Software-Defined Networking-based Crypto Ransomware Detection Using HTTP Traffic Characteristics
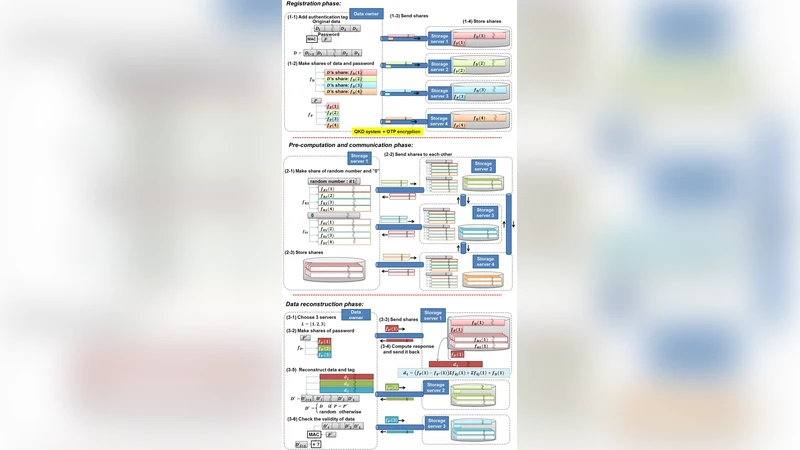
Unbreakable distributed storage with quantum key distribution network and password-authenticated secret sharing
Software-based Microarchitectural Attacks
The Shutdown Problem: How Does a Blockchain System End?

Term-based composition of security protocols
