Cs-Cr

Secure estimation and control for cyber-physical systems under adversarial attacks
Secure FSM- based arithmetic codes
Secure management of logs in internet of things
Secure voice based authentication for mobile devices: Vaulted Voice Verification
Secure Zones: An Attribute-Based Encryption advisory system for safe firearms
Secured Wireless Communication using Fuzzy Logic based High Speed Public-Key Cryptography (FLHSPKC)
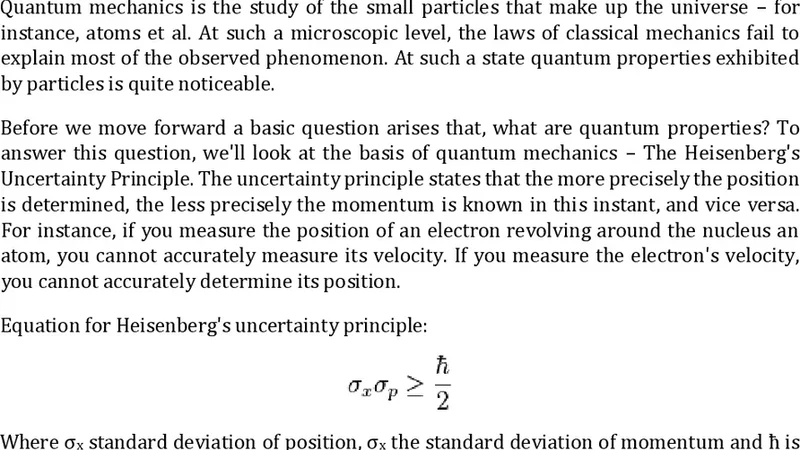
Securing Cloud - The Quantum Way
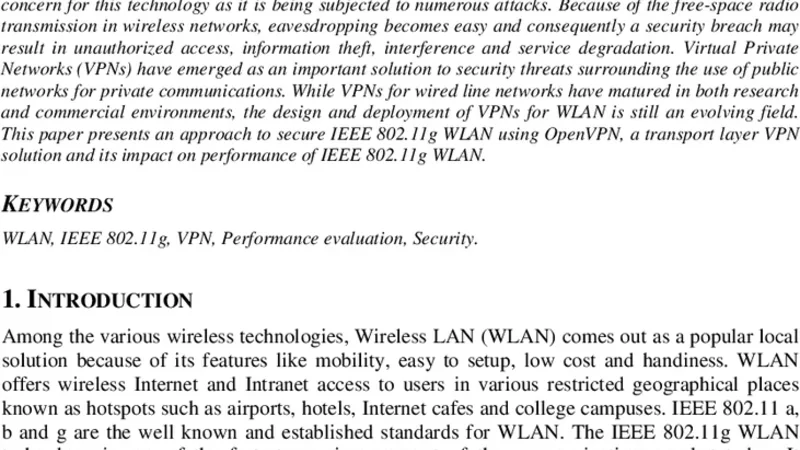
Securing IEEE 802.11G WLAN Using OpenVPN and Its Impact Analysis
Security Metrics in Industrial Control Systems
Security-aware selection of Web Services for Reliable Composition
Selective Watchdog Technique for Intrusion Detection in Mobile Ad-Hoc Network
Spread Spectrum based Robust Image Watermark Authentication
STAR-Vote: A Secure, Transparent, Auditable, and Reliable Voting System
Stickler: Defending Against Malicious CDNs in an Unmodified Browser
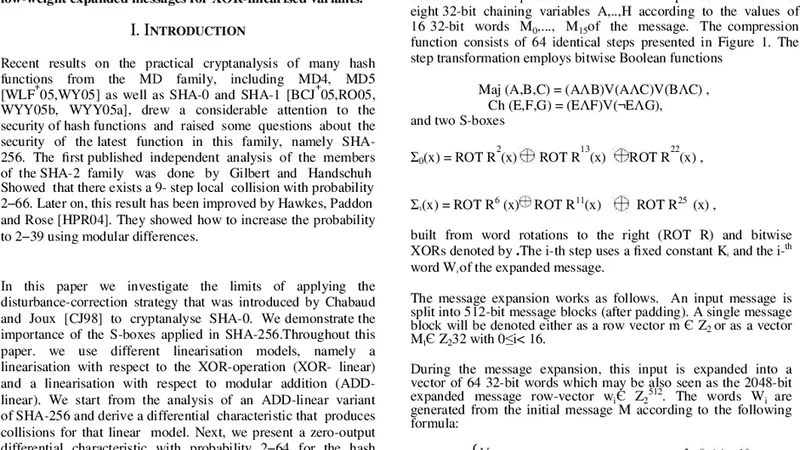
Study the function of building blocks in SHA Family
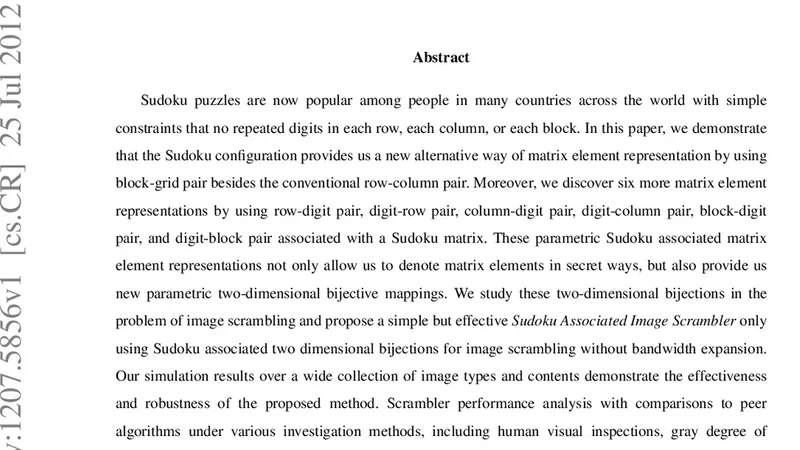
Sudoku Associated Two Dimensional Bijections for Image Scrambling
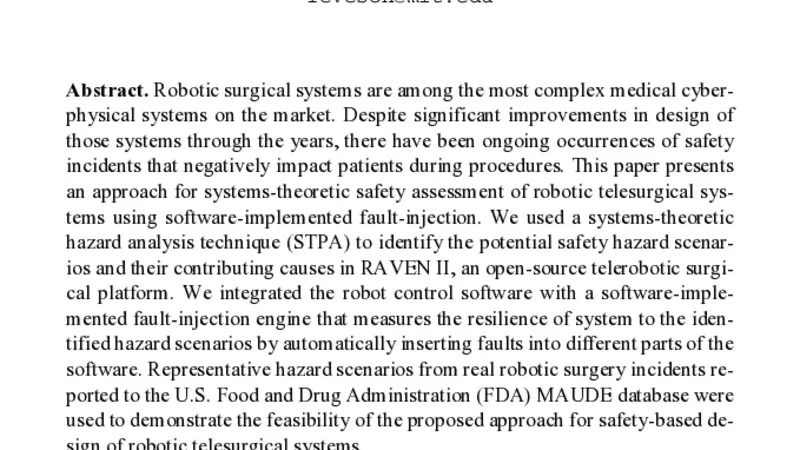
Systems-theoretic Safety Assessment of Robotic Telesurgical Systems
Technical Analysis of Security Infrastructure in RFID Technology

The Arduino as a Hardware Random-Number Generator

The Power of Linear Reconstruction Attacks
Towards Design and Implementation of Space Efficient and Secured Transmission scheme on EGovernance data
Towards Security of Additive Layer Manufacturing