
Cs-Cr

Improving GGH Public Key Scheme Using Low Density Lattice Codes
Information Hiding in CSS : A Secure Scheme Text-Steganography using Public Key Cryptosystem

Intrusion Detection using Continuous Time Bayesian Networks

Investigation of Hill Cipher Modifications Based on Permutation and Iteration
JoKER: Trusted Detection of Kernel Rootkits in Android Devices via JTAG Interface
Key recycling in authentication

Loc-Auth: Location-Enabled Authentication Through Attribute-Based Encryption
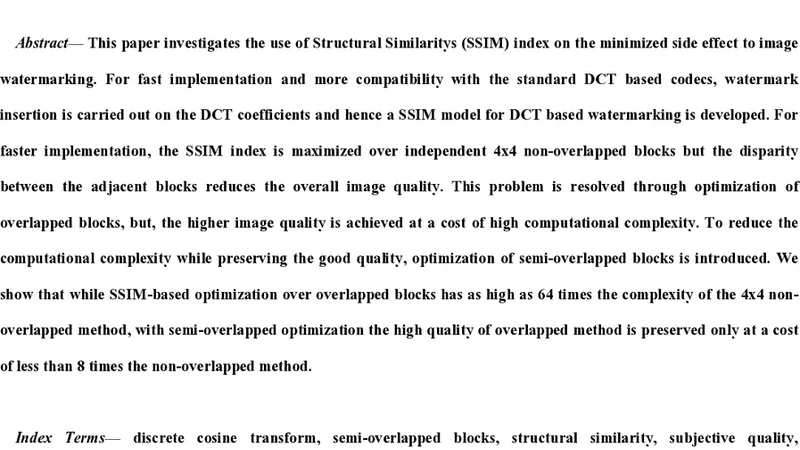
Minimization of image watermarking side effects through subjective optimization

Multiplayer Games and their Need for Scalable and Secure State Management
New Method for Public Key Distribution Based on Social Networks
Optimal error of query sets under the differentially-private matrix mechanism
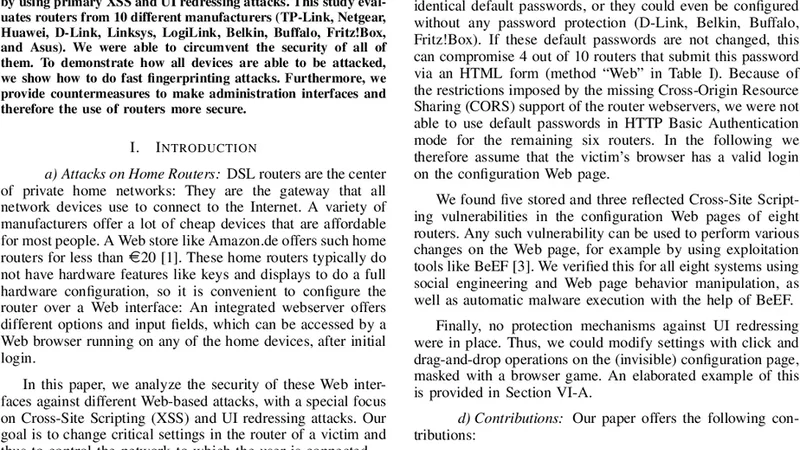
Owning Your Home Network: Router Security Revisited
Packet Drop Attack Detection Techniques in Wireless Ad hoc Networks: A Review
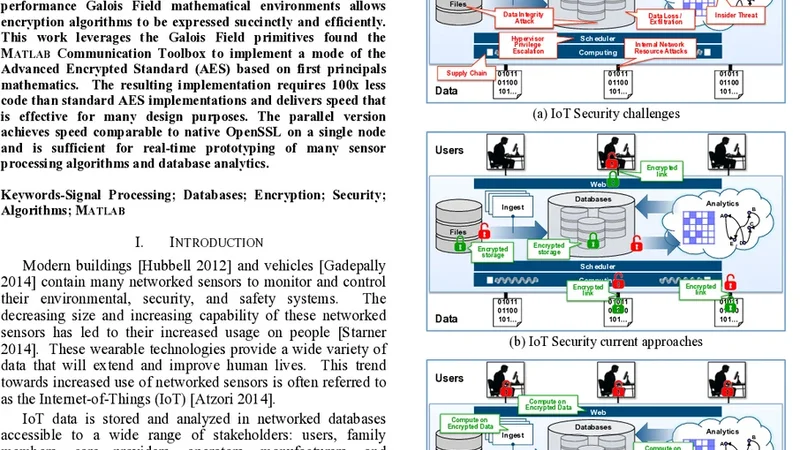
Parallel Vectorized Algebraic AES in MATLAB for Rapid Prototyping of Encrypted Sensor Processing Algorithms and Database Analytics
Percolation Model of Insider Threats to Assess the Optimum Number of Rules
Perfect Secrecy under Deep Random assumption
Performance Analysis of AODV, DSDV and DSR in MANETs
Planning Security Services for IT Systems
Policy based intrusion detection and response system in hierarchical WSN architecture
Predictive Cyber-security Analytics Framework: A non-homogenous Markov model for Security Quantification

Privacy by design in big data: An overview of privacy enhancing technologies in the era of big data analytics

Protecting Online Documents from an Unauthorized External Access (in Bulgarian)
