Cs-Cr

The Arduino as a Hardware Random-Number Generator

The Power of Linear Reconstruction Attacks
Towards Design and Implementation of Space Efficient and Secured Transmission scheme on EGovernance data
Towards Security of Additive Layer Manufacturing
Tracking and Quantifying Censorship on a Chinese Microblogging Site

Trust Management in Cloud Computing: A Critical Review
TSET: Token based Secure Electronic Transaction
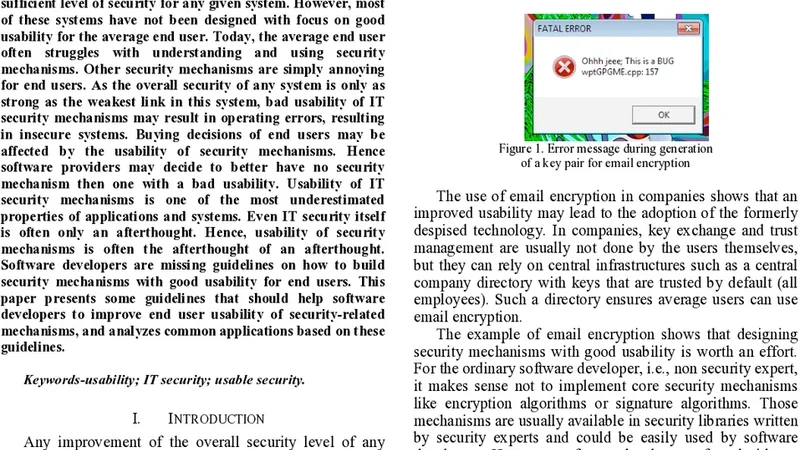
User-Centric IT Security - How to Design Usable Security Mechanisms